- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: How to connect to links between Coreswitch and Nexus switch
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
How to connect to links between Coreswitch and Nexus switch
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 07:19 AM - edited 02-10-2021 07:33 AM
Hello
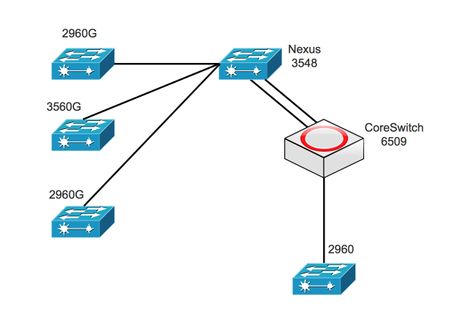
I need to connect two links between the Coreswitch 6509 (2 Trunk port) and Nexus 3548 (2 Trunk port), Also there is 3 edge switches Cisco 2960 uplink to Nexus.
So what is the recommendation to avoid any looping, should I create port-channel, Spanning-tree ?
Appreciate your help
Thanks
- Labels:
-
LAN Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 07:27 AM
Hello @mrmarie ,
yes a port-channel is recommended in your case.
The use of LACP is also a very good feature on C6509 side means channel-group X mode active on the member links.
on NX-OS should be similar
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 09:30 AM
Hello @Giuseppe Larosa
Thank you for your reply
and any spanning tree configuration should I do?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 02:26 PM
Hello @mrmarie ,
>> and any spanning tree configuration should I do?
No, because for STP a port-channel is a single logical link so no special configuration is needed. This is one of the advantages of bundles no member link is blocked by STP and it comes automatically with no special config.
if you have only one Nexus you will use a normal port channel on Nexus side also as noted by BB.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2021 09:09 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-14-2021 11:24 PM
Hello @mrmarie ,
if all devices are under your administration you shoud be able to increase bridge priority on devices that should never become root bridge for any STP instance ( if you are using PVST or Rapid PVST).
You might want to protect the root bridge choice on the core side you can use the spanning-tree root guard command.
Be very careful with this kind of commands giving them on the wrong devices can create a lot of issues.
Root guard in direction going away from root bridge is ok
Root guard in direction going to the root bridge is not ok at all ! You can use loop guard in direction to the root bridge on edge device side.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 07:35 AM
consider using Port-channel with LACP, and take where advantage use vPC on nexus.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 09:34 AM
Hello @balaji.bandi
Thank you for your reply
so should I configure channel-group from Core side and vPC from Nexus side?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 09:57 AM
yes you can do nexus side vPC and Core side normal Port-channel should work. (this high level technically should work)
if your network have many interconnected back to nexus we need to know fuill network diagram.
we suggested only based on the information what provided here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 11:38 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 01:50 PM
Is this your final diagram have only 1 device at each level, then standard port-channel is good enough with LACP ( you do not need vPC)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2021 10:07 AM
Cisco 6K Core SW
Cisco NSK 3K Aggregate SW
Cisco Catalyst 2960 Access SW ?
are NSK is vPC or not ?
why not L2 between Core and Aggregate SW?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-14-2021 11:52 PM
Hello,
on a side note, you might want to make sure that none of the 2960 switches accidentally become the root for any of your Vlans. You could set the 6509 as root primary and the Nexus as root secondary:
6509
spanning-tree vlan x root primary
Nexus
spanning-tree valn x root secondaty
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-15-2021 03:32 AM - edited 02-15-2021 03:34 AM
Hello
There are a couple of things you don’t mention
- is the Nexus are running vpc or it its a standalone switch(s)?
- What spanning-tree mode you are running
The following example would allow you connect two physical interfaces into a L2 EtherChannel from the cisco core into the nexus which is either running vpc or not, Also make sure the cisco core switch is indeed to STP root for the lan estate.
6509
default interface range x/x
interface range x/x
shut
channel-group 1 mode active
interface port-channel 1
description Nexus
switchport
switchport mode trunk
no shut
spanning-tree vlan 1-4094 priority 0
or
spanning-tree mst x priority 0
Nexus standalone switch
feature lacp
default interface range x/x
interface range x/x
channel-group 1 mode active
interface port-channel 1
description 6509
switchport mode trunk
no shut
default interface range x/x
interface range x/x
channel-group 2 mode active
interface port-channel 2
description access-switch
switchport mode trunk
no shut
Nexus VPC
switchs 1 & 2
feature vpc
feature lacp
default interface Ethernetx/x
interface Ethernetx/x
channel-group 1 mode active
interface port-channel 1
description 6509
switchport mode trunk
vpc 1
no shut
default interface x/x
interface x/x
channel-group 2 mode active
interface port-channel 2
description access-switch
switchport mode trunk
no shut
vpc 2
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide