- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: DHCP snooping allowing DHCP without trust port
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 07:47 AM - edited 03-08-2019 12:35 PM
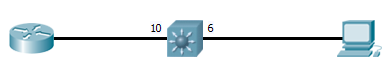
Can anyone please help with this? This is out of the box switch. I have attached config. Nothing at all on it except vlan, dhcp snooping. I have configured NO dhcp trustport as you can see and I AM able to get IP for hosts. I'm lost with this. I tried "no ip dhcp snooping information option"and with the option, no difference. My host is sitting on port 6 and router on 10. Router is configured with dhcp pool. This is the most simplest config. Any ideas whats going on here?
TEST_TEST#sh run Building configuration... Current configuration : 1460 bytes ! ! Last configuration change at 14:42:27 UTC Thu Nov 2 2017 ! version 15.2 no service pad service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname TEST_TEST ! boot-start-marker boot-end-marker ! ! no aaa new-model system mtu routing 1500 ! ! ! ! ! ! ip dhcp snooping vlan 1-4094 smartlog no ip dhcp snooping information option ip dhcp snooping ! ! ! spanning-tree mode rapid-pvst spanning-tree extend system-id ! ! ! ! vlan internal allocation policy ascending ! interface GigabitEthernet0/6 description HOST switchport access vlan 100 switchport mode access spanning-tree portfast edge ! interface GigabitEthernet0/10 description UPLINK switchport trunk allowed vlan 100 switchport trunk native vlan 100 switchport mode trunk ! interface Vlan1 no ip address shutdown ! interface Vlan100 ip address 10.90.9.253 255.255.255.0 no ip route-cache ! ip forward-protocol nd ip http server ip http secure-server ! ! ! ! ! line con 0 line vty 5 15 ! ! end
Solved! Go to Solution.
- Labels:
-
Other Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 12:22 PM
Yes, it is in database.
I have finally figured it out. Took only 2 days but found the issue. The problem was on the windows machine. Something with windows auto-reconfiguring the same IP over and over despite the snooping enabled.
I have gotten another host non desktop/laptop and plugged it directly into the switch. Worked perfectly. Could not get an IP at all. Configured the switch port trust and I was able to get an IP. Removed the trust, turned the port off and ON, could not get an IP, added the trust again and got one!
This was not the case with the windows machine. Just to make this even more interesting, I excluded the dhcp IP address on the router that the laptop was constantly getting, saved my config, rebooted router, switch and PC, came back ON with the same IP which clearly tells me it's not properly using rotuers DHCP but somehow auto-configuring its own from the first time it received it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 07:48 AM
here is additional info
TEST_TEST#sh ip dhcp snooping Switch DHCP snooping is enabled Switch DHCP gleaning is disabled DHCP snooping is configured on following VLANs: 1-4094 DHCP snooping is operational on following VLANs: 1,100 Smartlog is configured on following VLANs: 1-4094 Smartlog is operational on following VLANs: 1,100 DHCP snooping is configured on the following L3 Interfaces: Insertion of option 82 is disabled circuit-id default format: vlan-mod-port remote-id: ec1d.8bac.2d00 (MAC) Option 82 on untrusted port is not allowed Verification of hwaddr field is enabled Verification of giaddr field is enabled DHCP snooping trust/rate is configured on the following Interfaces: Interface Trusted Allow option Rate limit (pps) ----------------------- ------- ------------ ---------------- TEST_TEST#sh ip dhcp snooping statistics Packets Forwarded = 27 Packets Dropped = 0 Packets Dropped From untrusted ports = 0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:30 AM
Hello,
what switch platform is this ? Can you enable 'feature dhcp' globally ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:42 AM
yes I can enable dhcp service. Tried that too. No luck. I just enabled it though again
(C3560CX-UNIVERSALK9-M)
Version 15.2(4)E3
Also, I captured a debug of dhcp packets.
TEST_TEST# Nov 2 15:36:41.468: %SYS-5-CONFIG_I: Configured from console by console Nov 2 15:36:42.863: %LINK-3-UPDOWN: Interface GigabitEthernet0/6, changed state to down Nov 2 15:36:45.400: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:45.400: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:36:45.404: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:45.404: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:36:45.404: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, TEST_TEST# MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:45.404: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:45.404: DHCP_SNOOPING: add relay information option. Nov 2 15:36:45.404: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:36:45.404: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:36:45.404: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:36:45.404: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:36:45.404: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:36:45.425: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:45.425: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:36:45.425: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:45.425: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:36:45.425: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:45.425: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:45.425: DHCP_SNOOPING: add relay information option. Nov 2 15:36:45.425: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:36:45.425: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:36:45.425: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:36:45.428: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:36:45.428: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:36:47.337: %LINK-3-UPDOWN: Interface GigabitEthernet0/6, changed state to up Nov 2 15:36:48.340: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/6, changed state to up Nov 2 15:36:48.497: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:48.497: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:36:48.497: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:48.497: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:36:48.497: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:48.497: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:48.497: DHCP_SNOOPING: add relay information option. Nov 2 15:36:48.497: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:36:48.497: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:36:48.497: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:36:48.497: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:36:48.501: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:36:54.663: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:54.666: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:36:54.666: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:36:54.666: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:36:54.666: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:54.666: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:36:54.666: DHCP_SNOOPING: add relay information option. Nov 2 15:36:54.666: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:36:54.666: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:36:54.666: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:36:54.666: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:36:54.666: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. TEST_TEST# Nov 2 15:37:11.618: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:11.618: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:37:11.618: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:11.618: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:37:11.618: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6,u MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:11.618: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:11.618: DHCP_SNOOPING: add relay information option. Nov 2 15:37:11.618: DHCP_SNOOPING_SW: encoding opt82 cin vlan-mod-port format Nov 2 15:37:11.618: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:37:11.618: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:37:11.622: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:37:11.622: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:37:15.736: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:15.736: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:37:15.736: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:15.736: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:37:15.736: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:15.736: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:15.736: DHCP_SNOOPING: add relay information option. Nov 2 15:37:15.736: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:37:15.736: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:37:15.736: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:37:15.739: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:37:15.739: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:37:22.845: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:22.845: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:37:22.845: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:37:22.845: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:37:22.849: DHCP_SNOOPING: process new DHCP packet, message type: DHCPREQUEST, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 0.0.0.0, DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:22.849: DHCP_SNOOPING: message type : DHCPREQUEST DHCP ciaddr: 0.0.0.0, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:37:22.849: DHCP_SNOOPING: add relay information option. Nov 2 15:37:22.849: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:37:22.849: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:37:22.849: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:37:22.849: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:37:22.849: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:46 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:50 AM
never mind, the message just came in
Nov 2 15:49:58.288: DHCP_SNOOPING_SW: bridge packet get invalid mat entry: FFFF.FFFF.FFFF, packet is flooded to ingress VLAN: (100) Nov 2 15:49:58.288: DHCP_SNOOPING_SW: bridge packet send packet to cpu port: Vlan100. Nov 2 15:50:03.276: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:50:03.276: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Vl100 for pak. Was Gi0/6 Nov 2 15:50:03.276: DHCPSNOOP(hlfm_set_if_input): Setting if_input to Gi0/6 for pak. Was Vl100 Nov 2 15:50:03.276: DHCP_SNOOPING: received new DHCP packet from input interface (GigabitEthernet0/6) Nov 2 15:50:03.279: DHCP_SNOOPING: process new DHCP packet, message type: DHCPINFORM, input interface: Gi0/6, MAC da: ffff.ffff.ffff, MAC sa: 507b.9d72.dfc4, IP da: 255.255.255.255, IP sa: 10.90.9.52, DHCP ciaddr: 10.90.9.52, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:50:03.279: DHCP_SNOOPING: message type : DHCPINFORM DHCP ciaddr: 10.90.9.52, DHCP yiaddr: 0.0.0.0, DHCP siaddr: 0.0.0.0, DHCP giaddr: 0.0.0.0, DHCP chaddr: 507b.9d72.dfc4 Nov 2 15:50:03.279: DHCP_SNOOPING: add relay information option. Nov 2 15:50:03.279: DHCP_SNOOPING_SW: encoding opt82 cid in vlan-mod-port format Nov 2 15:50:03.279: DHCP_SNOOPING_SW: Encoding opt82 RID in MAC address format Nov 2 15:50:03.279: DHCP_SNOOPING: binary dump of relay info option, length: 20 data: Nov 2 15:50:03.279: 0x52 Nov 2 15:50:03.279: 0x12
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:51 AM - edited 11-02-2017 08:52 AM
Hello,
according to the feature navigator, for the 3560CX with 15.2(4)E3 you need at least IP Base or IP Services. Check if you might be running just the LAN Base image (show license all)...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 08:53 AM
TEST_TEST#sh license all
License Store: Primary License Storage
License Store: Built-In License Storage
StoreIndex: 0 Feature: ipservices Version: 1.0
License Type: Evaluation
License State: Active, Not in Use, EULA not accepted
Evaluation total period: 12 weeks 6 days
Evaluation period left: 12 weeks 6 days
Period used: 0 minute 0 second
License Priority: None
License Count: Non-Counted
StoreIndex: 1 Feature: ipservices Version: 1.0
License Type: PermanentRightToUse
License State: Inactive
Period used: 0 minute 0 second
License Priority: None
License Count: Non-Counted
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 09:21 AM
You are running IP Services (the evaluation version, don't forget to accept the EULA), so that should be fine...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 09:47 AM
i just tried accepting and i did not work looks like.
I tried these two and rebooted:
license right-to-use activate ipservices evaluation license right-to-use activate ipservices acceptEULA
After reboot:
TEST_TEST#sh license all
License Store: Primary License Storage
License Store: Built-In License Storage
StoreIndex: 0 Feature: ipservices Version: 1.0
License Type: Evaluation
License State: Inactive
Evaluation total period: 12 weeks 6 days
Evaluation period left: 12 weeks 6 days
Period used: 0 minute 0 second
License Priority: None
License Count: Non-Counted
StoreIndex: 1 Feature: ipservices Version: 1.0
License Type: PermanentRightToUse
License State: Active, In Use
Period used: 1 minute 35 seconds
License Priority: High
License Count: Non-Counted
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 09:56 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 11:27 AM - edited 11-02-2017 11:28 AM
Hello,
is VLAN 100 actually in your VLAN database ? Did you create it in config mode:
Switch(config)#vlan 100
?
Also, can you post the configuration of the router that serves as the DHCP server ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 12:22 PM
Yes, it is in database.
I have finally figured it out. Took only 2 days but found the issue. The problem was on the windows machine. Something with windows auto-reconfiguring the same IP over and over despite the snooping enabled.
I have gotten another host non desktop/laptop and plugged it directly into the switch. Worked perfectly. Could not get an IP at all. Configured the switch port trust and I was able to get an IP. Removed the trust, turned the port off and ON, could not get an IP, added the trust again and got one!
This was not the case with the windows machine. Just to make this even more interesting, I excluded the dhcp IP address on the router that the laptop was constantly getting, saved my config, rebooted router, switch and PC, came back ON with the same IP which clearly tells me it's not properly using rotuers DHCP but somehow auto-configuring its own from the first time it received it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 12:47 PM
Interesting. What happens if you stop/start the DHCP Client service on the Windows machine ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 12:52 PM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide