- Cisco Community
- Technology and Support
- Networking
- Routing
- No Internet Access?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
No Internet Access?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-12-2020 06:31 PM - edited 01-12-2020 06:33 PM
I have a test lab environment at home. I have one Cisco 1841 router and a Zyxel Zywall USG 20.
The Zywall connects to my ISP. The Cisco router is behind that.
The Zywall is on the 10.10.10.0/24 network (10.10.10.1)
Router setup:
-fa0/0 10.10.10.254 255.255.255.0 (directly connected to my Zywall)
-no shut
-fa0/1 10.10.11.254 255.255.255.0 (directly connected to my laptop)
-no shut
-No routing protocols are configured on this router (eigrp, rip, ospf, etc...)
Why can't I get out to the internet with my laptop directly connected to the router with static IP of 10.10.11.1/24?
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 07:17 AM
Hello
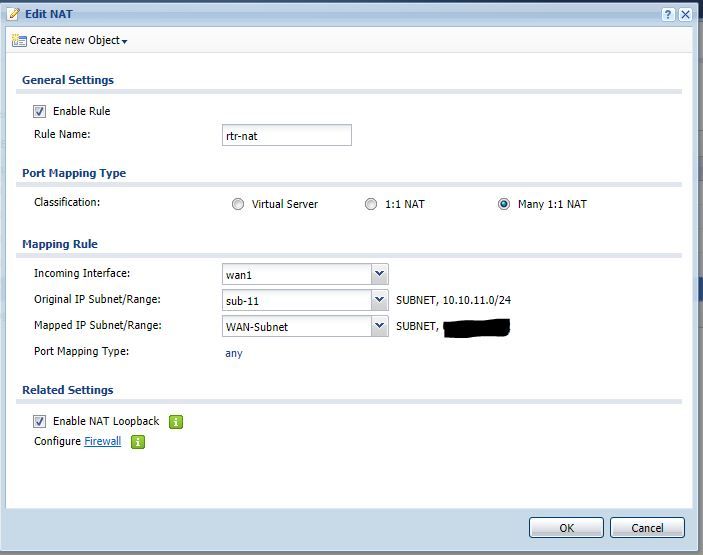
The Mapped ip subnet/range in the picture needs to be the object used for the wan public ip addressing and not the other lan subnet
I think you would already have an object created for this public ip address/range, if not then create one if so then just append that to the the Mapped ip subnet/range
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 07:53 AM
Okay so I added the NAT rule to the Firewall and removed the NAT rule from the Cisco 1841 router. I still can not access the the internet from the 10.10.11.0/24 network, but for the first time I can PING the 10.10.11.254/24 IP address from the 10.10.10.0/24 network.
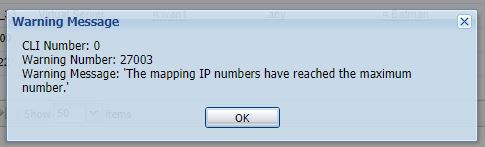
Just to add I did receive a message when configuring the NAT rule for the 10.10.11.0/24 network on the Firewall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 10:59 AM
Hello
Ive just noticed that says many1:1 nat not many:1 nat which is different. as many:1 basically means using port address translation (PAT)
Can you try deleting that rule and recreate it again the same way BUT select 1:1 NAT
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 07:19 AM
This discussion seems to be progressing along 2 tracks. One approach is to have the firewall configure a route for subnet 10.10.11.0 and configure address translation for that subnet. There seems to be some confusion about how to accomplish this or whether it has been done correctly. The second approach is to have the 1841 perform address translation for the 10.10.11.0 subnet. The posted configuration of the 1841 does have address translation configured and I am puzzled about why that seems not to be working. Perhaps showing the translation table might shed some light on this?
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2020 07:41 AM - edited 01-20-2020 08:20 AM
I deleted this one post because I did not want it to confuse people viewing this thread. It was a duplicate post on the Route's running configurations.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2020 11:09 PM - edited 01-16-2020 11:14 PM
looking at your post
try the following:
1)click on many:1 nat
2) rule name - rtr-nat
3) incoming interface = wan
4) Original/mapped ip range - need to create an object
5) create object - = name rtr1 subnet start 10.10.11.1 end ip - 10.10.11.254
6) create object - = name wan subnet start 1.1.1.1 end ip - 1.1.1.1 ( public ip address)
7) original ip range = rtr1 subnet
8) mapped ip range = wan subnet
9) port mapping type = any
10) enable rule
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-14-2020 02:30 PM - edited 01-14-2020 02:35 PM
Hello
@keithhampshire wrote:
Isn't NAT for routing internal private IP address out to the internet (Public IP address)?
Why would I use NAT when I'm using private IP addresses on both sides of the router? Remember my FireWall is facing the internet and then my router is behind that.
No it isn't - It sounds like your FW is natting on 10.10.10.254/24 ONLY.
Regards your fw its ONLY aware of its lan facing subnet (10.10.10.254/24) which is the rtrs wan facing interface
It is most probably as i stated before unaware of that rtrs own lan facing subnet (10.10.11.254/24) So you need to do either of those 2 options suggested.
1) On the FW - add a static route to point to its lan facing interface (the rtrs wan interface) and its ip address and then append its existing nat ruling to incorporate the rtr lan subnet 10.10.11.0/24
or
2) On the rtr apply nat @Georg Pauwen suggested
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-13-2020 01:04 AM
Hello
@keithhampshire wrote:
Router setup:
-fa0/0 10.10.10.254 255.255.255.0 (directly connected to my Zywall)
-no shut
-fa0/1 10.10.11.254 255.255.255.0 (directly connected to my laptop)
-no shut
Why can't I get out to the internet with my laptop directly connected to the router with static IP of 10.10.11.1/24?
Probably because the Fw isn't aware of the 10.10.11.0/24 subnet, you need to add a static route on the FW for that subnet to point towards the rtr and also add this subnet to the NAT FW rule.
Alternatively you can perform NAT on the rtr just for that subnet as stated by @Georg Pauwen
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide