- Cisco Community
- Technology and Support
- Security
- VPN
- VPN with Firepower/Anconnect over 2 different sites w/redundancy?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 12:20 PM
Hi everyone.
This one is a bit tricky.
We have 2 different Firepower devices, 21xx and 41xx, on different locations. The idea was to have them work independent from each other, but the customer wants some kind of automatic redundancy in case one fails. The current solution they have has the clients having to change the VPN concentrator IP address on their VPN client to connect to the other firewall (not Cisco).
Is there. way to do this? Perhaps leaving the IP address assignment to a DHCP server inside the LAN, and then some routing protocol to announce that IP address on one working firewall?
Really, I was just thinking of using separate IP address pools on each firewall, and instead relying on some kind of round robin feature on the AnyConnect client. Does this exist?
Thanks for your time.
Solved! Go to Solution.
- Labels:
-
AnyConnect
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 12:49 PM - edited 03-25-2020 12:51 PM
Hi,
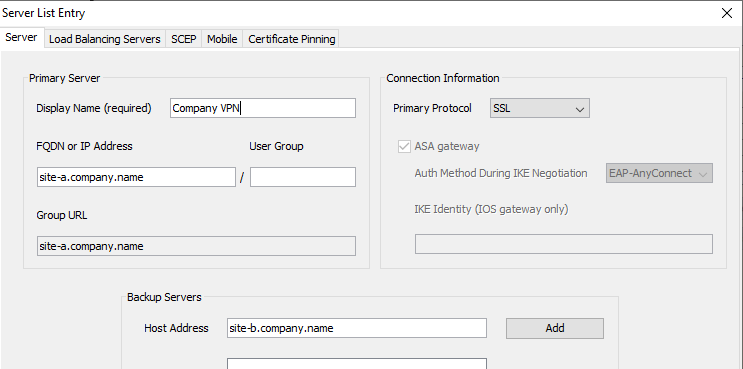
You can define a backup server which in the event the primary FTD/ASA fails, AnyConnect will connect to the backup FTD/ASA. This is configured using the AnyConnect VPN Profile Editor. Example below.
Why does the VPN Pool assignment matter? As you said you could get DHCP to issue the IP address to the clients and then distribute that using a routing protocol.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 12:49 PM - edited 03-25-2020 12:51 PM
Hi,
You can define a backup server which in the event the primary FTD/ASA fails, AnyConnect will connect to the backup FTD/ASA. This is configured using the AnyConnect VPN Profile Editor. Example below.
Why does the VPN Pool assignment matter? As you said you could get DHCP to issue the IP address to the clients and then distribute that using a routing protocol.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 02:04 PM
The answer you gave me is the one I needed. Thanks for your time.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide