- Cisco Community
- Technology and Support
- Networking
- Switching
- Question: Extend L2 network across L3 tunnels with only a L3 switch
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Question: Extend L2 network across L3 tunnels with only a L3 switch
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2018 10:22 AM - edited 11-25-2018 10:25 AM
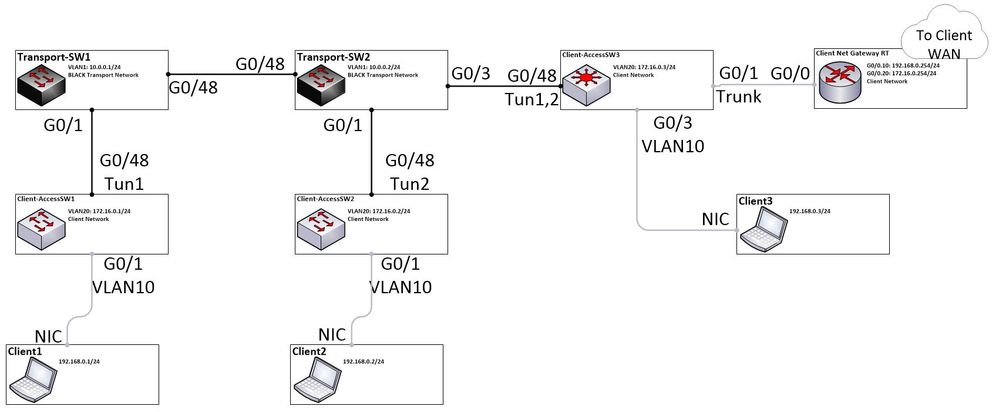
I currently have a large campus with multiple networks tunneling over a single inner campus transport network. Currently, these networks are using DOT1Q tunneling to connect to one another and the VLANs for each "client" network extend to every building on the campus. I'd to encrypt the traffic of the client networks before it gets to the transport network with IPSEC, but still maintain these campus wide VLANs.
Is there a way to do this with only one L3 switch in each building? I know Q-in-Q would likely be a good solution, but, as I understand it, I'd have to get an additional device for each building and don't want to suffer that expense. Also heard MACsec might be a good solution, but know little about it and am not sure if our current switches support it.
I'd essentially like to turn the in-side of the tunnel interface into a trunk port. Diagram below is the concept.
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2018 03:34 PM
Hello,
I am not clear on what you currently have configured. Dot1q tunneling and Q-in-Q are the same thing. That said, if all the equipment is under your control, why do you employ any sort of tunneling and/or IPSec at all, why not simply use trunks ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2018 05:03 PM
Policy mainly. All traffic across the transport network needs to be encrypted. Part of it is to keep an unmanaged internet access network separated from the corporate client network. Same with the security camera network, another network running over the transport. Don't want someone to get into a camera port and some how manage to gain access to the client network or see the traffic on it. That and transport network is owned and managed by a different entity than the client networks, I just work on both.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-26-2018 08:42 AM
If I am understanding your post correctly I believe that macsec would be the better solution to provide encryption. But of course it depends on whether your current switches support this feature. The other solutions that I can think of which supply encryption of traffic operate at layer 3 and would not support the layer 2 vlans spread across the entire campus.
HTH
Rick
Rick
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide