- Cisco Community
- Technology and Support
- Security
- VPN
- Anyconnect with FlexVPN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 03:52 AM
Hi,
I have been trying to configure the Anyconnect IPSEC on the ISR4000 router with latest IOS-XE-16.9.4.
Im facing issue with a debug message saying "IKEv2:(SESSION ID = 24,SA ID = 1):Auth exchange failed" and drop the negotiations.
Complete configuration and debugs are as attached. Please assist.
Saif
Solved! Go to Solution.
- Labels:
-
AnyConnect
-
FlexVPN
-
IPSEC
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 05:54 AM
Correct, you are.....but the server has to authenticate (authentication local rsa-sig) itself to the client using certificates as required by the IKEv2 RFC.
Refer to this guide here.
Note: In order to authenticate users against the local database on the router, EAP needs to be used. However, in order to use EAP, the local authentication method has to be rsa-sig, so the router needs a proper certificate installed on it, and it can't be a self-signed certificate.
You have a trustpoint that is using a self signed certificate.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 04:01 AM
Hi,
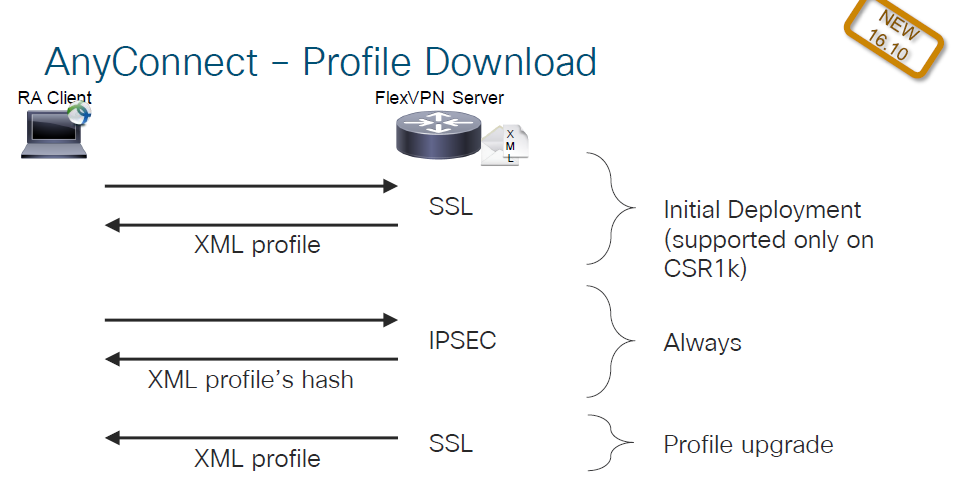
Try removing the anyconnect profile configuration as it's only supported on CSR1K
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 04:45 AM
Thanks for your prompt reply but it does not help. Still the same error in the debugs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 05:01 AM
Mar 2 14:28:23.659: IKEv2:% Received cert hash is invalid, using configured trustpoints from profile for signing
Mar 2 14:28:23.660: IKEv2:(SESSION ID = 24,SA ID = 1):Verification of peer's authentication data FAILED
Does the WIndows computer trust the certificate in use by the hub router?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 05:46 AM
The remote authentication is set to anyconnect-eap only so the certificate should not matter.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 05:54 AM
Correct, you are.....but the server has to authenticate (authentication local rsa-sig) itself to the client using certificates as required by the IKEv2 RFC.
Refer to this guide here.
Note: In order to authenticate users against the local database on the router, EAP needs to be used. However, in order to use EAP, the local authentication method has to be rsa-sig, so the router needs a proper certificate installed on it, and it can't be a self-signed certificate.
You have a trustpoint that is using a self signed certificate.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 08:24 PM
Thanks for the expert advise. It works.
Correct, you are.....but the server has to authenticate (authentication local rsa-sig) itself to the client using certificates as required by the IKEv2 RFC.
- I didnt do anything special for this.
Refer to this guide here.
- I have been configuring according to this guide but just overlooked EAP note.
Note: In order to authenticate users against the local database on the router, EAP needs to be used. However, in order to use EAP, the local authentication method has to be rsa-sig, so the router needs a proper certificate installed on it, and it can't be a self-signed certificate.
You have a trustpoint that is using a self signed certificate.
- Yes now I made a proper certificate and NOT self signed certificate and it works.
Thanks
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide