- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless - Mobility Knowledge Base
- Central Web Authentication (CWA) for guests with ISE
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
08-11-2012 12:04 AM - edited 11-18-2020 02:59 AM
Introduction
There are multiple ways of doing Web Authentication on the WLC. The first one is Local Web Authentication. In this case, the WLC will redirect the HTTP Traffic to an internal or external server where the user will be prompted to authenticate. The WLC will then fetch this credentials (sent back via HTTP GET Request in case of external server), and make a radius authentication. In case of guest user, we need an external server (like ISE or NGS), as the portal can provide some feature like Device Registering, Self Provisionning, ...
The flow would be the following:
-User associate to the Web Auth SSID
-User starts its browser
-The WLC Redirect to the guest portal (ISE/NGS)
-The user authenticate on the portal
-The Guest Portal redirect back to the WLC with the credentials entered
-The WLC Authenticate the guest user via Radius
-The WLC Redirects back to the original URL.
That makes a lot of redirection. The new approach is to use Central Web Authentication. This works with ISE > 1.1 and WLC > 7.2.
The flow in this case would be:
-User associate to the Web Auth SSID
-User starts its browser
-The WLC Redirect to the guest portal (ISE)
-The user authenticate on the portal
-The ISE send a Radius Change Of Authorization (CoA - UDP Port 3799) to indicate to the controller that the user is valid, and eventually push radius attributes (ACL for example).
-The User is prompted to retry his original URL
Setup Used
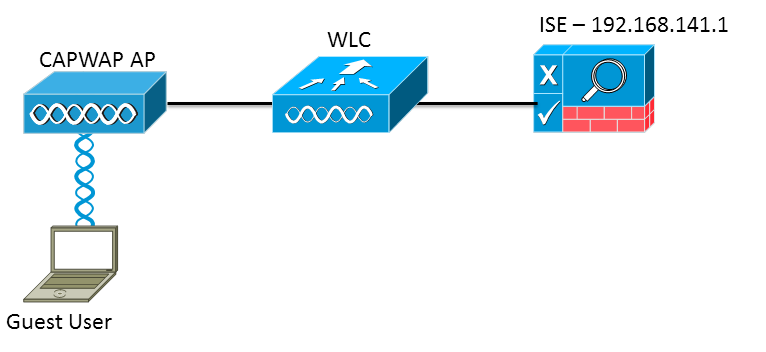
The version used are:
ISE: 1.1.1.268
WLC: 7.2.110.0
WLC Configuration
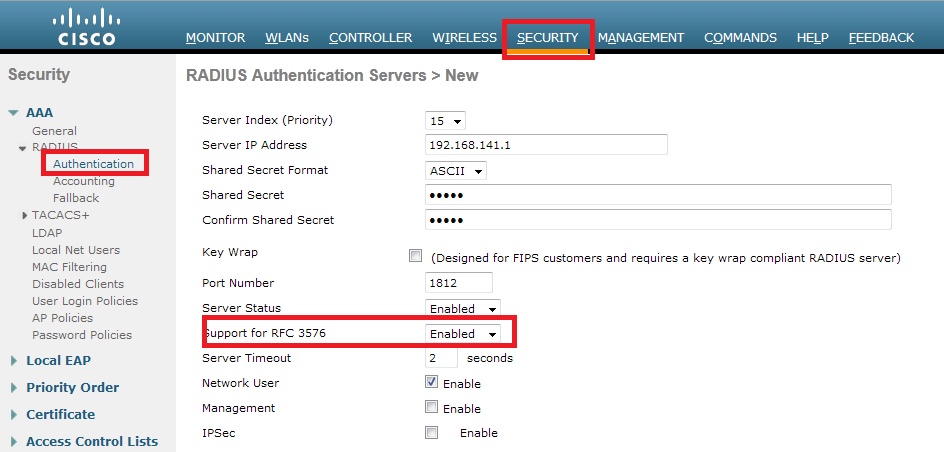
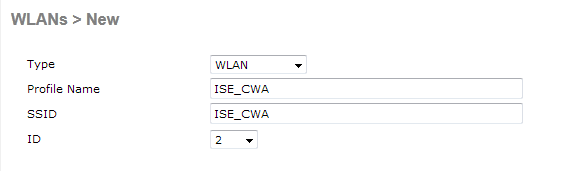
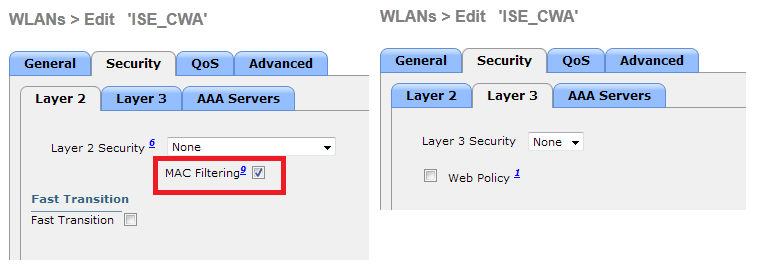
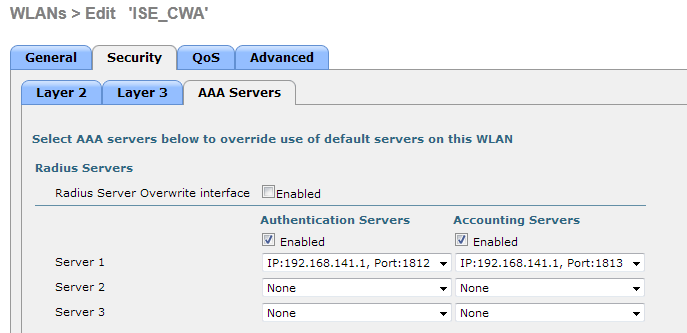
The WLC Configuration is pretty straight-forward. We uses a "trick" (same as on Switches) to get the dynamic authentication URL from the ISE (as it is using CoA, a session needs to be created, and the session ID is part of the URL). We need to configure the SSID to use MAC Filtering. We will configure the ISE to return an access-accept even if the mac address is not found, so that it will sends the redirection URL for all users.
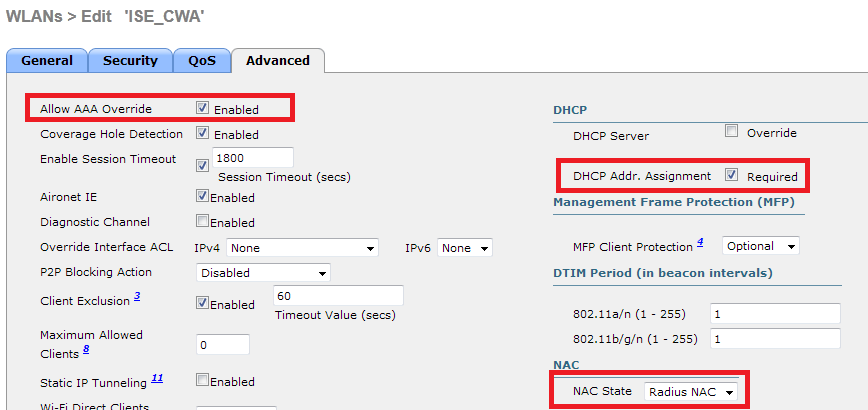
In addition to this, we need to enable Radius NAC and AAA Override. The Radius NAC allows the ISE to send a CoA Request to indicate that the user is now authenticated and can access the network. It is also used for Posture Assessment, in which case the ISE would change the user profile based on posture result.
We need also to be sure that the radius server have RFC 3576 (CoA) enabled, which is by default.
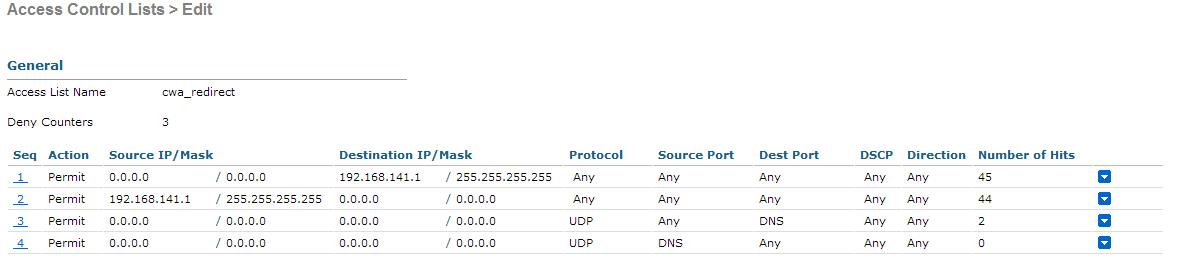
The final step is to create a Redirect-ACL. This ACL will be referenced in the access-accept of the ISE and will define what traffic should be redirected (denied by ACL), and what traffic shouldn't (permitted by the ACL). Basically, we need to permit DNS and traffic to/from ISE.
Everthing is now complete on the WLC. Let's configure the ISE
ISE Configuration
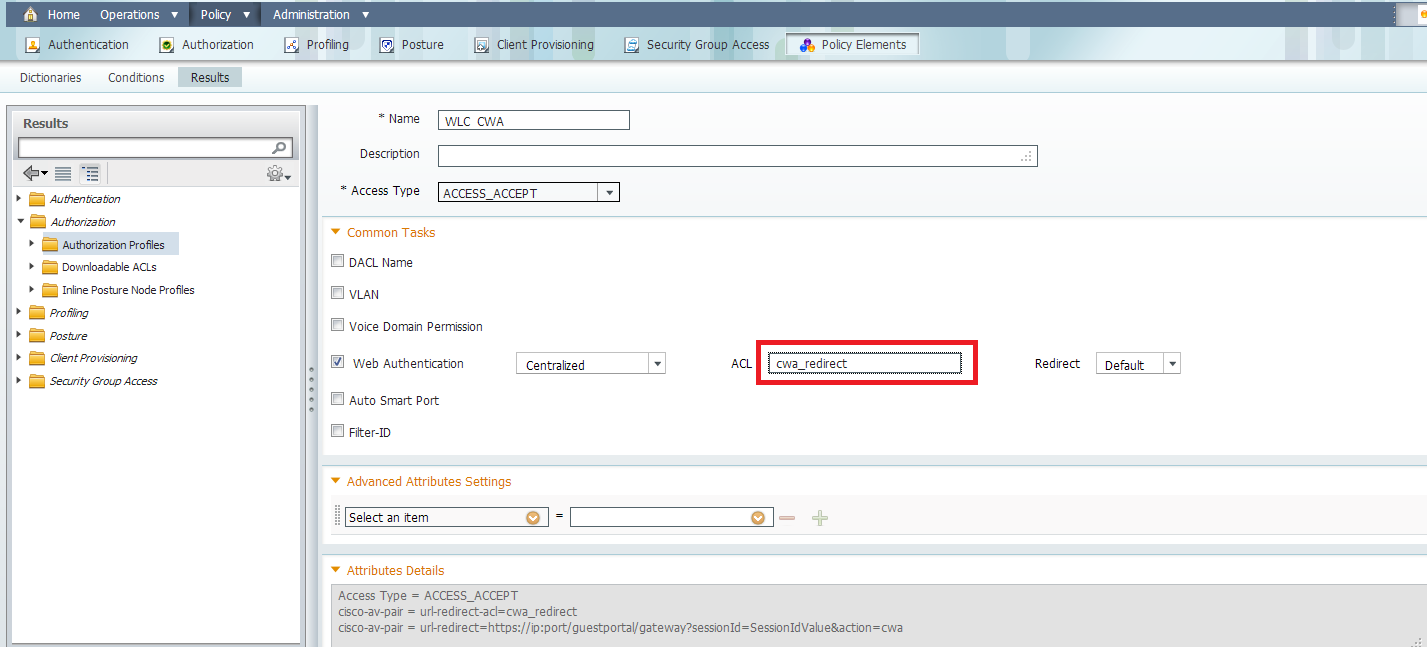
On the ISE, we need to make authorization profile, and then we can configure authentication and authorization. The WLC should already configured as a network device.
In the authorization profile, we need to put the name of the ACL has been created earlier on the WLC:
Now, we need to make sure the ISE is accepting all the MAC Authentication from the WLC and return the profile:

We can use the Built-In Wireless MAB condition, which match :
-Radius:Service-Type : Call Check (Mac Authorization use Call Check on WLC and Switches).
-Radius:NAS-Port-Type: Wireless - IEEE 802.11
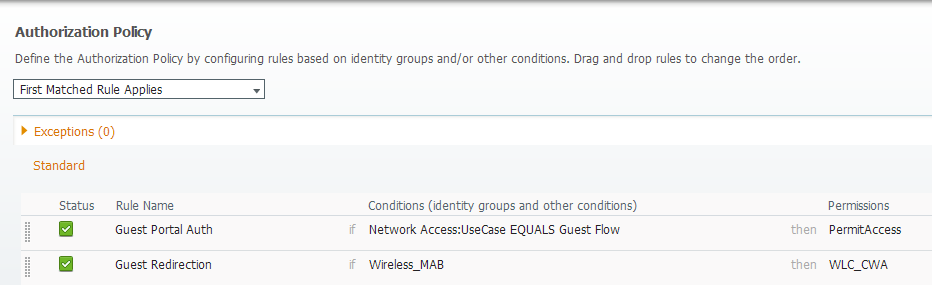
Now, we need to configure the authorization. One important thing to understand is that there will be 2 authentication / authorization:
-One when the user associate to the SSID, and when we need to return the cwa profile
-Another when the user authenticate on the web portal. This one will match the default rule (internal users), in my situation (you can configure it as you want). What is important is that the authorization part doesn't match the CWA Profile again, otherwise we would have a redirection loop. We can use the attribute "Network Access:UseCase Equals Guest Flow" to match this second authentication.
The result looks like this:
Test
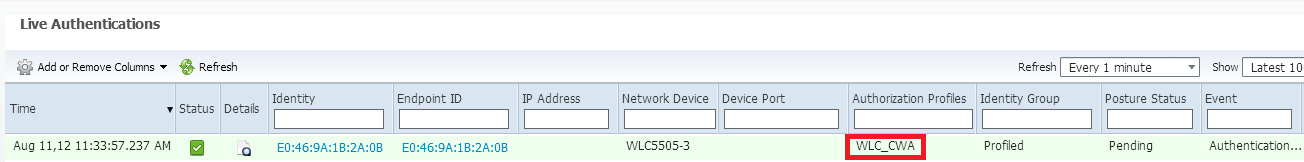
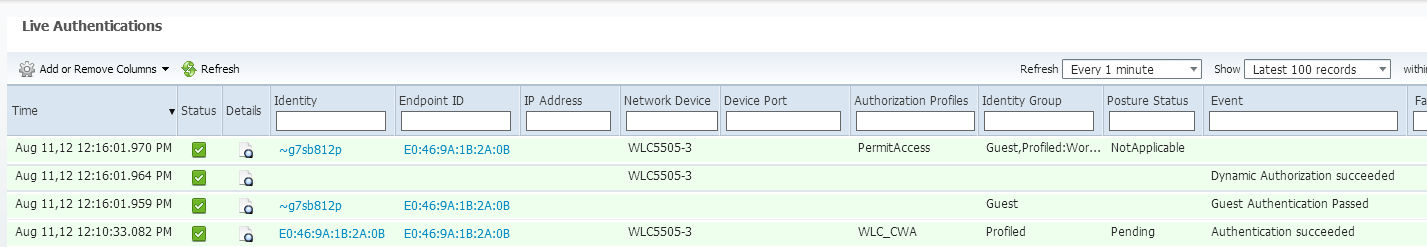
Once we associate to the SSID, we can see the auth in the ISE page:
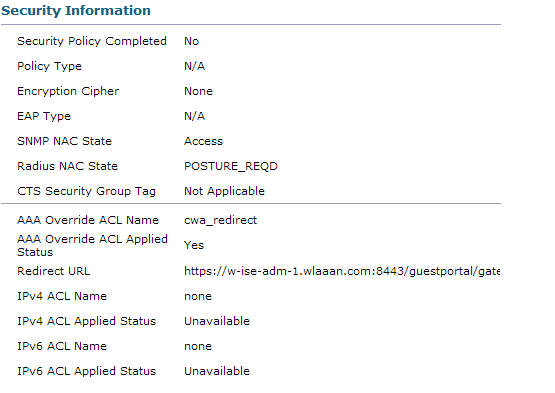
And if we check the client details in the WLC, we can see the Redirection URL and ACL are applied:
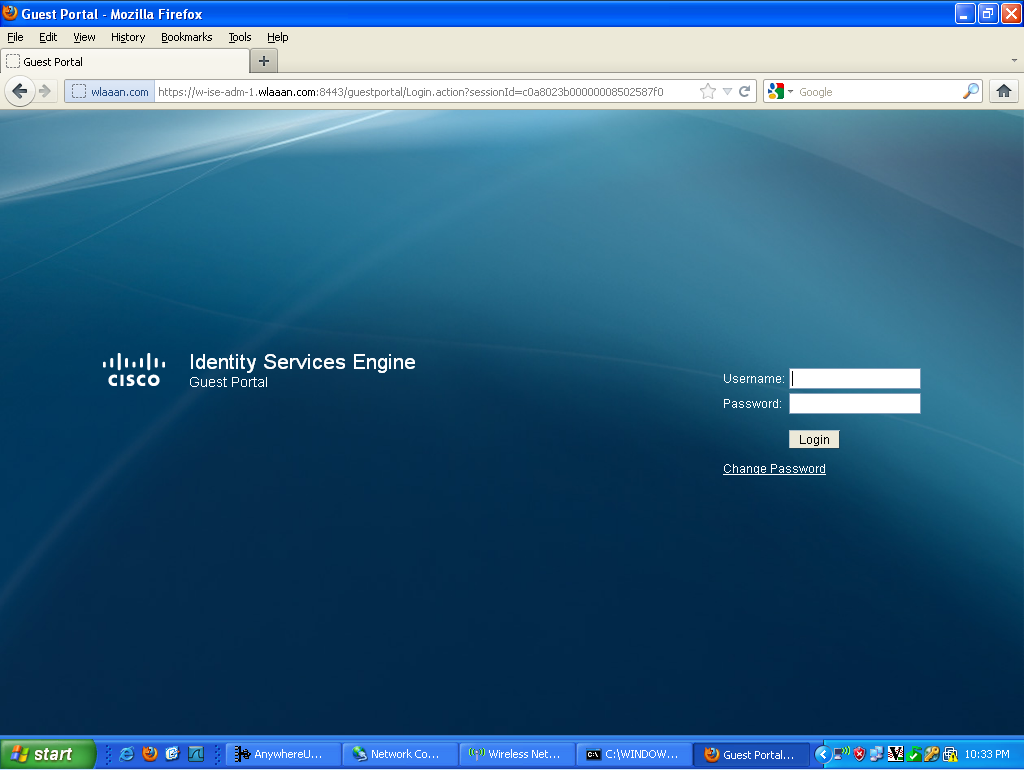
Now, when we open any address on the client, we are redirected to our ISE (be careful to have DNS setup correctly).
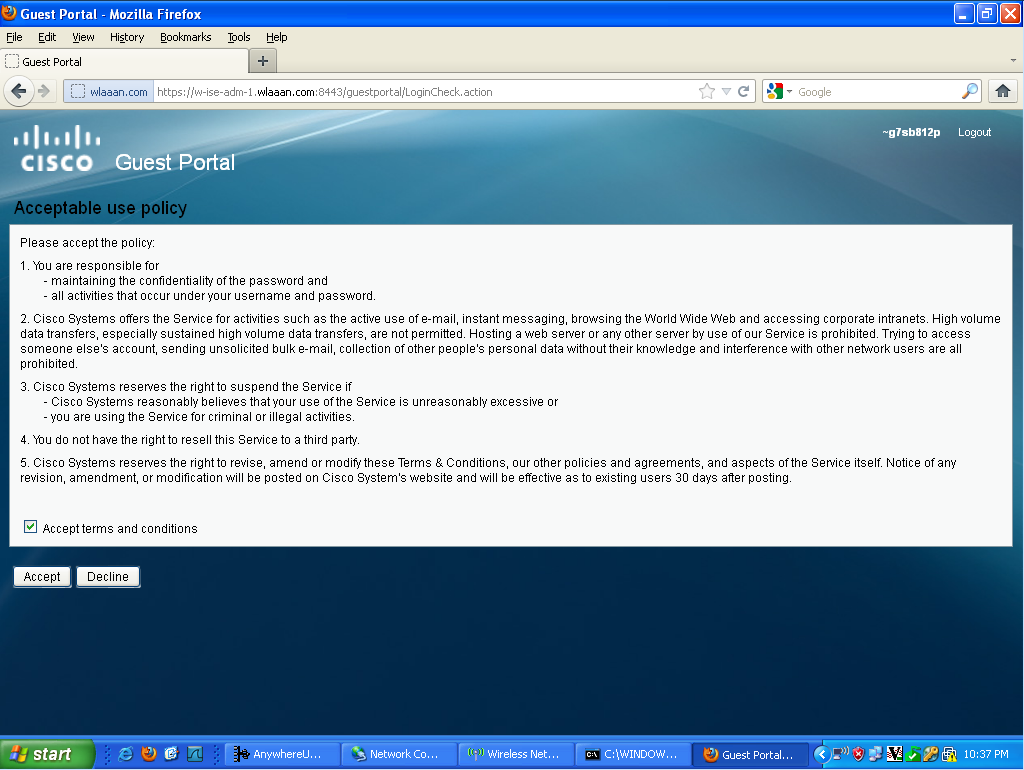
Then the user needs to accept the policies, and then it will be granted access to the network.
If we look back at my ISE, we can now see the authentication, the change of authorization, and that the profile applied is permitAccess:
On the controller, the Policy Manager State and Radius NAC State should change from "POSTURE_REQD" to "RUN"
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
If you disable client MFP and put a big idle-timeout value on the WLC that could work.
Making a custom portal with cookie should work as well, but that would basically still need the guest user to open the browser, then you can have some javascript to auto submit the form with cookie values.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
But on client behaivor we don´t have any influence !! Like disassiciate when lock the phone for example.
The problem is i need to cache something on ise like the mac address to directly permit the guest instead of redirecting to guestportal. Is that possible ?
Do you have any deeper information about abot the cookies or a how-to regarding using cookies with cisco ise ?
Should i open a ticket regarding this problem if there is no official doucement and it takes you too much time ?
Greetings
Philip
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Philip,
if client MFP is not enabled, when iPhone will log out that won't disconnect the session, until the idle timeout is reached.
Cookie / Javascript on guest portal is not really Cisco supported but rather custom made solution.
Another thing that comes to my mind is to include DeviceRegistration in your flow so CWA users will be put in a special group in which you can have no CWA (RegisteredUser) and use guest purge settings of 1 days, but I never tested it.
If you have design questions, usually you can ask your account team and open a TAC case if you face specific problems.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Bastien,
with my example i just mean that we need a way to control who is going to be redirected or not from the infrastructure view. Nobody knows what apple or google will do within the next updates ;-). I just want to configure something that makes sure that caching of guest users work independent of the client.
The config with the device registration i will try. You mean putting the guest automatically in an identity group and the built a auth policy which matches on that group right ? With the purge time i can regulate the "caching time". Generally this is a workaround but quite unsecure of someone duplicates the mac adress ;-)
Can you have a look if there is any document regarding the cookie staff ?
Greetings
Philip
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Fantastic info., thank you, Bastien.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Bastien,
excellent tutorial, I am having the issue that the sessions of clients who authenticated via web auth, after one hour the sessions on the ISE is not shown, but they still connected and have access to the network.
As you wrote "1 hour after session start if no accounting is received." that could be the problem.
Would you tell me how to see if the ISE is receiving accounting from those users?
Thanks a lot for your help.
Regards.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Abraham,
I have the same configuration on my vWLC,
I will see the reports on the ISE now,
Thanks for your help.
Regards.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
We have ISE CWA implemented with 8540-WLC:s and ISE 2.4
My question is, why is the WLC-certificate shown to the user when being redirected to the ISE-portal? Anyone seen similar behaviour?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Bastian,
You wrote:
Starting ISE 1.2, you have the ability to select "Static ip/hostname" in the authorization profile, under the WebAuth part. That way you can put ISE's Policy Node IP address if you don't have correct DNS Entry.
I have the same issue that the when the client connects, it cannot resolve the ISE FQDN Name.
Could you please provide snapshots on how to select staticIP in authorization profile?
Many thansk in advance
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Bastian and Bernardo,
This is an issue when enabling https-redirect on the WLC. I don't think there is a way around it, which is a shame.
Well, the only way around it would be to disable https-redirect - but then you wouldn't be redirected when connecting to a https-site? That wouldn't be good either.
From Ciscos support docs:
Certificate Warnings after HTTPS redirect is enabled
After https-redirect is enabled, the user may experience certificate trust issues during the redirect. This is seen even if there is a valid chained certificate on the controller and even if this certificate is signed by a 3rd party trusted Certificate Authority. The reason is that the certificate installed on the WLC is issued to its Virtual interface hostname or IP address. When the client tries https://cisco.com, the browser expects the certificate to be issued to cisco.com. However, for the WLC to be able to intercept the GET issued by the client, it first needs to establish the HTTPS session for which the WLC presents its Virtual Interface Certificate during SSL handshake phase. This causes the browser to display a warning as the certificate presented during the SSL handshake has not been issued to the original web site the client is trying to access (ie. cisco.com opposed to WLC's Virtual interface hostname). You might see different certificate error messages in different browsers but all relate to the same problem.
- « Previous
- Next »
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: