- Cisco Community
- Technology and Support
- Small Business Support Community
- Switches - Small Business
- Password Setting Updates in Cisco Business Switches Firmware 3.2
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Password Setting Updates in Cisco Business Switches Firmware 3.2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-07-2022 01:28 PM - edited 07-07-2022 01:29 PM
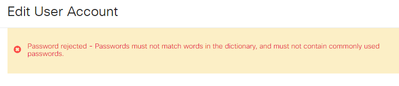
Heads up CBS250 & CBS350 users, the upcoming firmware update version 3.2 will contains updates to the password requirements. An article will be linked once published. Below is a snippet from that article highlighting the mandatory changes.
These will apply to all new user accounts and any password changes made to existing user accounts.
-
New Rules cannot be disabled.
-
It will verify that the password is not from a list of known common passwords. This common password list was compiled by choosing the 10,000 most used passwords from a list of the 10,000,000 most common passwords. This list can be found on the github link.
-
No variations of the common passwords using upper/lower case or using the following character substitutions:
"$" for "s", "@" for "a", "0" for "o", "1" for "l", "!" for "i", "3" for "e“
-
It will block passwords that include more than two sequential characters in a row (again looking for common substitutions and case). For example, if a password contains abc, it will be blocked as it has three sequential letters. So would @bc since there is the common substitution of the @ symbol for a. Similarly, cba will be blocked as it is sequential in reverse order. Other examples include “efg123!$”, “abcd765%”, “kji!$378”, "qr$58!230".
-
New password must not contain the username. For example, no “Admin548” for user admin.
-
New password must not contain the manufacturer name. For example, no C!sc0IsCool.
-
New password must not contain the product name. For example, no CBSCo0l$witch
- Labels:
-
Small Business Switches
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2023 12:04 PM
Cisco's arrogance never ceases to amaze me. You prevent device owners from using passphrases because some clueless programmer who thinks they know security thinks that doubled letters are a security risk yet "Now is the time for all good men" is a MUCH MUCH MUCH stronger password than something that has to be written down to be remembered. This is OUR hardware. Why don't you guys focus on fixing actual problems rather than fixing ones that don't exist?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2023 12:39 PM
Hello Terabyte,
Thank you for sharing your point of view. Password standards are something I agree we need to do better. Especially unifying the same standard across devices. There is agreement among our team that password standards need attention and we'll continue to represent this view in our conversations with our counterparts.
Thanks again,
Corey
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-28-2023 07:28 AM
I whoheartedly agree. Manufacturers should concentrate on firmware removing bugs, backdoors, etc and leave it upto the user to decide. A Cisco switch is a technical piece of kit and its usually sold to technical users not the average person in the street.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-28-2023 11:37 AM - edited 08-28-2023 11:38 AM
Bought some new switches and just spent 15 minutes trying to create a password to get into the first device. This new policy is awful! I gave up and used a randomly generated one which, as mentioned by another poster, will need to be written down because its **bleep** near impossible to remember. This is a terrible addition.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2023 10:13 AM
It is actually the little things like this (forcing people to come up with a password they will never remember, leading them to writing it down on a sticky note) that push people to a competitor's device. I have many cisco switches that all have the same administrative password, which nobody would ever be able to guess. I cannot use it with this new update. The quality of Cisco has not improved while the cost goes up. And don't even get me started on the fact that some Cisco products are bandwidth limited unless you pay for the extra license. I recently bought a switch from a Cisco competitor which is less than half the cost of a similar Cisco model, and it even has redundant power supplies unlike the Cisco model. I believe I will be going with this manufacturer for all of my networking needs from here on out. Sorry Cisco, you have lost the mark on the small/medium business market. I'm sure you will still be on top because of those large corporations that have millions of dollars in their IT budgets, and I hope you stay in the small/medium business market because that will keep the competitors' prices low.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2023 10:55 AM
Hey Thomas,
I hear you on this change being a painful one. On the support side we're always working with our internal partners on product development and that is an ongoing relationship. We'll continue to push for customer friendly password requirements internally.
Thank you for your feedback.
Corey
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-06-2023 08:03 AM
So Corey, basically what you're saying is Cisco has NO clue what good passwords are and made a horrible decision to FORCE this garbage on people who OWN these switches and we're at the mercy of the PM who signed off on this, right? I just got several of these in and will be RETURNING EVERY ONE OF THEM and buying switches from a vendor who 1) understands security, 2) respects customers, & 3) knows that without customers they're out of business.
I'm sorry if that's harsh or crass, but it's 2023, sugar coating doesn't solve problems. Firing PMs who make bad choices does.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-06-2023 08:35 AM
Hi ComCept,
I understand your frustration. While I cannot say I agree with your sentiment (Re: PMs), I appreciate your feedback.
The objective of these changes is to enhance the security of our devices in response to an increasingly sophisticated threat landscape. I know this product line has room for improvement, we'll continue to deliver yours and other's feedback even when its not sugar-coated. I understand, however, that these changes may not meet everyone's preferences and it's important to us that we hear from you when this is the case.
I hope you have a great day,
Corey
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2023 01:43 PM
I'm going to be blunt here. I really hope no one at Cisco is offended by this, Cisco's folks tend to get a little bent out of shape when called out on its poor decisions, but let's be perfectly clear, this does NOT enhance security. I get it, Cisco pays you so you have to tow the company line, but just because someone at Cisco says it's true does not make it so. Numerous studies have PROVEN this. In fact, many security researchers have been saying this for a decade. Spend 5 minutes in Google and you will see I'm correct.
Furthermore, explain why CsTm1962#%&( is NOT allowed but 9MWAjEhvc8uF is. It would be funny if it weren't so frustrating that your programmers believe the 2nd password is more secure than the first. The first password has FOUR categories and does NOT violate any of the reasons you claim in your rejection:
Furthermore, "There's nothing to fear but fear itself" is a far more complex password (in this case a pass-phrase) than anything I've gotten your system to accept. In the end what you've done is encouraged users, remember these are SMALL BUSINESS devices NOT enterprise devices, to write passwords down on sticky notes or just let a browser keep the passwords stored with anyone sitting at that computer now having FULL and unfettered access to those devices. This is NOT security in the small business world.
In the end, this is an indefensible requirement on hardware that your customers PAID FOR (or in this case, paid for and are returning and buying over 2 dozen new PoE switches from another vendor). Cisco needs to focus on fixing the plethora of actual problems with its products before forcing us to deal with this poorly considered and implemented system.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-10-2023 03:13 AM
Approaching from a different angle and more generally I think the IT industry as a whole needs to get a better handle on credentials. The vast majority of people struggle with password overload. IMHO passwords should be a thing of the past for every small business and consumer.
If someone can use biometrics to access their banking and other sensitive data then this concept should be extended to everything they use via agreed worldwide interoperability standards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-10-2023 05:44 AM
@jollypike you nailed it! Everyone EXCEPT Cisco has figured this out, passwords are a thing of the past (Cisco is 15 years too late on password requirements). Microsoft encourages PIN logins even on enterprise systems. Microsoft, Google, and Apple have all gone or are moving quickly to passwordless logins. Even the lowly likes of Facebook has that now.
Here's another thing. Cisco has told hackers EXACTLY what NOT to check for when trying to break into these devices. Hackers never never bother to check for CsTm1962#%&( (or any variation on that, trust me I've created that password in the same format a dozen times and it always fails) because they know it's not allowed. That's why smart companies NEVER disclose their security practices. Wonder what Cisco corporate would say if we asked them to share their internal security policies with the general public? We'd get laughed at. Wonder why? At the risk of being repetitive, Cisco's PMs have forced rules on us that actually HELP hackers break into devices. Allowing the OWNERS of the hardware, you now the people who actually make it possible for Cisco Small Business to exist, to use OUR hardware as we wish and set our own standards that would make the potential patterns infinitely more difficult to guess.
Anyway, it's not 2000. There are MANY other small business-focused networking vendors out there making excellent equipment at or below what Cisco gets for their small business equipment. I ditched Cisco WiFi years ago because of problems, now I'm ditching their switches. I have eval switches on order from several vendors to replace the ~2 dozen Cisco switches I have now, including 8 x 52 port PoE switches, 7 of which have 10Gbps ports to give you ideas on what they will cost to replace. That's a decent chunk of $ for us, but I guess Cisco just doesn't care because I'm sure they'd rather push customers to their pay-to-play division and phase out the small business division.
Anyway, time to RMA these switches
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2024 06:56 AM
What's the current status on the latest firmware?
Does Cisco still enforce this questionable policies?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide