- Cisco Community
- Technology and Support
- Networking
- Switching
- Configuring the Router to connect to ASA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 08:29 AM - edited 03-07-2019 07:59 AM
We are planning to install a new ASA Firewall. Currently the Router is connected to the internet Gateway and to 3 switches which are in 3 different networks
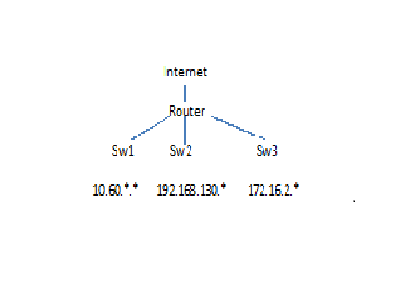
Router interfaces are 10.60.1.1 , 192.168.130.1, 172.16.2.1
Now it is going to be
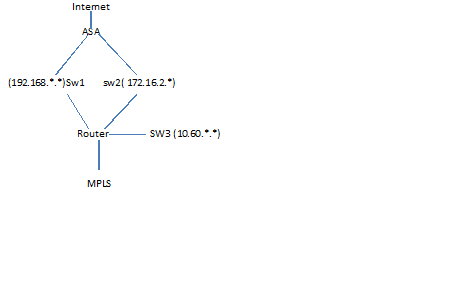
ASA interfaces will be 192.168.30.1, 172.16.2.1 and Router interfaces will be 192.168.130.2 and 172.16.2.2
1. currently the defult gateway on the router is configured as 0.0.0.0 0.0.0.0 220.*.*.*
I will be moving the default gateway to ASA
How do I configure the route on the Router ? will it be 0.0.0.0 0.0.0.0 192.168.130.1 OR 0.0.0.0 0.0.0.0 172.16.2.1
2. Currently the interfaces on the Router are configured as follows
interface GigabitEthernet0/0
description LAN
ip address 192.168.130.1 255.255.255.0
ip access-group col-in in
no ip redirects
no ip proxy-arp
ip accounting output-packets
ip nat inside
ip inspect SDM_L out
ip virtual-reassembly in
duplex auto
speed auto
media-type rj45
no mop enabled
service-policy output manage-gnet-bandwidth-out
!
interface GigabitEthernet0/1
description DMZ LAN
ip address 172.16.2.1 255.255.255.0
ip access-group dmz61in in
no ip redirects
no ip proxy-arp
ip accounting output-packets
ip nat inside
ip inspect SDM_L out
ip virtual-reassembly in
duplex auto
speed auto
media-type rj45
no mop enabled
After the Cutover will the configuration on the Router be
interface GigabitEthernet0/0
description LAN
ip address 192.168.130.2 255.255.255.0
interface GigabitEthernet0/1
description DMZ LAN
ip address 172.16.2.2 255.255.255.0
Do I need to change anything else on the Router
Solved! Go to Solution.
- Labels:
-
Other Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:41 AM
Hello Purple tech,
on the router you still need the default static route
ip route 0.0.0.0.0.0.0.0 192.168.130.1
it may be wise to use a different security level for DMZ because by default ASA doesn't allow communication between interfaces with same security level for example use 80 instead of 100
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 11:01 AM
Hello Purple tech,
your inside is 192.168.130.0/24 so it becomes
http server enable
http 192.168.130.0 255.255.255.0 inside
try to see if you can add a second line like:
http 10.60.1.0 255.255.255.0 inside
note: if the second line overrides the first one means only one statement is supported and you need to make a choice
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 09:08 AM
Hello Purple Tech,
1)
It depends on ASA configuration, generally speaking being the ASA a firewall it works well with symmetric routing so you need to make a choice and be consistenf on all devices.
From the router point of view it could support to configure both default static routes.
But the ASA being a firewall can route the return traffic only down one of the two interfaces.
So the most safe move is to use only one for example the internal LAN 192.168.130. for both directions to achieve symmetric routing
2)
Yes you can remove the ip inspect statements as this becomes the job of the ASA and also you are changing the topology.
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 09:47 AM
Thank you for for your help.
It is ASA 5525 Firewall.
So can I configure 2 static Routes on the router
ip route 192.168.130.0 255.255.255.0 192.168.130.1
ip route 172.16.2.0 255.255.255.0 192.168.130.1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:04 AM
Please help me configuring the routes on ASA and the Router
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:04 AM
Hello Purple Tech,
the first one is not needed is the shared link between ASA and router you will NEVER need it
The second static route is needed only if you remove the connection of the router to the 172.16.2.0 network, that is if you disable gi0/1 on the router. But this is not required. So also the second static route may be not needed.
Note:
I'm not saying that the router cannot be connected to both IP subnets anymore, I mean that routing with ASA will work well with only one of them used.
Edit:
the only required static route is on ASA and is for the 10.60.1.0 subnet
I assume you will name the ASA interface inside
the command on ASA will be:
route inside 10.60.1.0 255.255.255.0 192.168.130.2
where the IP next-hop is the new IP address of router interface gi0/0
Edit2:
you can follow the example below for how to configure the ASA (note ASA SW version counts a lot this for 8.3)
http://www.cisco.com/en/US/products/ps6120/products_configuration_example09186a0080b7c939.shtml
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:35 AM
Thank you for your help Giuseppe
So the basic configuration (before adding ACLs and NAT) on the ASA is going to be
int gig0/0
nameif outside
security-level 0
ip address 220.*.*.* 255.255.255.0
int gig0/1
nameif inside
security-level 100
ip address 192.168.130.1
int gig0/2
nameif dmz
security-level 100
ip address 172.16.2.1
route outside 0 0 220.*.*.* 1
route inside 10.60.1.0 255.255.255.0 192.168.130.2
On the Router:
interface GigabitEthernet0/0
description LAN
ip address 192.168.130.2 255.255.255.0
interface GigabitEthernet0/1
description DMZ LAN
ip address 172.16.2.2 255.255.255.0
and no ip routes on the Router
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:41 AM
Hello Purple tech,
on the router you still need the default static route
ip route 0.0.0.0.0.0.0.0 192.168.130.1
it may be wise to use a different security level for DMZ because by default ASA doesn't allow communication between interfaces with same security level for example use 80 instead of 100
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 10:45 AM
Thank you so much Giuseppe
How do I configure for http server. In the example you had sent I saw the following
http server enable
http 192.168.0.0 255.255.254.0 inside
how do I configure http in this network
Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 11:01 AM
Hello Purple tech,
your inside is 192.168.130.0/24 so it becomes
http server enable
http 192.168.130.0 255.255.255.0 inside
try to see if you can add a second line like:
http 10.60.1.0 255.255.255.0 inside
note: if the second line overrides the first one means only one statement is supported and you need to make a choice
Hope to help
Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 11:07 AM
Thank you Giuseppe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 11:34 AM
how do I configure for "ip inspect SDM_L out (currently on the Router) on ASA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 11:44 AM
On the Router it is configured as
ip inspect log drop-pkt
ip inspect max-incomplete high 10000
ip inspect max-incomplete low 8000
ip inspect one-minute high 10000
ip inspect one-minute low 8000
ip inspect tcp idle-time 14400
ip inspect tcp finwait-time 60
ip inspect tcp max-incomplete host 5000 block-time 0
ip inspect name SDM_L dns
ip inspect name SDM_L ftp
ip inspect name SDM_L h323
ip inspect name SDM_L https
ip inspect name SDM_L icmp
ip inspect name SDM_L imap
ip inspect name SDM_L pop3
ip inspect name SDM_L netshow
ip inspect name SDM_L rcmd
ip inspect name SDM_L realaudio
ip inspect name SDM_L rtsp
ip inspect name SDM_L sqlnet
ip inspect name SDM_L streamworks
ip inspect name SDM_L tftp
ip inspect name SDM_L udp
ip inspect name SDM_L vdolive
ip inspect name SDM_L tcp
ip accounting-threshold 4096
on the new ASA it is
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options policy-map global_policy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2012 12:49 PM
Hello Purple tech,
each of these objects like
SDM_L realaudio
are defined based on the protocol characteristics you should find them in the router configuration.
Some of the protocols are in common and others are not as the default settings are different.
You should find the list of defined protocols on the ASA going to configuration mode and under
config t
policy-map global_policy
class inspection_default
! then you issue
inspect ?
the on line help provides you a list of supported and defined protocols
Edit:
here is the link to command reference inspect command for ASA 8.3
http://www.cisco.com/en/US/docs/security/asa/asa83/command/reference/i2.html
note:
it is possible that you may not map all of the protocols defined on the router
Hope to help
Giuseppe
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide