- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: ISE 1.1.1 - Error Code 12521 EAP-TLS failed SSL/TLS handshak
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ISE 1.1.1 - Error Code 12521 EAP-TLS failed SSL/TLS handshake after a client alert
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2012 10:36 AM - edited 03-10-2019 07:25 PM
Hello,
Has anyone come across this error code before? I have looked in the 1.1.1 troubleshooting section and there is nothing there. When I click on the link for the description off the error in ISE I get the following error:
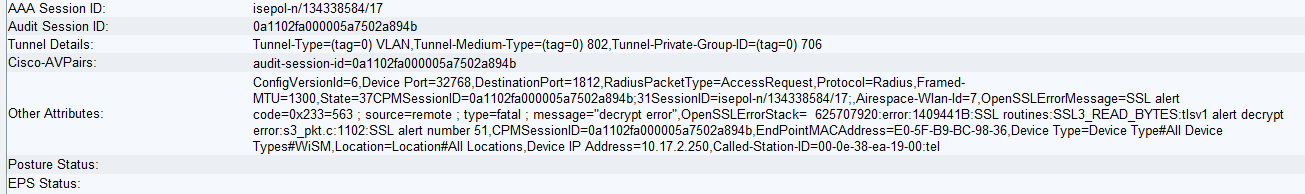
I setup 7925 phones for EAP-TLS using MIC. I have uploaded Cisco's Root CA and Manufactoring CA Certificates and enabled "Trust for client authentication". A Certificate Profile is configured matching Common Name and is added to the Identity Sequence. I got some additional attribute information, where there is a error message:
OpenSSLErrorMessage=SSL alert code=0x233=563 ; source=remote ; type=fatal ; message="decrypt error"
Anyone know what this error means?
- Labels:
-
AAA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2012 10:56 AM
Kyle,
If you are trying to authenticate Cisco phones, can you do me a favor and connect to the phone's https interface (see if you get any errors to see if the cert is corrupt), once you get the certificate warning can you export the phone's certificate using your browser. Once you export the certs you can view the chain and then export the root certificate (if any intermediate certs exist pull them too). You can view the certificate path, double click on the certificate you want to export and the copy to file and that will export the correct certificate.
Then replace the certificates you uploaded and test again.
Tarik Admani
*Please rate helpful posts*
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-15-2012 06:36 AM
The certificates on the phone appear to be in good order. The Root and Manufacturing root certificates on the phone are identical to the ones installed in ISE. Could it somehow be failing on the local Self-Signed certificate?
12502 Extracted EAP-Response containing EAP-TLS challenge-response and accepting EAP-TLS as negotiated
12800 Extracted first TLS record; TLS handshake started
12805 Extracted TLS ClientHello message
12806 Prepared TLS ServerHello message
12807 Prepared TLS Certificate message
12809 Prepared TLS CertificateRequest message
12505 Prepared EAP-Request with another EAP-TLS challenge
11006 Returned RADIUS Access-Challenge
11001 Received RADIUS Access-Request
11018 RADIUS is re-using an existing session
12504 Extracted EAP-Response containing EAP-TLS challenge-response
12815 Extracted TLS Alert message
12521 EAP-TLS failed SSL/TLS handshake after a client alert
12507 EAP-TLS authentication failed
11504 Prepared EAP-Failure
11003 Returned RADIUS Access-Reject
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-15-2012 09:33 AM
Yes,
That could be it see if you can follow this guide on importing the ISE self signed cert: (i used a 7921 guide but it should be similar).
Installing the Authentication Server Root Certificate
The Authentication Server Root Certificate must be installed on the Cisco Unified Wireless IP Phone 7921G.
To install the certificate, follow these steps:
Step 1 ![]() Export the Authentication Server Root Certificate from the ACS. See Exporting Certificates from the ACS.
Export the Authentication Server Root Certificate from the ACS. See Exporting Certificates from the ACS.
Step 2 ![]() Go to the phone web page and choose Certificates.
Go to the phone web page and choose Certificates.
Step 3 ![]() Click Import next to the Authentication Server Root certificate.
Click Import next to the Authentication Server Root certificate.
Step 4 ![]() Restart the phone.
Restart the phone.
Thanks,
Tarik Admani
*Please rate helpful posts*
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-26-2012 08:30 AM
Tarik,
I have exactly the same problem. EAP/TLS failed between 7925G and ISE 1.1.1. I could not solve it with the above propsed solution.
Any other idea?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-26-2012 08:36 AM
Wim,
I opened a TAC case for this a month and a half ago and I do not have a solution yet. I was promised an answer by end of this week. I will post the solution once I have it.
Kyle
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2012 05:22 AM
Kyle,
Very interesting. Thanks for the info. Looking forward to the result of your case.
best regards,
-wim-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2012 12:46 PM
Did you ever get a resolution to this? I am about to start working on this exact thing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-13-2012 08:43 PM
I have seen this issue when you decide not to validate the server side certificate in the phone settings. Seems like it still wants to trust the server side cert anyways.
Tarik Admani
*Please rate helpful posts*
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2013 04:23 AM
Hi,
i have the same problem. Any updates on this one?
@tarik: please note the 7925 admin guide Table 4-3. "Validate Server Certificate. Note: Applies to PEAP only."
So server certificate is always being validated when using EAP-TLS. I think the web gui shouldn't show this option when EAP-TLS is selected.
Anyway, how to solve the problem? Opening of TAC recommended/required?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2013 05:21 AM
Guys,
There is an enhancement request for phones 7925/7921 to support root cert key length 4096. At this time it only support 2048 so make sure we are not running in the same problem.
CSCtj44859 Request to support 4096 size key certificates
Symptom:
7925 / 7921 not working with 4096 bit keys
Conditions:
CA or cert uploaded on the phone has a 4096 bit key
Workaround:
use 2048 bit key
Jatin Katyal
- Do rate helpful posts -
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2013 05:31 AM
Hi,
thanks for the information.
But all certificates imported to the phone have only 2048 bit keys...
What now?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2013 06:38 AM
Sorry I did not get a resolution to this issue. Customer decided it was not worth the effort and went with a PSK.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2013 05:42 AM
Hi everybody,
what signature algorithm does your ISE certificate (and the chained certificates as well) use?
My certificate in my lab uses sha1. -> no access problem.
A customers's ISE uses sha256. -> problem mentioned above.
Could you please confirm?!
Does the 7925 support sha256?? Even the CiscoRootCA and CiscoManufacturingCA uses sha1...
EDIT:
From 7925 Deployment Guide:
"Only certificates with a key size of 1024 or 2048 are supported.
Ensure the CA server certificate is signed using the SHA-1 algorithm as the SHA-2 (SHA-224, SHA-256, SHA-384, SHA-512)
and SHA-3 signature algorithms are not supported.
Certificates dated January 1 2038 and later are not supported."
source: http://www.cisco.com/en/US/docs/voice_ip_comm/cuipph/7925g/7_0/english/deployment/guide/7925dply.pdf
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2013 06:48 AM
As per doc, it is supported. From the doc:
If Cisco ISE is set to operate in FIPS mode, the certificate must be 2048 bits in size and use either SHA-1 or SHA-256 encryption. http://www.cisco.com/en/US/docs/security/ise/1.1/user_guide/ise_man_cert.html#wp1103485
Jatin Katyal
- Do rate helpful posts -
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide