- Cisco Community
- Technology and Support
- DevNet
- DevNet Networking
- Crosswork Automation Hub
- NSO Developer Hub Discussions
- External Auth remote IP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-14-2019 09:08 AM
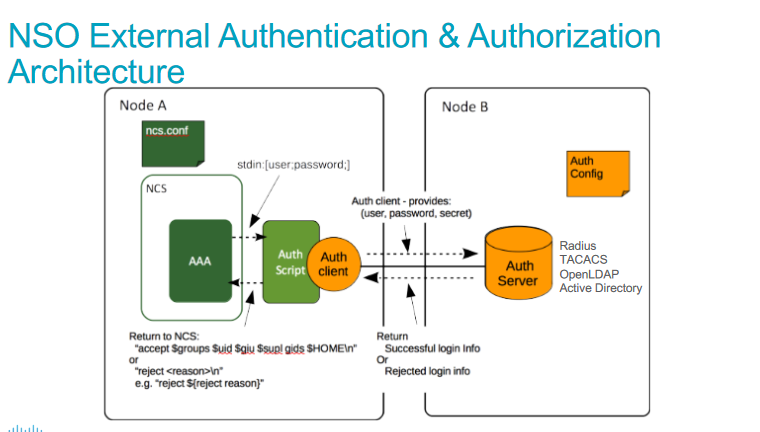
Trying to implement fail2ban onto the NSO service fro external auth. According to the docs NSO sends via stdin username and password. See the picture below.
Is it possible to add other fields to this? More specifically the remote IP of the auth request. This way we can implement fail2ban. Currently, the audit.log shows the from <HOST> but using a custom script for auth only sends via stdin (username, password).
So something like this:
#logging.info("userpass info: {}".format(user_pass_split))
username = user_pass_split[0]
password = user_pass_split[1]
remote_ip = user_pass_split[2]
Solved! Go to Solution.
- Labels:
-
Developer
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-14-2019 09:19 AM
You can configure "/ncs-config/aaa/external-authentication/include-extra" to "true" in ncs.conf.
From the man page for ncs.conf:
/ncs-config/aaa/external-authentication/include-extra (boolean) [false]
When set to 'true', additional information items will be provided to the executable:
source IP address and port, context, and protocol. I.e. the complete format
will be '[${USER};${PASS};${IP};${PORT};${CONTEXT};${PROTO};]\n'.
Example: '[bob;secret;192.168.1.1;12345;cli;ssh;]\n'.
/Ram
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-14-2019 09:19 AM
You can configure "/ncs-config/aaa/external-authentication/include-extra" to "true" in ncs.conf.
From the man page for ncs.conf:
/ncs-config/aaa/external-authentication/include-extra (boolean) [false]
When set to 'true', additional information items will be provided to the executable:
source IP address and port, context, and protocol. I.e. the complete format
will be '[${USER};${PASS};${IP};${PORT};${CONTEXT};${PROTO};]\n'.
Example: '[bob;secret;192.168.1.1;12345;cli;ssh;]\n'.
/Ram
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-14-2019 09:30 AM
Thank you /Ram.
That did the trick. After changing the ncs.conf
<aaa>
<ssh-server-key-dir>${NCS_CONFIG_DIR}/ssh</ssh-server-key-dir>
<!-- Depending on OS - and also depending on user requirements -->
<!-- the pam service value value must be tuned. -->
<pam>
<enabled>true</enabled>
<service>common-auth</service>
</pam>
<external-authentication>
<enabled>true</enabled>
<include-extra>true</include-extra>
<executable>python /sbin/tacacs_test.py</executable>
</external-authentication>
<local-authentication>
<enabled>false</enabled>
</local-authentication>
<expiration-warning>prompt</expiration-warning>
</aaa>I can now filter and send the rem ip and port.
tail: /var/log/nso_external_auth.log: file truncated 11-14 11:26 root INFO username: BAD_User, authen response: False, HOST: 192.168.99.10, PORT: 50850
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide