- Cisco Community
- Technology and Support
- Networking
- Switching
- connecting core switch to the internet ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2013 04:56 AM - edited 03-07-2019 04:02 PM
Hi,
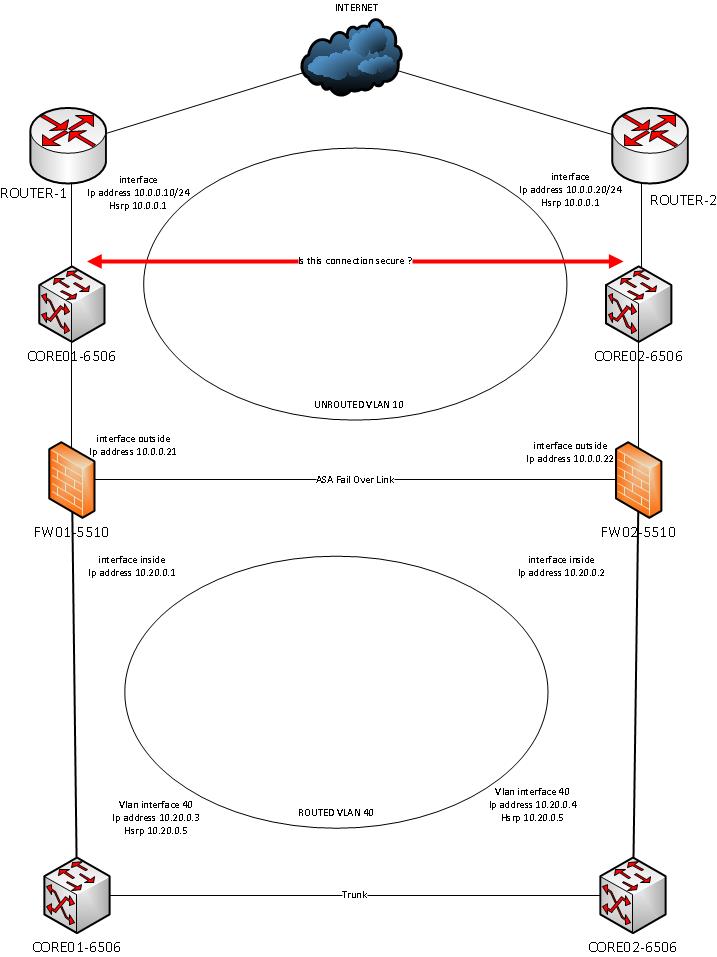
We have 2 6506's connected through an ether-channel trunk.
On these 6506's we have configured a vlan, vlan interface and 2 access ports for 2 ASA's.
These ASA's run in failover mode but only one ASA is physically connected at the moment.
We want to be more resilient so our provider has provided us with a redundant setup of routers for our internet connection.
However, for this construction they would need a layer 2 connection on our side to have HSRP running.
There are 2 options in my opinion :
- Buy a set of switches to facilitate the layer-2 connection between te routers and to connect the outside of the ASA's.
- Instead of buying 2 new switches, create a new unrouted vlan on our core 6506's and use access-ports for the routers and the ASA's.
But how safe is it to connected the core switch with an unrouted vlan to the internet router ?
In terms of vlan hopping or other possible attacks ?
I think i have to disable DTP, Spanning-Tree, CDP and maybe a lot more ?
Solved! Go to Solution.
- Labels:
-
Other Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2013 07:59 AM
Hi,
I don't think that is an issue. You have 2 border routers that face the provider's routers, which is a common setup. You also have firewalls behind your core routers to protect the internals network.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2013 05:07 AM
If the router and ASA interfaces are all access ports then DTP and VLAN hopping wouldn't be a factor on those interfaces. Then the only place it could happen is in the trunk between the 6506's. That you can mitigate by preventing native (untagged) packets being sent on that link in either direction.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2013 05:35 AM
Hi,
You don't need to buy a set of switches. You just need a trunk port between core1 and core-2 6500 switches. Then create 2 /29 subnets, one connects the 6500 core switches to the border router-1 and 2 with HSRP or VRRP and the other /29 connects the 6500 core switches to the firewall with VRRP or HSRP.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2013 07:54 AM
Hi Reza,
My main concern is security of the layer-2 port when connected to the router.
Any opinion about that ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2013 07:59 AM
Hi,
I don't think that is an issue. You have 2 border routers that face the provider's routers, which is a common setup. You also have firewalls behind your core routers to protect the internals network.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2013 12:17 AM
Hi,
And what about vlan hopping ? Because the 6506 between the router and firewall and the 6506 behind the firewall are the same devices.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2013 05:07 AM
If the router and ASA interfaces are all access ports then DTP and VLAN hopping wouldn't be a factor on those interfaces. Then the only place it could happen is in the trunk between the 6506's. That you can mitigate by preventing native (untagged) packets being sent on that link in either direction.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2013 07:36 AM
I am as far as applying this to secure the port :
switchport
switchport mode access
switchport access vlan X
switchport nonegotiate
spanning-tree bpdufilter enable
spanning-tree portfast edge
switchport port-security
switchport port-security maximum 3
switchport port-security violation restrict
no cdp enable
Any additions to this ?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide