- Cisco Community
- Technology and Support
- Networking
- Routing
- NAT rule order CISCO ASDM
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-01-2022 01:33 PM
I have configured my Cisco ASA to translate internal addresses to external (WAN) interface. Everything works right, internet connection works as expected.
I have created site to site tunnel between ASA and AWS. I was able to ping resources on AWS from hosts behind ASA but not other way around. I have finally discovered that the problem is with NAT Rules.
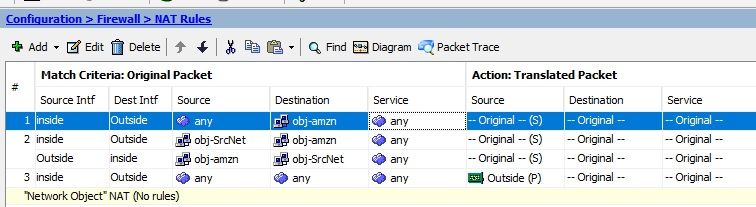
Here is how I have this set up:
If I disable the last rule (#3), I am able to access internal hosts form AWS but I am not able to access internet.
How do I set this up so when I communicate to and from AWS to inside addresses are not translated, but if I initiate communication from inside to everywhere else but AWS, ASA translates everything to outside (WAN)
obj-amz (VPC in AWS 196.168.0.0)
obj-SrcNet (Subnet INSIDE - behind ASA 10.0.1.0)
Solved! Go to Solution.
- Labels:
-
LAN Switching
-
Routing Protocols
-
WAN
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-01-2022 02:03 PM
This is usually accomplished by configuring a static NAT which translates the inside and outside addresses to themselves, which essentially exempts that traffic from being translated by your rule #3.
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-01-2022 02:03 PM
This is usually accomplished by configuring a static NAT which translates the inside and outside addresses to themselves, which essentially exempts that traffic from being translated by your rule #3.
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-01-2022 02:14 PM - edited 01-01-2022 02:21 PM
Thank you Richard. I have changed rule number 3 (source NAT type) from Dynamic PAT to Static, and it worked as a charm.
Can you please explain little more on how it works? I really would like understand this concept. Maybe you know some articles or yt tutorials that can be helpful.
I don't understand why rules number 1 and 2 were not overriding rule number 3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-01-2022 10:52 PM
Hello,
have a look at the site linked below, it has a pretty good explanation of how NAT exemptions work...
https://www.practicalnetworking.net/stand-alone/cisco-asa-nat/#asa-identity-nat
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-02-2022 06:20 AM
This is awesome. Thank you Georg!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-02-2022 08:10 AM - edited 01-02-2022 09:22 AM
Thank you again. I fixed it by following steps from recommended website. I needed to setup NAT exemption rule that does not translate addresses over the tunnel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-02-2022 09:26 AM - edited 01-02-2022 09:33 AM
I am a bit confused. In a previous response you said that you changed rule 3 and it worked. In the most recent post what I see as rule 2 looks to be the same as original rule 3, not a changed rule.
[edit] Apparently while I was typing my response the post was changed from one saying that there was still a problem to saying that it is fixed. Glad to know that it is fixed.
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-02-2022 09:36 AM - edited 01-02-2022 09:39 AM
That is correct. I was as confused as you are. Yesterday after I changed rule number 3 to static NAT every worked great. Therefore I got rid of some rules that were not needed and everything was still working out as expected.
This was not the case anymore this morning... I have no idea why but I followed articles suggested by George, I have set up the exemption rule and now everything seems to be working again.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide