- Cisco Community
- Technology and Support
- Security
- VPN
- DMVPN tunnel sourced via loopback error
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
DMVPN tunnel sourced via loopback error
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-23-2012 02:25 AM - edited 02-21-2020 06:30 PM
Hi all,
I am having a hard time trying to configure DMVPN with the tunnel being sourced via a loopback interface. (Hoping someone could help me out)
I have the following network topology:
R1 <----------> R3 <---------> R2
(Hub) (ISP router) (Spoke)
All routers are Cisco 886 routers which don't have L3 ports.
That is why I used SVI interfaces, and have configured the L2 ports (Fa0, Fa1, etc.) with the command switchport access vlan *
I have used this website as an example http://www.securityie.com/cgi-bin/ultimatebb.cgi?ubb=get_topic;f=10;t=002092
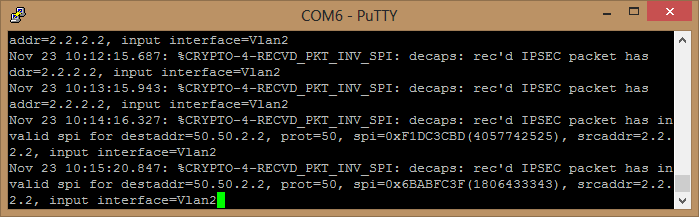
The problem is that I am receiving Invalid SPI error's only on the Hub router and I have no clue what could be the problem, because they use exactly the same parameters for IPsec.
Please find my configurations below.
I hope someone could help me out with this, any help will be very much appreciated.
Kind regards,
Dwayne
R1: Hub router:
R1#show run
Building configuration...
Current configuration : 2109 bytes
!
! Last configuration change at 10:08:31 UTC Fri Nov 23 2012
version 15.1
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Hub1
!
boot-start-marker
boot-end-marker
!
!
no aaa new-model
!
memory-size iomem 10
crypto pki token default removal timeout 0
!
!
ip source-route
!
!
ip cef
no ipv6 cef
!
!
multilink bundle-name authenticated
license udi pid CISCO886VA-SEC-K9 sn FCZ1636C0RU
!
!
controller VDSL 0
!
!
crypto isakmp policy 10
encr aes
authentication pre-share
group 5
crypto isakmp key cisco address 0.0.0.0 0.0.0.0
crypto isakmp invalid-spi-recovery
crypto isakmp keepalive 10 periodic
!
!
crypto ipsec transform-set MYSET esp-aes esp-sha-hmac
mode transport
!
crypto ipsec profile dmvpn
set transform-set MYSET
set pfs group5
!
interface Tunnel0
description DMVPN HUB INTERFACE
bandwidth 1000
ip address 192.168.1.2 255.255.255.0
no ip redirects
ip mtu 1416
ip nhrp authentication cisco
ip nhrp map multicast dynamic
ip nhrp network-id 1
ip tcp adjust-mss 1352
no ip split-horizon eigrp 10
tunnel source 50.50.2.2
tunnel mode gre multipoint
tunnel key 1
tunnel protection ipsec profile dmvpn
!
!
interface FastEthernet0
switchport access vlan 2
no ip address
!
interface FastEthernet1
switchport access vlan 3
no ip address
!
!
interface Vlan2
description HUB'S PUBLIC LAN
ip address 50.50.2.2 255.255.255.0
!
interface Vlan3
description HUB'S PRIVATE LAN
ip address 10.1.1.1 255.255.255.0
!
!
router eigrp 10
network 10.1.1.0 0.0.0.255
network 192.168.1.0
!
ip forward-protocol nd
no ip http server
no ip http secure-server
!
!
ip route 50.50.1.2 255.255.255.255 50.50.2.1
!
!
control-plane
!
!
line con 0
line aux 0
line vty 0 4
login
transport input all
!
end
----------------------------------------------------------------------
----------------------------------------------------------------------
R2: Spoke router:
R2#show run
Building configuration...
Current configuration : 2594 bytes
!
! Last configuration change at 10:10:06 UTC Fri Nov 23 2012
version 15.1
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Spoke
!
boot-start-marker
boot-end-marker
!
!
no aaa new-model
!
memory-size iomem 10
crypto pki token default removal timeout 0
!
!
ip source-route
!
!
ip cef
no ipv6 cef
!
!
multilink bundle-name authenticated
license udi pid CISCO887VA-SEC-K9 sn FCZ1637913G
!
!
controller VDSL 0
!
!
crypto isakmp policy 10
encr aes
authentication pre-share
group 5
crypto isakmp key cisco address 0.0.0.0 0.0.0.0
crypto isakmp invalid-spi-recovery
crypto isakmp keepalive 10 periodic
!
!
crypto ipsec transform-set MYSET esp-aes esp-sha-hmac
mode transport
!
crypto ipsec profile dmvpn
set transform-set MYSET
set pfs group5
!
!
interface Loopback0
description DMVPN TUNNEL SOURCE
ip address 2.2.2.2 255.255.255.0
ip nat inside
ip virtual-reassembly in
!
interface Tunnel0
description DMVPN SPOKE INTERFACE
bandwidth 1000
ip address 192.168.1.1 255.255.255.0
no ip redirects
ip mtu 1416
ip nhrp authentication cisco
ip nhrp map multicast 50.50.2.2
ip nhrp map 192.168.1.2 50.50.2.2
ip nhrp network-id 1
ip nhrp nhs 192.168.1.2
ip tcp adjust-mss 1352
tunnel source 2.2.2.2
tunnel mode gre multipoint
tunnel key 1
tunnel protection ipsec profile dmvpn
!
!
interface FastEthernet0
switchport access vlan 4
no ip address
!
interface FastEthernet1
switchport access vlan 3
no ip address
!
!
interface Vlan1
no ip address
!
interface Vlan3
description SPOKE'S PRIVATE LAN
ip address 172.168.1.1 255.255.255.0
ip nat inside
ip virtual-reassembly in
!
interface Vlan4
description SPOKE'S PUBLIC LAN
ip address 50.50.1.2 255.255.255.0
ip nat outside
ip virtual-reassembly in
no ip route-cache
!
!
router eigrp 10
network 172.168.1.0 0.0.0.255
network 192.168.0.0 0.0.255.255
!
ip forward-protocol nd
no ip http server
no ip http secure-server
!
!
ip nat inside source list pat interface Vlan4 overload
ip route 50.50.2.2 255.255.255.255 50.50.1.1
!
ip access-list extended pat
permit ip host 2.2.2.2 any
permit gre host 2.2.2.2 any
deny ip any 50.50.0.0 0.0.255.255
deny ip any 192.168.0.0 0.0.255.255
permit ip 172.168.1.0 0.0.0.255 any
!
!
control-plane
!
!
line con 0
line aux 0
line vty 0 4
login
transport input all
!
end
- Labels:
-
DMVPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-23-2012 03:57 AM
Also when I issue the command show crypto isakmp sa detail, it shows the following output.
Strange thing is when I issue the command a few times, the SA state changes (see below).
This is the same on both the hub and the spoke router.

Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide