- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Multiple IPsec tunnel
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Multiple IPsec tunnel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 12:15 AM - edited 01-20-2021 02:34 AM
Hi Everyone,
I have a question about using multiple IPsec tunnel.
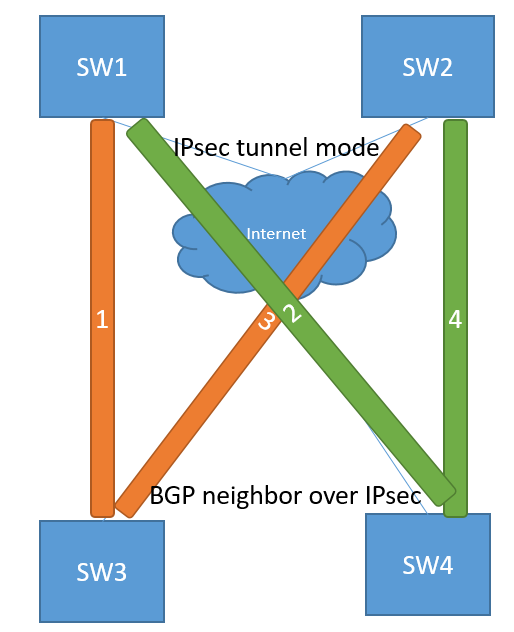
Below is a simple diagram that I think to implement.
1. I have 2 sites connecting over internet. I want to connect them with IPsec tunnel. (not use GRE or VTI tunnel)
2. I peer them with 4 tunnels as shown.
3. I use BGP routing which is forming neighbor over IPsec tunnel and I control BGP metric to redundant the tunnels.
4. All the IPsec tunnel have the same acl configured the same interest traffic.
My question is it possible to do that?
I'm not sure how it is working behind multiple IPsec tunnel like this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 12:21 AM
What hardware are you implementing this on? ASA, FTD or IOS-XE router?
If you wish to establish a BGP adjacency between peers you'd need to use a tunnel interface (route based VPN) not a crypto map (policy based VPN).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 12:45 AM - edited 01-20-2021 02:35 AM
I use cisco WS-C3650-24TS for SW1 and SW2 and SW3 and SW4 are switch in cloud.
The C3650 also has limitation configured tunnel interface because of I have only ipservice license. So that seems route-base vpn cannot be used.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 12:54 AM
IPSec is not supported on 3850
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvc07091/?rfs=iqvred
I suggest you purchase the right hardware for this scenario, either a firewall or a router.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 01:00 AM
Hi Rob,
This is also WS-C3650-24TS? I see the bug mensioned only 3850.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2021 01:28 AM
More than likely yes, I believe the 3850/3650 share the same code. Unfortunately the switches had the syntax to enter a lot of commands the hardware didn't actually support. I've never seen a document or guide from cisco on using a VPN on a switch, so use a router or a firewall.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide