- Cisco Community
- Technology and Support
- Security
- Email Security
- How to rate-limit outbound SMTP based on sender NOT host system?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
How to rate-limit outbound SMTP based on sender NOT host system?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2010 10:44 AM
I am wondering if there is a way with the IronPort AsyncOS to rate-limit outbound SMTP traffic based on a specific sender NOT by host system (or IP address of host system).
We have had situations where a compromised internal user mailbox becomes compromised (hijacked) and sends hundreds of thousands of spam messages outbound to Internet ISP mail systems causing our mail system to become blacklisted.
Adding outbound smtp rate-limiting confounds the problem as it blocks the entire system not just the compromised mailbox. This halts all mail from our system and upsets everyone.
If no, is there another (non-Cisco IronPort) product that does this? Many Internet ISPs (Verizon, Hotmail, etc. do this, just wondering how they do this?)
Thank you so much in advance, my job relies on an answer here!
- Labels:
-
Email Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-28-2010 07:23 AM
I second that idea.
But there is another variant of the problem that cannot be cater even if this feature is available.
The sender use different mutant of sender address in every sending mail.
Then the solution may need to be applied on per sending ip. I understand there is "recipient limit per hour", but this one doesn't effectively stop zombie spammers.
Chris
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-28-2010 12:18 PM
The best method to use to rate limit per sender (IP or email address) is to use message filter. There are good examples on the online documentation as shown below:
------------------------------------------------------------------
if (rcpt-count > 100) { |
------------------------------------------------------------------
You can also add more conditions to check for 'remote-ip' or 'mail-from' and see the also in the online documentation for message filter rules and actions.
~Fraidoon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-05-2010 12:26 PM
Does anyone know of a non-Cisco IronPort product that will do this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-07-2010 07:34 PM
I suppose I can build a greylisting mechanism based on sender and put it into the outbound transit mta.
But this is never been done before, greylisting usually used for inbound control.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2010 07:55 AM
Recently phishing emails have been responded to by our internal customers thus compromising their mailboxes which in turns causes it to send out large volumes of spam to Yahoo, Gmail, Hotmail, Comcast, etc. Our mail servers then get blacklisted.
Looking for a product to rate limit on the outbound side so we do not get blacklisted.
Can you explain your solution a little more?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-14-2010 07:08 AM
This is a little off topic, postfix policyd is able to define "quota" by sender (not just ip). you can whitelist the other good sender. But it will make your mail flow configuration (using postfix as transit mta) a little complex (i.e. regular maintenance).
http://www.policyd.org/tiki-index.php?page=Quotas&structure=Documentation
p.s. i have never tried it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2016 11:25 AM
It has been six years, and as a customer running AsyncOS 9.6, I would like to know if any further progress has been made on this front? With some of our mail relays, we do use some method to rate-limit some mail. But it would be nice if the IronPorts provided this, as most of our email flows through them.
The current options under Mail Flow Policies and Max. Recipients Per Time Interval pertain to recipients per envelope. So I can send an email with several recipients, say 10. But if I'm only allowed to send to 5 per hour based on Max. Recipients Per Time Interval then 5 of those 10 are blocked. But if I immediately send 10 individually addressed emails, those are delivered, no problem. The User Guide describes this feature as, "The maximum number of recipients during a specified time period that this listener will receive from a unique envelope sender..." which is not accurate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2016 04:19 PM
Hello Tim,
From testing on my device on 9.6 as well;
Envelope Sender Rate limiting enabled to '10' as the limit.
(see screenshot)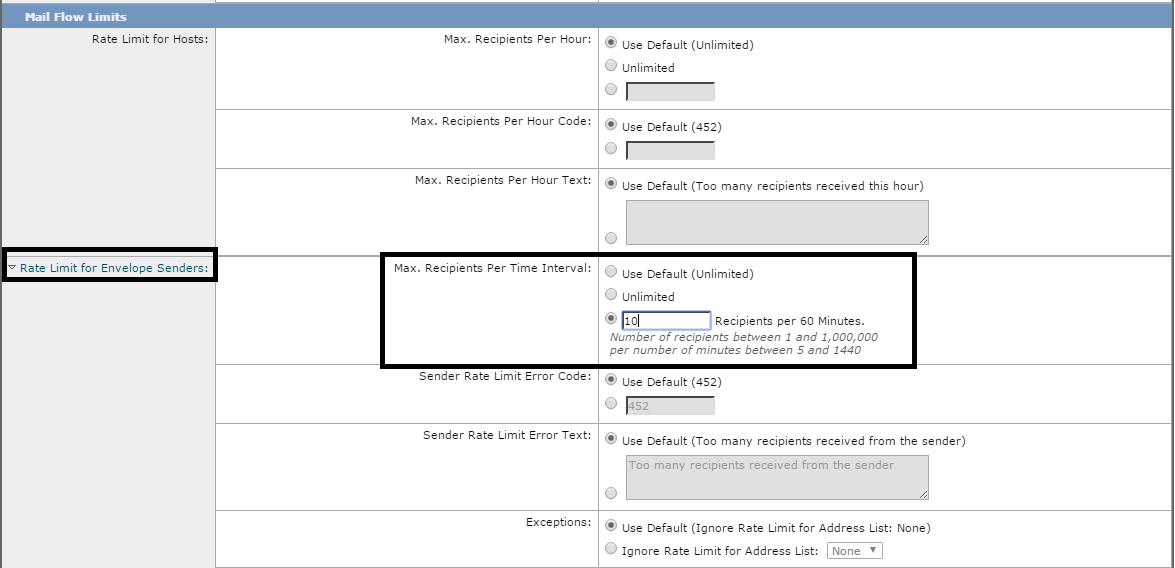
Sent a test email with '11' recipients.
10 of those accepted, MID generated but when the 11th recipient is defined in that message, it will trigger the rate limiting and abort the email with the envelope sender recipient limit exceeded, so the entire email of 11 recipients aborted.
Fri Feb 26 10:11:58 2016 Info: ICID 76003 ACCEPT SG UNKNOWNLIST match sbrs[none] SBRS rfc1918
Fri Feb 26 10:11:58 2016 Info: Start MID 1316 ICID 76003
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 From: <matt@lee.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 0 To: <Mat_test@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 1 To: <test1@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 2 To: <test33@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 3 To: <test123@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 4 To: <test1231321@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 5 To: <6email@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 6 To: <7address@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 7 To: <8address@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 8 To: <9address@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 ICID 76003 RID 9 To: <10address@cisco.com>
Fri Feb 26 10:11:58 2016 Info: MID 1316 To: <11address@cisco.com> From: <matt@lee.com> Rejected by Rate Limiting per Envelope Sender
This sender will then be blocked for 1 hour until counters reset (the 1 hour limit is configurable only by the default policy).
If i broke that email to 11 separate MID, the first 10 MIDs will send, 11th will get rejected from this sending address.
If i separated it to 1 MID with 5 recipients, then second MID with 6, the second MID will be rejected completely and rate limit applied.
Regards,
Matthew
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-29-2016 08:58 AM
Is that occurring in a cluster? We have a cluster of 20 systems, and it appears that the settings is acting per machine, not for the cluster. I know it was coved in the User Guide. I will test more, but so far this setting isn't behaving as I expected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-29-2016 01:47 PM
Hey Tim,
I can re-pro this behaviour in a cluster as well.
Each ESA will hold it's own individual counters so it's right for it to act per machine.
IE : sending 10 emails to ESA 1 will be accepted, If i decide to send another 10 (that should exceed my limit) to ESA 1 again, it'll be rejected, but if I put it to ESA2, it'll be accepted.
At that point both ESA1 and ESA2 will have me on their individual counters and stop me going forward.
Regards,
Matthew
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2016 05:34 AM
Thanks, Matt, for testing. That's what I am experiencing. So I will need to look at other solutions. Hopefully, more options will be added to this feature in future releases.
Tim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-13-2023 01:45 PM
With Mail flow policies and HAT configuration we can't limit based on internal sender just based on Ip or domain.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

