- Cisco Community
- Technology and Support
- Networking
- Switching
- VLAN between two routers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-21-2015 10:29 PM - edited 03-07-2019 11:11 PM
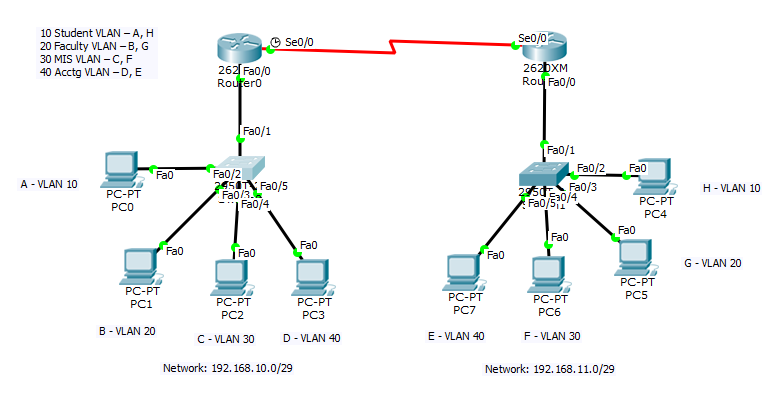
Hello. I am trying to solve a practice problem and I cant seem to route the VLANs. The layout is this:
You have two routers connected two each other. Each router has one switch and each switch has four generic PCs connected. Each PC on that switch belongs on its own VLAN. So,
| Switch 1 | Switch 2 |
|---|---|
|
|
|
|
|
|
|
|
So PC A on Router 1/Switch 1 can ping PC E on Router2/Switch 2 and it cant ping all the others. So on and so forth.
So I tried setting PC C as VLAN 10 to check if my configuration works, and it does. But then I attach my router and made sub interfaces, set interface fa0/1 on my switch as trunk and allowed VLAN 10, 20, 30 and 40. Now all of the PCs on the router can ping each other! That should not happen. Now I don't know what is wrong. Can anyone help me?
I attached the docx and the packet tracer file.
Solved! Go to Solution.
- Labels:
-
LAN Switching
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 12:35 PM
Sorry I've just realised you don't want connectivity between all PCs.
Which is a relief because looking at your configuration I couldn't see why they wouldn't be able to 🙂
You need to use acls on your subinterfaces to only allow traffic you want to.
If you want to allow any PC to ping any other PC within the same site but only the PC in the same vlan in the other site then use an acl outbound on the serial interfaces of the routers.
If you want to only allow ping between PCs in the same vlan then use acls inbound on the subinterfaces.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 06:29 AM
Are you using the same IP subnet for all vlans in each site ?
If so you can't do this.
As to why some pings work it entirely depends on what vlan you place the router interfaces that connect to the switches into.
So when PC A could ping PC B I assume you had the router interfaces connecting to the switches in vlan 10.
Then when you put PC C into vlan 10 it worked.
If you want each PC to have a different vlan in each site you need a different IP subnet per vlan at each site and then you can setup subinterfaces on the router for each vlan.
Note also that vlan 10 in one site is not the same vlan as vlan 10 in the other site.
You may know that but just wanted to point out that simply reusing the vlan ID does not make it the same vlan because the routers are connected with a L3 link.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 11:20 AM
Are you using the same IP subnet for all vlans in each site ?
No. In the first router, I'm using subnets of 192.168.10.0/29 and in the second, i use the subnets of 192.168.11.0/29.

So when PC A could ping PC B I assume you had the router interfaces connecting to the switches in vlan 10. Then when you put PC C into vlan 10 it worked.
I already set up the VLANs for each PC.

What I meant when I said that I changed PC C (fa0/4) to VLAN 10 is that I wanted to see if my configuration worked (if PC A could successfully ping PC C while failing to ping other hosts). It was just temporary. After I was sure that the problem was not in the VLAN assignment in the switch, I reassigned PC C again to VLAN 30. But after trunking the fa0/1 in the switch and typed: switchport trunk allowed vlan 10,20,30,40, PC A can now successfully ping PC B, C, D even if they are on different VLAN.
What I want is to connect:
PC0 ---------------------------------------- PC4
PC1 ---------------------------------------- PC5
PC2 ---------------------------------------- PC6
PC3 ---------------------------------------- PC7
PC0 should not be able to ping PC1-3 and PC5-7. So on and so forth.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 11:20 AM
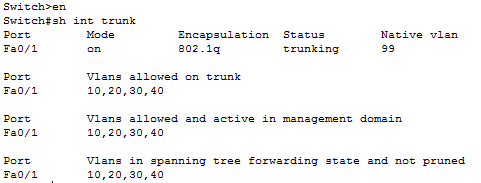
Okay, your original diagram didn't make clear you were actually using multiple /29 subnets at each site.
So at each site the switch connection to the router is configured as a trunk link ?
If so can you post -
"sh ip route" from each router and
"sh int trunk" from each switch.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 11:42 AM
| Router 1 |
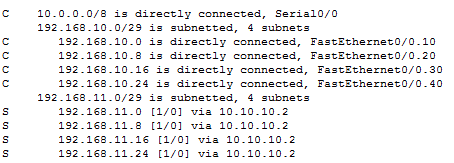 |
| Router 2 |
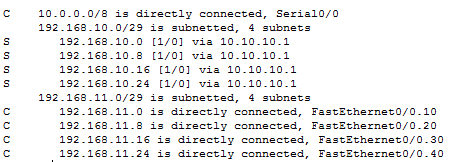 |
| Switch 1 |
 |
| Switch 2 |
 |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 12:35 PM
Sorry I've just realised you don't want connectivity between all PCs.
Which is a relief because looking at your configuration I couldn't see why they wouldn't be able to 🙂
You need to use acls on your subinterfaces to only allow traffic you want to.
If you want to allow any PC to ping any other PC within the same site but only the PC in the same vlan in the other site then use an acl outbound on the serial interfaces of the routers.
If you want to only allow ping between PCs in the same vlan then use acls inbound on the subinterfaces.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2015 09:38 PM
Thanks man. I thought I could solve my problem by using only VLAN commands. Can you give me any tips on ACLs or any resources? If you don't mind.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2015 06:16 AM
Have a read of this document -
http://www.cisco.com/c/en/us/support/docs/security/ios-firewall/23602-confaccesslists.html
it gives a good overview of acls.
If you need any help with them then feel free to come back with any queries.
Jon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2017 05:01 PM
Is your problem solved.... i am too facing same problem....can you please share the information regarding the same.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2022 12:57 PM
what configurations are enabled on serial interface
how you make serial interface to take traffic of different vlan without making subinterfaces
thankyou
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide