- Cisco Community
- Technology and Support
- Networking
- SD-WAN and Cloud Networking
- Question about establishing SDWAN overlay tunnels with single NAT IP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Question about establishing SDWAN overlay tunnels with single NAT IP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-28-2022 07:01 PM
Hi,
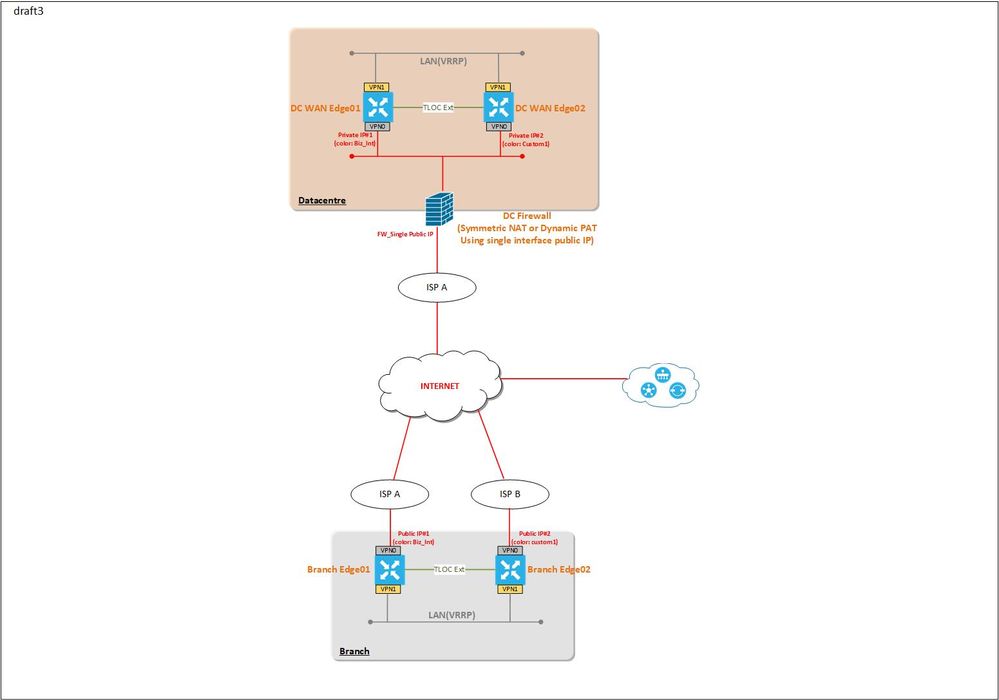
I am trying to design SDWAN connection between DC and remote sites.
DC has a firewall having a single Internet connection and will be supposed to do NAT for internal hosts to the Internet.
As the design plan, I am thinkg DC WAN Edges will be positioned behind the firewall and assigned to private IP address to each the transport VPN.
And remote site WAN Edges will be assigned with static public IP addresses.
From checking SDWAN document, overlay tunnels are available between public IP and private IP(via Symmetric NAT).
I'd like to have TLOC extension between two colors for load sharing between two colors.
Given this base setup, my question is if it's possible to establish overlay tunnels with different color to each DC WAN Edge, which each has private IP address and NATTed to the sinlg public IP on the DC firewall.
It will be great if you can share your experience with the similar design experience before.
- Labels:
-
Other SD-WAN
-
SD-WAN Architecture
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2022 03:32 PM
Hello,
If I understand your question correctly, you want know if it's possible to have two edge routers NATed by 1 public IP form tunnels with remotes edge routers in static public IP. The answer to your question is yes, it is common to have multiple edge routers behind same public IP for TLOC ext scenario. One thing I noticed in the topology is your DC has only one transport, so I dont know why do you need load sharing. If the goal is to provide redundancy if local connection to FW fails, you can consider put transport on loopback. That way tunnel will stay up if local connection to FW fail.
HTH,
Lei Tian
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2022 04:09 PM - edited 03-01-2022 04:59 PM
Thanks for you response, Lei.
Actually, my question was specifically whether it's possible to establish overlay tunnels between branch site and DC.
Each DC WAN Edge will be assigned to different color and private IP and will be Natted to the single public IP on the DC firewall.
It seems it's possible as you also answered.
I know there will be only one ISP link to the DC firewall which not much expected to share load using TLOC Ext, but I guess it might help on branch side which will have actual separate ISP links when traffic comming down to and comming up from branch office.
And of course, the HA setup was for hardware redundancy too. The DC firewall is also clustered using two hardware BTW.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide