- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: No Internet Access?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
No Internet Access?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-12-2020 06:31 PM - edited 01-12-2020 06:33 PM
I have a test lab environment at home. I have one Cisco 1841 router and a Zyxel Zywall USG 20.
The Zywall connects to my ISP. The Cisco router is behind that.
The Zywall is on the 10.10.10.0/24 network (10.10.10.1)
Router setup:
-fa0/0 10.10.10.254 255.255.255.0 (directly connected to my Zywall)
-no shut
-fa0/1 10.10.11.254 255.255.255.0 (directly connected to my laptop)
-no shut
-No routing protocols are configured on this router (eigrp, rip, ospf, etc...)
Why can't I get out to the internet with my laptop directly connected to the router with static IP of 10.10.11.1/24?
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-12-2020 06:53 PM
Hello,
you probably need to configure NAT on your Cisco router. Add the below to your configuration:
interface FastEthernet0/0
ip nat outside
!
interface FastEthernet0/1
ip nat inside
!
ip nat inside source list 1 interface FastEthernet0/0 overload
!
access-list 1 permit 10.10.11.0 0.0.0.255
!
ip route 0.0.0.0 0.0.0.0 FastEthernet0/0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-13-2020 01:13 AM
@Georg Pauwen wrote:
ip route 0.0.0.0 0.0.0.0 FastEthernet0/0
Georg - Specifying a more of a specific static route to would cut down on unnecessary arp requests
ip route 0.0.0.0 0.0.0.0 fa0/0 10.10.10.1
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-14-2020 01:54 PM - edited 01-14-2020 01:55 PM
Isn't NAT for routing internal private IP address out to the internet (Public IP address)?
Why would I use NAT when I'm using private IP addresses on both sides of the router? Remember my FireWall is facing the internet and then my router is behind that.
I can ping both sides of the router 10.10.11.254/24 and 10.10.10.254/24.
I can't ping the firewall 10.10.10.1/24
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-14-2020 02:02 PM
There are at least 2 probable issues that may be causing your problem:
1) the firewall is probably not aware of the subnet where your PC is connected. It needs a route to that subnet. Or you need to configure nat so that the PC address looks like part of the subnet connecting the firewall and your router.
2) the firewall is probably not configured to perform address translation for the address of your PC. If you choose to add a route on the firewall for the subnet of your PC then you also need to add address translation for that subnet.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-15-2020 06:30 PM - edited 01-15-2020 06:31 PM
Getting closer... I can almost taste it!
After adding the static route to the new subnet (10.10.11.0/24) in the Firwall, I'm able to PING the Firewall's private (internal) IP address from my laptop. I still need to setup NAT for the 10.10.11.0/24 network in the Firewall.
I've never done this before on the Zywall USG 20. I'm not sure of the terms it's asking me.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2020 12:11 AM
Hello,
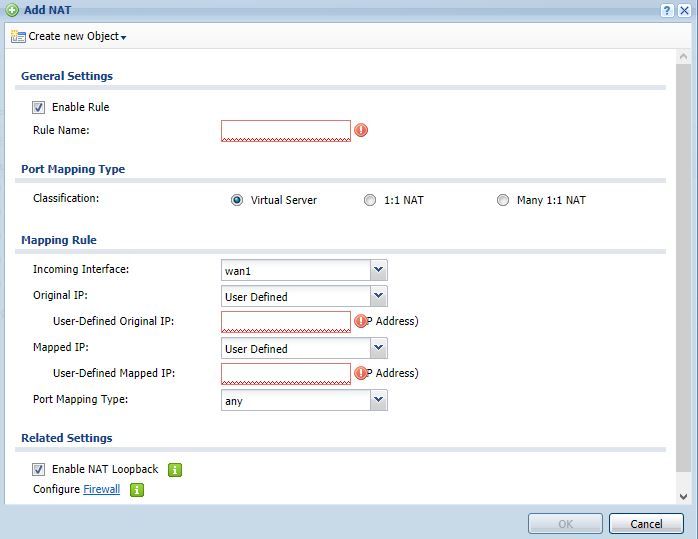
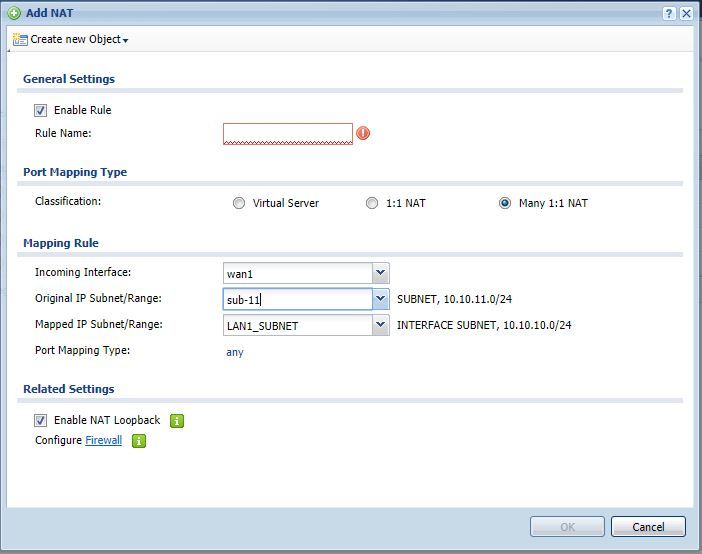
you need to create a new object for the 10.10.11.0/24 network and select that from the drop down list:
If you configure the NAT on the 1841, you don't need to add anything on the Zyxel except a static route to the 10.10.11.0/24 network, so that is probably the easier option.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2020 06:27 PM
I followed your NAT directions to a "T" but I'm still not able to get out to the internet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-17-2020 12:02 AM
Hello,
with the 1841 configured for NAT, can you ping the 10.10.11.0 network from the Zyxel ?
To be sure you configured it correctly, post the amended configuration of the 1841 again including the NAT part.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-17-2020 05:43 PM
I can not PING the 10.10.11.0/24 (.254 or .1) network from a workstation that is on the 10.10.10.0/24 network. I can PING the FW (10.10.10.1) from a workstation that is on the 10.10.11.0/24.
Lets recap my setup in case we have some new viewers tuning in.
My setup so far:
- I have a internet facing Firewall (Zywall USG 20) w/ a LAN IP of 10.10.10.1/24.
- I also have a Cisco 1841 route connected to the Firewall w/ a IP 10.10.10.254/24. The other network is 10.10.11.0/24
- I have a static route on the Firewall pointing to the 10.10.11.0/24 using the port that has the IP 10.10.10.254
- I have NAT setup on the Cisco 1841 w/ an access list allowing the 10.10.11.0/24 to go to the 10.10.10.0/24 network
What else is there to do?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2020 12:16 AM
Hello,
you must be missing something basic, post the full config of the 1841 again as it is currently configured.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2020 09:07 AM
There has been some discussion about configuring the firewall to translate the addresses for network 10.10.11.0 (and to route to that network) and in some respects I consider this to be the more traditional and better solution. But there has also been discussion about configuring the 1841 to translate the 10.10.11.0 addresses and I believe that this is the approach currently being attempted by the original poster. (please correct me if I am not correct about that)
If the 1841 is correctly translating addresses for traffic originated in 10.10.11.0 using the router address in 10.10.10.0 then the firewall should not see anything from 10.10.11.0 and therefore has no need of translation or routing for that subnet. If traffic from that subnet is not working then it suggests that the address translation is not correctly configured. I agree that it would be very helpful to see the complete current running config.
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2020 06:36 AM - edited 01-19-2020 07:20 AM
Here is my running config on the Cisco 1841.
Also just to add a note, I can PING the WAN side of the Zywall (Public IP address) from the 10.10.11.0/24 network. I'm getting closer I just don't know what I'm missing.
R1#sh run
Building configuration...
Current configuration : 1141 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R1
!
boot-start-marker
boot-end-marker
!
enable secret 5 $1$OUBD$XFT4F6CbXxRlBO1bhKVAR0
!
no aaa new-model
!
resource policy
!
ip cef
!
!
!
!
no ip domain lookup
!
!
!
!
!
!
interface FastEthernet0/0
ip address 10.10.10.254 255.255.255.0
ip nat outside
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 10.10.11.254 255.255.255.0
ip nat inside
duplex auto
speed auto
!
interface Serial0/0/0
no ip address
shutdown
no fair-queue
!
ip route 0.0.0.0 0.0.0.0 FastEthernet0/0
!
!
ip http server
no ip http secure-server
ip nat inside source list 1 interface FastEthernet0/0 overload
!
access-list 1 permit 10.10.11.0 0.0.0.255
!
!
!
control-plane
!
!
banner motd ^C
##########################################################
UNAUTHERIZED ACCESS TO THIS ROUTER IS PROHIBITED!!!
##########################################################
^C
!
line con 0
exec-timeout 0 0
password Password123
logging synchronous
login
line aux 0
line vty 0 4
login
!
scheduler allocate 20000 1000
end
R1#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2020 07:26 AM
Hello
It looks like now after adding a static route on that FW you now have reachabilty to the 10.10.11.0/24 so If your are natting on the Zywall then you dont need nat on the rtr1 so remove it let the Zywall fw to this.
You just now need to create a nat rule for that subnet 10.10.110/24 on the FW as explained before and you should be good to go.
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 05:56 AM
Last time I made these settings it brought down the 10.10.10.0/24 network.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide