- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Site to Site VPN behind NAT with Cisco 871 router
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Site to Site VPN behind NAT with Cisco 871 router
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 01:39 PM
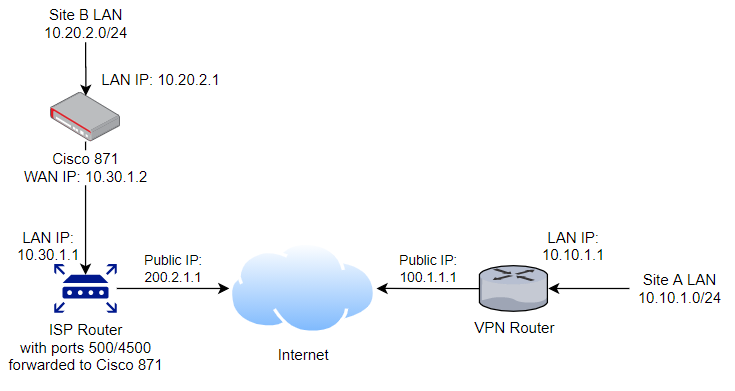
I need to set up a site to site VPN with a Cisco 871 on one side behind a NAT router. Ports 500 and 4500 are forwarded to the 871 router. This should be a fairly standard configuration. The above diagram shows everything for clarity.
If the 871 VPN router was the public router, this would be fairly straight forward with a crypto map. So far I've tried that, but from "show crypto isakmp sa", it looks like it is stuck in the MM_KEY_EXCH. I'm guessing that this may be a mismatch in the identity. Perhaps the router is comparing the private address instead of the public address.
Example output of show crypto isakmp sa:
dst: 100.1.1.1
src: 10.30.1.2
state: MM_KEY_EXCH
Relevant configuration on 871:
crypto isakmp key keyhere address 100.1.1.1
crypto ipsec transform-set vpnts esp-aes 256 esp-sha-hmac
crypto map vpnmap 1 ipsec-isakmp
set peer 100.1.1.1
set transform-set vpnts
match address aclforthisvpn
What am I missing to get this to communicate over the NAT?
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 02:20 PM
The Issue is VPN router not this 871,
can you share the config of it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 03:19 PM
Unfortunately I don't have that configuration. Essentially it's configured with peer as 200.2.1.1 (public address of site B) and the interesting traffic from 10.10.1.0/24 (site A) to 10.20.2.0/24 (site B). I can recommend any changes, but I don't have direct access to that side. I can change anything on the 871 side.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 03:34 PM
Only make him change the crypto isakmp key address 200.2.1.1
i think that will work,
also can I see show crypto isakmp sa detail, and crypto ipsec sa
I want to check if both side agree to use NAT-t.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 08:34 AM
I asked them to verify the configuration on their side, especially the crypto isakmp key command or their equivalent. I don't know what type of device they have.
Here is the output from show crypto isakmp sa detail:
Codes: C - IKE configuration mode, D - Dead Peer Detection
K - Keepalives, N - NAT-traversal
X - IKE Extended Authentication
psk - Preshared key, rsig - RSA signature
renc - RSA encryption
IPv4 Crypto ISAKMP SA
C-id Local Remote I-VRF Status Encr Hash Auth DH Lifetime Cap.
2226 10.30.1.2 100.1.1.1 ACTIVE aes sha psk 2 0 DN
Engine-id:Conn-id = SW:226
Output from show crypto ipsec sa:
interface: FastEthernet4
Crypto map tag: vpnmaps, local addr 10.30.1.2
protected vrf: (none)
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (10.10.1.115/255.255.255.255/0/0)
current_peer 100.1.1.1 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 0, #pkts encrypt: 0, #pkts digest: 0
#pkts decaps: 0, #pkts decrypt: 0, #pkts verify: 0
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 38, #recv errors 0
local crypto endpt.: 10.30.1.2, remote crypto endpt.: 100.1.1.1
path mtu 1500, ip mtu 1500, ip mtu idb FastEthernet4
current outbound spi: 0x0(0)
inbound esp sas:
inbound ah sas:
inbound pcp sas:
outbound esp sas:
outbound ah sas:
outbound pcp sas:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 10:42 AM
from my view the router is not using NAT-T and hence failed.
enable NAT-T in your router
crypto ipsec nat-transparency udp-encapsulation
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 11:39 AM
I thought of that. But, isn't that enabled by default. I added the command anyway, but it hasn't made a difference. I do see in the log a reference to NAT-T. I'll try to post the log.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 11:45 AM
The output of show crypto ipsec sa is interesting. In my experience you get output like this only when the ISAKMP negotiation was successful and the IPSEC negotiation is successful. the output does indicate that no traffic is flowing over the VPN (pkts encap pkts decaps are both zero). I have seen this symptom (caps and decaps are zero) when there were issues with routing logic or issues with address translation, and I am sure that there might be other causes. Before we can give much more advice we will need to see the configuration of the router (with Public IP and any other sensitive information masked).
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-02-2020 05:44 PM
Hi,
Do you have access to the ISP router NAT configuration? If you do, please share the part of config related with the Cisco 871 (you can alias IP addresses with private IP addresses). Also, please share the whole configuration on 871 related with the IPSec (including the ACL defining the interesting traffic, all crypto ipsec commands, ...).
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 11:37 AM
I have full access to the ISP router. There is nothing special here. It is just a generic Xfinity router with standard NAT. The only specific configuration is the forwarding of ports 500 and 4500. I can see the requests hitting the 871 router, so I know the port forwarding is working.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 12:02 AM
Hello,
shut/no shut the WAN interface on the 871 and post the output of:
debug crypto isakmp
debug crypto ipsec
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 08:05 AM - edited 12-03-2020 08:05 AM
Hello
Need to make sure both rtrs are NAT-T capable , what ios versions are currenlty running on them or at least the 871?
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 11:41 AM
The 871 is running Version 12.4(15)T6. I don't know about the other router.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 12:01 PM - edited 12-03-2020 12:01 PM
Okay
Then that rtr is NAT-T capable (above 12.2(13)T, now if the other rtr isn't then it could be the reason why the s2s vpn isn't working.
Lastly can you confirm you have a crypto policy created?
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-03-2020 12:03 PM
Debug output for isakmp:
Dec 3 19:46:54.845: ISAKMP:(2445): retransmitting phase 1 MM_KEY_EXCH... Dec 3 19:46:54.845: ISAKMP (0:2445): incrementing error counter on sa, attempt 4 of 5: retransmit phase 1 Dec 3 19:46:54.845: ISAKMP:(2445): retransmitting phase 1 MM_KEY_EXCH Dec 3 19:46:54.845: ISAKMP:(2445): sending packet to 100.1.1.1 my_port 4500 peer_port 4500 (I) MM_KEY_EXCH Dec 3 19:46:54.845: ISAKMP:(2445):Sending an IKE IPv4 Packet. Dec 3 19:47:00.387: ISAKMP:(0): SA request profile is (NULL) Dec 3 19:47:00.387: ISAKMP: Created a peer struct for 100.1.1.1, peer port 500 Dec 3 19:47:00.387: ISAKMP: New peer created peer = 0x839D81EC peer_handle = 0x8000069D Dec 3 19:47:00.387: ISAKMP: Locking peer struct 0x839D81EC, refcount 1 for isakmp_initiator Dec 3 19:47:00.387: ISAKMP: local port 500, remote port 500 Dec 3 19:47:00.387: ISAKMP: set new node 0 to QM_IDLE Dec 3 19:47:00.387: ISAKMP: Find a dup sa in the avl tree during calling isadb_insert sa = 83127C80 Dec 3 19:47:00.387: ISAKMP:(0):Can not start Aggressive mode, trying Main mode. Dec 3 19:47:00.387: ISAKMP:(0):found peer pre-shared key matching 100.1.1.1 Dec 3 19:47:00.387: ISAKMP:(0): constructed NAT-T vendor-rfc3947 ID Dec 3 19:47:00.387: ISAKMP:(0): constructed NAT-T vendor-07 ID Dec 3 19:47:00.387: ISAKMP:(0): constructed NAT-T vendor-03 ID Dec 3 19:47:00.391: ISAKMP:(0): constructed NAT-T vendor-02 ID Dec 3 19:47:00.391: ISAKMP:(0):Input = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM Dec 3 19:47:00.391: ISAKMP:(0):Old State = IKE_READY New State = IKE_I_MM1 Dec 3 19:47:00.391: ISAKMP:(0): beginning Main Mode exchange Dec 3 19:47:00.391: ISAKMP:(0): sending packet to 100.1.1.1 my_port 500 peer_port 500 (I) MM_NO_STATE Dec 3 19:47:00.391: ISAKMP:(0):Sending an IKE IPv4 Packet. Dec 3 19:47:00.415: ISAKMP (0:0): received packet from 100.1.1.1 dport 500 sport 500 Global (I) MM_NO_STATE Dec 3 19:47:00.415: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH Dec 3 19:47:00.415: ISAKMP:(0):Old State = IKE_I_MM1 New State = IKE_I_MM2 Dec 3 19:47:00.415: ISAKMP:(0): processing SA payload. message ID = 0 Dec 3 19:47:00.415: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.415: ISAKMP:(0): vendor ID is DPD Dec 3 19:47:00.415: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.415: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch Dec 3 19:47:00.415: ISAKMP (0:0): vendor ID is NAT-T RFC 3947 Dec 3 19:47:00.415: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.415: ISAKMP:(0): vendor ID seems Unity/DPD but major 201 mismatch Dec 3 19:47:00.419: ISAKMP:(0):found peer pre-shared key matching 100.1.1.1 Dec 3 19:47:00.419: ISAKMP:(0): local preshared key found Dec 3 19:47:00.419: ISAKMP : Scanning profiles for xauth ... sitebvpn Dec 3 19:47:00.423: ISAKMP:(0):Checking ISAKMP transform 4 against priority 5 policy Dec 3 19:47:00.423: ISAKMP: encryption AES-CBC Dec 3 19:47:00.423: ISAKMP: keylength of 256 Dec 3 19:47:00.423: ISAKMP: hash SHA Dec 3 19:47:00.423: ISAKMP: default group 2 Dec 3 19:47:00.423: ISAKMP: auth pre-share Dec 3 19:47:00.423: ISAKMP: life type in seconds Dec 3 19:47:00.423: ISAKMP: life duration (VPI) of 0x0 0x1 0x51 0x80 Dec 3 19:47:00.423: ISAKMP:(0):atts are acceptable. Next payload is 0 Dec 3 19:47:00.423: ISAKMP:(0):Acceptable atts:actual life: 0 Dec 3 19:47:00.423: ISAKMP:(0):Acceptable atts:life: 0 Dec 3 19:47:00.423: ISAKMP:(0):Fill atts in sa vpi_length:4 Dec 3 19:47:00.423: ISAKMP:(0):Fill atts in sa life_in_seconds:86400 Dec 3 19:47:00.423: ISAKMP:(0):Returning Actual lifetime: 86400 Dec 3 19:47:00.423: ISAKMP:(0)::Started lifetime timer: 86400. Dec 3 19:47:00.423: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.423: ISAKMP:(0): vendor ID is DPD Dec 3 19:47:00.423: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.423: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch Dec 3 19:47:00.423: ISAKMP (0:0): vendor ID is NAT-T RFC 3947 Dec 3 19:47:00.423: ISAKMP:(0): processing vendor id payload Dec 3 19:47:00.423: ISAKMP:(0): vendor ID seems Unity/DPD but major 201 mismatch Dec 3 19:47:00.423: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE Dec 3 19:47:00.423: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM2 Dec 3 19:47:00.427: ISAKMP:(0): sending packet to 100.1.1.1 my_port 500 peer_port 500 (I) MM_SA_SETUP Dec 3 19:47:00.427: ISAKMP:(0):Sending an IKE IPv4 Packet. Dec 3 19:47:00.427: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE Dec 3 19:47:00.427: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM3 Dec 3 19:47:00.463: ISAKMP (0:0): received packet from 100.1.1.1 dport 500 sport 500 Global (I) MM_SA_SETUP Dec 3 19:47:00.463: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH Dec 3 19:47:00.463: ISAKMP:(0):Old State = IKE_I_MM3 New State = IKE_I_MM4 Dec 3 19:47:00.467: ISAKMP:(0): processing KE payload. message ID = 0 Dec 3 19:47:00.511: ISAKMP:(0): processing NONCE payload. message ID = 0 Dec 3 19:47:00.511: ISAKMP:(0):found peer pre-shared key matching 100.1.1.1 Dec 3 19:47:00.511: ISAKMP:received payload type 20 Dec 3 19:47:00.511: ISAKMP (0:2447): NAT found, the node inside NAT Dec 3 19:47:00.511: ISAKMP:received payload type 20 Dec 3 19:47:00.511: ISAKMP:(2447):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE Dec 3 19:47:00.511: ISAKMP:(2447):Old State = IKE_I_MM4 New State = IKE_I_MM4 Dec 3 19:47:00.511: ISAKMP:(2447):SA is doing pre-shared key authentication using id type ID_IPV4_ADDR Dec 3 19:47:00.511: ISAKMP (0:2447): ID payload next-payload : 8 type : 1 address : 10.30.1.2 protocol : 17 port : 0 length : 12 Dec 3 19:47:00.511: ISAKMP:(2447):Total payload length: 12 Dec 3 19:47:00.515: ISAKMP:(2447): sending packet to 100.1.1.1 my_port 4500 peer_port 4500 (I) MM_KEY_EXCH Dec 3 19:47:00.515: ISAKMP:(2447):Sending an IKE IPv4 Packet. Dec 3 19:47:00.515: ISAKMP:(2447):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE Dec 3 19:47:00.515: ISAKMP:(2447):Old State = IKE_I_MM4 New State = IKE_I_MM5 Dec 3 19:47:00.711: ISAKMP:(2446): retransmitting phase 1 MM_KEY_EXCH... Dec 3 19:47:00.711: ISAKMP (0:2446): incrementing error counter on sa, attempt 2 of 5: retransmit phase 1 Dec 3 19:47:00.711: ISAKMP:(2446): retransmitting phase 1 MM_KEY_EXCH Dec 3 19:47:00.711: ISAKMP:(2446): sending packet to 100.1.1.1 my_port 500 peer_port 500 (R) MM_KEY_EXCH Dec 3 19:47:00.711: ISAKMP:(2446):Sending an IKE IPv4 Packet.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide