- Cisco Community
- Technology and Support
- Networking
- Switching
- Internet switch placement after firewall
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Internet switch placement after firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 07:47 AM
I want justification of placing internet switch for HA firewall.
I proposed design for client as below:
internet --> ONT --> ISP internet Router -- > Internet Switch(WAN side) --> HA firewall --> (LAN side )stacked 9300 core switch
While reviewing client asked me why need internet switch as above why not connecting ISP internet router to coreswitch with proper non routable VLAN.
ie internet --> ONT --> ISP internet Router -- > stacked 9300 core switch(WAN) --> HA firewall --> stacked 9300 core switch(LAN)
I told its doable but its not recommended. he asked why not. i told its not secured to do that way connecting internet connection directly on coreswitch. He told that firewall will take care. I told if core switch is compromised we can't tell its impact will be.
Can anybody give me a justification for our next sitting on this matter?
Any recommended standard or topology or security issue related if connecting directly in core switch .
what security issue will be faced if internet is directly connected to core switch even if we configure non routable layer 2 vlan?
- Labels:
-
Catalyst 9000
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 08:08 AM
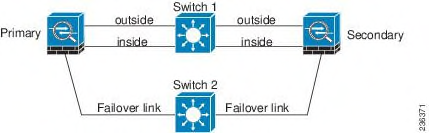
all ASA HA design in above link.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 08:13 AM
my question is that whether we can connect internet directly to coreswitch or not..
this connection will be non routable vlan. firewall WAN port also will be in the same vlan.
I know it can be done this way.. But what I feel is that my LAN device is directly connected to internet even though they are separated by vlan..
but is it recommended? is that good design? is that secured ? for me its a big NO.
But I want a justification in this regard with client with proper document.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 08:53 AM
As I mention before the guide give you more than 5 topology with advantage and disadvantage for each one.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 09:23 AM
I cannot see any internet connection connecting directly to coreswitch in the topology you mentioned
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 10:01 AM
You want doc. From cisco about uaing one sw "or stack" to connect inisde and outside of FW HA and if this solution is secure or not?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 08:28 AM
You are completely right but you may not find a document to prove you are right. This is a design consideration and on this situation quite often clients use their power or bosses justify with budget to make decisions.
I would not connect the internet on the core either but if I does, it is going to work and if you thing about protection, you can use VLAN and VRF, depending on the tools you have you can use SGT (SDA + DNAC).
It is a complicate discussion and not always technicians wins because design is open to interpretation and the client or the money speaks louder.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 09:25 AM - edited 05-10-2022 09:39 AM
I too agree what you say.
But Is there any design document at least mentioning about that.. I checked cisco CVD for campus LAN. But this scenario not mentioned .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 10:06 AM
Yeah, that´s what I said. Design is meant to be interpreted so, each company is invidual on that part and even if you can find a particular cisco design, chances are it will not match with your environment.
I had this kind of discussion trying to convince bosses the best way to do thing but sometimes I gave up and just do what they told.
Something you can possibly use is DDoS. With core front open to Internet, you can be vulnerable to an DDoS attack and this will affect you whole environment, instead only the firewall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 10:01 AM
I like your idea of having the (WAN) 9300 switch, in my experience its nice to have somewhat of a demarcation switch to connect to the service provider or outside entity and then connect your network behind this. It also helps to be able to troubleshoot using this switch as far as SLA goes.
I would also say it doesn't feel natural to connect the (LAN) switch directly to the service provider. For security reasons if anything I would want the Firewall to filter traffic before it connects to my LAN side. The concept of having trusted security zones, ISP (least trusted) and LAN (most trusted) would be a good point to bring up.
I can see how there are multiple design options to choose from, in the end this is going to be a design that you will most likely have to support afterwards correct? Standardizing could possibly be something to consider, especially if you are considering this design for additional sites.
Maybe also list the role the Firewall has in this design, is it also an IPS? If so that's another reason to put it closest to the untrusted side.
I'm assuming in the customers proposal: ie internet --> ONT --> ISP internet Router -- > stacked 9300 core switch(WAN) --> HA firewall --> stacked 9300 core switch(LAN)
The WAN and LAN switch is the same physical switch?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 11:53 PM
I proposed as below:
internet --> ONT --> ISP internet Router -- > stacked 9300 internet switch(WAN) --> HA firewall --> stacked 9300 core switch(LAN)
then customer asked why not do like this as below:
internet --> ONT --> ISP internet Router -- > stacked 9300 core switch(WAN) --> HA firewall --> same stacked 9300 core switch(LAN)
Here both WAN and LAN stacked 9300 core switch is same physical switch
I just want to tell which one is best design. There should be a justification for what Im telling. I know both are doable. if there is no budget issue which is best choice in this case. and why? In the justification we can consider scalability, high availability and security concerns.
Thats what i wanted to know.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2022 01:47 PM
"""NOTE: the function of the inner, outer and DMZ switches may be collapsed in a single pair of switches. In this case, the inside, DMZ, and outside segments of the firewall need to be properly segmented with VLANs."""
https://www.cisco.com/c/en/us/td/docs/solutions/Enterprise/Security/SAFESolOver.html
for any security design, check this guide or any cisco SAFE guide.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide