- Cisco Community
- Technology and Support
- Networking
- Routing
- OSPF vs vPC, which solution is the best / more stable?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-16-2019 08:27 PM
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2019 03:00 AM
Hello RMUTT,
>> The layer three loop occur harder than layer two loop, right?
They are not comparable for impact and scope.
A layer3 routing loop can occur for a specific destination / IP subnet/ prefix packets are discarded when their TTL expires.
It can be detected in a traceroute if you see the same two IP next-hops alternated.
There is no effects on other networks and there is no performance issues and no multiplication of packets.
In a layer 2 bridging loop:
if occurs the impact is very high: broadcast, multicast and unknown unicast frames can be multiplied using all the available resources. Switch cpu usage can become very high. Often requires someone to remove some cables to break the loop.
There is no equivalent of IPv4 TTL and IPv6 hop count that can help to discard frames that are travelling on the loop.
Storm-control can help in getting enough time to access a switch and shut some ports.
In some cases the faster way to solve is to power off and /or isolate one distribution/core switch (if not using VSS or other virtualization modes like vPC or SVL on new Catalyst 9x00 in classic network architecture).
A proper configured vPC provides a "single box" view to downstream switches that do not realize the Nexus are two different devices.
At this point with Nexus vPCs the worst scenario is the dual active or split brain. But you should have a dedicated vPC for keepalive between the two Nexus devices to take care of this.
In your case you can use OSPF and you can connect directly to the multilayer switch this avoids any L2 issues.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-16-2019 11:38 PM
Hello RMUTT,
OSPF is a routing protocol working on OSI layer 3.
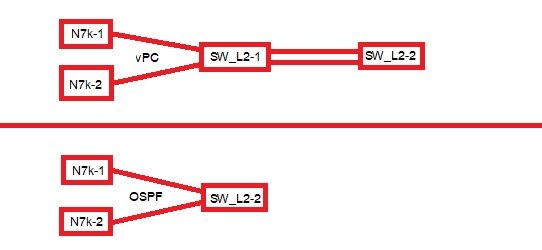
In your network diagram you describe connections of two Nexus 7k switches to a device named SW_L2-1.
If this last device is a L2 only device vPC is your only option here.
Enable LACP this is highly recommended to check every member link health and it is part of the right bundle (vPC on Nexus side and port-channel on the other side)
If devices SW_L2-1 and SW_L2-2 are multilayer switch with IP routing enabled you can run OSPF over the vPC if you want or you can use two indipendent L3 links and perform ECMP Equal cost multi path.
In this last scenario the downstream device will see two different devices N7k-1 and N7k-2 as two different devices with different OSPF RIDs. No LACP is required in this case.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2019 01:08 AM
For the OSPF solution, we can remove the SW_L2-1 then connect the multi-layer SW_L2-2 direct to both N7k. For the OSPF load balance, I think we can tune the configuration. So, back to my question which solution is better?
Thank you very much.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2019 01:30 AM
Hello RMUTT,
OSPF ECMP is enabled by default in standard IOS.
I would expect the same for NX OS.
At this point I would connect directly the multilayer L3 device SW_L2-2 to the two Nexus using two indipendent routed links and would use OSPF over them.
If SW_L2-1 is only L2 it would be better to avoid to have it in the path.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2019 02:19 AM
The layer three loop occur harder than layer two loop, right?
Thank you very much.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2019 03:00 AM
Hello RMUTT,
>> The layer three loop occur harder than layer two loop, right?
They are not comparable for impact and scope.
A layer3 routing loop can occur for a specific destination / IP subnet/ prefix packets are discarded when their TTL expires.
It can be detected in a traceroute if you see the same two IP next-hops alternated.
There is no effects on other networks and there is no performance issues and no multiplication of packets.
In a layer 2 bridging loop:
if occurs the impact is very high: broadcast, multicast and unknown unicast frames can be multiplied using all the available resources. Switch cpu usage can become very high. Often requires someone to remove some cables to break the loop.
There is no equivalent of IPv4 TTL and IPv6 hop count that can help to discard frames that are travelling on the loop.
Storm-control can help in getting enough time to access a switch and shut some ports.
In some cases the faster way to solve is to power off and /or isolate one distribution/core switch (if not using VSS or other virtualization modes like vPC or SVL on new Catalyst 9x00 in classic network architecture).
A proper configured vPC provides a "single box" view to downstream switches that do not realize the Nexus are two different devices.
At this point with Nexus vPCs the worst scenario is the dual active or split brain. But you should have a dedicated vPC for keepalive between the two Nexus devices to take care of this.
In your case you can use OSPF and you can connect directly to the multilayer switch this avoids any L2 issues.
Hope to help
Giuseppe
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide