- Cisco Community
- Technology and Support
- Security
- VPN
- Re: PPTP VPN passing through Cisco 1921
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
PPTP VPN passing through Cisco 1921
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 03:34 AM
I hope this is the correct location to post this...I am not using AnyConnect, but this is VPN related.
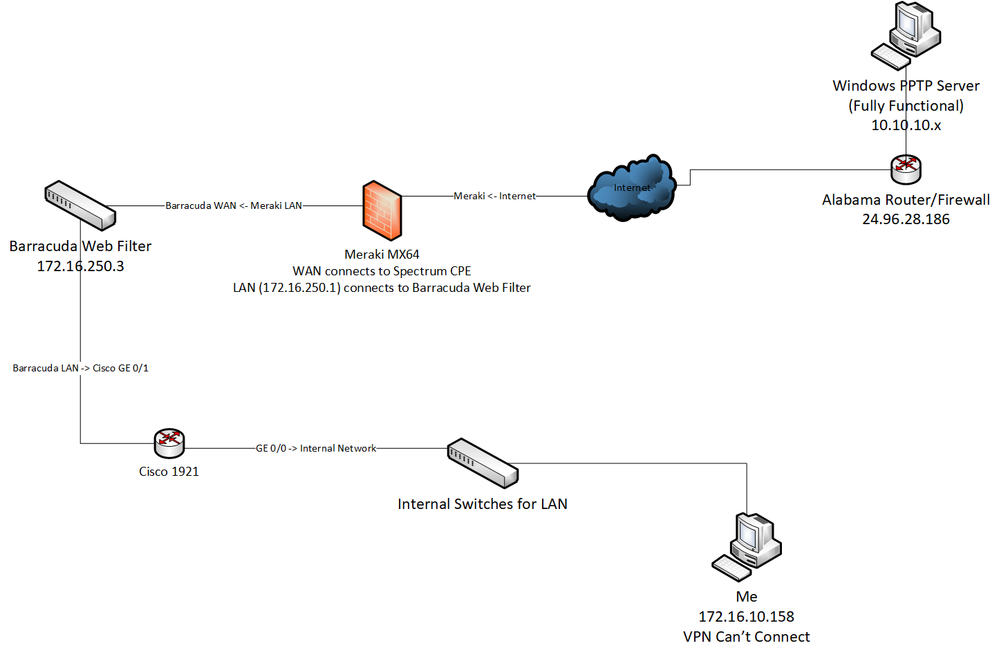
I have a Spectrum Business Fiber connection at my office. The first device in my network after the Spectrum CPE is a Cisco 1921. The Cisco config is nothing spectacular (I'll post the config below). After the Cisco is a Barracuda Web Filter, followed by a Meraki MX64 which feeds all of my internal switches and such.
We recently merged with a company in Alabama which has Windows PPTP VPN server. That PPTP server is fully functional, and I can connect to it from my house in Wisconsin without issue.
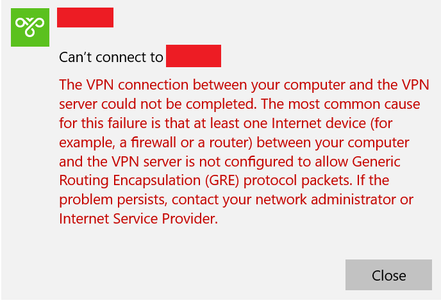
The issue I am having is as follows: While at my office in Wisconsin, I am unable to connect to the PPTP VPN in Alabama. I am using the same laptop at home and the Wisconsin office, so I can rule out that out as an issue. When I am at the Wisconsin office and I try to connect to the VPN, this is the error that I eventually see:
I am not sure what is causing this, but both Spectrum and Meraki are saying that it most likely has something to do with the Cisco 1921 that is in place. Looking at the configuration, I realize that I am a bit out of my depth of knowledge, so I thought I would reach out here to see if anyone can possibly see what may be causing the issue.
My computer at the office is wired into the network, it is not on WiFi. My internal IP is 172.16.10.x
Here is the configuration for my Cisco 1921:
Using 4635 out of 262136 bytes
!
! Last configuration change at 10:47:12 CDT Tue Sep 4 2018 by jhecker
! NVRAM config last updated at 10:47:13 CDT Tue Sep 4 2018 by jhecker
! NVRAM config last updated at 10:47:13 CDT Tue Sep 4 2018 by jhecker
version 15.2
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname CiscoRouter
!
boot-start-marker
boot-end-marker
!
!
logging buffered 51200 warnings
enable secret 5 ******************************
!
aaa new-model
!
!
aaa authentication login default local
aaa authorization exec default local
!
!
!
!
!
aaa session-id common
clock timezone CST -6 0
clock summer-time CDT recurring
!
ip cef
!
!
!
!
!
!
no ip domain lookup
ip domain name yourdomain.com
no ipv6 cef
multilink bundle-name authenticated
!
!
crypto pki trustpoint TP-self-signed-668782424
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-668782424
revocation-check none
rsakeypair TP-self-signed-668782424
!
!
crypto pki certificate chain TP-self-signed-668782424
certificate self-signed 01 nvram:IOS-Self-Sig#1.cer
license udi pid CISCO1921/K9 sn FTX181583CQ
!
!
file privilege 0
username ******** privilege 15 secret 5 ******************************
username ******* privilege 15 password 0 ***********
username ***** privilege 15 view enduserview password 0 ***********
!
!
!
!
!
!
interface Embedded-Service-Engine0/0
no ip address
shutdown
!
interface GigabitEthernet0/0
description *** Trunk to Inside Network ***
no ip address
duplex auto
speed auto
!
interface GigabitEthernet0/0.1
description Management VLAN 1 - Native VLAN
encapsulation dot1Q 1 native
ip address 172.16.1.1 255.255.255.0
!
interface GigabitEthernet0/0.10
description *** LAN VLAN ***
encapsulation dot1Q 10
ip address 172.16.10.1 255.255.254.0
ip helper-address 172.16.20.0
ip helper-address 172.16.11.0
!
interface GigabitEthernet0/0.20
description *** Wireless LAN VLAN ***
encapsulation dot1Q 20
ip address 172.16.20.1 255.255.255.0
ip helper-address 172.16.10.0
ip helper-address 172.16.10.10
ip helper-address 172.16.11.0
!
interface GigabitEthernet0/1
description *** Link to ASA Fa0/1 ***
ip address 172.16.250.2 255.255.255.248
duplex auto
speed auto
!
!
router eigrp 10
network 172.16.0.0
!
ip forward-protocol nd
!
ip http server
ip http authentication local
ip http secure-server
ip http timeout-policy idle 60 life 86400 requests 10000
!
ip route 0.0.0.0 0.0.0.0 172.16.250.1
ip route 192.168.1.0 255.255.255.0 172.16.250.1
!
!
!
!
!
!
control-plane
!
!
banner exec ^CC
---------------------------------------------------------------------------------------
!!! Authorized Access Only !!!
---------------------------------------------------------------------------------------
^C
banner login ^CC
---------------------------------------------------------------------------------------
!!! Authorized Access Only !!!
---------------------------------------------------------------------------------------
^C
parser view enduserview
secret 5 ******************************
commands interface include switchport
commands configure include cns trusted-server
commands configure include cns
commands configure include scheduler max-task-time
commands configure include scheduler
commands exec include dir all-filesystems
commands exec include dir
commands exec include write memory
commands exec include write
commands exec include configure terminal
commands exec include configure
commands exec include show ip interface brief
commands exec include show ip interface
commands exec include show ip
commands exec include show diag
commands exec include show version
commands exec include show running-config
commands exec include show interfaces
commands exec include show
!
!
line con 0
exec-timeout 120 0
password **********
logging synchronous
line aux 0
password **********
line 2
no activation-character
no exec
transport preferred none
transport output pad telnet rlogin lapb-ta mop udptn v120 ssh
stopbits 1
line vty 0 4
access-class 23 in
privilege level 15
password **********
transport input telnet ssh
line vty 5 15
access-class 23 in
privilege level 15
transport input telnet ssh
!
scheduler max-task-time 5000
scheduler allocate 20000 1000
ntp server 172.16.10.10
cns trusted-server all-agents yourname
!
end
Does it look like something in the Cisco configuration may be the issue, or do I need to continue looking elsewhere?
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 06:59 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 07:28 AM
You are correct. That diagram was inaccurate. Thank you for pointing that out. Here is the correct diagram. (I went and physically looked at it this time, rather than trying to do it from memory)
I spoke to Barracuda, and they stated that the Web Filter is only looking at HTTP/HTTPS traffic, allowing all other traffic to pass through it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 07:35 AM
Also what interface was the packet capture on the meraki performed on? inside or outside interface? If it was the outside interface could it have been blocked by the meraki and therefore not appear on the outside interface capture?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 07:42 AM
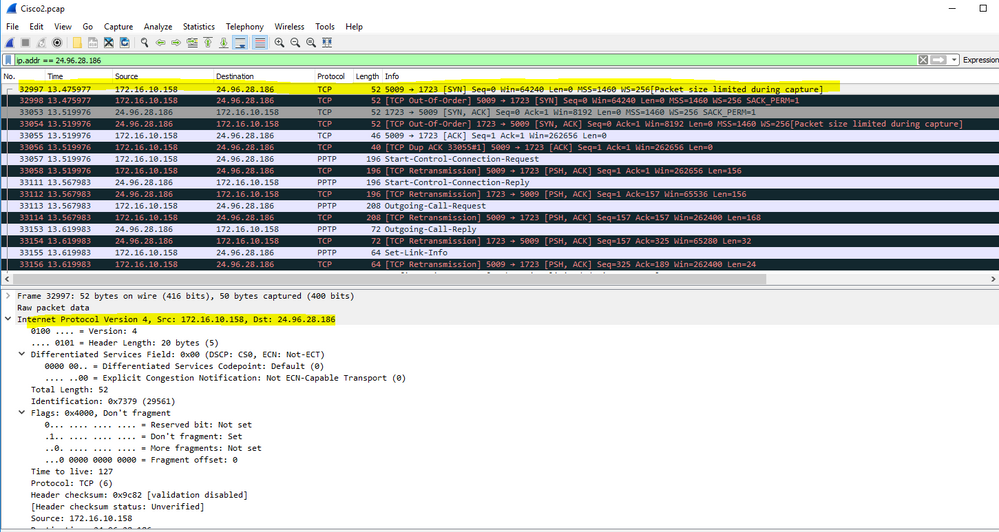
curious if maraki have similar command like ASA to capture the packet. RJI is right. i can see the packet on cisco capture the pc 172.16.10.158 port 5009 dest 24.96.28.186 port 1723 doing syn but no ack-syn.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 07:43 AM
curious if maraki have similar command like ASA to capture the packet. RJI is right. i can see the packet on cisco capture the pc 172.16.10.158 port 5009 dest 24.96.28.186 port 1723 doing syn but no ack-syn.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 07:55 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2019 10:19 AM
Can you take a packet capture on the Alabama router/firewall?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2019 09:17 AM
My apologies for the delayed response. I took a packet capture from the Watchguard device in Alabama, and have attached it here. I did filter it first, as it was 1.3gb for 90 seconds of traffic...so I filtered it so it only has the traffic to/from my IP here in Wisconsin.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2019 09:19 AM
Is this for RJI only or other can see too?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2019 09:21 AM
@Sheraz.Salim by all means, have at it. I've been struggling with this for far too long. The more eyes, the better :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2019 09:33 AM - edited 01-10-2019 09:48 AM
I was joking no offense to you and to RJI.
ok i see the packet capture. 74.62.103.218 is a Alcatel device communicate to 24.96.28.186 which is your remote router. looking at the traffic pattern all they communication is TLS.
looking for into this will get back
update. do you have any more packet capture here is not much speacail only tls traffic between those two above ip addresses.
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide