- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: SW_MATM-4-MACFLAP_NOTIF between 3750 and Nexus 5k
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
SW_MATM-4-MACFLAP_NOTIF between 3750 and Nexus 5k
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2021 12:44 PM
Hi,
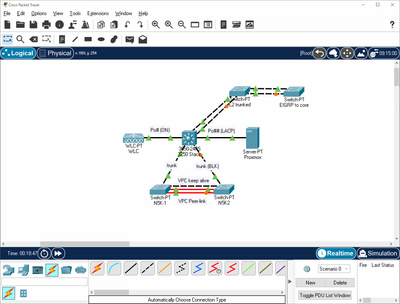
Recently we decided to prepare a Nexus 5k switch (paired in VPC w/ FEX's) and connect it to our 3750 stack, which also has a WLC (etherchannel ON) and a Proxmox cluster with trunking LACP ports connected to it.
The problem that we ran into was sudden and fairly regular spamming of the console logs on the 3750 (core switch) regarding the SW_MATM-4-MACFLAP_NOTIF from hosts that are on both the WLC and the Proxmox cluster.
Some digging and debugging showed that the logged hosts are flapping between the non (STP) blocked Nexus uplink and the proper port. I did an outbound trunk monitor session to a machine on the N5K running tcpdump and found that it appears that only BUM traffic that is confusing the 3750. Specifically ARP appears to be getting sent into the Nexus and then back out of the interface (trunk) it came in on, for unknown reasons.
I tried put the second nexus (vpc peer) into maintenance, and even disable the VPC on both ends, but nothing seems to stop the 5K from mirroring the ARP's (and an IP6 RS I saw) from going back out the trunk link to the core, which in turn causes the flapping message.
Does anyone know of any reason that could cause this? It's a rather basic stripped down setup with out the vlan and native vlan relevant to the network I want to share being allowed. I suppose I could make a separate vlan just for the Nexus and setup a GW etc, but I am concerned that the Nexus switch could cause similar issues in the final environment.
Thoughts?
- Labels:
-
Catalyst 3000
-
Other Switches
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2021 01:27 PM
Hello,
post a diagram of your topology showing how all devices involved are connected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2021 07:20 PM
Hey,
I did a quick stripped down layout to give a general idea of the setup.
The hosts are flapping between the WLC and the PVE cluster only, and doesn't happen when I turn off the Nexus trunks, of course.
Hope that helps! Thanks.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide