- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Per-user IP address Assignment on ISE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2016 10:22 AM
One of our customers is migrating their existing ACS 4.2 to ISE due to the ACS EoS.
Do we have any plans to add IP pool definition and IP address assignment from ISE like we used to do on ACS? The users are stored in internal database.
I did look at a few old Service requests and mail threads on topic but could not find anything concrete.
https://search-prd.cisco.com/topic/news/cisco/cs/cs-ise/dsc00721.html.
Is this supported on 2.0 or is there any workaround to achieve this?
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-27-2016 10:26 AM
If using AD attributes, then it's supported now in ISE (since 2.0). If using internal user, then it should work with string type.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2016 11:35 AM
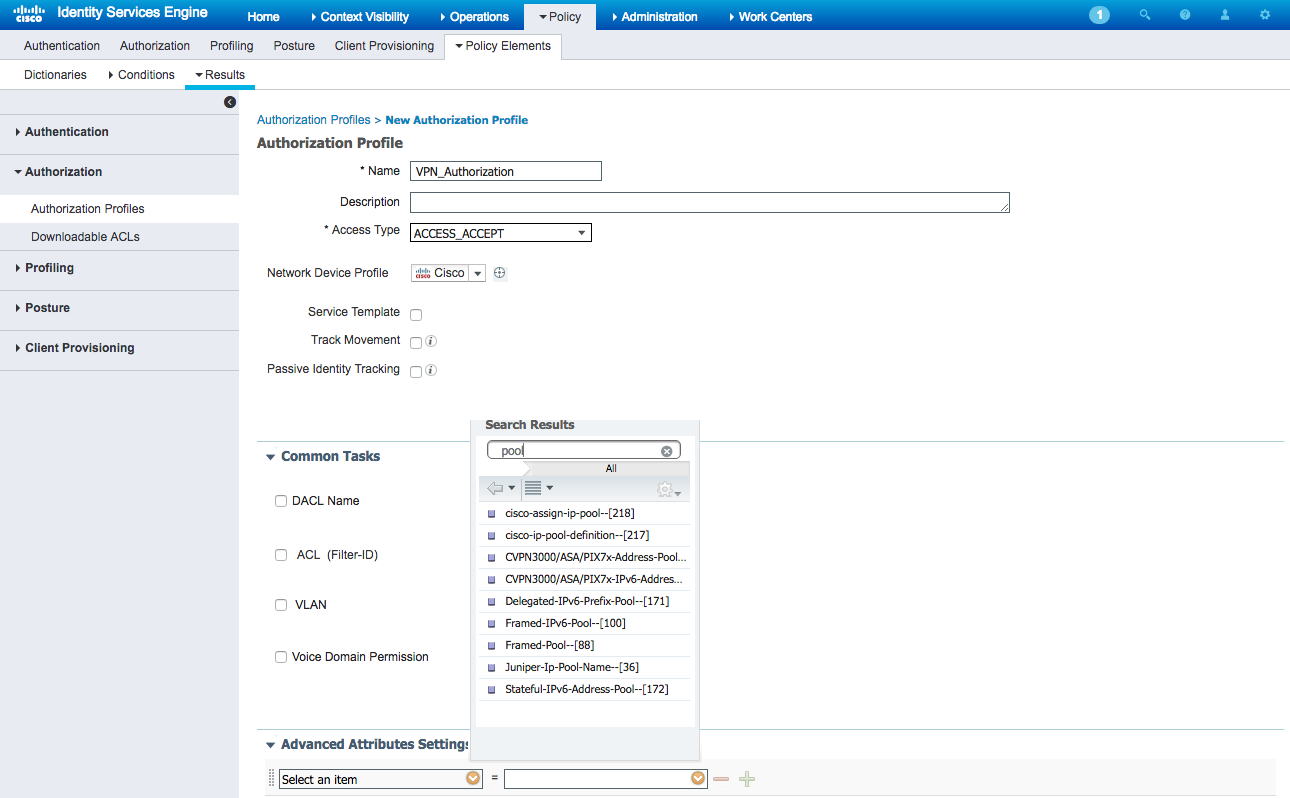
ISE authorization profile can invoke an IP address pool configured on the Network Device. If its a Cisco ASA, then it uses Cisco AV pair (see below). For 3rd party, it is RADIUS attribute 88 Framed-Pool.
Number | Attribute | Description |
217 | IP-Pool-Definition | Defines a pool of addresses using the following format: X a.b.c Z Where X is the pool index number, a.b.c is the pool’s starting IP address, and Z is the number of IP addresses in the pool. For example, 3 10.0.0.1 5 allocates 10.0.0.1 through 10.0.0.5 for dynamic assignment |
218 | Assign-IP-Pool | Tells the router to assign the user and IP address from the IP pool |
You can define these under 'Advanced Attribute Settings' within the Authorization Profile definition in ISE:
Here are some discussions from archives for reference:
https://supportforums.cisco.com/discussion/11740786/cisco-assign-ip-pool-radius-vsa-integer
https://supportforums.cisco.com/discussion/11837241/ip-pool-selection-radius
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-27-2016 10:26 AM
If using AD attributes, then it's supported now in ISE (since 2.0). If using internal user, then it should work with string type.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-28-2016 03:46 AM
Thanks.
Could you please help me understand how it would work with string type?
Manasi Jain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-28-2016 11:42 AM
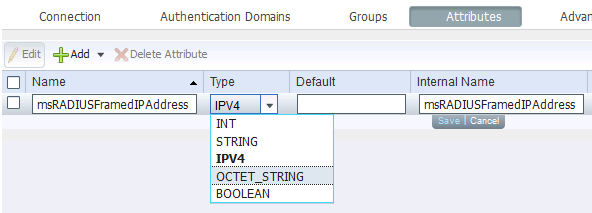
AD had an issue that the value for IPv4-typed attribute not presenting correctly because AD stores the attribute msRADIUSFramedIPAddress in IPv4 type while earlier ISE releases (< 2.0) fetch all AD attributes as string type only. Below is a screenshot in ISE 2.0.1 and updating the type from string to IPv4 after retrieving it from AD.
Internal users have no such problem because ISE may store the IPv4 value as string and present it as string. AFAIK it has always worked if the NAD supporting it.
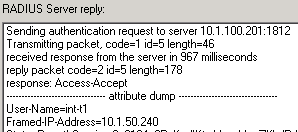
Below is a sample procedure to assign static IP address (Framed-IP-Address) to a session.
1. Define a custom attribute of String type for internal user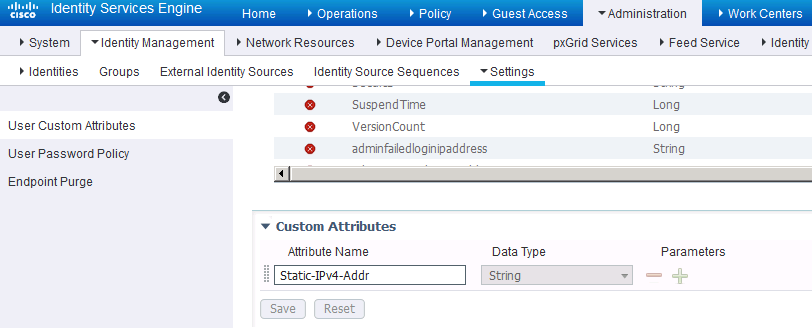
2. Assign the custom internal-user attribute with the static IP address 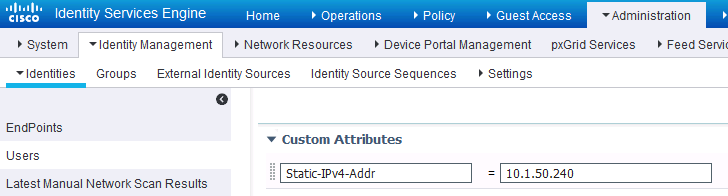
3. Assign a RADIUS authorization profile with advanced attributes settings to assign Radius:Framed-IP-Address with the value from the custom attribute
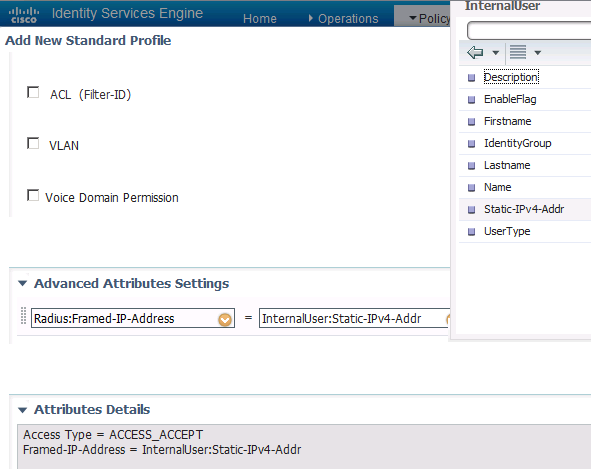
4. Use it in ISE RADIUS authorization policy rule
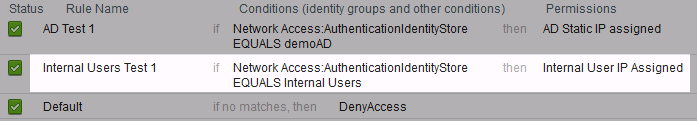
5. Test
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 12:06 AM
Hey Hslai,
first thank you for ur useful Post.
I would like to ask you how can I have a Dynamic IP Pool in ISE2.3? Is it possible? if yes, how could I make it?
Kind Regards,
Keyvan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 11:14 AM
ISE provides RADIUS services so you need to check whether the NAD allows it overridden by AAA attributes and which attributes. Some third-party NAD requires vendor-specific dictionary imported to ISE.
To support web redirects with 3rd-party access NAD, ISE has DNS/DHCP services. See Configure Third-Party NAD Redirection on ISE 2.1 - Cisco
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 12:25 PM
Thanks.
Actually I had read that 3rd party article and I had configured my ISE like that to use DHCP service too but unfortunately it didn't work.
I have installed ISE on VMware and we wanna use it for our Radius server.
That would be nice if you can help me more.
Have a great time.
Cheers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 01:21 PM
Please either start a new discussion thread or engage Cisco TAC, as your request is off topic from this thread.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 11:37 AM
Keyvan
I had the same requirements some years ago already, and we decided to use the API to solve the issue since ISE does not support dynamic IP assignment, which in fact is a poor situation since it was there in ACS 4.x and before...
This for we built a Webfrontend with a DB to hold the IP's (in fact they are created automatically when create a corresponding IP Range/Subnet). Then the intelligence is built on this Webserver to choose one of the next available IP Addresses when a new user is created, without any intervention of the Admin. And all of it, it is multi tenancy...
If you are more interested in the solution, I can provide you a pdf which describes all this in more detail (but it is in german, as well as the webfrontend). But would be easy to translate...
The customer is very happy, since there is almost no other product which supports dynamic IP assignment anymore (neither Aruba CP or Juniper stealbelted).
This is how the architecure looks like:
And this is the look and feel for the admins:
Cheers, Marco
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2017 12:38 PM
Hi Marco
Thanks alot for ur message.
U R right, Exactly I had the same problem with ISE! It is really sucks that it doesn't support dynamic IP assignment!
when I tried to use DHCP service, unfortunately I couldn't figure it out. I thinks it must be a specific authorisation rule for that to use as dhcp rule profile!
Also we wanna use ISE as our Radius Server for our Smartphone management by MDM. It would be great if u wanna share ur docs with me. By the way I live in Germany and speak German too;)
Ur great experience would help us definitely.
Have a nice time.
Cheers
Keyvan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2018 01:35 PM
Hi hslai,
i configured it exactly like in your post, however my AnyConnect result is:
"The secure gateway has rejected the connection attempt. A new connection attempt to the same or another secure gateway is needed, which requires re-authentication.
The following message was received from the secure gateway: No assigned address"
Am i missing something?
Please help!
thx Wladimir
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-16-2018 06:20 PM
Assuming you are using ASA, try the following:
Syslogs
logging class auth
Debugs
The following debug settings focus on radius processing:
- debug radius [all | user | session] - troublehshooting of RADIUS AAA processing initated by the ASA
- debug radius decode - focus on RADIUS message content
- debug radius dynamic authorization - troubleshooting of RADIUS CoA processing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2018 03:46 AM
Hi hslai,
it is working now.
With ISE 2.3 the solution was to use Type IP not String.
With Type String ISE was not sending Framed-IP-Address towards ASA.
Regards,
Wladimir
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2019 01:41 PM
How about something a little less cryptic.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide