- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- How to Integrate Cisco ISE with Microsoft SCCM for Patch Management and MDM Flow
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
10-15-2018
08:20 AM
- edited on
01-27-2021
08:08 AM
by
thomas
![]()
Deploying Cisco ISE with Microsoft SCCM
Nidhi Pandey, Technical Marketing Engineer
Serhii Kucherenko, Technical Consulting Engineer
October 2018
Table of Contents
- Introduction
- AboutThisGuide
- Define
- What is SCCM?
- SCCM Workflow For MDM Flow
- SCCM Workflow for Patch Management
- Design
- ISE Integration with SCCM for MDM Flow
- Communicating Ports
- Use Cases for ISE MDM support for SCCM
- Deploy
- Preparing for ISE Integration with SCCM for MDM Flow
- Configuration Changes on the Microsoft SCCM Server
- Adding SCCM server as MDM in ISE
- New MDM Attributes in ISE for SCCM server
- Preparing for ISE Integration with SCCM for Patch Management Flow
- Supported Versions
- Patch management Conditions
- Patch Management Remediation
- Configuration steps for Patch Management condition and Remediation action on ISE
- Steps to Validate the Patch Management solution with ISE
- Operate
- Troubleshooting
- SCCM MDM Flow Troubleshooting
- SCCM Patch Management Flow Troubleshooting
- ISE Troubleshooting
Introduction
About Cisco Identity Services Engine (ISE)
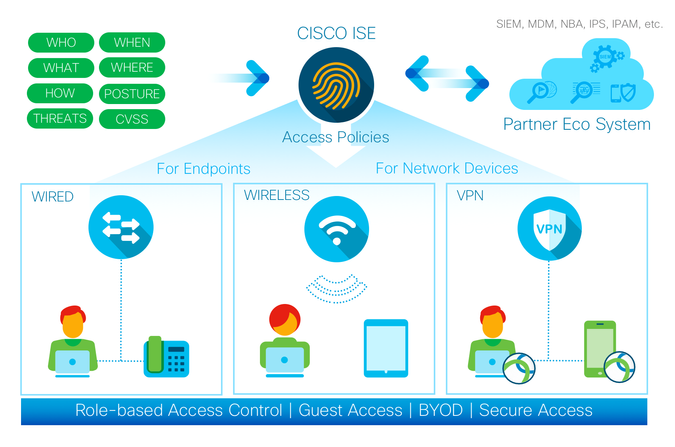
Figure 1: Cisco Identity Services Engine
Cisco ISE is a leading, identity-based network access control and policy enforcement system. It is a common policy engine for controlling, endpoint access and network device administration for enterprises. ISE allows an administrator to centrally control access policies for wired, wireless, and VPN endpoints in a network.
ISE builds context about the endpoints that include users and groups (Who), device type (What), access time (When), access location (Where), access type (Wired/Wireless/VPN) (How), threats, and vulnerabilities. By sharing vital contextual data with technology partner integrations and the implementation of the Cisco TrustSec® policy for software-defined segmentation, ISE transforms a network from a conduit for data into a security enforcer that accelerates the time-to-detection and time-to-resolution of network threats.
About This Guide
This guide is intended to provide technical guidance to design, deploy and operate Cisco Identity Services Engine (ISE) with Microsoft SCCM Server. This document focuses on integration of ISE with SCCM so that ISE can retrieve compliance information from SCCM server and leverage the information to control network access to the user’s Windows device.
This document also shows how Cisco AnyConnect Secure Mobility client (aka AnyConnect) can be integrated with Cisco Identity Service Engine and System Center Configuration Manager (SCCM) for patching Microsoft Windows platform with windows patches.
The first half of the document focuses on the planning and design activities, the other half covers specifics of configurations and operations. There are four major sections in this document. The initial, define part talks about defining the problem area, planning for deployment, and other considerations. Next, in the design section, you will see how to configure SCCM server to communicate with Cisco ISE to make policy decision based on the compliance information. Third, in the deploy part, the various configuration and best practice guidance will be provided. Lastly, in the operate section, you will learn how troubleshoot and monitor.
Define
ISE supports Microsoft's System Center Configuration Manager (SCCM) as a partner MDM server for managing Windows computers. AnyConnect and ISE integration with SCCM client, provides the ability, to verify if the SCCM client is pending install of patches (as classified by Microsoft®)
What is SCCM?
SCCM is short for System center Configuration Manger. SCCM is a software management suite provided by Microsoft that allows users to manage a large number of Windows based computers. SCCM features remote control, patch management, operating system deployment, network protection and other various services. It also provides administrators with the tools to control all aspects of their IT system while keeping costs low.
ISE can perform a policy check with SCCM by following methods
- Using AnyConnect for posture (leveraging OPSWAT libraries)
- ISE checking status with SCCM as an MDM Server using WMI
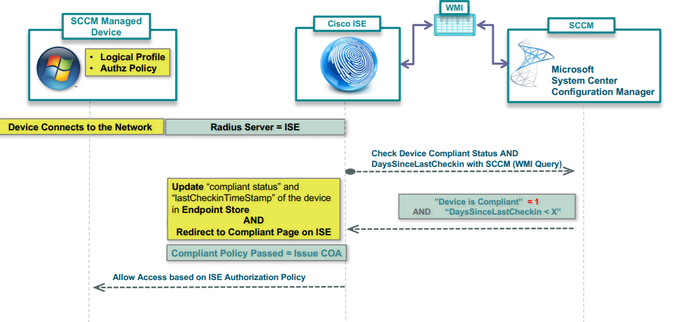
Figure 2
SCCM Workflow For MDM Flow
ISE is able to retrieve information from the SCCM server about whether a device is registered, and if it is registered, is it compliant. The following diagram shows the workflow for devices managed by SCCM.
Figure 3
When a device connects and a SCCM policy is matched, ISE queries the SCCM server specified in the authorization policy to retrieve compliance and last logon (check-in) time. With this information, ISE updates the compliance status and lastCheckinTimeStamp of the device in the Endpoint list.
If the device is not compliant or not registered with SCCM, and a redirect profile is used in the authorization policy, a message is displayed to the user that the device is not compliant or not registered with the SCCM. After the user acknowledges the message, ISE can issue a CoA to the SCCM registration site. Users can be granted access based on the authorization policy and profile.
SCCM Workflow for Patch Management
SCCM is the Microsoft’s Patch Management Solution,which manages patch updates on Microsoft endpoints. The SCCM server deploys a ‘Configuration Manager Client’ on the endpoints that it controls. This client is responsible for notifying the end-user that there are patches that are missing on endpoint. The client also lets the user install the patches that are deployed at the server.
The SCCM server does a Software Update Scan at configured intervals, which causes it to probe for the patch update status of the endpoints administered by the SCCM server. The SCCM server then notifies the SCCM client that there are patches/updates that need to install. (If there were patches uninstalled manually on client or there are new patches/updates deployed on the Software Update Groups on the SCCM server).
Design
ISE Integration with SCCM for MDM Flow
Communicating Ports
Microsoft SCCM and ISE uses TCP 135, TCP 445 to communicate with each other. This is to enable the communication over SMB port. However, SMB port can be disabled if the registry keys are added manually ( Step 3 in Deploy section )
Use Cases for ISE MDM support for SCCM
SCCM Integration supports the following use cases for Managed devices
- Managed Device which is NOT yet registered with SCCM Server
- Managed Device which is registered with SCCM Server but NON-Compliant
- Managed Device which is registered with SCCM Server and Compliant
Managed Device which is NOT yet registered with SCCM Server
Figure 4
Here is an example of a flow of managed device which is not registered with SCCM. When a Windows device connects to the network, ISE does a WMI query to SCCM server to check if the device is registered or not. SCCM server responds back with flag set to 0 indicating that the device is not registered. The endpoint can be notified about the registration status and can be redirected to register the device. From ISE, CoA( change of Authorization) is issued and appropriate policy is assigned to the endpoint.
Managed Device which is Non-Compliant 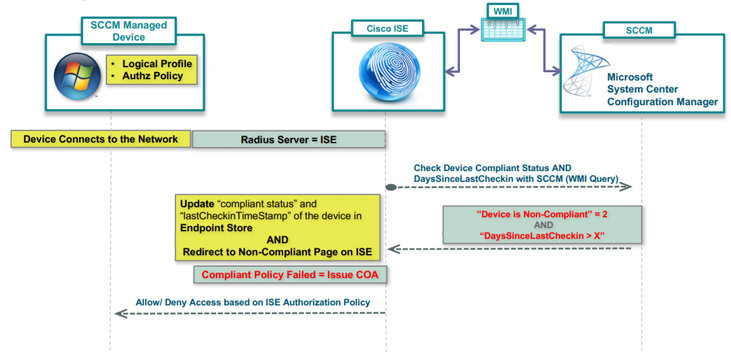
Figure 5
Here is an example of a flow of managed device which is registered with SCCM and is non-compliant.The device connects to the network. Once the the user is authenticated, ISE does a WMI query to SCCM server to check the ‘last checkin’ time-stamp and the compliant status based on the SCCM policy. SCCM server responds with the status as non-compliant. From ISE change of authorization is triggered and device is given limited access or blocked access.
Managed Device which is registered with SCCM server and Compliant
Figure 6
Here is an example of the flow of managed device which is registered with SCCM server and is Compliant. When a Windows endpoint connect to the network, ISE sends WMI query to SCCM server to check the status to the endpoint. SCCM server responds back with flag set to 1 if the device is compliant and days since last check in value. Based on this information, ISE triggers a CoA and assigns compliant access for the device.
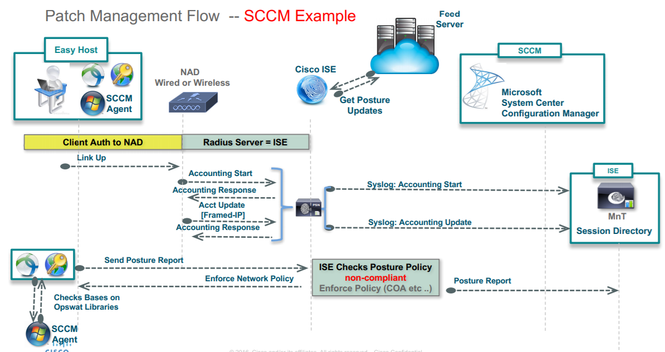
ISE Integration with SCCM for Patch Management
Figure 7
ISE 1.4 onwards, We have the ability to integrate with SCCM patch management solution to verify if the endpoint has any pending patch installations by Microsoft, as mentioned in the SCCM client.
In case if there are patches available for install in the SCCM client, Anyconnect client can trigger the SCCM client to install the patches before providing full network access to the endpoint.
Deploy
Preparing for ISE Integration with SCCM for MDM Flow
ISE communicates with the SCCM server using WMI. WMI must be configured on the Windows server running SCCM.
Configuration Changes on the Microsoft SCCM Server
This section covers the changes which are to be done in the Microsoft SCCM server.
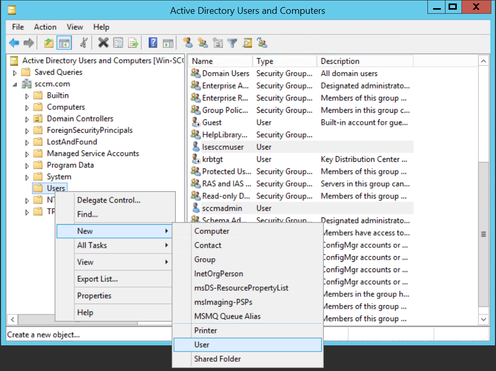
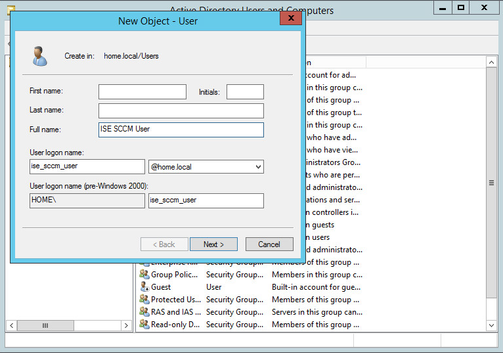
Step 1 Create a user within the Active Directory domain that will be used by ISE to communicate with SCCM and issue queries about the status of authenticating machines.
- Open Active Directory Users and Computers administrative tool.
- Right-click on the OU container where you want to create the new user and select the option to create a new user. You should see the following dialog box.
- Fill in the information as necessary. Select Next. In this example, we are using the “ise_sccm_user” logon name.
- Create a password that adheres to your organization’s security policy.
- Uncheck the option “User must change password at next logon”.
- Click Next.
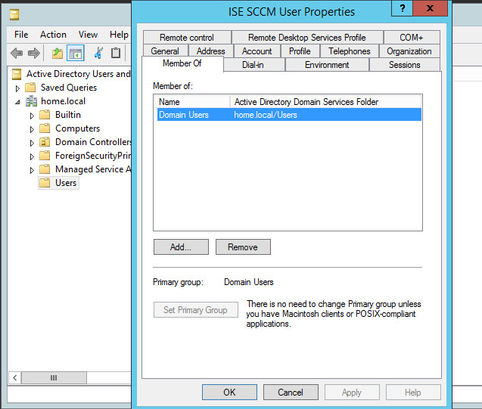
- The new user is now created. If you check the properties of the user, you will see that the user is only a member of the Domain Users security group in AD.
Figure 10
Step 2
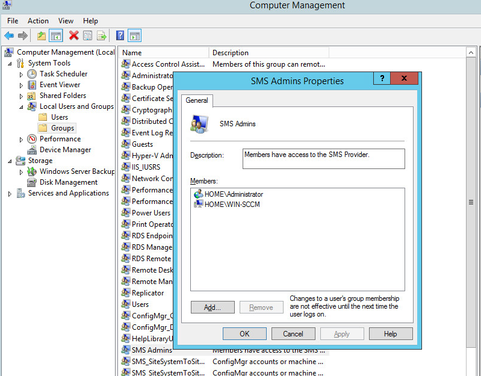
Add the new user created in Step 1 to the “SMS Admins” security group on the Microsoft SCCM Server.
On the SCCM Server, open the Computer Management administrative tool
- Select Local Users and Groups.
- Select Groups.
- Locate the “SMS Admins” security group.
Figure 11 - Double click on the “SMS Admins” security group. This will open up the dialog box showing which users and groups are a member of this local security group.
Figure 12 - We need to add the user created for ISE to this group. Select the “Add…” button.
Figure 13
- Ensure the location selected is the Active Directory domain. In this example, the domain name is “home.local”.
- Enter the logon name of the account created in Step 1 and then select the “Check Names” button. The user name should now be underlined, indicating that the server was able to locate the object in the AD domain.
- Select “OK”.
Figure 14
- You should now see that the new user is a member of the “SMS Admins” local security group.
- Click “Apply” and “OK” to save the settings and close the dialog box.
Figure 15
Step 3
Configure the Distributed Component Object Model (DCOM) to allow the new user to access, launch, and activate the objects remotely.
- On the SCCM Server, open Component Services administrative tool.
- In the left pane, expand “Component Services” and “My Computer”. You should see something similar to the screenshot below.
Figure 16
- Expand the “DCOM Config” section and there will be a long list of objects.
Manual configuration to add the registry keys in SCCM server. The steps below are needed if the SMB port is blocked. - You will need to do the following to make the registry keys to appear. These steps need to be done on the SCCM CAS/Primary server in which ISE is trying to connect to.
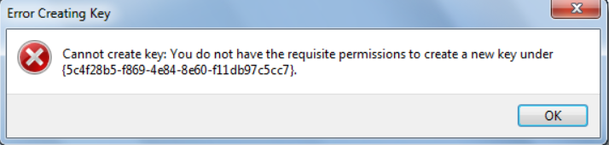
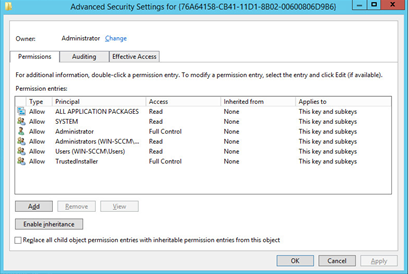
Adding permission to modify the registry keys
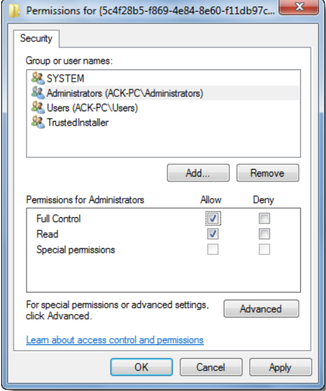
- The original owner of the registry keys is TrustedInstaller which will not allow you to make modifications to those keys. You will need to take ownership and grant yourself full control full access you can then modify the keys. These were the registry keys that had to be add/modified in order for the DCOM to appear. You will get below error if you do not have permissions.
- Close this error dialog box and right click on the registry key where you want to make the changes and click on Permissions.
- In the Permissions box, under its sole security tab, highlight your own Administrators account and then check the box under Full Control – Allow. Click Apply > OK.
If you see security warning – Unable to save permission changes, do the following. - Open the Permissions windows again and click on Advanced button instead, and click on the Owner tab.
- Do you see another owner like say, trustedInstaller? If so, change owner to your Name. Click Apply > OK.
NOW again in the Permissions box, under its sole security tab, highlight your own Administrators account and then check the box under Full Control – Allow. Click Apply > OK.
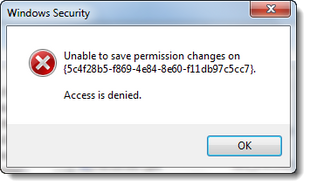
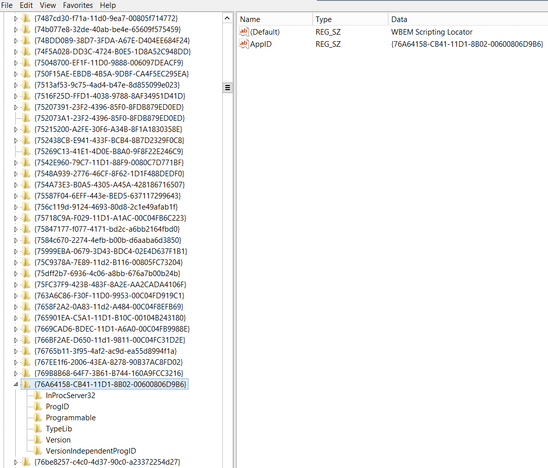
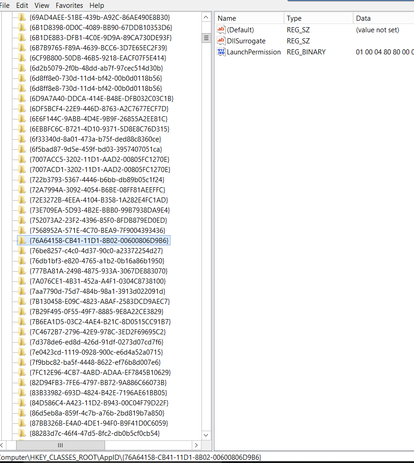
Adding the registry Keys
The information that you need to import into the registry is:
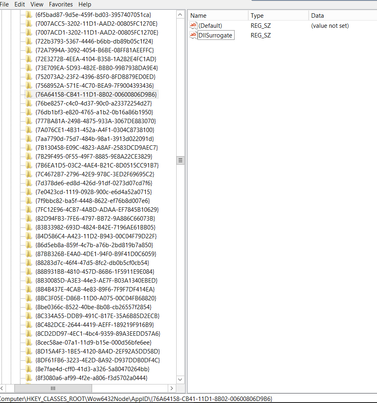
- [HKEY_CLASSES_ROOT\CLSID\{76A64158-CB41-11D1-8B02-00600806D9B6}]
"AppID"="{76A64158-CB41-11D1-8B02-00600806D9B6}" - [HKEY_CLASSES_ROOT\AppID\{76A64158-CB41-11D1-8B02-00600806D9B6}]
"DllSurrogate"=" "
Note: be sure you use 2 spaces above for the DllSurrogate value. - Manually add the key "{76A64158-CB41-11D1-8B02-00600806D9B6}" under AppID
- [HKEY_CLASSES_ROOT\Wow6432Node\AppID\{76A64158-CB41-11D1-8B02-00600806D9B6}]
"DllSurrogate"=" "
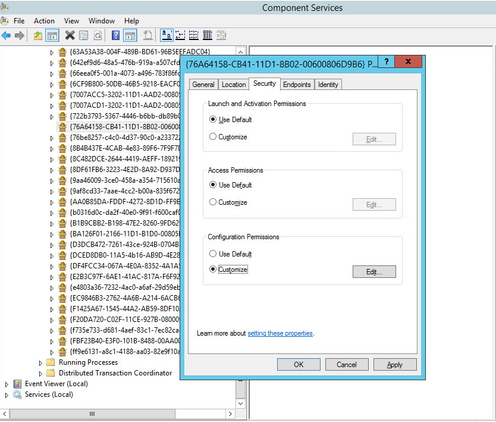
Here, you will have to manually add the key -\{76A64158-CB41-11D1-8B02-00600806D9B6} - Locate the object named “{76A64158-CB41-11D1-8B02-00600806D9B6}” as shown below.
Right-click on the object and select “Properties”. A dialog box will open.
Select the “Security” tab. - In the “Launch and Activation Permissions” section, select the “Customize” radio button.
- Now click on the “Edit…” button in that same section. Another dialog box will open showing the permissions.
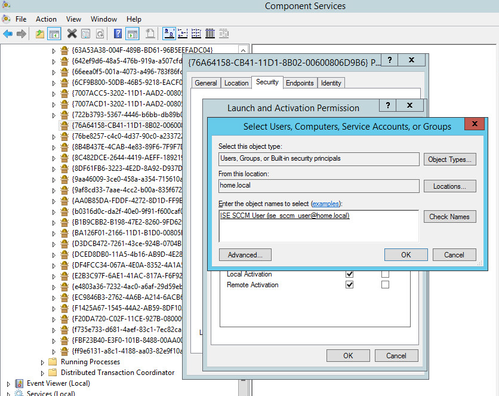
- Click the “Add…” button to add the new user for ISE.
- In the new dialog box, ensure that the location is set to the AD domain.
- Enter the new username created in Step 1 and select “Check Names”.
- Ensure that the username is found and is now underlined, indicating that the account is valid.
- Click “OK”.
- Now select “Allow” for all permissions while the new account is selected. The end result should look similar to the following screenshot.
Select “OK” on all dialog boxes.
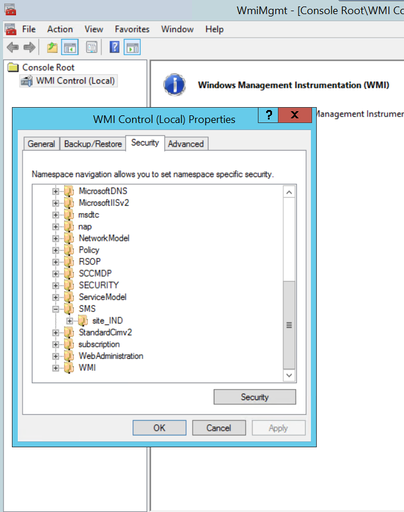
Step 4
By default, Active Directory users do not have permissions for the Execute Methods and Remote Enable. You can grant access using the wmimgmt.msc MMC console.
- Click Start > Run and type wmimgmt.msc.
- Right-click WMI Control and click Properties.
- Under the Security tab, expand Root and choose CIMV2.
- Click Security.
- Add the Active Directory user, and configure the required permissions as shown below.
Figure 29
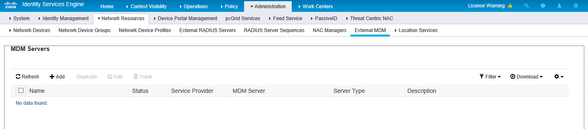
Adding SCCM server as MDM in ISE
Step 5
Configure ISE to connect to the SCCM server, test the connection, and add the SCCM server as an available MDM server in the ISE system.
- Login to the ISE Primary Admin node web interface
- Select Administration -> Network Resources -> External MDM
- Click on the “Add” button to add a new MDM server.
- The “Name” field can be any name you want to reference the MDM as when creating policies within ISE. The name cannot contain any spaces. In this example, we are using “sccm”.
- The “Server Type” must be set to “Desktop Device Manager” for SCCM.
- Enter the Fully Qualified Domain Name (FQDN) of the SCCM server or the IP address that is reachable from the ISE Admin node.
- For the “Site or Instance Name”, please use the SCCM Site Name.
- The username will be the user account that was created in Step 1. It is important to preface the username with the domain name. For example, “SCCM\Isesccmuser” where “SCCM” is the AD domain name.
- Enter the password for the user account created in Step 1.
- Select the “Test Connection” button at the bottom to test the connection to the SCCM server. If the connection is successful, you should see a dialog box stating it was successful
- Click the “OK” button on the success dialog.
- Change the “Status” to “Enabled”.
- Click “Submit” to add the new SCCM server to ISE as an MDM.
- Verify that you can see the SCCM server added to the MDM servers Page .
New MDM Attributes in ISE for SCCM server
- MDM.Server type: MDM (MobileDeviceManager), DM (DeviceManager)
- MDM.lastCheckinTimeStamp: last logon/checkin timestamp for device on SCCM
- MDM.DaysSinceLastCheckin: Number of days since user last checked in or synched the device with SCCM. Min value = 1, Max value=365 If user specifies a value outside this range an error will be displayed
- MDM.UserNotified: Yes/No – Indicates if user has been notified (about device not registered/not compliant) and acknowledged the message.
Policy Set Example:
The following table shows set of policies to support SCCM
Preparing for ISE Integration with SCCM for Patch Management Flow
Supported Versions
Patch Management posture conditions and remediation actions are supported with ISE 1.4 and above and AnyConnect 4.1.x and above.
Patch management Conditions
Installed Check
This check evaluates if supported patch management software client is installed.
The condition Passes when, finds a supported PM client software (as in support charts), installed on endpoint. Fails when, does not find a supported PM client software installed on endpoint
Enabled Check
This check evaluates if supported Patch Management client software is enabled
The condition Passes when it finds that supported patch management client services are running and Fails otherwise.
Up-to-date Check
This checks for the SCCM Client’s patch update status. The check passes when the SCCM client installed on the endpoint indicates that there are no pending patches/updates to be installed. The PM up-to-date check looks for patches (classified by Microsoft), missing on the endpoint.
The condition can be configured to check for All/ Critical and other categories of patches to be installed on the client.
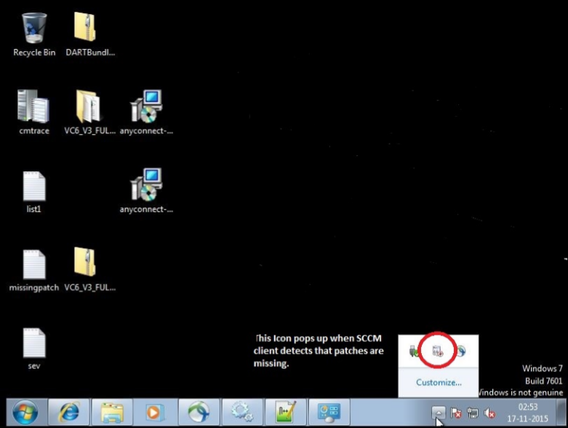
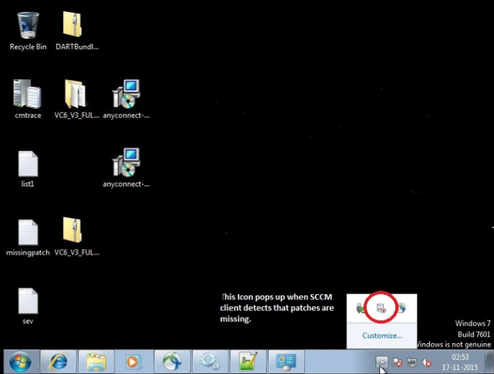
When SCCM client is notified by the SCCM server about the missing patches, it prompts user with the notification icon highlighted in the screenshot below.
The PM up-to-date check will deem the client COMPLIANT, if the SCCM Client does not have any notifications from SCCM server that there are patches pending for installation.
The PM check will deem the client NONCOMPLIANT, if the SCCM Client has got notifications from server that there are pending patches / updates for install and the user has not yet installed those critical patches.
Patch Management Remediation
Patch management remediation can be configured for Manual and Automatic remediation option.
Enable
Remediation action starts the required services for the supported PM client software.
Install Missing Patches
This directs the installed and supported PM client software, to download the patch or patches that were found while evaluating the PM condition.
Activate Patch Management Software GUI
Displays the patch management software user interface. Follow the instructions on this page to change the software settings or initiate software updates.
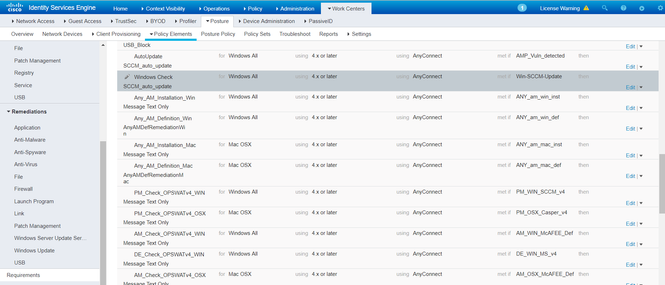
Configuration steps for Patch Management condition and Remediation action on ISE
Step 1
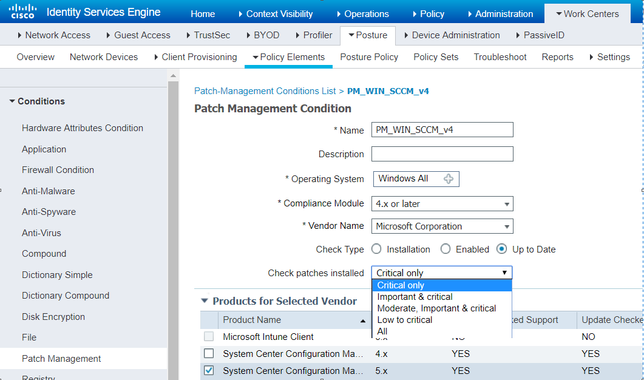
Go to Workcentre-> Posture-> Policy Elements-> Condition-> Patch management. Add a patch management condition to check for up-to-date patch status. This conditions checks if there are any pending patches to be installed in the SCCM client.
Figure 35
Step 2
Create a Patch Management Remediation action to trigger the SCCM remediation if the condition configured in step 1 fails. Go to Workcentre-> Posture-> Policy Elements-> Remediation-> Patch Management to create the remediation action. Select the appropriate SCCM client version installed on the client. The screenshot below is the remediation action for any pending critical patches. 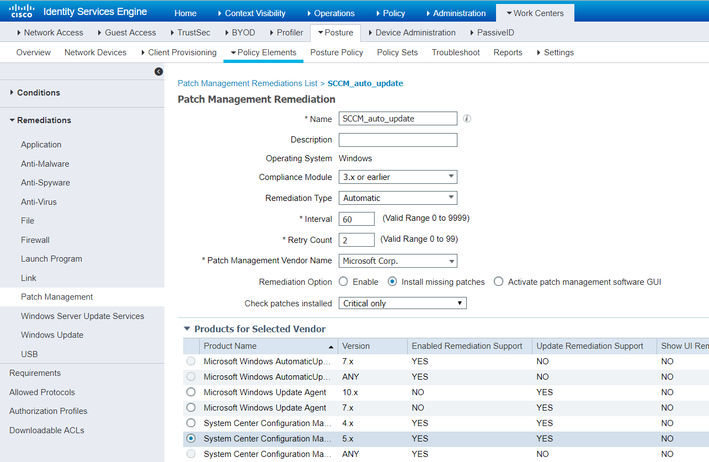
Step 3
Create a requirement for the condition and remediation action created.
Figure 37
Step 4
Create a Posture Policy to enforce it for Windows endpoints.
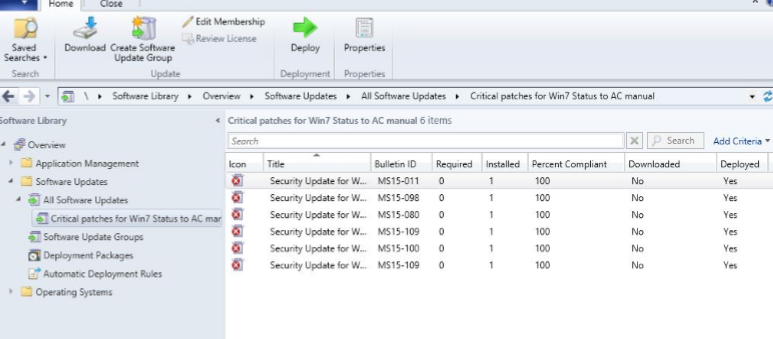
Steps to Validate the Patch Management solution with ISE
Step 1
On the SCCM server, configure a software update group containing at least 1 CRITICAL patch from Microsoft for the target endpoints. And deploy this software update group for target group of computers. Please refer to screenshot below.
Figure 38
Step 2
On the endpoint, verify that SCCM client has missing patches, at least 1 CRITICAL patch should be missing for AnyConnect to remediate the SCCM client. Please note that the popup is shown only when SCCM clients detects missing patches on end point.
Figure 39
Step 3
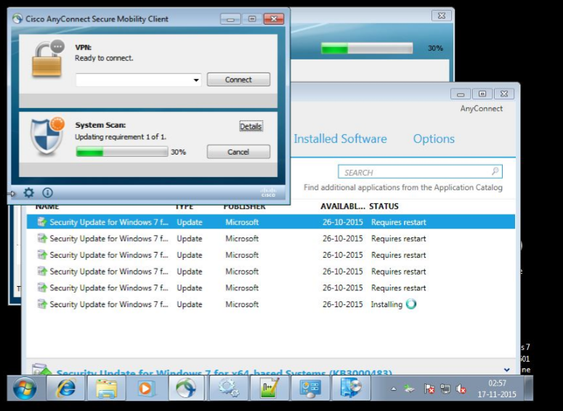
At this point install Anyconnect (VPN and System Scan Modules), and connect to NAD, which is managed by ISE server on which Patch management policy is enforced.
Step 4
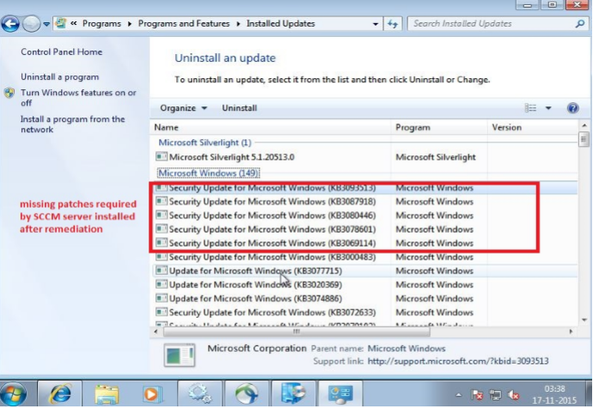
At this instant, remediation is triggered by AnyConnect ‘System Scan’ component and in the process SCCM client downloads the missing critical patches required by the SCCM server’s Software update group.
Step 5
If a reboot is required after remediation to complete, please reboot the endpoint. Windows pop will show up on the taskbar indicating that a Reboot is required to update patches.
Note: Unless the system is rebooted the check for up-to-date patches will fail, and system scan will show Non-Compliant after the remediation timer expires, if reboot is still pending.
After reboot, when Anyconnect connects back to NAD, it evaluates the PM condition for ‘up-to-date’ checks again and finds all patches required my SCCM installed on endpoint. At this point the Patch management condition passes and endpoint is deemed compliant. Please refer to screen shots below.
Figure 41
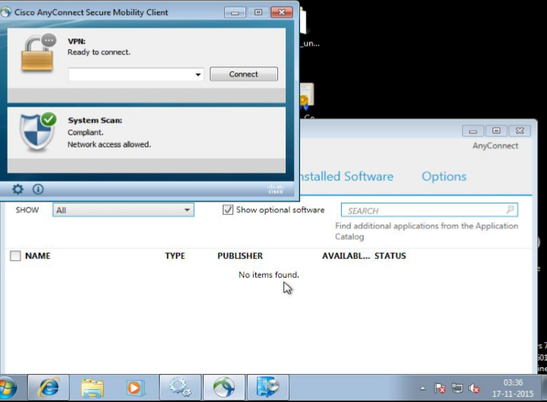
Figure 42
Operate
Troubleshooting
SCCM MDM Flow Troubleshooting
Review of the integration flows
From the flow level perspective, initial SCCM connection may occur in two different ways:
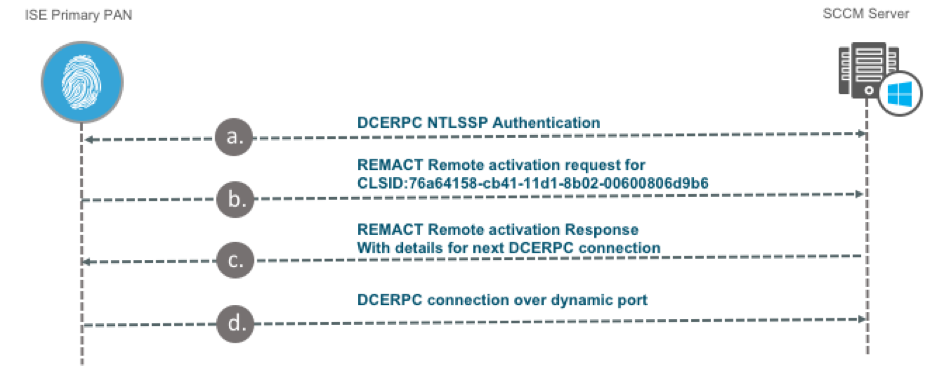
- Initial connection which does not involve SMB communication. This flow happens when all configuration changes described in the section 'Configuration Changes on the Microsoft SCCM Server' are implemented. This flow is optimal, and we encourage administrators to follow this guide precisely.
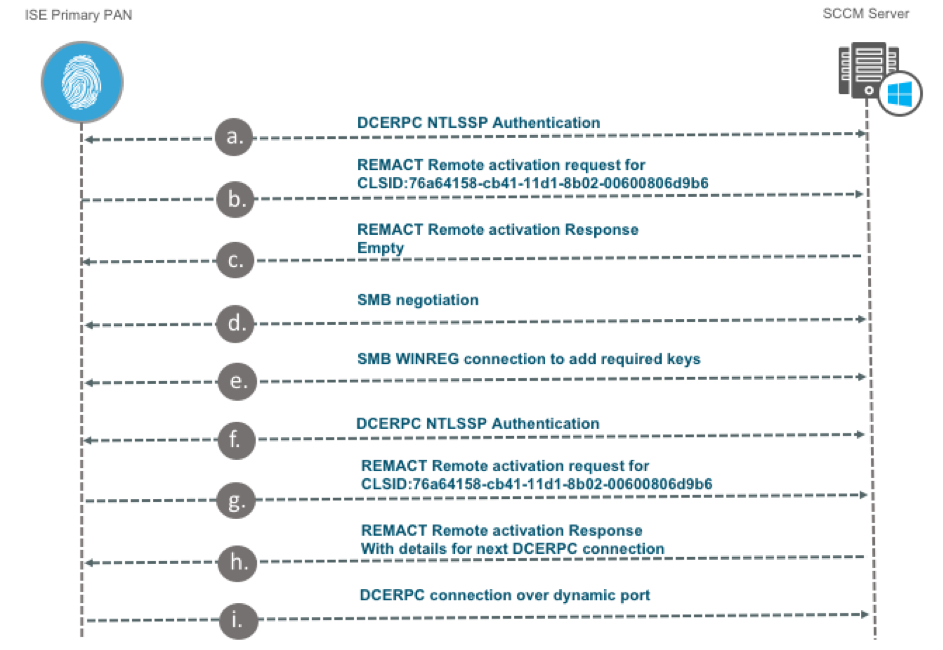
- Initial connection which involves SMB communication between ISE and SCCM server for remote registry keys creation.
Note: Due to limitation described in CSCvf23341 this flow can only happen when SCCM server has SMBv1 enabled.
Diagram below provides high-level overview of SCCM flow without going into the details of TCP/IP or application layer exchanges. See section – ‘Use packet capture for troubleshooting’ for more detailed overview of the actual exchanges.
Integration flow without SMB
Figure 43
a. NTLMSSP authentication during DCERPC connection establishment with credentials specified in the MDM server settings.
b.Remote activation call to the CLSID object - 76a64158-cb41-11d1-8b02-00600806d9b6 to establish separate DCOM session for WMI queries.
c. Response to the activation request. If required keys are present in the system and have right permissions this response contains details required for the second connection (like port number for example). If the keys are not presented then response is empty and second diagram applies.
d. DCERPC connection inside of which actual WMI queries are executed.
Note: While on the diagram itself Primary PAN is mentioned we need to keep in mind that after connection is configured on the PAN, MDM server details are placed into the ISE configuration database and distributed to all nodes in the deployment. All PSNs establish a separate connection to the SCCM server. When authentication request hits the PSN, query is send from the PSN to the SCCM server.
Integration flow with SMB
Figure 44
a.NTLMSSP authentication during DCERPC connection establishment with credentials specified in the MDM server settings.
b. Remote activation call to the CLSID object - 76a64158-cb41-11d1-8b02-00600806d9b6 to establish separate DCOM session for WMI queries.
c. Empty response to the activation call which instructs ISE to attempt and SMB connection attempt.
d. SMB negotiation. This step is successful only in the environments where SMBv1 is enabled/allowed.
e. ISE over SMB WINREG creates Registry keys required for integration. For this step to be successful the following minimum requirements needs to be in place:
- Account which is used for integration has a right permission to HKEY_CLASSES_ROOT\CLSID\{76A64158-CB41-11D1-8B02-00600806D9B6}.
- DCOM permission are defined like specified in the guide.
f. - i. Steps represent the same operations which are executed in the steps a. – d. of the previous flow.
Testing ISE WMI query directly on the SCCM server
There is a possibility to create a customer query on the SCCM and execute it manually. This is useful for troubleshooting issues with endpoint registration and compliance.
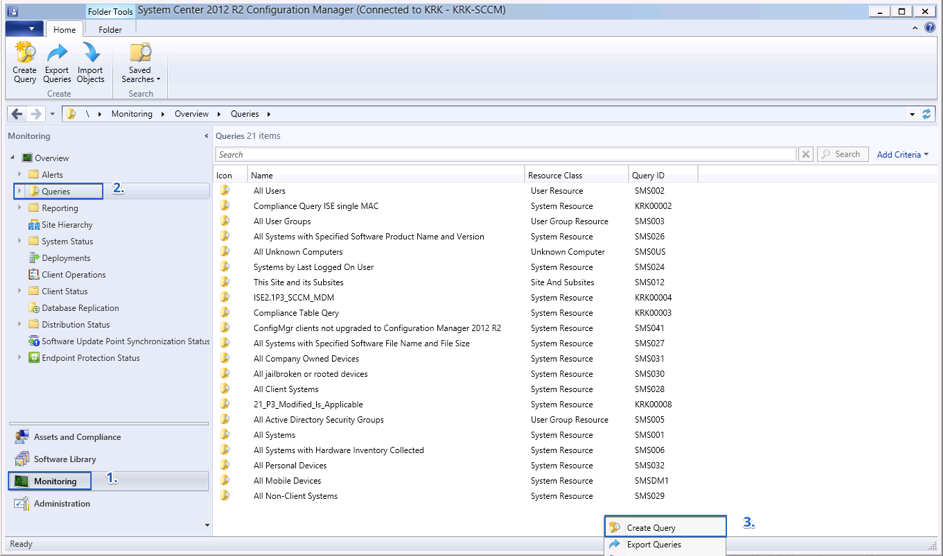
To create custom query launch Configuration Manager Console
Figure 45
Navigate to Monitoring (1) > Queries (2) > Do a right-click and select ‘Create Query’
Figure 46
In new window specify the query name (1) > and select ‘Edit Query Statement’ (2)
Figure 47
In a new window press on ‘Show Query Language’ (1), In next windows paste your query statement (2), press ‘OK’ (3) and follow the wizard by pressing ‘Next’

Figure 48 Figure 49
WMI query which is executed by ISE:
select SMS_R_System.Name,
SMS_G_System_CI_ComplianceState.CI_UniqueID,
SMS_G_System_CI_ComplianceState.ComplianceState,
SMS_G_System_CI_ComplianceState.LocalizedDisplayName,
SMS_G_System_CH_ClientSummary.LastPolicyRequest from
SMS_R_System left join SMS_G_System_CI_ComplianceState on
SMS_G_System_CI_ComplianceState.ResourceID = SMS_R_System.ResourceId left join
SMS_G_System_CH_ClientSummary on SMS_G_System_CH_ClientSummary.ResourceID = SMS_R_System.ResourceId left join
SMS_G_System_NETWORK_ADAPTER on SMS_G_System_NETWORK_ADAPTER.ResourceId = SMS_R_System.ResourceId where SMS_R_System.MacAddresses like '%64:31:50:10:DA:60%' OR
SMS_G_System_NETWORK_ADAPTER.MACAddress like '%64:31:50:10:DA:60%'
MAC address which we see in the query is taken by ISE from the Calling-Station-ID attribute which ISE gets from the radius packet during authentication. For the devices with multiple NICs it's important to ensure that all MAC addresses are presented in the SCCM database.
Original query needs to be adjusted a little bit to be used with SCCM:
select SMS_R_System.Name,
SMS_G_System_CI_ComplianceState.CI_UniqueID,
SMS_G_System_CI_ComplianceState.ComplianceState,
SMS_G_System_CI_ComplianceState.LocalizedDisplayName,
SMS_G_System_CH_ClientSummary.LastPolicyRequest from
SMS_R_System left join SMS_G_System_CI_ComplianceState on
SMS_G_System_CI_ComplianceState.ResourceID = SMS_R_System.ResourceId left join
SMS_G_System_CH_ClientSummary on SMS_G_System_CH_ClientSummary.ResourceID = SMS_R_System.ResourceId left join
SMS_G_System_NETWORK_ADAPTER on SMS_G_System_NETWORK_ADAPTER.ResourceId = SMS_R_System.ResourceId where SMS_R_System.MacAddresses=##PRM:SMS_R_System.MACAddresses## OR
SMS_G_System_NETWORK_ADAPTER.MACAddress=##PRM:SMS_G_System_NETWORK_ADAPTER.MACAddress##
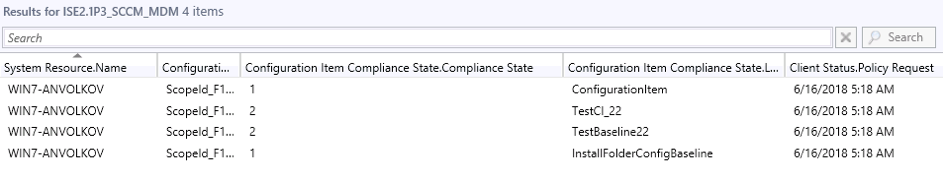
When this query is executed same MAC address needs to be specified two times. Below is an example of query result:
Figure 50
Third column contains compliance status for each element. Microsoft defines the following values for the compliance status:
|
0 |
Compliance State Unknown |
|
1 |
Compliant |
|
2 |
Non-Compliant |
|
4 |
Error |
ISE marks endpoint as compliant only if all values in this column are equal to 1.
Testing the connection to SCCM server manually
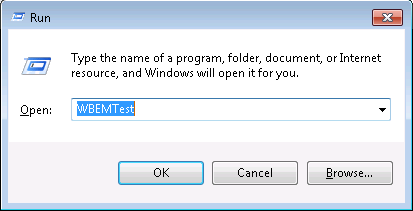
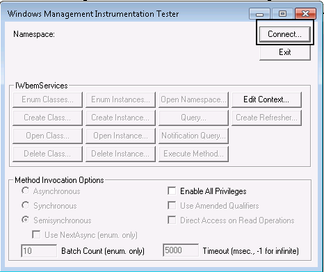
Windows has WBEMTest tool for WMI calls testing, which is built in Windows utility and is extremely useful for permissions and network troubleshoot.
Step 1
Figure 51
Step 2
Figure 52
Step 3
Figure 53
Step 4
Figure 54
Troubleshooting Connectivity Issues from ISE to SCCM server
Step 1 Collecting Packet capture
Enable Packet Capture from ISE from Operations- Troubleshoot as below-
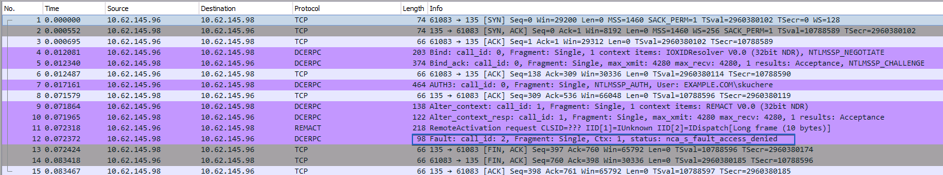
Step 2 Analyzing packet capture
Issue 1 wrong credentials:
SCCM server replies with nca_s_fault_access_denied when wrong credentials were provided.
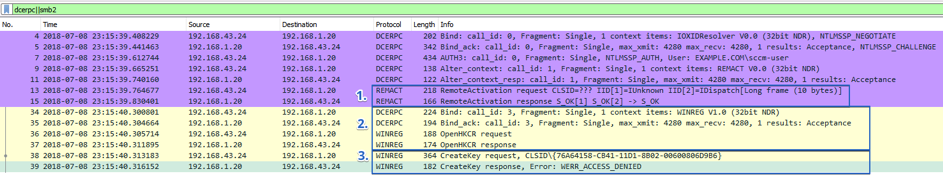
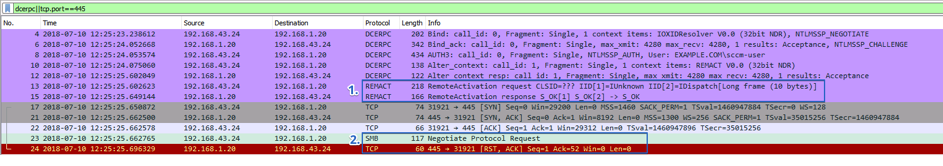
Issue 2 no access to registry keys
When correct credentials provided during Activation call and ISE gets an empty response from Server (1), this triggers WinReg SMB connection. If registry key –
HKEY_CLASSES_ROOT\CLSID\{76A64158-CB41-11D1-8B02-00600806D9B6} does not have required permissions WinReg connection fails with WERR_ACCESS_DENIED (3)
Issue 3 SMB connection is failing
Working with ISE debugs
To get visibility into communication between ISE and SCCM server the following component needs to be enabled into TRACE on ISE:
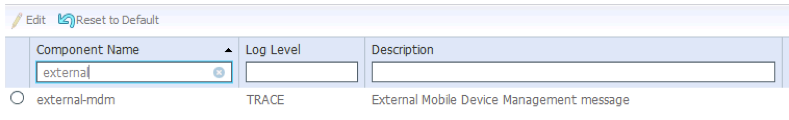
Figure 61
Logging level can be changed by navigating to Administration > System > Logging > Debug Log Configuration
During the node selection, choose Primary PAN node if you need to troubleshoot initial connection. When issues are seen with actual authentications, logging level needs to be changed on the PSN where endpoints are authenticated.
External-MDM component writes logs into the ise-psc.log, all logs related to the MDM operation can be easily filtered by the ‘cpm.mdm’
Below are couple of examples of the logs.
Endpoint is not presented on the SCCM:
2016-09-06 13:04:11,496 DEBUG [Thread-101][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- using default MDM server SCCM to get the MDM info data)
2016-09-06 13:04:11,692 TRACE [Thread-101][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - start query: SELECT SMS_R_System.Name, SMS_G_System_CI_ComplianceState.CI_UniqueID, SMS_G_System_CI_ComplianceState.ComplianceState, SMS_G_System_CI_ComplianceState.LocalizedDisplayName, SMS_G_System_CH_ClientSummary.LastPolicyRequest from SMS_R_System inner join SMS_G_System_CI_ComplianceState on SMS_R_System.ResourceId = SMS_G_System_CI_ComplianceState.ResourceID inner join SMS_G_System_CH_ClientSummary on SMS_R_System.ResourceId = SMS_G_System_CH_ClientSummary.ResourceId where SMS_R_System.MacAddresses like '%C0:4A:00:21:42:27%', keyproperty: SMS_G_System_CI_ComplianceState@CI_UniqueID
2016-09-06 13:04:11,788 TRACE [Thread-101][] cpm.mdm.sccm.util.WmiUtil -::::- WmiUtil - executeQuery - last element - Incorrect function. [0x00000001]
2016-09-06 13:04:11,788 TRACE [Thread-101][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - end
2016-09-06 13:04:11,788 DEBUG [Thread-101][] cpm.mdm.sccm.api.SccmClient -::::- Device with mac: C0-4A-00-21-42-27 formatted mac C0:4A:00:21:42:27 does not exist in SCCM server: SCCM
Endpoint is not compliant on SCCM:
2016-09-09 12:51:49,313 DEBUG [Thread-103][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MDM PIP got device info from EP DB: session 0a3e94660000381d57d2943e + C0-4A-00-21-42-27
2016-09-09 12:51:49,313 DEBUG [Thread-103][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MDM PIP returns for endpoint sessionId 0a3e94660000381d57d2943e and macAddr C0-4A-00-21-42-27
2016-09-09 12:51:49,313 TRACE [Thread-103][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MDM PIP for attribute: MDM.DeviceRegisterStatus, returned: {MDM.MDMServerName=SCCM, MDM.MDMServerReachable=true, MDM.Model=, MDM.compliance=[Ljava.lang.String;@62f9d789, MDM.DeviceRegisterStatus=false, MDM.PinLockStatus=false, MDM.Provider=false, MDM.SerialNumber=, MDM.LastCheckInTimeStamp=0, MDM.register_url=N/A, MDM.IMEI=, MDM.DiskEncryptionStatus=false, MDM.ServerType=DesktopDeviceManager, MDM.OsVersion=null, MDM.PhoneNumber=, MDM.UDID=, MDM.JailBrokenStatus=false, MDM.UserNotified=true, MDM.MEID=, MDM.DaysSinceLastCheckin=0, MDM.Manufacturer=, MDM.DeviceCompliantStatus=false, MDM.MDMFailureReason=, MDM.query_attribute=MDM.DeviceRegisterStatus}
2016-09-09 12:51:49,702 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - start query: SELECT SMS_R_System.Name, SMS_G_System_CI_ComplianceState.CI_UniqueID, SMS_G_System_CI_ComplianceState.ComplianceState, SMS_G_System_CI_ComplianceState.LocalizedDisplayName, SMS_G_System_CH_ClientSummary.LastPolicyRequest from SMS_R_System inner join SMS_G_System_CI_ComplianceState on SMS_R_System.ResourceId = SMS_G_System_CI_ComplianceState.ResourceID inner join SMS_G_System_CH_ClientSummary on SMS_R_System.ResourceId = SMS_G_System_CH_ClientSummary.ResourceId where SMS_R_System.MacAddresses like '%C0:4A:00:21:42:27%', keyproperty: SMS_G_System_CI_ComplianceState@CI_UniqueID
2016-09-09 12:51:50,381 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WMI query returned - key: ScopeId_F1E07ECF-7DE2-493C-92FD-3BAEE9C060A5/Baseline_a2ee9124-26a1-448a-9d6c-76fd7a757672, values: {LastPolicyRequest=20160909090359.000000+000, LocalizedDisplayName=Compliance Policy, ComplianceState=2, Name=WIN7-SKUCHERE}
2016-09-09 12:51:50,391 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WMI query returned - key: ScopeId_F1E07ECF-7DE2-493C-92FD-3BAEE9C060A5/OperatingSystem_7bd09415-a9b4-4655-bdea-d585d19b6e7a/1, values: {LastPolicyRequest=20160909090359.000000+000, LocalizedDisplayName=Compliance, ComplianceState=2, Name=WIN7-SKUCHERE}
2016-09-09 12:51:50,400 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WMI query returned - key: ScopeId_F1E07ECF-7DE2-493C-92FD-3BAEE9C060A5/OperatingSystem_7bd09415-a9b4-4655-bdea-d585d19b6e7a/2, values: {LastPolicyRequest=20160909090359.000000+000, LocalizedDisplayName=Compliance, ComplianceState=2, Name=WIN7-SKUCHERE}
2016-09-09 12:51:50,452 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WmiUtil - executeQuery - last element - Incorrect function. [0x00000001]
2016-09-09 12:51:50,452 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - end
2016-09-09 12:51:50,656 TRACE [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.api.SccmClient -::::- SCCM returned device with compliance state: false, checkinTime: 1452326639000, failureReason: Compliance, Compliance, Compliance Policy
2016-09-09 12:51:50,656 DEBUG [MdmEventHandler-46-thread-2][] cpm.mdm.sccm.api.SccmClient -::::- Found device with mac: C0-4A-00-21-42-27 formatted mac C0:4A:00:21:42:27 in SCCM server: SCCM
2016-09-09 12:51:50,665 INFO [Thread-76][] ise.sxp.sessionbinding.handler.SxpSessionNotifier -::::- Inside notifyAddedSession() - thread : Thread-76, sessionId = 0a3e94660000381d57d2943e , sessState = ACCEPTED, ipAddress = , sgTag = null , nasIpAddress = 10.62.148.102
Endpoint is registered and compliant:
2018-12-03 15:47:27,166 DEBUG [Thread-1691][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MACaddressIfDoesnotExistOrValid - MAC address is valid, no need to update, returning actual: C0-4A-00-15-6C-C3
2018-12-03 15:47:27,166 DEBUG [Thread-1691][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MDM PIP returns for endpoint sessionId 0a3e9498000000555c054226 and macAddr C0-4A-00-15-6C-C3
2018-12-03 15:47:27,167 TRACE [Thread-1691][] cisco.cpm.mdm.pip.MdmPartnerPIPHandler -::::- MDM PIP for attribute: MDM.DeviceCompliantStatus, returned: {MDM.MDMServerName=SCCM, MDM.MDMServerReachable=true, MDM.compliance=[Ljava.lang.String;@4e6d916e, MDM.PinLockStatus=false, MDM.register_url=N/A, MDM.IMEI=, MDM.DiskEncryptionStatus=false, MDM.ServerType=DesktopDeviceManager, MDM.OsVersion=, MDM.PhoneNumber=, MDM.UserNotified=false, MDM.Manufacturer=, MDM.DeviceCompliantStatus=true, MDM.Model=, MDM.DeviceRegisterStatus=true, MDM.Provider=false, MDM.SerialNumber=, MDM.LastCheckInTimeStamp=0, MDM.macaddress=C0:4A:00:15:6C:C3, MDM.UDID=, MDM.JailBrokenStatus=false, MDM.MEID=, MDM.DaysSinceLastCheckin=0, MDM.MDMFailureReason=, MDM.query_attribute=MDM.DeviceCompliantStatus}
2018-12-03 15:47:27,741 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - start query: select SMS_R_System.Name, SMS_G_System_CI_ComplianceState.CI_UniqueID, SMS_G_System_CI_ComplianceState.ComplianceState, SMS_G_System_CI_ComplianceState.LocalizedDisplayName, SMS_G_System_CH_ClientSummary.LastPolicyRequest from SMS_R_System left join SMS_G_System_CI_ComplianceState on SMS_G_System_CI_ComplianceState.ResourceID = SMS_R_System.ResourceId left join SMS_G_System_CH_ClientSummary on SMS_G_System_CH_ClientSummary.ResourceID = SMS_R_System.ResourceId left join SMS_G_System_NETWORK_ADAPTER on SMS_G_System_NETWORK_ADAPTER.ResourceId = SMS_R_System.ResourceId where SMS_R_System.MacAddresses like '%C0:4A:00:15:6C:C3%' OR SMS_G_System_NETWORK_ADAPTER.MACAddress like '%C0:4A:00:15:6C:C3%', keyproperty: SMS_G_System_CI_ComplianceState@CI_UniqueID
2018-12-03 15:47:28,146 INFO [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- Since Unique ID is empty generating Random key to update data.
2018-12-03 15:47:28,214 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- WMI query returned - key: 1543848448146, values: {LastPolicyRequest=20181126160149.000000+000, LocalizedDisplayName=Domain-Memebers-Baseline, ComplianceState=1, Name=SKUCHERE-WIN10}
2018-12-03 15:47:28,235 INFO [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- Since Unique ID is empty generating Random key to update data.
2018-12-03 15:47:28,281 INFO [Thread-30][] com.cisco.epm.util.NodeCheck -::::- Inside confirmAndDemoteIfNotPrimary
2018-12-03 15:47:28,283 INFO [Thread-30][] api.services.persistance.dao.DistributionDAO -::::- In DAO getRepository method for HostConfig Type: PAP
2018-12-03 15:47:28,285 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- WMI query returned - key: 1543848448235, values: {LastPolicyRequest=20181126160149.000000+000, LocalizedDisplayName=Domain-Memeber-Registry, ComplianceState=1, Name=SKUCHERE-WIN10}
2018-12-03 15:47:28,288 INFO [Thread-30][] com.cisco.epm.util.NodeCheck -::::- Now checking against secondary pap skuchere-ise23-2nat
2018-12-03 15:47:28,288 INFO [Thread-30][] com.cisco.epm.util.NodeCheckHelper -::::- inside getHostConfigRemoteServer
2018-12-03 15:47:28,290 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- WmiUtil - executeQuery - last element - Incorrect function. [0x00000001]
2018-12-03 15:47:28,290 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.util.WmiUtil -::::- WMI Client executeQuery - end
2018-12-03 15:47:28,316 TRACE [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.api.SccmClient -::::- SCCM returned device with compliance state: true, checkinTime: 1516978909000, failureReason:
2018-12-03 15:47:28,316 DEBUG [MdmEventHandler-50-thread-1][] cpm.mdm.sccm.api.SccmClient -::::- Found device with mac: C0-4A-00-15-6C-C3 formatted mac C0:4A:00:15:6C:C3 in SCCM server: SCCM
2018-12-03 15:47:28,320 DEBUG [MdmEventHandler-50-thread-1][] cisco.cpm.mdm.util.MDMUtil -::::- Processing updateEndpoint: C0-4A-00-15-6C-C3
2018-12-03 15:47:28,324 DEBUG [MdmEventHandler-50-thread-1][] cisco.cpm.mdm.util.MDMUtil -::::- updating device mdm attributes - mdmServer id: 4e582630-bfd1-11e8-84f4-000c291d059d in endpoint
2018-12-03 15:47:28,325 DEBUG [MdmEventHandler-50-thread-1][] cisco.cpm.mdm.util.MDMUtil -::::- updating device mdm attributes - mdmServer name: SCCM in endpoint
SCCM Patch Management Flow Troubleshooting
SCCM Logs to Monitor
C:\Windows\CCM\Logs\ScanAgent.log (Scan requests for software updates)
C:\Windows\CCM\Logs\WUAHandler.log (Status of patch installation)
C:\Windows\CCM\Logs\UpdatesStore.log ()patch details that are being installed during remediation)
Some of the IOS show and debugging commands that are handy to understand and troubleshoot ISE operations are as follows:
- show running-config aaa
- show authentication sessions
- show dot1x all
- show epm statistics mac <MAC_Address>
- show aaa servers
- show device-sensor cache all
- debug radius
- debug radius authentication
- debug dot1x all
- debug epm all
- debug mab all
- debug eap events
ISE Troubleshooting
Refer the following links for details on ISE troubleshooting:
- How To: Troubleshoot ISE Failed Authentications & Authorizations
- Troubleshoot and Enable Debugs on ISE
- Troubleshooting Cisco's ISE without TAC
- Troubleshooting TechNotes
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Very well done!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Nice work - question: is the MDM/SCCM integration on ISE required? Can it be used without it to still validate if patches are missing? Per TAC - the whole MDM integration wasn't needed for patch validation. So that once anyconnect client with posture module connects via VPN, ISE will wait for client to talk to SCCM server and if it detects that the client received missing patches pop-out it'll react.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Anyconnect integration is with SCCM as a posture agent check where
MDM has nothing to do with anyconnect. It runs as its own app. You need to integrate MDM with ISE if you want to do enforcement and segmentation. Example if unenrolled/quarantine due to missing patches then limit access. This requires communication between ISE and the MDM to pass the attributed to setup associated authorization rules
https://community.cisco.com/t5/security-documents/how-to-integrate-cisco-ise-with-microsoft-sccm-for-patch/ta-p/3725035
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Adding to what Jason says,
Patch management flow is part of Posture. and as you mentioned, if the patch management condition is configured, anyconnect agent checks with SCCM client in endpoint to verify the missing patches and triggers the install.
With MDM flow, you can check the compliance of an endpoint based on the checks configured in SCCM server and authorize the user for appropriate access accordingly. Here ISE directly queries the SCCM server.
so 2 different use cases. you do not need to integrate SCCM server for MDM flow to use the patch management flow.
Thanks,
Nidhi
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great - thank you for your comments/feedback and clarification. As a follow up to the SCCM/ISE (without MDM) use case, will ISE posture/anyconnect client actually trigger the client to CHECK with SCCM during posture unknown state OR does it solely rely on the client's ability to check (pending what GPO / how often timer is configured).
Use case 3: patching based on 'registry key' . Possible to check patch based on registry value key and then have remediation install ALL missing patches? Would this work or again - based on my 1st comment - can ISE anyconnect client trigger sccm client to check with sccm server because its missing certain condition (in this case reg key for patch).
Thank you.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Anyconnect posture agent solely depend on what the SCCM client shows as pending. It cannot recheck with SCCM server. if the client shows no patch as pending , the posture status will be compliant.
Registry check is a seperate check and cannot be clubbed with SCCM patch management check. You can create registry conditions to check for an existing key/value.
Thanks,
Nidhi
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Nevermind - had some trouble with modifying registry keys - but got it to work after all.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @Nidhi,
Thank you so much for the very detailed article. If I may, I wanted to confirm that I fully understand the solution.
1) Are the MDM Flow and Patch Management Flow 2 separate solutions, so I could configure just one or the other?
2) According to a comment response you made earlier, it seems that the Patch Management Flow will rely on what the client knows. Therefore, if a client is disconnected from the network in a compliant state and some time later is reconnected without having gotten any updates since, the client would still report that it is compliant and be allowed to connect to the network? If this is true, the MDM Flow solution seems to be the more secure option?
@Nidhi wrote:
Anyconnect posture agent solely depend on what the SCCM client shows as pending. It cannot recheck with SCCM server. if the client shows no patch as pending , the posture status will be compliant.
3) For the MDM Flow solution, is there any more detailed documentation with regards to the final step of configuring policies specific to SCCM integration?
Thank you again for your support!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Well done!
Cisco should integrate this great job in his official documentation.
I just need a clarification
When you say
Manual configuration to add the registry keys in SCCM server. The steps below are needed if the SMB port is blocked.
do you mean that if SMB traffic between PAN e SCCM server is enabled all the subsequent stuff about registry keys (points 4 to 12) can be ignored ?
Do you think that with SCCM integration one can get rid of MAR?
Think of a network on which all windows machine use native supplicant with default configuration (PEAP MSCHAV2 with machine and user authentication). In this scenario we use MAR to try to understand whether a PAEP/MSHAPv2 authentication is coming from a corporate windoes endpoint. Maybe "WasMachineAuthenticaed=true" condition could be replace by "DeviceRegisterStatus=registered"?
Regards
MM
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
All,
is it normal for SCCM to take up to 20 mins to update on the endpoint compliance status?
Anyconnect denies access to users who are already updated due to the status update delay on SCCM.
Anyone facing the same?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
All,
I know the MDM flow and PM is a separate use case. So my doubt is:
What best practices for creating the policy sets between MDM Flow and Anyconnect posture? What i check first, the MDM FLOW or Posture FLow, or create all in the same rule?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@Nidhi Does this capability require the premier license in ISE 3.x? or is it included in essentials or advantage?
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: