- Cisco Community
- Technology and Support
- Networking
- Switching
- IP Helper_Address Problem 3750
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-13-2012 02:21 PM - edited 03-07-2019 06:07 AM
Hello everyone.
I think it is my last resort for help, as i broke my head already over this problem i am experiencing.
I have stack of 2 switches 3750s for core networking on the site and a stack of 4 2960-s for distribution
My problem is that my DHCP which is Win2008 Server is not working on the vlan interfaces.
It does work on the native vlan 1 which is 192.168.186.1/24
But i have 3 other VLANs(2,3,4:187.1,188.1,189.1).
So teh problem is that when i connect a workstation to VLAN2,3 or 4 i do not get DHCP ip address.
if i connect workstation to VLAN1 either to the core switch port or to any port of the 2960s switches, which assigned vlan1 interface i do get ip address
for the connected workstation.
The thing is when i connect WS to the vlan2,3, or 4 and assign ip address manually i can ping my DHCP server which connected to the VLAN1 port on the core switch and opposite can ping that manually assigned ip from DHCP server.
So i do not know what the problem is and service dhcp command was performed.
Here i am providing config output. of the core switch.
Please if anyone can help with soemthing or what i can do to troubleshoot.
By the way i've tried to us: debug dhcp detail command on the core switch when switching WS to get the ip from DHCP on VLAN2,3 or 4 but no output.
Current configuration : 7583 bytes
!
version 12.2
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname OpusCoreSwitch
!
boot-start-marker
boot-end-marker
!
enable secret 5 $1$AcFb$8eC/HK3tjW7B4wD8j2/bu.
!
no aaa new-model
switch 1 provision ws-c3750g-48ts
switch 2 provision ws-c3750g-48ts
system mtu routing 1500
vtp mode transparent
ip subnet-zero
ip routing
!
!
!
!
crypto pki trustpoint TP-self-signed-2680796288
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-2680796288
revocation-check none
rsakeypair TP-self-signed-2680796288
!
!
crypto pki certificate chain TP-self-signed-2680796288
certificate self-signed 01
30820247 308201B0 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 32363830 37393632 3838301E 170D3933 30333031 30303033
33325A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D32 36383037
39363238 3830819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100D4CC 30CD8504 CDFF9238 4B28C001 FB388FA5 8EE5CBFA 6D5EE6D1 C0CC383B
CD7A94E2 9C0D4063 3EBBC494 0D9BB6A8 7448E8CF 06548C4C 9814670B 70C8EAD8
D7684AF2 2FA71128 9E8471C5 32252380 A4EA8DA4 A1E8A5DA 4751337B 2E0DD2A4
9F38381D 424A4F06 3D4A2EB5 5F76BF48 D57FB957 C05C802B 3161DE03 6895DD8F
3C7B0203 010001A3 6F306D30 0F060355 1D130101 FF040530 030101FF 301A0603
551D1104 13301182 0F4F7075 73436F72 65537769 7463682E 301F0603 551D2304
18301680 14A8F3EF DD632629 CEF9AC20 6F55312E 835646B4 1E301D06 03551D0E
04160414 A8F3EFDD 632629CE F9AC206F 55312E83 5646B41E 300D0609 2A864886
F70D0101 04050003 81810069 23FE6240 203BA97E 2A4C605F C434B6CB AB92EC04
6B16F733 5C37F1E2 C9377165 A1CCA0D6 3A3A26CF 649058D3 EC363701 BDEDF0D7
DA60BB4D FC7D33D9 DD215AF7 9F9894F3 F102B6F1 1E341F42 B8594211 A44B1EE2
2A40615A 61457E2D 5BAC0194 FAC6048E 02A816FC B87FC566 904200FC 4C84336A
EEB468C7 ECC8661D 9380D3
quit
!
!
!
!
!
spanning-tree mode pvst
spanning-tree portfast default
spanning-tree extend system-id
!
vlan internal allocation policy ascending
!
vlan 2-4
!
!
!
!
interface Port-channel1
switchport trunk encapsulation dot1q
switchport mode trunk
switchport nonegotiate
!
interface GigabitEthernet1/0/1
!
interface GigabitEthernet1/0/2
!
interface GigabitEthernet1/0/3
!
interface GigabitEthernet1/0/4
description OPUS_PBX
switchport access vlan 4
switchport mode access
spanning-tree portfast
!
interface GigabitEthernet1/0/5
!
interface GigabitEthernet1/0/6
switchport access vlan 4
switchport mode access
spanning-tree portfast
!
interface GigabitEthernet1/0/7
switchport access vlan 2
switchport mode access
spanning-tree portfast
!
interface GigabitEthernet1/0/8
switchport access vlan 3
switchport mode access
!
interface GigabitEthernet1/0/9
!
interface GigabitEthernet1/0/10
!
interface GigabitEthernet1/0/11
!
interface GigabitEthernet1/0/12
!
interface GigabitEthernet1/0/13
description Domain Cont
switchport mode access
!
interface GigabitEthernet1/0/14
!
interface GigabitEthernet1/0/15
!
interface GigabitEthernet1/0/16
!
interface GigabitEthernet1/0/17
!
interface GigabitEthernet1/0/18
!
interface GigabitEthernet1/0/19
!
interface GigabitEthernet1/0/20
!
interface GigabitEthernet1/0/21
!
interface GigabitEthernet1/0/22
!
interface GigabitEthernet1/0/23
!
interface GigabitEthernet1/0/24
!
interface GigabitEthernet1/0/25
!
interface GigabitEthernet1/0/26
!
interface GigabitEthernet1/0/27
!
interface GigabitEthernet1/0/28
!
interface GigabitEthernet1/0/29
!
interface GigabitEthernet1/0/30
!
interface GigabitEthernet1/0/31
!
interface GigabitEthernet1/0/32
!
interface GigabitEthernet1/0/33
switchport mode access
switchport port-security
switchport port-security aging time 2
switchport port-security violation restrict
switchport port-security aging type inactivity
macro description cisco-desktop
spanning-tree portfast
spanning-tree bpduguard enable
!
interface GigabitEthernet1/0/34
!
interface GigabitEthernet1/0/35
!
interface GigabitEthernet1/0/36
!
interface GigabitEthernet1/0/37
!
interface GigabitEthernet1/0/38
!
interface GigabitEthernet1/0/39
!
interface GigabitEthernet1/0/40
!
interface GigabitEthernet1/0/41
!
interface GigabitEthernet1/0/42
!
interface GigabitEthernet1/0/43
!
interface GigabitEthernet1/0/44
!
interface GigabitEthernet1/0/45
!
interface GigabitEthernet1/0/46
!
interface GigabitEthernet1/0/47
!
interface GigabitEthernet1/0/48
!
interface GigabitEthernet1/0/49
switchport trunk encapsulation dot1q
switchport mode trunk
switchport nonegotiate
channel-protocol lacp
channel-group 1 mode active
!
interface GigabitEthernet1/0/50
switchport trunk encapsulation dot1q
switchport mode access
switchport nonegotiate
shutdown
channel-protocol pagp
!
interface GigabitEthernet1/0/51
!
interface GigabitEthernet1/0/52
!
interface GigabitEthernet2/0/1
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/0/2
!
interface GigabitEthernet2/0/3
!
interface GigabitEthernet2/0/4
!
interface GigabitEthernet2/0/5
!
interface GigabitEthernet2/0/6
!
interface GigabitEthernet2/0/7
!
interface GigabitEthernet2/0/8
!
interface GigabitEthernet2/0/9
!
interface GigabitEthernet2/0/10
!
interface GigabitEthernet2/0/11
!
interface GigabitEthernet2/0/12
!
interface GigabitEthernet2/0/13
!
interface GigabitEthernet2/0/14
!
interface GigabitEthernet2/0/15
!
interface GigabitEthernet2/0/16
!
interface GigabitEthernet2/0/17
!
interface GigabitEthernet2/0/18
!
interface GigabitEthernet2/0/19
!
interface GigabitEthernet2/0/20
!
interface GigabitEthernet2/0/21
!
interface GigabitEthernet2/0/22
!
interface GigabitEthernet2/0/23
!
interface GigabitEthernet2/0/24
!
interface GigabitEthernet2/0/25
!
interface GigabitEthernet2/0/26
!
interface GigabitEthernet2/0/27
!
interface GigabitEthernet2/0/28
!
interface GigabitEthernet2/0/29
!
interface GigabitEthernet2/0/30
!
interface GigabitEthernet2/0/31
!
interface GigabitEthernet2/0/32
!
interface GigabitEthernet2/0/33
!
interface GigabitEthernet2/0/34
!
interface GigabitEthernet2/0/35
!
interface GigabitEthernet2/0/36
!
interface GigabitEthernet2/0/37
!
interface GigabitEthernet2/0/38
!
interface GigabitEthernet2/0/39
!
interface GigabitEthernet2/0/40
!
interface GigabitEthernet2/0/41
!
interface GigabitEthernet2/0/42
!
interface GigabitEthernet2/0/43
!
interface GigabitEthernet2/0/44
!
interface GigabitEthernet2/0/45
!
interface GigabitEthernet2/0/46
!
interface GigabitEthernet2/0/47
!
interface GigabitEthernet2/0/48
description WAP1
switchport access vlan 3
!
interface GigabitEthernet2/0/49
switchport trunk encapsulation dot1q
switchport mode trunk
switchport nonegotiate
channel-protocol lacp
channel-group 1 mode active
!
interface GigabitEthernet2/0/50
!
interface GigabitEthernet2/0/51
!
interface GigabitEthernet2/0/52
!
interface Vlan1
ip address 192.168.186.20 255.255.255.0
ip helper-address 192.168.186.17
ip mask-reply
!
interface Vlan2
ip address 192.168.187.1 255.255.255.0
ip helper-address 192.168.186.17
!
interface Vlan3
ip address 192.168.188.1 255.255.255.0
ip helper-address 192.168.186.17
!
interface Vlan4
ip address 192.168.189.1 255.255.255.0
!
ip default-gateway 192.168.186.1
ip classless
ip default-network 192.168.186.0
!
ip default-gateway 192.168.186.1
ip classless
ip default-network 192.168.186.0
ip route 0.0.0.0 0.0.0.0 192.168.186.1
ip http server
ip http secure-server
!
!
!
!
control-plane
!
!
line con 0
line vty 0 4
password ****************
login
line vty 5 15
login
!
end
PLEASE if anyone can help me out with this i would appreciate as i do not know what else i can do to get it working.
Thank you very much in advance.
Danila
Solved! Go to Solution.
- Labels:
-
Other Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 12:01 PM
I agree but with everything else looking ok I don't know what else to look at. All routing for vlans are done on switch. Vlan 1 routing is done on 192.168.186.1. Maybe change default gateway on dhcp server to ip of switch. Also change in vlan1 dhcp pool.
Sent from Cisco Technical Support iPhone App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-13-2012 02:34 PM
If you connect to VLAN 2 3 or 4, and assign a static IP to the PC are you able to talk to the DHCP server (i.e. ping if windows firewall isn't blocking ICMP, or RDP, etc.)?
A quick look at the config it seems ok (missing the ip helper on VLAN 4 interface though, and VLAN 1 should not need the ip helper command as it is the vlan with the DHCP server)
Can you confirm that you do have DHCP scopes for 192.168.187.0 /24, 192.168.187.0 /24, and 192.168.187.0 /24 created on the DHCP server? confirm they are enabled, and confirm that each scope has a default gateway address assigned (that is the .1 address...same as the vlan interface)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-13-2012 05:07 PM
"If you connect to VLAN 2 3 or 4, and assign a static IP to the PC are you able to talk to the DHCP server (i.e. ping if windows firewall isn't blocking ICMP, or RDP, etc.)?"
Yes, as i stated earlier:
"The thing is when i connect WS to the vlan2,3, or 4 and assign ip address manually i can ping my DHCP server which connected to the VLAN1 port on the core switch and opposite can ping that manually assigned ip from DHCP server."
"Can you confirm that you do have DHCP scopes for 192.168.187.0 /24, 192.168.187.0 /24, and 192.168.187.0 /24 created on the DHCP server? confirm they are enabled, and confirm that each scope has a default gateway address assigned (that is the .1 address...same as the vlan interface)?"
Yes all confirm.
DHCP server configured correctly with default getaways:
vlan2- 192.168.187.1
vlan3-192.168.188.1
vlan4 - i od not really need dhcp here as this vlan for voice sip trunk.
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-13-2012 07:28 PM
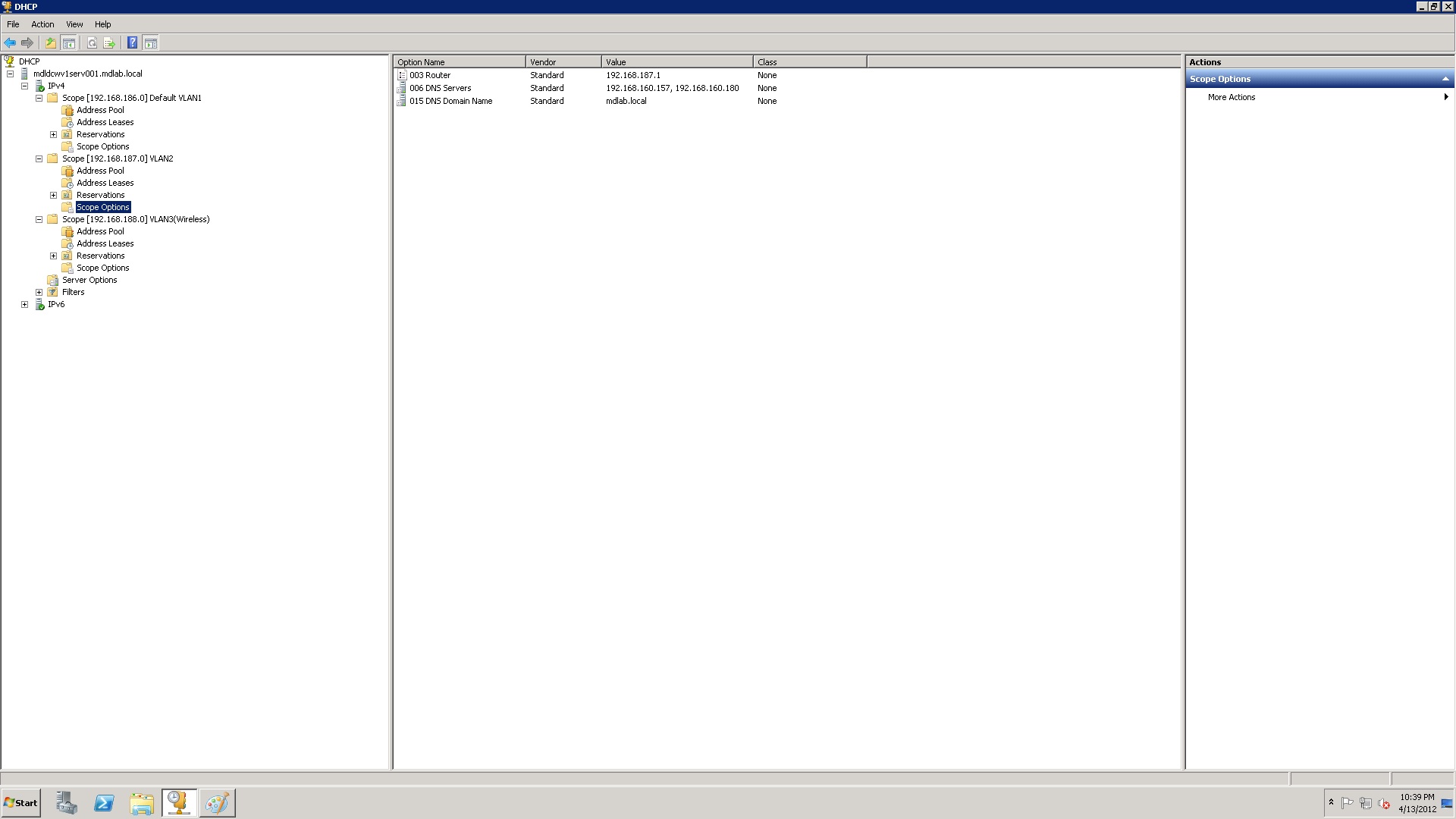
Can you include screenshots of your dhcp server scopes and the options configured. You switch config look correct so I would say there is a problem on the shop server.
Sent from Cisco Technical Support iPhone App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-13-2012 07:48 PM
Sure.
Attached please find screenshots of the dhcp server.
Thank you.



- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 07:20 AM
Please anyone ever had any similar problems?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 08:33 AM
Hello Danila,
I agree with all Paul's suggestions and verifications so far. Sadly it seems that so far, we have not identified the cause of your problem.
Are you by any chance running DHCP Snooping on your distribution 2960S switches? Is it possible to post the config of the 2960S stack as well?
Paul, please continue to submit your suggestions!
Best regards,
Peter
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 11:17 AM
What's at 192.168.186.1? If a cisco router can you provide configuration of it? Looking for ip route statements. Ip route 192.168.187.0 255.255.255.0 192.168.186.20 and so forth for the other vlan.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 11:42 AM
Hi Paul,
don't you think routing could be allright? Danila confirmed that she successfully pings the DHCP server when she staticaly assigns IP in any of the VLANs.
It would be most interesting to find out where are the DHCP requests dropped.
But this is really an strange problem...
Best regards,
Jan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 12:01 PM
I agree but with everything else looking ok I don't know what else to look at. All routing for vlans are done on switch. Vlan 1 routing is done on 192.168.186.1. Maybe change default gateway on dhcp server to ip of switch. Also change in vlan1 dhcp pool.
Sent from Cisco Technical Support iPhone App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 12:34 PM
Paul,
The symptoms would perfectly align with DHCP Snooping being activated on 2960S stack for VLANs 2-4 and either no trusted port towards the 3750, or the 3750 dropping the DHCP requests coming from clients because of Option-82 being present and GIADDR being zero. If the 3750 was DHCP server itself, it would surely drop such DHCP requests. I am not sure what is it going to do if only the relay functionality is being used but we shall check that as well.
Danila, can you please run the debug ip dhcp server packet on your 3750 (make sure the terminal monitor is issued as well) and see if the 3750 complains about any problems with processing the DHCP requests coming from clients? The debug dhcp ... you originally performed is a debug of client functionality in the IOS, not a debug of the server/relay functionality.
Best regards,
Peter
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2012 07:15 PM
"The symptoms would perfectly align with DHCP Snooping being activated on 2960S stack for VLANs 2-4 and either no trusted port towards the 3750, or the 3750 dropping the DHCP requests coming from clients because of Option-82 being present and GIADDR being zero. If the 3750 was DHCP server itself, it would surely drop such DHCP requests. I am not sure what is it going to do if only the relay functionality is being used but we shall check that as well."
Well besides 2960-s even when i connect workstation to the port on the core 3750 switch assigned to vlan 2 or 3 i do not get dhcp ip.
I will come tomorrow and will do debug ip dhcp server packet to see any errors.
Thank you all.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2012 06:23 AM
Okay got some debuging output:
*Mar 3 19:16:08.209: DHCPD: Reload workspace interface Vlan2 tableid 0.
*Mar 3 19:16:08.209: DHCPD: tableid for 192.168.187.1 on Vlan2 is 0
*Mar 3 19:16:08.209: DHCPD: client's VPN is .
*Mar 3 19:16:08.209: DHCPD: Finding a relay for client 0100.c0b7.5aa2.6b on int erface Vlan2.
*Mar 3 19:16:08.209: DHCPD: Looking up binding using address 192.168.187.1
*Mar 3 19:16:08.209: DHCPD: setting giaddr to 192.168.187.1.
*Mar 3 19:16:08.209: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.6b forwarded to 192 .168.186.17.
*Mar 3 19:16:23.082: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:16:23.082: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:16:23.082: DHCPD: client's VPN is .
*Mar 3 19:16:23.082: DHCPD: Finding a relay for client 0100.c0b7.5aa2.49 on interface Vlan1.
*Mar 3 19:16:23.082: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:16:23.082: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:16:23.082: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.49 forwarded to 192.168.186.17.
*Mar 3 19:16:27.494: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:16:27.494: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:16:27.494: DHCPD: client's VPN is .
*Mar 3 19:16:27.494: DHCPD: Finding a relay for client 0100.c0b7.5aa2.52 on interface Vlan1.
*Mar 3 19:16:27.494: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:16:27.494: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:16:27.494: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.52 forwarded to 192.168.186.17.
*Mar 3 19:16:38.475: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:16:38.475: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:16:38.475: DHCPD: client's VPN is .
*Mar 3 19:16:38.475: DHCPD: Finding a relay for client 0100.c0b7.5aa2.64 on interface Vlan1.
*Mar 3 19:16:38.475: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:16:38.475: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:16:38.483: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.64 forwarded to 192.168.186.17.
*Mar 3 19:16:38.500: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:16:38.500: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:16:38.500: DHCPD: client's VPN is .
*Mar 3 19:16:38.500: DHCPD: Finding a relay for client 0100.c0b7.5aa2.65 on interface Vlan1.
*Mar 3 19:16:38.500: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:16:38.500: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:16:38.500: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.65 forwarded to 192.168.186.17.
*Mar 3 19:16:45.203: DHCPD: option 61 is a duplicate.
*Mar 3 19:16:45.203: DHCPD: Reload workspace interface Vlan2 tableid 0.
*Mar 3 19:16:45.203: DHCPD: tableid for 192.168.187.1 on Vlan2 is 0
*Mar 3 19:16:45.203: DHCPD: client's VPN is .
*Mar 3 19:16:45.203: DHCPD: using received relay info.
*Mar 3 19:16:45.203: DHCPD: Looking up binding using address 192.168.187.1
*Mar 3 19:16:45.203: DHCPD: setting giaddr to 192.168.187.1.
*Mar 3 19:16:45.203: DHCPD: BOOTREQUEST from 0000.c0b7.5aa2.6b00.0000 forwarded to 192.168.186.17.
*Mar 3 19:20:12.284: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:20:12.284: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:20:12.284: DHCPD: client's VPN is .
*Mar 3 19:20:12.284: DHCPD: Finding a relay for client 0100.c0b7.5aa2.64 on interface Vlan1.
*Mar 3 19:20:12.284: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:20:12.284: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:20:12.284: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.64 forwarded to 192.168.186.17.
*Mar 3 19:20:19.951: %IP-4-DUPADDR: Duplicate address 192.168.188.1 on Vlan3, sourced by 00a0.c87e.3c21
*Mar 3 19:20:25.160: DHCPD: Reload workspace interface Vlan1 tableid 0.
*Mar 3 19:20:25.160: DHCPD: tableid for 192.168.186.20 on Vlan1 is 0
*Mar 3 19:20:25.160: DHCPD: client's VPN is .
*Mar 3 19:20:25.160: DHCPD: Finding a relay for client 0100.c0b7.5aa2.65 on interface Vlan1.
*Mar 3 19:20:25.160: DHCPD: Looking up binding using address 192.168.186.20
*Mar 3 19:20:25.160: DHCPD: setting giaddr to 192.168.186.20.
*Mar 3 19:20:25.160: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.65 forwarded to 192.168.186.17.
*Mar 3 19:20:37.525: DHCPD: Finding a relay for client 0100.c0b7.5aa2.6b on interface Vlan2.
*Mar 3 19:20:37.525: DHCPD: Looking up binding using address 192.168.187.1
*Mar 3 19:20:37.525: DHCPD: setting giaddr to 192.168.187.1.
*Mar 3 19:20:37.533: DHCPD: BOOTREQUEST from 0100.c0b7.5aa2.6b forwarded to 192.168.186.17.
So it seems like 3750 is forwarding request to dhcp server for vlan 2, so what might be the problem then?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2012 08:16 AM
Okay Guys.
Thank yuo everyone for help.
As soon as i changed default getaway ip on the Win2008 server to the core switch ip 192.168.186.20.and not the ISP router, DHCP service strated giving out ips to other vlans as well.
The problem seemd in this:
As all the vlan routig is done on the core switch, i guess default getaway ip on the DHCP server needs to be a next hop which is 3750 core switch: Go figure.
OpusCoreSwitch#sh ip route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is 192.168.186.1 to network 0.0.0.0
C 192.168.189.0/24 is directly connected, Vlan4
C 192.168.188.0/24 is directly connected, Vlan3
C 192.168.187.0/24 is directly connected, Vlan2
C* 192.168.186.0/24 is directly connected, Vlan1
S* 0.0.0.0/0 [1/0] via 192.168.186.1
Thank you all for helping, specifically Paul for pointing to look into right direction.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2012 09:06 PM
One question though left.
How can i make all this work but with the 192.168.186.1 ip as default getaway (which is ip of the router) ?
Thank you.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


