- Cisco Community
- Technology and Support
- Networking
- Switching
- ASA 5505 VLAN bi-directional communication issue, no Security Pl
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 11:00 AM - edited 03-07-2019 05:42 AM
I know this is a pretty typical way to start this off but I am a bit of a newbie with VLANs and Cisco equipment. I am attempting to setup a communication between 2 VLANs. This setup is between two seperate medical practices Client1 who I have access to and Client2 which is not managed by be. I have access to only one of the practice's equipment. I have physically attached a cable from thier switch to my ASA in an attempt to get access to a shared server on Client2's network. I have created a VLAN called dmz to allow access from Client1 to the Client2. So far I am able to access the server from Client1 but I need to enable bi-directional access from Client2 to Client1's network. Namely to enable the ability for the server at Client2 to contact a printer on Client1's network. I have a visio that I have attached and the show run is also attached.
Can anyone point me in the right direction?
Solved! Go to Solution.
- Labels:
-
LAN Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 12:55 PM
Correct, I was clear about that. Here are some screen shots to clear up any confusion.
This is from the .51 host

On the .50 host
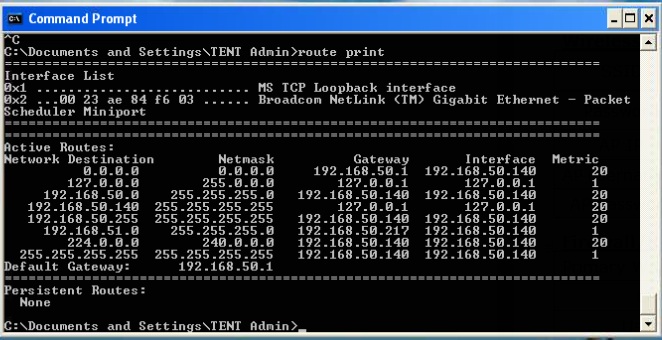
Pinging from the .50 host to the .51 host. I have not been able to get this to work.

trying to ping the .50 host from the .51 network. this worked before we made changes.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:02 PM
the configuration is correct.
can you post :
sh run nat-control
show xlate
Regards
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:06 PM
TEXASVOICE# sh run nat-control
no nat-control
TEXASVOICE# show xlate
23 in use, 92 most used
PAT Global 172.25.10.31(40128) Local 192.168.51.102(53045)
PAT Global 172.25.10.31(43588) Local 192.168.51.102(59631)
PAT Global 172.25.10.31(46826) Local 192.168.51.102(55656)
PAT Global 172.25.10.31(47615) Local 192.168.51.102(55654)
PAT Global 172.25.10.31(51196) Local 192.168.51.102(55648)
PAT Global 172.25.10.31(5820) Local 192.168.51.102(55633)
PAT Global 172.25.10.31(25096) Local 192.168.51.102(55632)
PAT Global 172.25.10.31(20522) Local 192.168.51.102(55629)
PAT Global 172.25.10.31(49337) Local 192.168.51.102(55628)
PAT Global 172.25.10.31(37230) Local 192.168.51.102(55626)
PAT Global 172.25.10.31(52274) Local 192.168.51.102(55621)
PAT Global 172.25.10.31(61775) Local 192.168.51.102(55620)
PAT Global 172.25.10.31(37847) Local 192.168.51.102(55613)
PAT Global 172.25.10.31(48891) Local 192.168.51.102(55611)
PAT Global 172.25.10.31(6892) Local 192.168.51.101(50932)
PAT Global 172.25.10.31(5621) Local 192.168.51.101(52633)
PAT Global 172.25.10.31(20992) Local 192.168.51.101(50931)
PAT Global 172.25.10.31(19175) Local 192.168.51.101(50917)
PAT Global 172.25.10.31(44687) Local 192.168.51.101(50916)
PAT Global 172.25.10.31(45123) Local 192.168.51.101(50897)
PAT Global 172.25.10.31(20574) Local 192.168.51.100(41975)
PAT Global 172.25.10.31(40036) Local 192.168.51.100(57262)
PAT Global 172.25.10.31(32355) Local 192.168.51.100(57611)
TEXASVOICE#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:10 PM
Paste the output for each
packet-tracer input inside icmp 192.168.51.100 0 0 192.168.50.100
packet-tracer input dmz icmp 192.168.50.100 0 0 192.168.51.100
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:15 PM
TEXASVOICE# packet-tracer input inside icmp 192.168.51.100 0 0 192.168.50.100
Phase: 1
Type: ACCESS-LIST
Subtype:
Result: ALLOW
Config:
Implicit Rule
Additional Information:
MAC Access list
Phase: 2
Type: ROUTE-LOOKUP
Subtype: input
Result: ALLOW
Config:
Additional Information:
in 192.168.50.0 255.255.255.0 dmz
Phase: 3
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group inside_access_in in interface inside
access-list inside_access_in extended permit ip any any
Additional Information:
Phase: 4
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 5
Type: INSPECT
Subtype: np-inspect
Result: ALLOW
Config:
Additional Information:
Phase: 6
Type: NAT
Subtype:
Result: DROP
Config:
nat (inside) 1 0.0.0.0 0.0.0.0
match ip inside any dmz any
dynamic translation to pool 1 (No matching global)
translate_hits = 29, untranslate_hits = 0
Additional Information:
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: dmz
output-status: up
output-line-status: up
Action: drop
Drop-reason: (acl-drop) Flow is denied by configured rule
TEXASVOICE#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:21 PM
The issue is the "nat (inside) 1 0.0.0.0 0.0.0.0" as you can see
!!! Beware that this will cause traffic distruption for those active flows
access-list NAT-TO-OUTSIDE deny 192.168.51.0 255.255.255.0 192.168.50.0 255.255.255.0
access-list NAT-TO-OUTSIDE permit ip any any
no nat (inside) 1 0.0.0.0 0.0.0.0
nat (inside) 1 access-list NAT-TO-OUTSIDE
After this try again :
packet-tracer input inside icmp 192.168.51.100 0 0 192.168.50.100
Regards
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:34 PM
I recieved the following error when trying to enter the command:
TEXASVOICE(config)# access-list NAT-TO-OUTSIDE deny 192.168.51.0 255.255.255.0$
access-list NAT-TO-OUTSIDE deny 192.168.51.0 255.255.255.0 192.168.50.0 255.255. ^255.0
ERROR: % Invalid input detected at '^' marker.
However!, I am now able to ping between both of those hosts on the network. Do you think I still need to fix the above error?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:35 PM
access-list NAT-TO-OUTSIDE extended deny ip 192.168.51.0 255.255.255.0 192.168.50.0 255.255.255.0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:56 PM
ok
access-list nonatvpn extended permit ip 192.168.51.0 255.255.255.0 192.168.50.0 255.255.255.0
nat (inside) 1 0.0.0.0 0.0.0.0
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 02:11 PM
Looks like it is working! Thanks! Now I need to add routes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 02:12 PM
My pleasure
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:36 PM
TEXASVOICE# packet-tracer input inside icmp 192.168.51.100 0 0 192.168.50.100
Phase: 1
Type: ROUTE-LOOKUP
Subtype: input
Result: ALLOW
Config:
Additional Information:
in 192.168.50.0 255.255.255.0 dmz
Phase: 2
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group inside_access_in in interface inside
access-list inside_access_in extended permit ip any any
Additional Information:
Phase: 3
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 4
Type: INSPECT
Subtype: np-inspect
Result: ALLOW
Config:
Additional Information:
Phase: 5
Type: HOST-LIMIT
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 6
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group dmz_access_out out interface dmz
access-list dmz_access_out extended permit ip any any
Additional Information:
Phase: 7
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 2257, packet dispatched to next module
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: dmz
output-status: up
output-line-status: up
Action: allow
TEXASVOICE#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:39 PM
Perfect !
Try now pinging from one end to the other
Regards
Dan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:40 PM
See below for that access-list command.
TEXASVOICE# conf t
TEXASVOICE(config)# access-list NAT-TO-OUTSIDE extended deny ip 192.168.51.0 2$
WARNING:
TEXASVOICE(config)# exit
TEXASVOICE# show run
: Saved
:
ASA Version 8.2(5)
!
hostname TEXASVOICE
enable password dtJhjDaLEVdFCjPH encrypted
passwd aMQgPzkWn3LmfS0x encrypted
names
name 192.168.50.4 NETMEN
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
switchport access vlan 12
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.51.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address 172.25.10.31 255.255.255.0
!
interface Vlan12
no forward interface Vlan2
nameif dmz
security-level 100
ip address 192.168.50.217 255.255.255.0
!
ftp mode passive
same-security-traffic permit inter-interface
access-list inside_access_in extended permit ip any any
access-list outside_access_in extended permit icmp any any echo-reply
access-list outside_access_in extended permit icmp any any echo
access-list outside_access_in extended permit icmp any any time-exceeded
access-list outside_access_in extended permit icmp any any unreachable
access-list outside_access_in extended permit tcp 10.1.100.0 255.255.255.0 192.168.51.0 255.255.255.0 eq 9100
access-list outside_access_in extended permit tcp 10.1.100.0 255.255.255.0 192.168.51.0 255.255.255.0 eq lpd
access-list DATACENTER-VPN extended permit ip 192.168.51.0 255.255.255.0 10.1.100.0 255.255.255.0
access-list nonatvpn extended permit ip 192.168.51.0 255.255.255.0 10.1.100.0 255.255.255.0
access-list inside_nat_outbound extended permit ip any 192.168.50.0 255.255.255.0
access-list dmz_access_in extended permit ip any any
access-list NAT-TO-OUTSIDE extended permit ip any any
access-list NAT-TO-OUTSIDE extended deny ip 192.168.51.0 255.255.255.0 192.168.50.0 255.255.255.0
access-list dmz_access_out extended permit ip any any
pager lines 24
logging asdm informational
mtu inside 1500
mtu outside 1500
mtu dmz 1500
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 0 access-list nonatvpn
access-group inside_access_in in interface inside
access-group outside_access_in in interface outside
access-group dmz_access_in in interface dmz
access-group dmz_access_out out interface dmz
route outside 0.0.0.0 0.0.0.0 172.25.10.1 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
http server enable
http 0.0.0.0 0.0.0.0 inside
http 0.0.0.0 0.0.0.0 outside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
no sysopt connection permit-vpn
crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
crypto map outside_map 1 match address DATACENTER-VPN
crypto map outside_map 1 set peer 69.39.160.194
crypto map outside_map 1 set transform-set ESP-3DES-SHA
crypto map outside_map interface outside
crypto isakmp identity address
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
telnet timeout 5
ssh 0.0.0.0 0.0.0.0 inside
ssh 0.0.0.0 0.0.0.0 outside
ssh timeout 60
console timeout 0
management-access inside
dhcpd dns 10.110.12.8 10.120.62.15
dhcpd auto_config outside
!
dhcpd address 192.168.51.100-192.168.51.199 inside
dhcpd enable inside
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
tunnel-group 69.39.160.194 type ipsec-l2l
tunnel-group 69.39.160.194 ipsec-attributes
pre-shared-key *****
!
!
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:b246a79b16ad2c607fc2d30e3591ee75
: end
TEXASVOICE#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2012 01:44 PM
no access-list NAT-TO-OUTSIDE extended permit ip any any
access-list NAT-TO-OUTSIDE extended permit ip any any
nat (inside) 1 access-list NAT-TO-OUTSIDE
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
