- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: uRPF question
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
uRPF question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2014 03:59 AM - edited 03-07-2019 07:08 PM
Hello
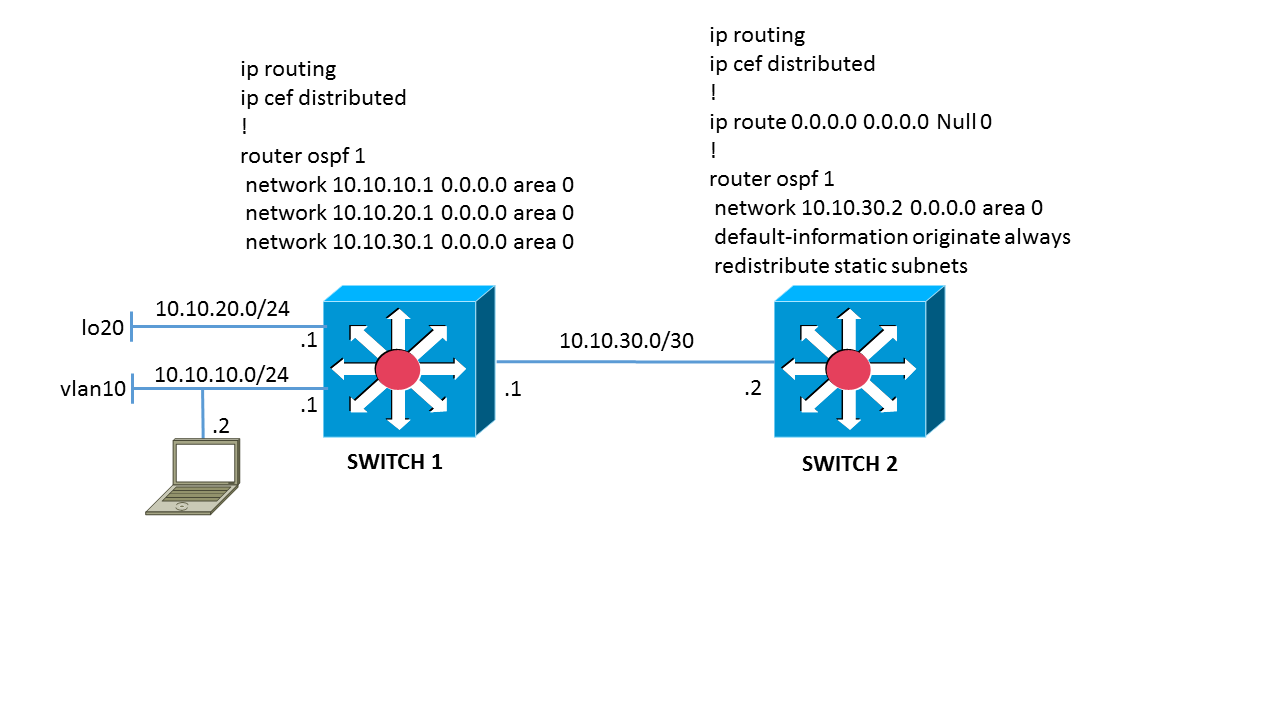
I setup the above lab to test uRPF on vlan SVIs using a WS-C3850-24P (IOS XE 03.03.02SE cat3k_caa-iosd-universalk9.SPA.150-1.EZ2.pkg) for switch1
I enabled the following debugs:
debug ip cef drops detail
debug ip cef drops rpf
And added the following to vlan 10 svi for rpf:
ip verify unicast source reachable-via rx
ip verify unicast notification threshold 0
TEST 1 The allow-default option isn't enabled for urpf on vlan 10. To check if urpf is working ok I pinged the vlan 10 svi from the switch1 cli:
switch1#ping 10.10.10.1
*Apr 16 08:11:10.641: CEF-Drop: Packet from 10.10.10.1 via Vlan10 -- via-rx
*Apr 16 08:11:10.642: CEF-Drop: packet from 10.10.10.1 via Vlan10: unicast rpf failed.
show ip interface vlan 10 and show ip traffic counters show increments for RPF
TEST2 Spoof a Source IP address in the same range as Lo20 on the laptop using nmap:
nmap -e eth4 -S 10.10.20.22 4.4.4.4
*Apr 16 08:15:11.249: CEF-Drop: Packet from 10.10.20.2 via Vlan10 -- via-rx
*Apr 16 08:15:11.249: CEF-Drop: Packet from 10.10.20.2 (Vl10) to 4.4.4.4, Input feature uRPF
show ip interface vlan 10 and show ip traffic counters show increments for RPF
TEST3 Spoof an arbitary source IP address on the laptop using nmap:
nmap -e eth4 -S 10.10.60.1 4.4.4.4
No outputs from the debugs and show ip interface vlan 10 and show ip traffic counters do not show increments for RPF.
I disabled rpf on vlan 10 and created a logging acl on switch1's interface to switch2 to check for this spoofed traffic and could see the acl hits ok. When I re-enable rpf on vlan 10 these acl hits stop.
I also enabled debug ip packet to see what was happening to the spoofed traffic but nothing appeared in the debug. The spoofed traffic is being dropped with rpf enabled but I am seeing nothing in the debugs, logs or counters.
Am I missing something? I repeated the above on a WS-C3750X-24P-E 12.2(58)SE2 with the same results.
Thanks
Andy
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-01-2018 07:51 AM
I realize that this is an old post, but I'm looking into deploying uRPF on SVIs and saw this. There are a few courses I can recommend. First, sniff the traffic on the laptop. Check to see if the packets you think you are generating are actually crafted in the manner that you expect. Check to see what the destination MAC address is, and if it belongs to the SVI interface VLAN 10. If it doesn't, then the SVI will not receive the traffic. Next, try debug ip packet. This is extremely verbose, so don't ever try this on production equipment. You might find some useful output. Finally, although most likely redundant, try spanning the incoming traffic from the laptop's connected switch port and sniff the traffic. This obviously doesn't answer your question, though it should provide you with the tools to answer it yourself. Of course, the 3850 switch is the buggiest Cisco device I've ever worked with, so make sure you're running the latest recommended code. Cheers!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide