- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: Twice NAT on Cisco 9300 switch?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Twice NAT on Cisco 9300 switch?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2024 09:14 PM - edited 07-17-2024 09:16 PM
Is it possible to perform twice NAT on a Catalyst 9300 switch?
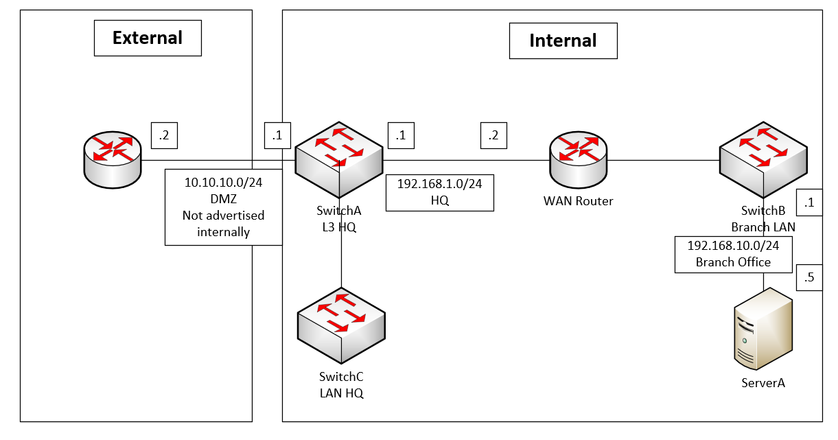
Our switch is connected to a DMZ (10.10.10.0/24)
The outside interface of the switch is 10.10.10.1
The inside interface of the switch is 192.168.1.1
THe destination (host 192.168.10.5) is on our internal network but several router hops away.
We do not want to route 10.10.10.0/24 internally. So the internal host 192.168.10.5 will not know how to route back to the DMZ network.
I would like to NAT the outside local and global address to the internal interface of the switch (192.168.1.1) and then to the destination (192.168.10.5)
So basically I would like to NAT as follows (I'm using 10.10.10.2, a host that is connecting from the outside as an example)
Outside local Outside global Inside global Inside local
10.10.10.2 10.10.10.2 192.168.1.1 192.168.10.5
This would be easy on ASA firewall however I do not see a way to do this on a 9300 switch.
Can this be done on a 9300 switch?
- Labels:
-
Catalyst 9000
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2024 10:27 PM
Hello!
On IOS-XE, a single rule cannot accommodate Twice-NAT (to my knowledge). To achieve this, you need to configure dynamic NAT/PAT for one direction and static NAT for the other.
BR
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2024 05:42 AM
you need two nat
ip nat inside source
ip nat outside source
this way you get twice NAT like we use in ASA or FW
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2024 12:50 PM - edited 07-18-2024 01:01 PM
I'm having a hard time with this.
THe DMZ network 10.10.10.0/24 is local to the HQ only and is not advertised to any internal branch sites.
We run BGP between the HQ SwitchA, the WAN router and the branch office SwitchB.
However since the DMZ network is not advertised to the branch office ServerA does not know how to return traffic from the DMZ network.
I had 2 ideas to make this work but no luck so far:
1) PAT overload on the inside interface 192.168.1.1 of SwitchA. I could be wrong but I don't see any commands that allow me to configure overload on the inside interface.
I only get an option to use pat overload when I use it with ip nat inside source and not ip nat outside source.
ip nat inside source list 1 interface xx overload
2) Use a 3rd subnet (eg 192.168.100.0/24) to NAT inside and outside.
ip nat inside source static 192.168.10.5 192.168.100.5
ip nat outside source static 10.10.10.2 192.168.100.5
Does not work either.
Some more ideas would be appreciated.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide