The information in this document is based on these software and hardware versions:
ASA 5510 that runs software version 8.2(2) and ASDM version 6.4(9)
Anyconnect client software version 3.0 (It will work the same for versions prior to 8.3)
Microsoft Windows 2003 server as the CA server for the scenario.
Since the ASA version in use is 8.2.x we can enable per tunnel-group certificate authentication.
(Feature in the ASA 8.2.x release, using pre-8.2.x ASA code it will require to globally enabling the certificate authentication with the command
"ssl certificate-authentication interface <interface> port <portnum>").
In order to acomplish the AnyConnect authentication using certificates the AnyConnect client should get a valid certificate from the CA server, at the
same time the ASA should have the CA Root certificate in order to properly validate the certificate of the connecting client.

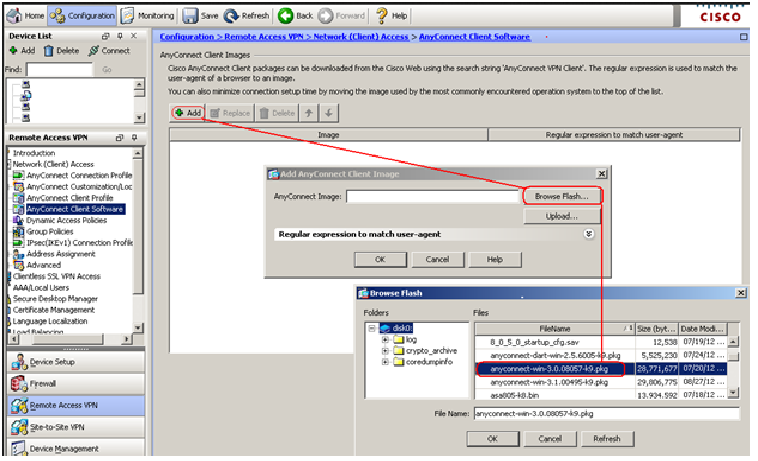
1-) Make sure you have an AnyConnect image applied in the ASA firewall:
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Client Software
Click the Add button, and browse the flash for the proper image (optionally you can upload the client from the local PC).
![]()
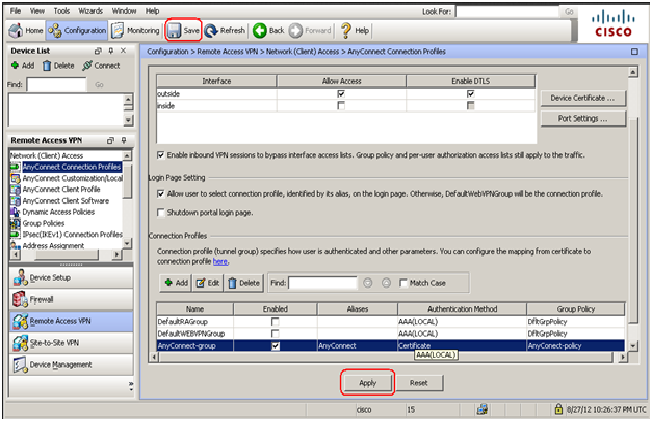
2-) Enable anyconnect in the outside interface:
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles
Check the box "Enable Cisco AnyConnect VPN Client or legacy SSL Client"
Then select the interface where the AnyConnect clients will be connecting to (in this example the outside interface).
![]()
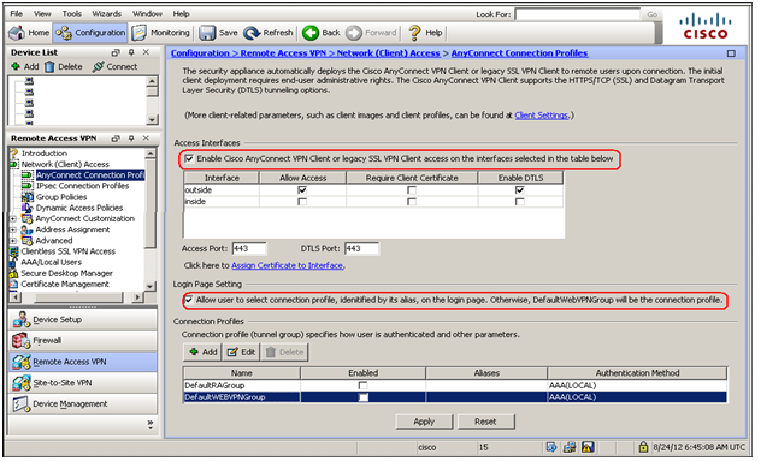
The " Allow user to select connection profile" check option will allow the AnyConnect user to select the group they will be connecting to.
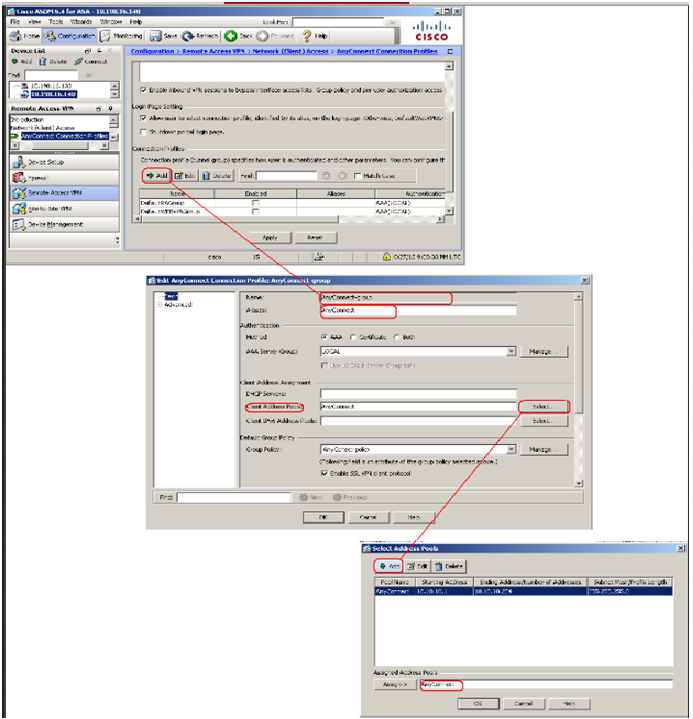
3-) Create a new AnyConnect connection profile:
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles
Click the Add button, the "AnyConnect connection profile" window will open.
Give the connection profile a name and optionally a group alias.
Click the "Select" button next to the "Client Address Pools" option.
The " Select Address Pools" window will appear.
Click the "Add" button in order to create a new pool of addresses.
4-) Create a Group-policy:
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles
Click the "Manage" button next to the "Group Policy" option in the connection profile.
Click the "Add" button in order to create the new policy.
Give the policy a name (In this example "AnyConnect-Policy") and check the "Clientless SSL VPN" and "SSL VPN Client" boxes, then click the "ok" button.
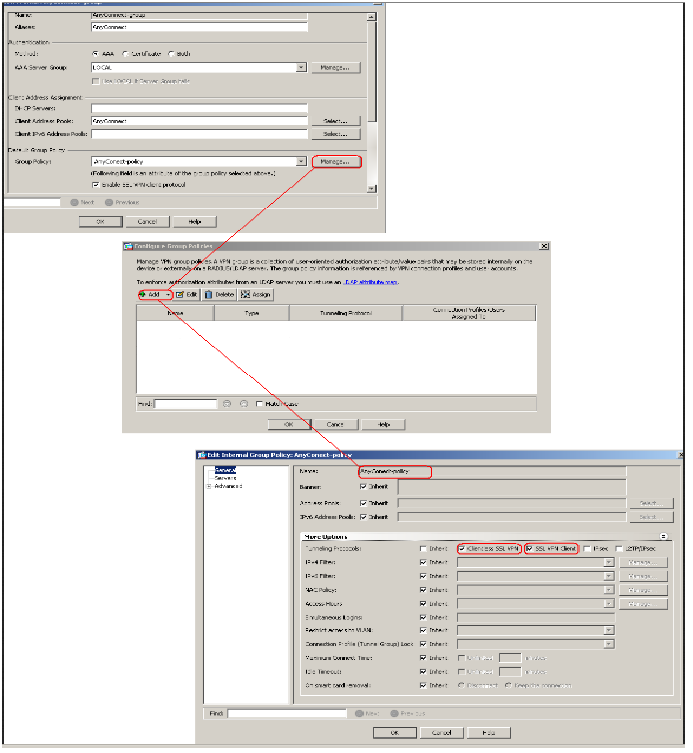
The AnyConnect group have been created at this point.
5-) Install the CA certificate in the ASA:
The CA certificate must be downloaded from the CA server and installed in the ASA.
Complete these steps in order to download the CA certificate from the CA server.
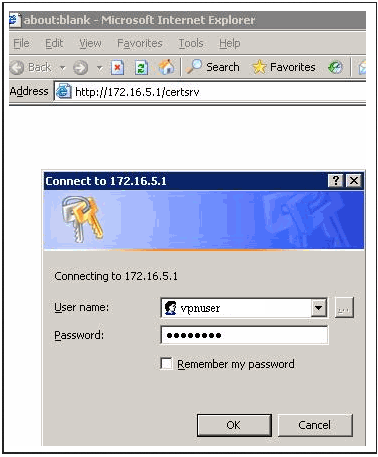
Perform the web login into the CA server CA-server with the help of the credentials supplied to the VPN server.

Click Download a CA certificate, certificate chain or CRL in order to open the window,
as shown. Click the Base 64 radio button as the encoding method, and click Download CA certificate.
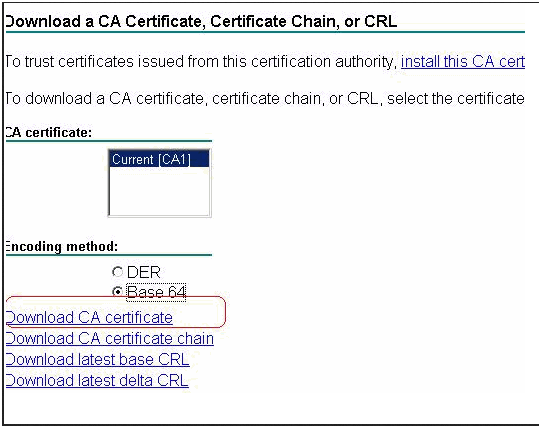
Save the CA certificate with the certnew.cer name on your computer.
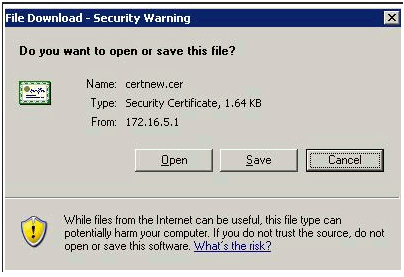
Go to Configuration > Remote Access VPN > Certificate Management > CA Certificates in the ASA firewall.
Click on the "Add" button, the "Install Certificate" window will open.
Click the "Browse" button next to the "Install from a file" option.
Browse to the location where you saved the CA certificate, highlight the CA certificate and click on the "Install" button.
At this point the CA certificate will be installed in the ASA fiwall and it willl be able to validate the connecting users, which user's certificate was created from the same CA server.
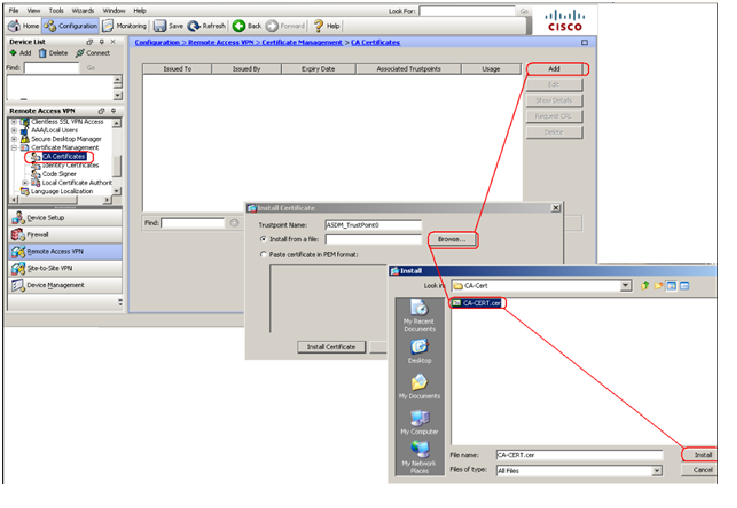
6-) Go back to the AnyConnect connection profiles and change the profile to use certificate authentication:
Configuration > Remote Access VPN > Network (Client) Access > AnyConnect Connection Profiles
Highlight the "AnyConnect-group" profile and click the "Edit" button.
The "Edit AnyConnect Connection Profile" will open, then you will be able to select the authentication method to be "Certificate"

Click the "OK" button and then click "Apply"
(Remember to save the configuration performed)
7-) The next step would be to install the certificate in the AnyConnect client PC:
The user will need to log in into the CA server with his credentials.
Once in the CA server, the user will need to click in the "Request a certificate" option.
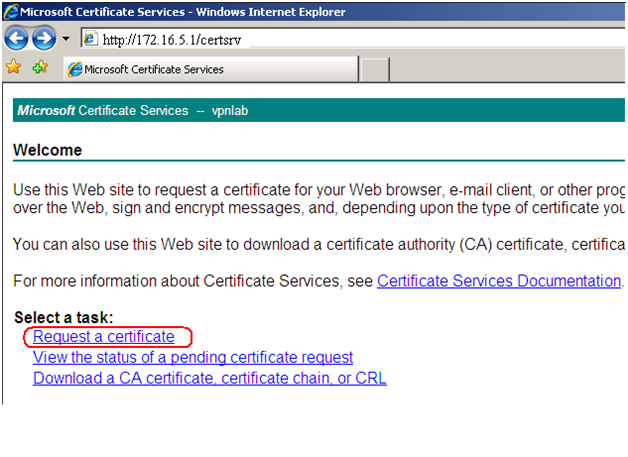
The user will want to select the "User Certificate" option.

At this point the CA sever will provide the user certificate to be installed.
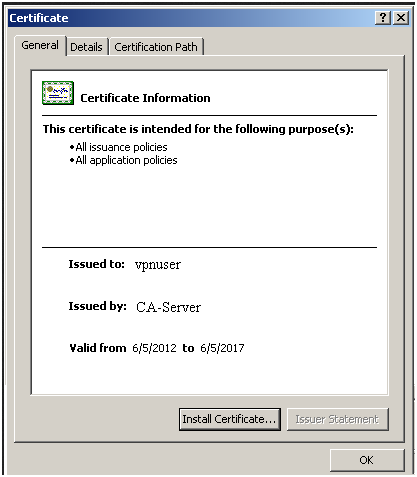
Once the certificate is installed the user will be able to connect the AnyConnect client authenticating with the previously installed certificate
(No username and password required)

Below you will find how the configuration should look like in the CLI interface:
ip local pool AnyConnect 10.10.10.1-10.10.10.254 mask 255.255.255.0
group-policy AnyConect-policy internal
group-policy AnyConect-policy attributes
vpn-tunnel-protocol svc webvpn
tunnel-group AnyConnect-group type remote-access
tunnel-group AnyConnect-group general-attributes
address-pool AnyConnect
default-group-policy AnyConect-policy
tunnel-group AnyConnect-group webvpn-attributes
authentication certificate
group-alias AnyConnect enable
webvpn
enable outside
svc image disk0:/anyconnect-dart-win-2.5.6005-k9.pkg 1
svc enable
tunnel-group-list enable
crypto ca trustpoint ASDM_TrustPoint0
revocation-check none
no id-usage
enrollment terminal
crypto ca authenticate ASDM_TrustPoint0
MIIEtDCCA5ygAwIBAgIQcNSMRXs696JMHFgTc+OKPjANBgkqhkiG9w0BAQUFADBV
MRMwEQYKCZImiZPyLGQBGRYDY29tMRUwEwYKCZImiZPyLGQBGRYFY3J0YWMxFjAU
BgoJkiaJk/IsZAEZFgZ2cG5sYWIxDzANBgNVBAMTBnZwbmxhYjAeFw0xMjA2MDUy
MDAyNThaFw0xNzA2MDUyMDExNTdaMFUxEzARBgoJkiaJk/IsZAEZFgNjb20xFTAT
BgoJkiaJk/IsZAEZFgVjcnRhYzEWMBQGCgmSJomT8ixkARkWBnZwbmxhYjEPMA0G
A1UEAxMGdnBubGFiMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA2Wo7
iCHElRUbgGAJgsf52AxlQLmeyMTSgS2I6/hTCOmra5BkP4cUieSeWqnOAPYgGTj/
it3qGVLBjkjf2sHBUBHfIUm8nnQF2UNjTbJZVIfCAyrHoRXNDFNV6qlKFoMmi7VG
2CudXsbuC86LsFDTMkk2Y2UB/T1xUpf5TBX+uQDb7w4jIZs1DkpQBmE946lH8vyA
GHU6RdainLr/44Sa0iPjzngMdssq0QlE/8gYWr6HsAOvmKhf8RcokjqXEQ36JyAF
+N/6sqoDTYl6jXg72PuoLO/zcmu8qbY+aRQGu5tlKXVemb9FyEKOuLe/Q4PirCz1
TUHw8urOHcHCquo5PwIDAQABo4IBfjCCAXowEwYJKwYBBAGCNxQCBAYeBABDAEEw
CwYDVR0PBAQDAgGGMA8GA1UdEwEB/wQFMAMBAf8wHQYDVR0OBBYEFNI2q3uAQNAg
nR+BfjqEcGUZaHoNMIIBEgYDVR0fBIIBCTCCAQUwggEBoIH+oIH7hoG7bGRhcDov
Ly9DTj12cG5sYWIsQ049dnBuLXNlcnZlci0wMSxDTj1DRFAsQ049UHVibGljJTIw
S2V5JTIwU2VydmljZXMsQ049U2VydmljZXMsQ049Q29uZmlndXJhdGlvbixEQz12
cG5sYWIsREM9Y3J0YWMsREM9Y29tP2NlcnRpZmljYXRlUmV2b2NhdGlvbkxpc3Q/
YmFzZT9vYmplY3RDbGFzcz1jUkxEaXN0cmlidXRpb25Qb2ludIY7aHR0cDovL3Zw
bi1zZXJ2ZXItMDEudnBubGFiLmNydGFjLmNvbS9DZXJ0RW5yb2xsL3ZwbmxhYi5j
cmwwEAYJKwYBBAGCNxUBBAMCAQAwDQYJKoZIhvcNAQEFBQADggEBAEHyvayVbKqT
0rwZNFBC3GAnUCDCK3kJxyjvir+T2pcCVS5KLukhTcDtr5VBOrSGsFA+zJvqB7qS
dwAvh9tKjpdb6rQKM5bo7NKii7mU71WxK8/wSupLMlNEZemvZcnaLKB2P5TGwJ0K
9LTp/rT89pvO9QbEMnRMPi0dPHQbu90sDLLBksxUfXII8qNyjjqNnVq2GDHX56Gz
DzltLTLnrL4Gb/1M9ulwO2bzNV9J7uVg6iELJDbzkHFaCNXTvQJyDsN41xETg54Y
uv6hViCXnu0SaaWi2rjVqx8pUXD7O3jrH9jnBC71cUqzv+MBvJI3th9iMMA80Gno
Rl0Ipuf7dYk=
quit
I hope this information can be helpful for you..
