- Cisco Community
- Technology and Support
- Security
- VPN
- ssl anyconnect authen acs5.0 fail
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ssl anyconnect authen acs5.0 fail
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2011 04:05 AM - edited 02-21-2020 05:14 PM
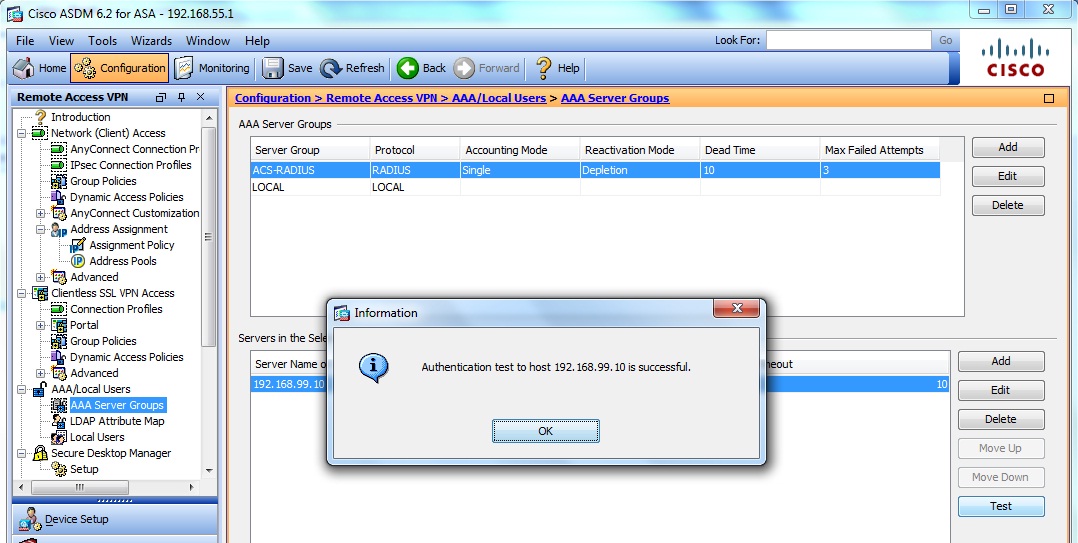
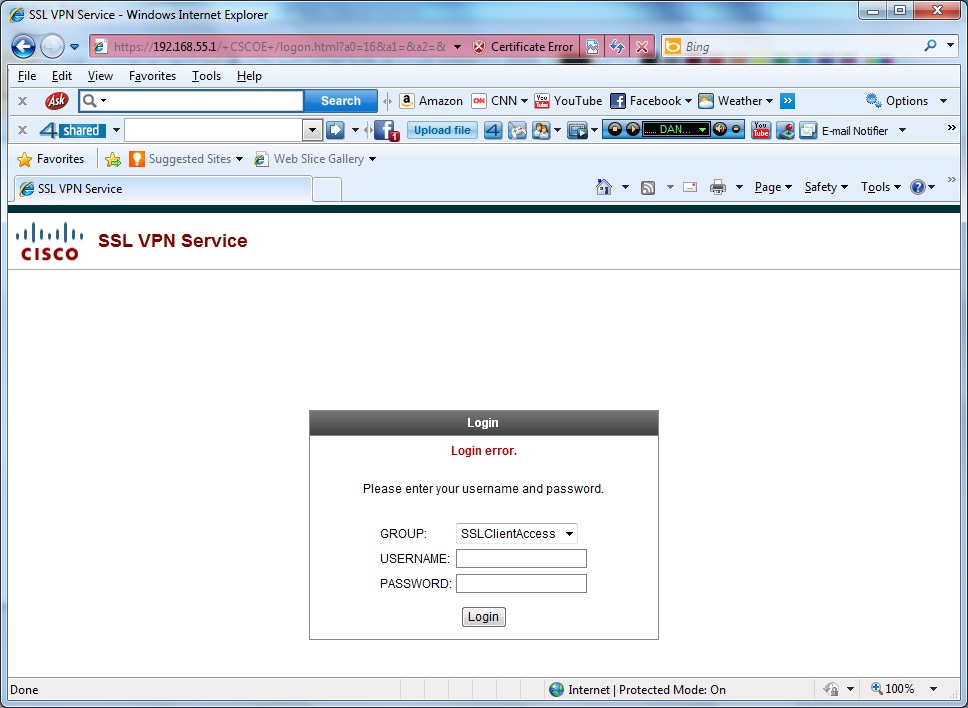
I creat ssl anyconnect authen acs5.0 when i create aaa server group on asa5520 and test command it can authen success but when i open browser and enter username and password can not authen it show login error help me please
ASA Version 8.2(2)
!
hostname ASA5520
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address 192.168.55.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 192.168.99.20 255.255.255.0
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
no ip address
!
<--- More --->
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
boot system disk0:/asa822-k8.bin
ftp mode passive
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
access-list inside_nat0_outbound extended permit ip 192.168.99.0 255.255.255.0 any
pager lines 24
mtu outside 1500
mtu inside 1500
ip local pool SSLPOOL1 192.168.66.1-192.168.66.10 mask 255.255.255.0
no failover
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-625-53.bin
<--- More --->
no asdm history enable
arp timeout 14400
nat (inside) 0 access-list inside_nat0_outbound
route outside 0.0.0.0 0.0.0.0 192.168.55.2 1
route outside 192.168.33.0 255.255.255.0 192.168.55.2 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
aaa-server ACS-RADIUS protocol radius
aaa-server ACS-RADIUS (inside) host 192.168.99.10
key *****
radius-common-pw *****
http server enable
http 0.0.0.0 0.0.0.0 inside
http 0.0.0.0 0.0.0.0 outside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
<--- More --->
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
enable outside
svc image disk0:/anyconnect-win-2.4.0202-k9.pkg 1
svc enable
tunnel-group-list enable
group-policy SSLGP1 internal
group-policy SSLGP1 attributes
vpn-tunnel-protocol svc
address-pools value SSLPOOL1
group-policy DfltGrpPolicy attributes
vpn-tunnel-protocol IPSec l2tp-ipsec svc webvpn
tunnel-group SSLTG1 type remote-access
tunnel-group SSLTG1 general-attributes
address-pool SSLPOOL1
authentication-server-group ACS-RADIUS
authorization-server-group ACS-RADIUS
default-group-policy SSLGP1
tunnel-group SSLTG1 webvpn-attributes
<--- More --->
group-alias SSLClientAccess enable
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
<--- More --->
inspect sip
inspect xdmcp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:d58d92639c70e39cea3b9645966d4fa8
: end
ASA5520(config)#
- Labels:
-
AnyConnect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2011 04:17 AM
Hi,
Please obtain 'debug aaa common 200' from ASA while trying to authenticate anyconnect client along with ACS log for this attempt under Monitoring and reports --> AAA attempts.
Paps
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2011 04:21 AM
It would also be a good idea to move to ACS 5.1/5.2.
Paps
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide