- Cisco Community
- Technology and Support
- Security
- VPN
- asa 5520 ver 8.0(4) vpn client on stick access to site 2 site networks
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
asa 5520 ver 8.0(4) vpn client on stick access to site 2 site networks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2012 11:50 PM
Greetings
I have asa 5520 ver 8.0(4)
I have vpn client access created and working
I have l2l vpn created and working with another set of asa
The issue at hand
VPN client from internet connects and authenticates, this client can access Site A's networks with no problems. However vpn client on Site A ASA can not access Networks through l2l tunnel located at Site B.
full example here
Site A config:
outside interface x.x.x.x
TTHGCVPN interface y.y.y.y
access-list splitter standard permit 10.1.0.0 255.255.0.0
access-list tt2rb_vpn extended permit ip 10.2.0.0 255.255.0.0 10.1.0.0 255.255.0.0
access-list tt2rb_vpn extended permit ip 192.168.2.0 255.255.254.0 10.1.0.0 255.255.0.0
access-list nonat extended permit ip 10.2.0.0 255.255.0.0 10.1.0.0 255.255.0.0
access-list nonat extended permit ip 192.168.2.0 255.255.254.0 10.1.0.0 255.255.0.0
ip local pool ttvpndhcp 192.168.2.5-192.168.3.254 mask 255.255.254.0
global (outside) 101 interface
nat (outside) 101 192.168.2.0 255.255.254.0
nat (inside) 0 access-list nonat
nat (inside) 101 0.0.0.0 0.0.0.0
route outside 0.0.0.0 0.0.0.0 x.x.x.x 1
route TTHGCVPN 10.1.0.0 255.255.0.0 y.y.y.y
route inside 10.2.0.0 255.255.0.0 z.z.z.z 1
crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec transform-set myset esp-3des esp-sha-hmac
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set pfs
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set security-association lifetime seconds 28800
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set security-association lifetime kilobytes 4608000
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto map IPSec_map 5 match address tt2rb_vpn
crypto map IPSec_map 5 set peer x.x.x.x
crypto map IPSec_map 5 set transform-set myset
crypto map IPSec_map 5 set security-association lifetime seconds 28800
crypto map IPSec_map 5 set security-association lifetime kilobytes 4608000
crypto map IPSec_map interface TTHGCVPN
crypto isakmp enable outside
crypto isakmp enable TTHGCVPN
crypto isakmp policy 5
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
group-policy vpnldap attributes
dns-server value 10.2.x.x 10.2.x.x
ipsec-udp enable
split-tunnel-policy tunnelspecified
split-tunnel-network-list value splitter
default-domain value blah blah blah
address-pools value ttvpndhcp
tunnel-group vpnldap general-attributes
address-pool ttvpndhcp
authentication-server-group LDAP1
default-group-policy vpnldap
tunnel-group vpnldap ipsec-attributes
pre-shared-key *
isakmp keepalive threshold 60 retry 2
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x ipsec-attributes
pre-shared-key *
isakmp keepalive threshold 60 retry 2
same-security-traffic permit intra-interface
when these are applied it slows access to internet and internal resources at Site A - Site B resources are unreachable
split-tunnel-policy tunnelspecified
split-tunnel-network-list value splitter
without the split-tunnel site vpn clients are fast to internet and site A internal resources - but unable to access Site B resources
SITE B Config:
access-list rb2tt_vpn extended permit ip 10.1.0.0 255.255.0.0 10.2.0.0 255.255.0.0
access-list rb2tt_vpn extended permit ip 10.1.0.0 255.255.0.0 192.168.2.0 255.255.254.0
access-list nonat extended permit ip 10.1.0.0 255.255.0.0 10.2.0.0 255.255.0.0
access-list nonat extended permit ip 10.1.0.0 255.255.0.0 192.168.2.0 255.255.254.0
nat (inside) 0 access-list nonat
nat (inside) 101 0.0.0.0 0.0.0.0
route RBHGCVPN 10.2.0.0 255.255.0.0 x.x.x.x 1
crypto ipsec transform-set myset esp-3des esp-sha-hmac
crypto map IPSec_map 5 match address rb2tt_vpn
crypto map IPSec_map 5 set peer x.x.x.x
crypto map IPSec_map 5 set transform-set myset
crypto map IPSec_map 5 set security-association lifetime seconds 28800
crypto map IPSec_map 5 set security-association lifetime kilobytes 4608000
crypto map IPSec_map 20 set security-association lifetime seconds 28800
crypto map IPSec_map 20 set security-association lifetime kilobytes 4608000
crypto map IPSec_map interface RBHGCVPN
crypto isakmp enable outside
crypto isakmp enable RBHGCVPN
crypto isakmp policy 5
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group x.x.x.x ipsec-attributes
pre-shared-key *
isakmp keepalive threshold 60 retry 2
same-security-traffic permit intra-interface
Any thoughts or insights would be appreciated
Cheers
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2012 06:57 PM
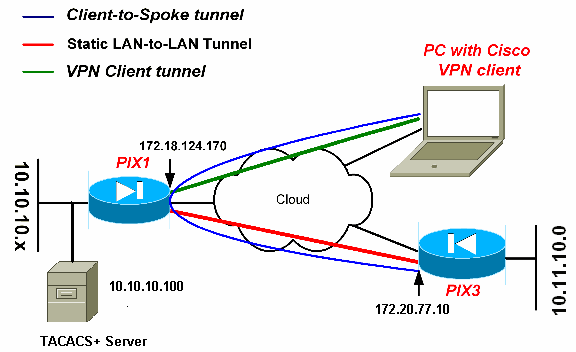
The client connects to Site A via dynamic VPN on the outside interface.
After Auth
the client can reach Site A resources and has Internet access.
The Client can not access internal resources at Site B
This is kind of like a hairpin, except I have a second internet interface same security as outside that is being used for the L2L connections between Site A and Site B
all L2L traffic works
vpn client - internet works
vpn client - Site A internal resources work.
vpn client access to Site B fails
syslog error
Mar 19 09:14:44 10.1.5.1 Jan 18 2003 23:31:10: %ASA-3-305006: portmap translation creation failed for icmp src outside:192.168.4.5 dst L2LVPN:10.2.10.1 (type 8, code 0)
I have created an acl for nonatclient and applied to the L2LVPN interface on both sides
have a route pointing to the far side and have interesting traffic defined.
the traffic does not seem to leave the Site A ASA
looks like a NAT issue

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2012 07:44 PM
Ok I have made some progress.
I applied nonat acl to outside interface for the vpn client ip range and the 2nd interface
traffic seems to flow now
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide