- Cisco Community
- Technology and Support
- Networking
- Routing
- TCP retransmission and TCP Dup ACKs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
TCP retransmission and TCP Dup ACKs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2010 11:35 AM - edited 03-04-2019 09:56 AM
I have a windows 2003 server (192.168.30.1) behind a Linksys RV042 (192.168.30.254) router connected to a Comcast cable box.
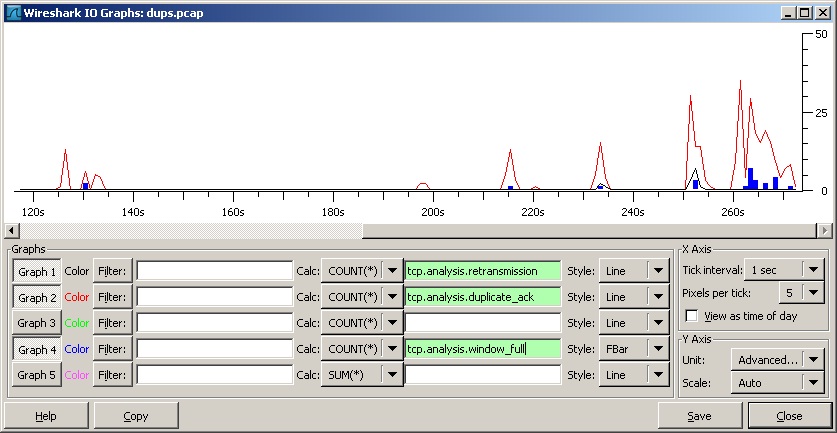
I see some TCP retransmission and TCP Dup ACKs in wireshark when I access websites form that server.
What information do I need from the packet that would help me determine if the problem is with the router configuration or network card settings or cable modem perhaps?
Thanks
Do i need to adjust TCP window size?
- Labels:
-
Other Routing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2010 02:13 PM
Hi Eugene,
I would say that a certain level of TCP retransmissions and duplicate acks are expected, especially over the internet with multiple routing paths and non-reliable delivery.
Of course, we do not want to see too high a proportion of these! What overall rate of retransmissions do you have in this tcp stream?
Adjusting the window size would need to be done on both end-points - this would effectively increase the data pipe between the hosts before they require acknowledgement so in effect you would be able to increase the tcp throughput. I'm not sure if this is a good idea over the internet however, as reliability is never guaranteed so you could see more lost acknowledgements but for larger windows, hence higher payload retransmissions required and degraded performance.
But you'll never know till you try!
Kind regards, Ash.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-30-2010 06:23 AM
Ash,
Out of 8453 captured packets 27 are retransmissions and 355 are duplicate acks. Which comes out do be less than 1%. Do you know what would be the acceptable percentage of errors on the WAN connection?
Thanks
p.s. Capture is attached to my 1st post
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-30-2010 07:04 AM
Hi Eugene,
I have often asked myself this question - and it seems logical that the answer may be different applications have different levels of tolerance for the level of TCP retransmissions. So there may not be any hard and fast acceptable threshold for retransmits (that I can find), I would be concerned at anything above 5-10% for sure!
See this post over on ethereal.com, discussing the same thing:
http://www.ethereal.com/lists/ethereal-users/200601/msg00166.html
So, I would seek to minimise the retransmissions where possible, but only if I have a cast-iron reason to do so. Else my energies may be better spent elsewhere!
Regards, Ash.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide