- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Need Help Configuring ASA 5508-X w/ FTD
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Need Help Configuring ASA 5508-X w/ FTD
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-20-2019 02:37 PM - edited 06-20-2019 02:41 PM
Hi All,
Recently purchased an ASA 5508-X w/ FTD. I'm trying to configure a flat network for it, but it seems to not be able to route out. I created the route rule and set the gateway in the WEB GUI but it doesn't seem like it'll stick? Here's a clean file of "show running-config". All i'm trying to do is to set it up so that it hands out 192.168.1.0/24 and have that interface be able to access the management portal as well.
Serial Number: JAD23160E7E : Hardware: ASA5508, 8192 MB RAM, CPU Atom C2000 series 2000 MHz, 1 CPU (8 cores) : NGFW Version 6.2.3 ! hostname firepower enable password strong-encryption-disable names ! interface GigabitEthernet1/1 nameif outside cts manual propagate sgt preserve-untag policy static sgt disabled trusted security-level 0 ip address dhcp setroute ipv6 address autoconfig ipv6 enable ! interface GigabitEthernet1/2 nameif inside cts manual propagate sgt preserve-untag policy static sgt disabled trusted security-level 0 ip address 192.168.1.1 255.255.255.0 ! interface GigabitEthernet1/3 shutdown no nameif no security-level no ip address ! interface GigabitEthernet1/4 shutdown no nameif no security-level no ip address ! interface GigabitEthernet1/5 shutdown no nameif no security-level no ip address ! interface GigabitEthernet1/6 shutdown no nameif no security-level no ip address ! interface GigabitEthernet1/7 shutdown no nameif no security-level no ip address ! interface GigabitEthernet1/8 shutdown no nameif no security-level no ip address ! interface Management1/1 management-only nameif diagnostic cts manual propagate sgt preserve-untag policy static sgt disabled trusted security-level 0 no ip address ! boot system disk0:/os.img ftp mode passive ngips conn-match vlan-id object network AIM_SERVERS-64.12.31.136 host 64.12.31.136 object network AIM_SERVERS-64.12.46.140 host 64.12.46.140 object network AIM_SERVERS-64.12.186.85 host 64.12.186.85 object network AIM_SERVERS-205.188.1.132 host 205.188.1.132 object network AIM_SERVERS-205.188.11.228 host 205.188.11.228 object network AIM_SERVERS-205.188.11.253 host 205.188.11.253 object network AIM_SERVERS-205.188.11.254 host 205.188.11.254 object network AIM_SERVERS-205.188.210.203 host 205.188.210.203 object network AIM_SERVERS-64.12.24.0-23 subnet 64.12.24.0 255.255.254.0 object network AIM_SERVERS-64.12.28.0-23 subnet 64.12.28.0 255.255.254.0 object network AIM_SERVERS-64.12.161.0-24 subnet 64.12.161.0 255.255.255.0 object network AIM_SERVERS-64.12.163.0-24 subnet 64.12.163.0 255.255.255.0 object network AIM_SERVERS-64.12.200.0-24 subnet 64.12.200.0 255.255.255.0 object network AIM_SERVERS-205.188.3.0-24 subnet 205.188.3.0 255.255.255.0 object network AIM_SERVERS-205.188.5.0-24 subnet 205.188.5.0 255.255.255.0 object network AIM_SERVERS-205.188.7.0-24 subnet 205.188.7.0 255.255.255.0 object network AIM_SERVERS-205.188.9.0-24 subnet 205.188.9.0 255.255.255.0 object network AIM_SERVERS-205.188.153.0-24 subnet 205.188.153.0 255.255.255.0 object network AIM_SERVERS-205.188.179.0-24 subnet 205.188.179.0 255.255.255.0 object network AIM_SERVERS-205.188.248.0-24 subnet 205.188.248.0 255.255.255.0 object network any-ipv4 subnet 0.0.0.0 0.0.0.0 object network any-ipv6 subnet ::/0 object-group network AIM_SERVERS network-object object AIM_SERVERS-64.12.46.140 network-object object AIM_SERVERS-205.188.3.0-24 network-object object AIM_SERVERS-64.12.28.0-23 network-object object AIM_SERVERS-64.12.31.136 network-object object AIM_SERVERS-205.188.5.0-24 network-object object AIM_SERVERS-205.188.153.0-24 network-object object AIM_SERVERS-205.188.1.132 network-object object AIM_SERVERS-205.188.7.0-24 network-object object AIM_SERVERS-64.12.200.0-24 network-object object AIM_SERVERS-205.188.11.254 network-object object AIM_SERVERS-205.188.11.253 network-object object AIM_SERVERS-64.12.24.0-23 network-object object AIM_SERVERS-205.188.248.0-24 network-object object AIM_SERVERS-64.12.186.85 network-object object AIM_SERVERS-64.12.161.0-24 network-object object AIM_SERVERS-205.188.11.228 network-object object AIM_SERVERS-205.188.179.0-24 network-object object AIM_SERVERS-205.188.9.0-24 network-object object AIM_SERVERS-205.188.210.203 network-object object AIM_SERVERS-64.12.163.0-24 access-list NGFW_ONBOX_ACL remark rule-id 268435457: ACCESS POLICY: NGFW_Access_Polic y access-list NGFW_ONBOX_ACL remark rule-id 268435457: L5 RULE: Inside_Outside_Rule access-list NGFW_ONBOX_ACL advanced trust ip ifc inside any ifc outside any rule-id 2 68435457 event-log both access-list NGFW_ONBOX_ACL remark rule-id 1: ACCESS POLICY: NGFW_Access_Policy access-list NGFW_ONBOX_ACL remark rule-id 1: L5 RULE: DefaultActionRule access-list NGFW_ONBOX_ACL advanced deny ip any any rule-id 1 pager lines 24 logging timestamp mtu outside 1500 mtu inside 1500 mtu diagnostic 1500 no failover no monitor-interface service-module icmp unreachable rate-limit 1 burst-size 1 no asdm history enable arp timeout 14400 no arp permit-nonconnected arp rate-limit 16384 nat (any,outside) source dynamic any-ipv4 interface access-group NGFW_ONBOX_ACL global timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:01:00 timeout floating-conn 0:00:00 timeout conn-holddown 0:00:15 timeout igp stale-route 0:01:10 user-identity default-domain LOCAL aaa authentication login-history http server enable http ::/0 inside http 0.0.0.0 0.0.0.0 inside ip-client diagnostic ip-client diagnostic ipv6 ip-client outside ip-client outside ipv6 ip-client inside ip-client inside ipv6 no snmp-server location no snmp-server contact sysopt connection tcpmss 0 no service sw-reset-button crypto ipsec security-association pmtu-aging infinite crypto ca trustpool policy crypto ikev2 policy 100 encryption des integrity sha group 5 prf sha lifetime seconds 86400 crypto ikev1 policy 160 authentication pre-share encryption des hash sha group 5 lifetime 86400 telnet timeout 5 console timeout 0 dhcp-client client-id interface outside dhcpd auto_config outside ! dhcpd address 192.168.1.5-192.168.1.254 inside dhcpd enable inside ! threat-detection basic-threat threat-detection statistics access-list no threat-detection statistics tcp-intercept dynamic-access-policy-record DfltAccessPolicy ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map parameters message-length maximum client auto message-length maximum 512 no tcp-inspection policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect ip-options inspect icmp inspect icmp error ! service-policy global_policy global prompt hostname context call-home profile CiscoTAC-1 no active destination address http https://tools.cisco.com/its/service/oddce/services/DDCESer vice destination address email callhome@cisco.com destination transport-method http subscribe-to-alert-group diagnostic subscribe-to-alert-group environment subscribe-to-alert-group inventory periodic monthly subscribe-to-alert-group configuration periodic monthly subscribe-to-alert-group telemetry periodic daily snort preserve-connection Cryptochecksum:6735856a429bc55140c3326ace634758 : end >
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-20-2019 03:43 PM
Hello,
It looks like the security level on the outside and the inside interface is set to 0. Try and set the security level on the inside interface to 100...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-20-2019 03:57 PM
do you know where i would be able to find that? i just clicked thru everything an unable to see where i can set the security level.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 05:19 AM - edited 06-21-2019 05:20 AM
Hello Shoong001,
Georg is right by default two interfaces with same security level are not allowed to communicate.
via CLI
you just need to connect via SSH
when you get the enabled prompt
issue
config t
int gi1/2
security-level 100
end
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 06:53 AM
It looks like you are running FTD software. If that is the case then there is no concept of Security Levels as there are in ASA software. All interfaces have security level 0.
- same-security-traffic is not applicable on FTD. Traffic between FTD interfaces (inter) and (intra) is allowed by default
Are you getting a default route from the ISP via DHCP?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 08:30 AM
Hello Grant,
thanks for your correction and update
the same security-level is not an issue with FTD as you have noted.
Nice to learn something new.
Best Regards
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 08:58 AM
Static. When I change it to DHCP, I still get the same error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 12:12 PM
My understanding is:
You are trying to have your Inside hosts get dhcp from the firewall? - Does this part work?
You are then trying to have those hosts get out to Internet? - This is not working?
What are the hosts using for DNS btw?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 12:53 PM
Hello,
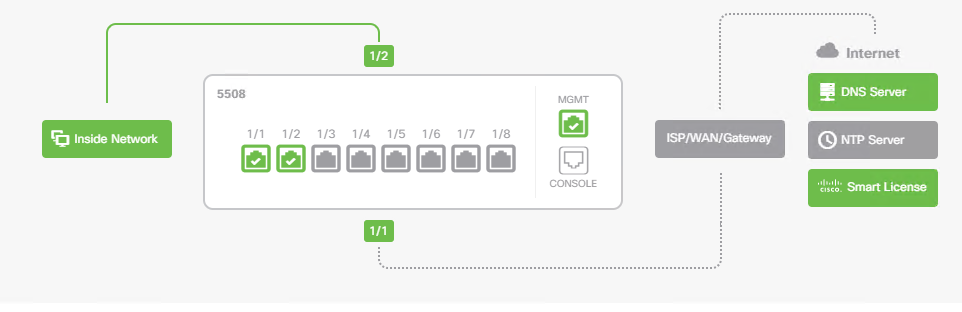
how exactly are you adding the default route ? Just be sure to follow the procedure below...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 12:56 PM
I had a distinct feeling that changing the security levels was too easy...:(
Thanks from me also for the correction...learned something useful...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 01:03 PM
@Georg Pauwen @Giuseppe Larosa
Nothing compared to what I have learned and still learning from you both over the years on CSC 🙂, so thank you.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide