- Cisco Community
- Technology and Support
- Security
- VPN
- Re: AnyConnect VPN SSO with Cisco ISE and Firepower
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-11-2020 11:08 PM - edited 02-21-2020 09:51 PM
Hi,
We are designing a VPN infrastructure as 2 connection profile; one for employees and the other for VIP users. We have Firepower as RA VPN device and Cisco ISE for AAA and posture. We are deploying the connection profile created by VPN policy editor.
For employee; We have a connection profile on Firepower designes as Client Certificate & AAA. We are using 2FA and it is configured on ISE. And also we are checking posture on ISE. Everything for employee is working.
For VIP users; it is desired to make VPN connection on untrusted network automatically. But it is also desired posture check for VIP users so that i could not choose only certificate authenticaton on Firepower RA VPN configuration. On ISE i configured the auth policy as check only certificate for VIP user (by checking cisco av-pair mac address attribute) but AnyConnect VPN client still prompts username and password.
AnyConnect does not support SSO so that how can i achieve this configuration for VIP users' VPN connection ?
Thanks,
Solved! Go to Solution.
- Labels:
-
AnyConnect
-
Other VPN Topics
-
Remote Access
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2020 01:32 AM
If you still have issue please provide screenshots of your configuration and ISE log error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 01:17 AM
To achieve SSO for the VIP users you should be able to configure "client certificate only" authentication on the VIP connection profile. Authentication will be between the client and the FTD only, you can pass Authorization onto ISE. The VIP must have a user certificate that the FTD trusts in order to successfully authenticate the user.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:09 AM
By this way, i think i need to create one more connection profile on ftd because it is desired that employee types their username and password with 2FA.
If i need to create one more connection profile how can i deploy it by VPN profile editor. It is not wanted to use alias and I did not see any field on VPN profile editor about connection profile.
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 02:16 AM
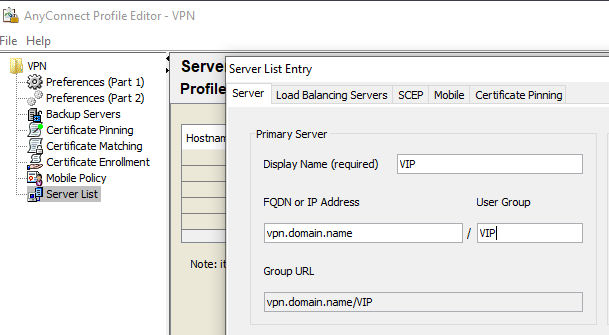
When you create a Server List entry using the VPN Profile Editor, you would define the "User Group" which is the name of the Connection Profile. E.g:-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2020 09:47 PM
Hi RJI,
Thanks for your contribution, now the radius requests are accessing to ISE. But now we have some problems on ISE. ISE says that auth failed because we are using cert based authenticaton on ISE. We are derivering username field from cert on ftd and sent it to ISE. But ise says that auth failed i have tried both cert based auth and password based on ISE.
When cert based ISE says ; "Check the appropriate configuration in Policy > Authentication. This error happens when the identity source is configured for certificate based and received a password based authentication request."
When not cert based and lookup user only DC, ISE says ; the username is invalid.
I have achieved this by configuring the authenticaton policy as if auth fails continue, and created a new authorization policy for check only radius username derived from cert,but now authorization policy hits default policy and deny access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2020 01:32 AM
If you still have issue please provide screenshots of your configuration and ISE log error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2020 09:40 AM
Hi RJI,
Yes, done, successfull, i have created another radius with same ISE noded for related connection profile. thanks for your contribution again, i need to say that for user group at connection profile i have added URL for related connection profile, now everything is working with success. The only thing sometimes, when wifi connection down on untrusted network anyconnect gives an error as ; "The secure gateway has rejected the connection attempt. A new connection attempt to the same or another secure gateway is needed, which requires re-authentication. The following message was received from the secure gateway: No assigned address" and i need to logoff the session on ftd when this error happens.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide