Since the last blog on IOS-XE release, there has been a standard maintenance release which was followed by the recently published Extended Maintenance Release(EMR) and the last release on the 16.x train, IOS-XE 16.12.1. With this being an EMR release, it would be supported for 36 months with multiple rebuilds providing defect and PSIRTS fixes. This EMR release would also support SMUs for issues wherever possible.
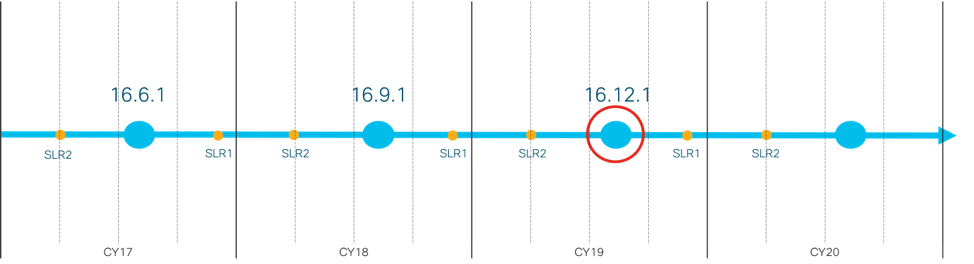
Availability of IOS-XE 16.12.1 for Catalyst Switches continues our journey to building Intent-based Networking through introduction of key software features and exciting innovations on Catalyst 9200, 9300, 9400, 9500 and 9600 Series Switches.
Hardware introductions
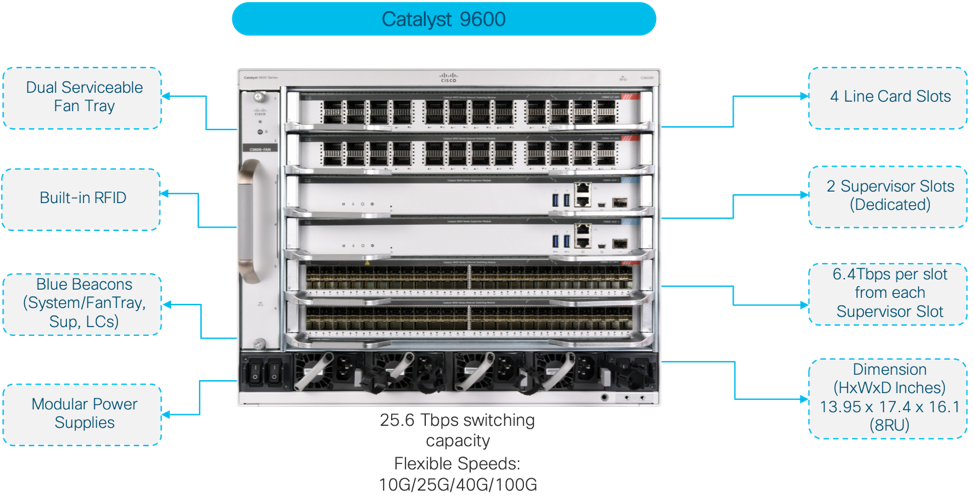
Since 16.10.1 was released, we continued the expansion of Catalyst Switching family by releasing “The ONE thing”,the Catalyst 9600 built on the tradition of the Catalyst6k with all the modern capabilities of Catalyst 9000 family.
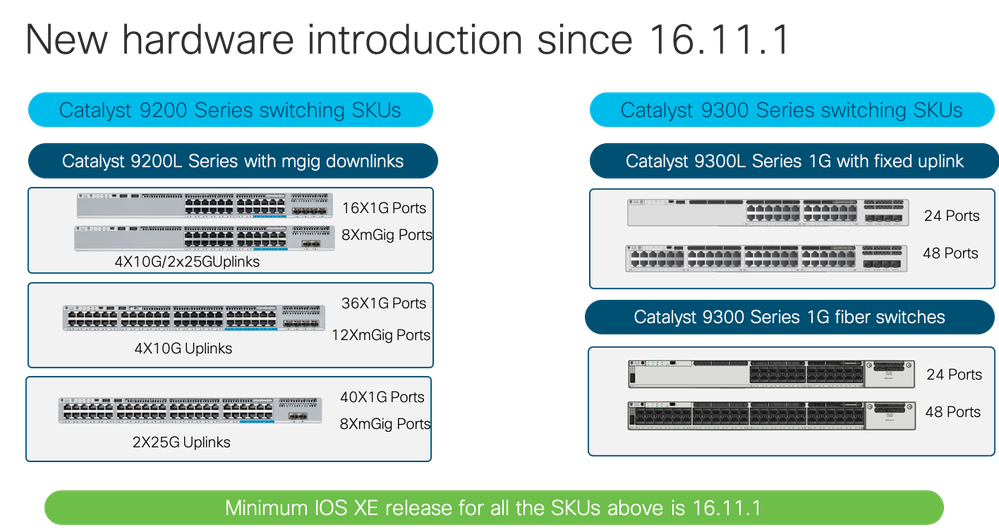
Expansion of Catalyst family continued with introduction of new variants of Catalyst 9200 and Catalyst 9300 Series Switches
One family, One Operating System
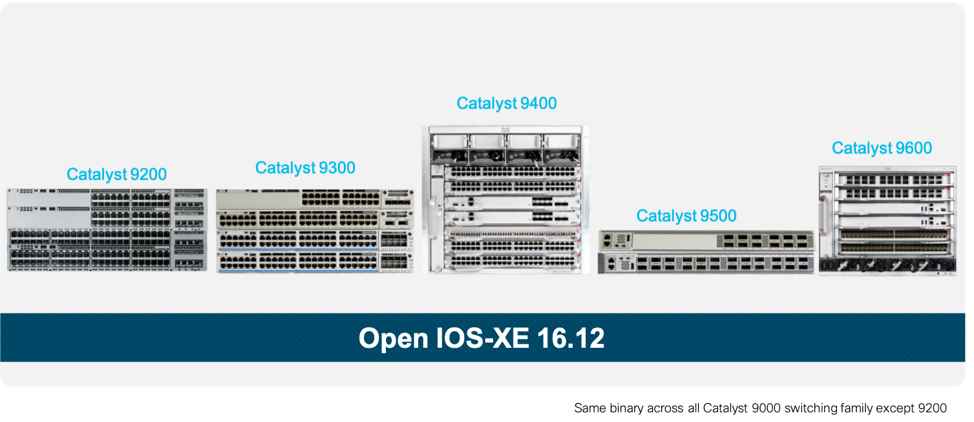
Cisco IOS-XE 16.12.1 is supported across the Catalyst 9000 Series switching family. Taking it further, the same binary image is shared across Catalyst 9300, 9400, 9500 and 9600 thus simplifying the life cycle management of devices across your network.
Extending Intent Based Networking
The Catalyst 9000 family sits at the heart of everything Intent Based Networking, and with these key innovations delivered on our platform we are able to deliver value and experience that our customers desire. In this release, features across security, high availability, segmentation and infrastructure were delivered. Here’s some of the key features introduced on this release.

The open, extensible and programmable IOS-XE 16.12.1 accelerates innovation with the introduction of native docker engine as part of Application Hosting on C9300 enabling Intelligence at Edge. With native docker support, developers can quickly develop applications and deploy them where needed and its entire lifecycle can either be managed via Cisco DNA Center or through CLI and YANG Data models.
With the release, Catalyst 9600 and 9300 Series switches now support StackWise Virtual, bringing virtual chassis redundancy to your network. Using StackWise Virtual, your effective bandwidth can be doubled, while providing multiple paths to all downstream and upstream devices and services, without the need for complex protocols or traffic engineering. We can now Secure StackWise Virtual by encrypting both Control and Data Plane to provide FIPS compliance using Symmetric Early Stack Authentication (SESA) a control plane protocol for key-exchange.
MKA high availability feature adds support for Platforms which support SSO redundancy mode. The feature allows to preserve the existing MKA sessions which are established between Host to Switch and Switch to Switch after failover by syncing the MKA sessions between Active and Standby Switches.
Flexlinks+ has now been introduced in IOS-XE with the 16.12.1 release, which solves the use-cases of Flexlinks, a very well deployed feature. This enables the user to configure up to 26 pairs of Layer 2 interfaces (trunk ports or port channels) where one interface is configured to act as a backup to the other.
Using a Bluetooth dongle connected to front panel USB port, now a user can access the console over the air through Bluetooth allowing easy device management without having to draw cables on the console port.
Catalyst 9300 and 9400 series switches that support 60W of power are now all of IEEE 802.3bt type 3 standards thus allowing administrators to power any end point that is complaint with the standard. The standard itself is backward compatible with 802.3at and 802.3af. Along with this, now there is support for port priority on Catalyst 9400 Series switches to provide more control to users on which ports are given priority in case of power shortage.
IEEE 1588v2 is now supported on Catalyst 9500 High Performance SKUs extending the same support that exists today on Catalyst 9300. With this release, we also introduced Native Layer 3 PTP interface support.
Enhancements have been done on BGP-EVPN domain as well, there is now support for StackWise Virtual on VTEP providing a unified control plane and load balancing across EtherChannels without having to perform any additional configuration on the VTEP. On the border leaf switch, external connectivity now can be achieved through VRF Lite handoff or via L2VPN and L3VPN handoff.
As this being a EMR release, In Service Software Upgrade (ISSU)would be supported within the 16.12 train, enabling users to upgrade their networks with minimal downtime. ISSU can either be done on a standalone Catalyst 9400 and Catalyst 9600 with dual supervisors, or on StackWise Virtual System on Catalyst 9300, 9400, 9500 and 9600.
Finally, support for new optics and breakout cables has also been added and more specifics on this and all other features can be found in the platform specific IOS-XE 16.12 release notes, links to which are provided below:
Call for action!
Participate in Code for Catalyst Challenge where you’ll be building Docker apps for Catalyst 9300 that analyses data available on the switch, generates insights and drives network automation outcomes. The timeframe for the challenge is July 16, 2019, at 12:00 a.m. Pacific Time and ends on September 13, 2019, at 11:59 p.m. Pacific Time. You can participate as an individual contributor or in group of maximum of 3. All the rules and regulations can be found here.
And don’t forget to visit our GitHub repository for examples on how YANG models and Ansible can be used to automate various network tasks. Have an idea of your own? Just do a git push and have your scripts published!
