- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Anyconnect Error - Cryptographic algorithms required by the secure gateway do not match those s...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
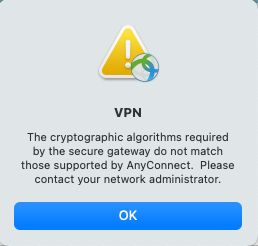
Anyconnect Error - Cryptographic algorithms required by the secure gateway do not match those supported by AnyConnect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 08:34 AM
Hi,
We upgraded our AnyConnect image to (anyconnect-win-4.9.01095-webdeploy-k9.pkg) version now we are receiving the Cryptographic algorithms required by the secure gateway do not match those supported by AnyConnect error. Can anyone assist with this error? It would be greatly appreciated. I posted the policy and tunnel groups info for review.
WFC-COT-ASA-1# sh run group-policy
group-policy GroupPolicy_x.x.x.x internal
group-policy GroupPolicy_x.x.x.x attributes
vpn-tunnel-protocol ikev1
group-policy GroupPolicy_WFC_Anyconnect internal
group-policy GroupPolicy_WFC_Anyconnect attributes
wins-server none
dns-server value x.x.x.x x.x.x.x
vpn-tunnel-protocol ikev2 ssl-client
default-domain value wwad.wilwoodclinic.com
client-bypass-protocol enable
webvpn
anyconnect profiles value WFC_Anyconnect_client_profile type user
WFC-COT-ASA-1# sh run tunnel-group
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
tunnel-group WFC_Anyconnect type remote-access
tunnel-group WFC_Anyconnect general-attributes
authentication-server-group LDAP LOCAL
default-group-policy GroupPolicy_WFC_Anyconnect
dhcp-server link-selection x.x.x.x
tunnel-group WFC_Anyconnect webvpn-attributes
group-alias WFC_Anyconnect enable
--------------------------------------------------------------------------------------------------------
WFC-MAD-ASA-1# sh run group-policy
group-policy GroupPolicy_x.x.x.x internal
group-policy GroupPolicy_x.x.x.x attributes
vpn-tunnel-protocol ikev1
group-policy GroupPolicy_x.x.x.x internal
group-policy GroupPolicy_x.x.x.x attributes
vpn-tunnel-protocol ikev1
group-policy GroupPolicy_WFC_Anyconnect internal
group-policy GroupPolicy_WFC_Anyconnect attributes
wins-server none
dns-server value x.x.x.x x.x.x.x
vpn-tunnel-protocol ikev2 ssl-client
default-domain value wwad.wildwoodclinic.com
client-bypass-protocol enable
webvpn
anyconnect profiles value WFC_Anyconnect_client_profile type user
WFC-MAD-ASA-1# sh run tunnel-group
tunnel-group WFC_Anyconnect type remote-access
tunnel-group WFC_Anyconnect general-attributes
authentication-server-group LDAP LOCAL
default-group-policy GroupPolicy_WFC_Anyconnect
dhcp-server link-selection x.x.x.x
tunnel-group WFC_Anyconnect webvpn-attributes
group-alias WFC_Anyconnect enable
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
- Labels:
-
AnyConnect
-
IPSEC
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 08:41 AM - edited 08-26-2020 08:42 AM
Hi,
Unfortunately that does not tell us what algorithms you are using.
Are you using IPSec or SSL?
In AnyConnect 4.9 the follow changes were made:-
-
For SSL VPN, AnyConnect no longer supports the following cipher suites from both TLS and DTLS: DHE-RSA-AES256-SHA and DES-CBC3-SHA
-
For IKEv2/IPsec, AnyConnect no longer supports the following algorithms:
-
Encryption algorithms: DES and 3DES
-
Pseudo Random Function (PRF) algorithm: MD5
-
Integrity algorithm: MD5
-
Diffie-Hellman (DH) groups: 2, 5, 14, 24
-
If you are using any of the above algorithms I suggest you modify your configuration accordingly.
If you need further assistance, provide the output of "show run crypto" and "show run ssl"
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 09:36 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-26-2020 09:56 AM - edited 08-26-2020 11:09 AM
Are you using IPSec or SSL for Remote Access VPN?
You are using TLS1.2 so that using the more secure algorithms, you should consider modify your SSL dh-group to use group 14, instead of group 5.
WFC-COT-ASA-1# sh run ssl
ssl dh-group group5
Your IKEv1/IKEv2 Policies are also using depreciated algorithms. You'd probably want to amend your IKE Policies, remove DES, 3DES, DH group 2, 5 etc and use AES, DH Group 19, 20 or 21. Be careful if these IKE policies are used for S2S VPN's aswell as RAVPN.
crypto ikev2 policy 1
encryption aes-256
integrity sha
group 5
prf sha
lifetime seconds 86400
crypto ikev2 policy 10
encryption aes-192
integrity sha
group 5
prf sha
lifetime seconds 86400
crypto iev2 policy 30
encryption 3des
integrity sha
group 5
prf sha
crypto ikev2 policy 40
encryption des
integrity sha
group 5
prf sha
lifetime seconds 86400
crypto ikev1 policy 100
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 110
authentication rsa-sig
encryption 3des
hash sha
group 2
lifetime 86400
Alternatively you could create a new more secure IKEv2 Policy (see below), however you will need to delete the existing IKEv2 Policy #1 and re-add using a number greater than the new policy, e.g 6. This ensures that the RAVPN users can connect using the new policy and existing S2s VPN can also still connect using the older policies.
crypto ikev2 policy 5
encryption aes-gcm
integrity null
group 19
prf sha256
You may need/want to upgrade your ASA version depending on what you are currently running. In 9.13 those algorithms have been depreciated. https://www.cisco.com/c/en/us/td/docs/security/asa/asa913/release/notes/asarn913.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2020 06:50 AM
thanks.. that was the solution:
crypto ikev2 policy 5
encryption aes-gcm
integrity null
group 19
prf sha256
Anyconnect on iPhone works again..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2021 11:44 AM
Hi, on cisco anyconnect 4.10, we had the same error. We correct the dh group, but we have the next problem: the gw vpn is added with profile editor on server list, with a display name, fqdn and group. But when it try to connect the error appear again. If I put manually the fqdn on the client, then connect.. do you know why?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2021 12:01 PM
We are running on a Mac with OS 10.15.7. We don't have the commands 'show run crypto' or 'show run ssl' available in the terminal. We also don't have control of the algorithms, since they come with the OS. How can we get something that will run with 4.9?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2021 08:02 PM
@IntellexRSK those commands are to be used on the ASA headend - not on the client AnyConnect or terminal.
FYI Mac OS 10.15.7 (Catalina) or 11.x (Big Sur) clients should use the latest AnyConnect version - currently 4.9.06037 - for best compatibility, especially with Big Sur.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2021 08:32 PM
We're using 4.9.0403, which is the latest version the school has on their installer, but it's giving us this crypto error when we try to log in. I can't figure out what ssl it wants or how I can upgrade to it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2021 12:53 AM
As noted, the crypto settings that cause this error are on the ASA - not anywhere on the client. The administrator of the ASA needs to fix the issue. There is nothing you can do from the client side to remedy the problem.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2021 12:00 PM
So Why does this only happen on some clients I have 40 clients and only 3 are having this issue? All are windows 10, is there version of windows 10 that does not have the requried algorithms?
Thanks
Scott
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2021 07:00 AM
I had this same issue. What I found was that it was an issue on the client with the AnyConnect profile file.
After upgrading the client, AnyConnect would come up with the connection as something like "MARS-5506X (Ipsec) IPV4" (at which time it did not prompt to accept the SSL cert), which was a stored profile.
I went back and entered just the IP address for the connection, it prompted me for the SSL cert, I accepted and the error went away.
So, looks like it is something that is being stored in the local XML profile file (c:\ProgramData\Cisco\Cisco AnyConnect Secure Mobility Client\Profile)
Hope that helps.
John
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-13-2022 10:51 AM
I am using a MacBook Pro with macOS Monterrey Version 12.6
I was only receiving the error from this client and could always connect from other devices, Win10, iPhone and iPad.
The solution was to remove this line from the profile
<PrimaryProtocol>IPsec</PrimaryProtocol>
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide