- Cisco Community
- Technology and Support
- Security
- VPN
- Actually, I think what might
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco Anyconnect client connects to the VPN, but cannot reach any other network/subnet from the clients machine
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2016 04:34 AM - edited 02-21-2020 09:01 PM
Hi folks,
I have one huge issue regarding VPN which I cannot resolve or connect the dots (what can possibly cause an issue)
One of our customers wants to replace old snapgear with something better so they've choose ASA to do so.
I have created all the configuration in ASA and tested inside our test network. I was able to connect with clients machine from outside to ASA VPN and to ping any machine inside the network. Everything worked perfectly. After that I have set same firewall/config to the customers site, and as soon as I connected ASA to their network and tried to connect from outside using Any connect, I was not able to ping any machine inside their network. All networks, subnets were out of reach/no reply.
At first I have set static routes and static IP of the ASA interface, but without luck. Then I set interface to get the IP address from DHCP server and all the routes from "L3 Core switch" that is doing all the routing, again without any luck.
Configuration of the ASA (dynamic)
: Saved
:
: Serial Number: xxxxxxxx
: Hardware: ASA5506, 4096 MB RAM, CPU Atom C2000 series 1250 MHz, 1 CPU (4 cores)
:
ASA Version 9.5(2)
!
hostname xxxxxxxx
enable password xxxxxxxxxxxxxx encrypted
passwd xxxxxxxxxxxxxx encrypted
names
ip local pool VPN_xxxxxx 10.13.3.2-10.13.3.200 mask 255.255.255.0
!
interface GigabitEthernet1/1
description WAN Connection
nameif outside
security-level 0
ip address xxx.xxx.xxx.88 255.255.255.224
!
interface GigabitEthernet1/2
description LAN address
nameif inside
security-level 100
ip address dhcp setroute
!
interface GigabitEthernet1/3
description Test Connection Outside
nameif testConn
security-level 0
ip address xxx.xxx.xxx.218 255.255.255.248
!
interface GigabitEthernet1/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/6
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/7
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/8
nameif mgmtbck
security-level 100
ip address 192.168.96.1 255.255.255.0
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
!
ftp mode passive
clock timezone GMT 0
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network TestConnection
subnet 192.168.10.0 255.255.254.0
description TestConnection
object network WANAddress
host xxx.xxx.xxx.217
object network WAN_Connection
subnet 192.168.10.0 255.255.254.0
description InternetConnection
object network WANConnectionxxxxxx
host xxx.xxx.xxx.65
object network WANConn
subnet 192.168.10.0 255.255.254.0
object network NETWORK_OBJ_10.13.3.0_24
subnet 10.13.3.0 255.255.255.0
object network Network_A
subnet 192.168.0.0 255.255.254.0
description Network 192.168.0.0/23
object network Network_B
subnet 172.17.110.0 255.255.255.0
description Network 172.17.110.0
object network Network_C
subnet 172.17.101.0 255.255.255.0
description Network 172.17.101.0/24
object network Network_D
subnet 172.17.137.0 255.255.255.0
description Network 172.17.137.0/24
object network Gateway_Inside
host 192.168.10.1
description inside gateway address
object network OutsideNAT
subnet 192.168.10.0 255.255.254.0
object-group icmp-type DM_INLINE_ICMP_1
icmp-object echo
icmp-object echo-reply
icmp-object time-exceeded
icmp-object traceroute
icmp-object unreachable
access-list inside_access_in extended permit ip any any
access-list inside_access_in extended permit icmp any any object-group DM_INLINE_ICMP_1
access-list 101 extended permit icmp any any echo-reply
access-list 101 extended permit icmp any any source-quench
access-list 101 extended permit icmp any any unreachable
access-list 101 extended permit icmp any any time-exceeded
access-list Split-Tunnel standard permit 192.168.10.0 255.255.254.0
pager lines 24
logging enable
logging asdm informational
mtu outside 1500
mtu inside 1500
mtu testConn 1500
mtu mgmtbck 1500
icmp unreachable rate-limit 1 burst-size 1
icmp permit any inside
asdm image disk0:/asdm-762.bin
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (inside,testConn) source static any any destination static NETWORK_OBJ_10.13.3.0_24 NETWORK_OBJ_10.13.3.0_24 no-proxy-arp route-lookup
nat (inside,outside) source static any any destination static NETWORK_OBJ_10.13.3.0_24 NETWORK_OBJ_10.13.3.0_24 no-proxy-arp route-lookup
!
object network WANConn
nat (inside,testConn) dynamic interface dns
object network OutsideNAT
nat (inside,outside) dynamic interface dns
access-group 101 in interface outside
access-group inside_access_in in interface inside
access-group 101 in interface testConn
route testConn 0.0.0.0 0.0.0.0 xxx.xxx.xxx.217 1
route outside 0.0.0.0 0.0.0.0 xxx.xxx.xxx.65 2
route inside 172.17.101.0 255.255.255.0 192.168.10.1 1
route inside 172.17.110.0 255.255.255.0 192.168.10.1 1
route inside 172.17.137.0 255.255.255.0 192.168.10.1 1
route inside 192.168.0.0 255.255.254.0 192.168.10.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
aaa-server NPS protocol radius
aaa-server NPS (inside) host 192.168.0.186
key *****
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
http server enable
http 192.168.1.0 255.255.255.0 inside
http 192.168.10.0 255.255.254.0 inside
http 192.168.96.0 255.255.255.0 mgmtbck
no snmp-server location
no snmp-server contact
service sw-reset-button
crypto ipsec ikev2 ipsec-proposal DES
protocol esp encryption des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal 3DES
protocol esp encryption 3des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES
protocol esp encryption aes
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES192
protocol esp encryption aes-192
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES256
protocol esp encryption aes-256
protocol esp integrity sha-1 md5
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev2 ipsec-proposal AES256 AES192 AES 3DES DES
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto map testConn_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map testConn_map interface testConn
crypto ca trustpoint xxxxxxxx
enrollment self
fqdn xxxxxx.local
subject-name CN=xxxxxxxx
serial-number
proxy-ldc-issuer
crl configure
crypto ca trustpool policy
crypto ca certificate chain xxxxxxxx
certificate cffdf657
3082036f 30820257 a0030201 020204cf fdf65730 0d06092a 864886f7 0d010105
05003047 31133011 06035504 03130a41 646d6972 616c4153 41313030 12060355
0405130b 4a414432 30323330 34435430 1a06092a 864886f7 0d010902 160d6164
6d697261 6c2e6c6f 63616c30 1e170d31 36313030 37303234 3431335a 170d3236
31303035 30323434 31335a30 47311330 11060355 0403130a 41646d69 72616c41
121616e7 7014f20f dbf9733a bca6055a 15f68e68 8fa67ea5 0c63d7ed 712e5517
a392775d 2f4bdd5a df207e10 0413c878 fba699
quit
crypto ikev2 policy 1
encryption aes-256
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 10
encryption aes-192
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 20
encryption aes
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 30
encryption 3des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 40
encryption des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 enable outside client-services port 443
crypto ikev2 enable testConn client-services port 443
crypto ikev2 remote-access trustpoint xxxxxxxx
crypto ikev1 enable outside
crypto ikev1 enable testConn
crypto ikev1 policy 20
authentication rsa-sig
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 30
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 50
authentication rsa-sig
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 60
authentication pre-share
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 80
authentication rsa-sig
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 90
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 110
authentication rsa-sig
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 120
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 140
authentication rsa-sig
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 150
authentication pre-share
encryption des
hash sha
group 2
lifetime 86400
telnet timeout 5
no ssh stricthostkeycheck
ssh 192.168.10.0 255.255.254.0 inside
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0dhcp-client client-id interface inside
dhcpd auto_config outside
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server xxx.xxx.xxx.44 source testConn prefer
ssl trust-point xxxxxxxx outside
ssl trust-point xxxxxxxx inside
ssl trust-point xxxxxxxx testConn
ssl trust-point xxxxxxxx mgmtbck
webvpn
enable outside
enable testConn
anyconnect image disk0:/anyconnect-win-4.3.01095-k9.pkg 1
anyconnect profiles xxxxxxMain_client_profile disk0:/xxxxxxMain_client_profile.xml
anyconnect profiles xxxxxx_client_profile disk0:/xxxxxx_client_profile.xml
anyconnect profiles TestVPN_client_profile disk0:/TestVPN_client_profile.xml
anyconnect enable
tunnel-group-list enable
cache
disable
error-recovery disable
group-policy GroupPolicy_TestVPN internal
group-policy GroupPolicy_TestVPN attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel
default-domain none
webvpn
anyconnect profiles value TestVPN_client_profile type user
group-policy GroupPolicy_xxxxxxMain internal
group-policy GroupPolicy_xxxxxxMain attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel
default-domain none
webvpn
anyconnect profiles value xxxxxxMain_client_profile type user
group-policy GroupPolicy_VPN internal
group-policy GroupPolicy_VPN attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ssl-client
default-domain none
group-policy Policy_xxxxxx internal
group-policy Policy_xxxxxx attributes
vpn-tunnel-protocol ssl-clientless
webvpn
url-list none
dynamic-access-policy-record DfltAccessPolicy
username admin password xxxxxxxx encrypted privilege 15
tunnel-group VPN type remote-access
tunnel-group VPN general-attributes
address-pool VPN_xxxxxx
default-group-policy GroupPolicy_VPN
tunnel-group VPN webvpn-attributes
group-alias VPN enable
tunnel-group TestVPN type remote-access
tunnel-group TestVPN general-attributes
address-pool VPN_xxxxxx
default-group-policy GroupPolicy_TestVPN
tunnel-group TestVPN webvpn-attributes
group-alias TestVPN enable
tunnel-group xxxxxxMain type remote-access
tunnel-group xxxxxxMain general-attributes
address-pool VPN_xxxxxx
authentication-server-group NPS
default-group-policy GroupPolicy_xxxxxxMain
tunnel-group xxxxxxMain webvpn-attributes
group-alias xxxxxxMain enable
tunnel-group VPN_SSL type remote-access
tunnel-group VPN_SSL general-attributes
default-group-policy Policy_xxxxxx
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
: end
Configuration of the ASA (static)
: Saved
:
: Serial Number: xxxxxxxx
: Hardware: ASA5506, 4096 MB RAM, CPU Atom C2000 series 1250 MHz, 1 CPU (4 cores)
: Written by xxxxx at 08:27:30.065 GMT Wed Oct 12 2016
!
ASA Version 9.5(2)
!
hostname xxxxxxxxASA
enable password xxxxxxxxxxxxxxxxxxxxxxxx encrypted
passwd xxxxxxxxxxxxxxxxxxxxxxxx encrypted
names
ip local pool VPN_xxxxxxxx 10.13.3.2-10.13.3.254 mask 255.255.255.0
!
interface GigabitEthernet1/1
description WAN Connection
nameif outside
security-level 0
ip address xxx.xxx.xxx.88 255.255.255.224
!
interface GigabitEthernet1/2
description LAN address
nameif inside
security-level 100
ip address 192.168.10.3 255.255.254.0
!
interface GigabitEthernet1/3
description Test Connection Outside
nameif testConn
security-level 0
ip address xxx.xxx.xxx.218 255.255.255.248
!
interface GigabitEthernet1/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/6
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/7
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/8
shutdown
no nameif
no security-level
no ip address
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
!
ftp mode passive
clock timezone GMT 0
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network TestConnection
subnet 192.168.10.0 255.255.254.0
description TestConnection
object network WANAddress
host xxx.xxx.xxx.217
object network WAN_Connection
subnet 192.168.10.0 255.255.254.0
description InternetConnection
object network WANConnectionxxxxxxxx
host xxx.xxx.xxx.65
object network WANConn
subnet 192.168.10.0 255.255.254.0
object network NETWORK_OBJ_10.13.3.0_24
subnet 10.13.3.0 255.255.255.0
object network Network_A
subnet 192.168.0.0 255.255.254.0
description Network 192.168.0.0/23
object network Network_B
subnet 172.17.110.0 255.255.255.0
description Network 172.17.110.0
object network Network_C
subnet 172.17.101.0 255.255.255.0
description Network 172.17.101.0/24
object network Network_D
subnet 172.17.137.0 255.255.255.0
description Network 172.17.137.0/24
object network Gateway_Inside
host 192.168.10.1
description inside gateway address
object network OutsideNAT
subnet 192.168.10.0 255.255.254.0
object-group icmp-type DM_INLINE_ICMP_1
icmp-object echo
icmp-object echo-reply
icmp-object time-exceeded
icmp-object traceroute
icmp-object unreachable
access-list inside_access_in extended permit ip any any
access-list inside_access_in extended permit icmp any any object-group DM_INLINE_ICMP_1
access-list 101 extended permit icmp any any echo-reply
access-list 101 extended permit icmp any any source-quench
access-list 101 extended permit icmp any any unreachable
access-list 101 extended permit icmp any any time-exceeded
access-list Split-Tunnel standard permit 192.168.10.0 255.255.254.0
pager lines 24
logging enable
logging asdm informational
mtu outside 1500
mtu inside 1500
mtu testConn 1500
icmp unreachable rate-limit 1 burst-size 1
icmp permit any inside
asdm image disk0:/asdm-762.bin
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (inside,testConn) source static any any destination static NETWORK_OBJ_10.13.3.0_24 NETWORK_OBJ_10.13.3.0_24 no-proxy-arp route-lookup
nat (inside,outside) source static any any destination static NETWORK_OBJ_10.13.3.0_24 NETWORK_OBJ_10.13.3.0_24 no-proxy-arp route-lookup
!
object network WANConn
nat (inside,testConn) dynamic interface dns
object network OutsideNAT
nat (inside,outside) dynamic interface dns
access-group 101 in interface outside
access-group inside_access_in in interface inside
access-group 101 in interface testConn
route outside 0.0.0.0 0.0.0.0 xxx.xxx.xxx.65 1
route testConn 0.0.0.0 0.0.0.0 xxx.xxx.xxx.217 3
route inside 172.17.101.0 255.255.255.0 192.168.10.1 1
route inside 172.17.110.0 255.255.255.0 192.168.10.1 1
route inside 172.17.137.0 255.255.255.0 192.168.10.1 1
route inside 192.168.0.0 255.255.254.0 192.168.10.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
aaa-server NPS protocol radius
aaa-server NPS (inside) host 192.168.0.186
key xxxxxxx
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
http server enable
http 192.168.1.0 255.255.255.0 inside
http 192.168.10.0 255.255.254.0 inside
no snmp-server location
no snmp-server contact
service sw-reset-button
crypto ipsec ikev2 ipsec-proposal AES256
protocol esp encryption aes-256
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES192
protocol esp encryption aes-192
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES
protocol esp encryption aes
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal 3DES
protocol esp encryption 3des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal DES
protocol esp encryption des
protocol esp integrity sha-1 md5
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev2 ipsec-proposal AES256 AES192 AES 3DES DES
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto map testConn_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map testConn_map interface testConn
crypto ca trustpoint xxxxxxxxCert
enrollment self
fqdn xxxxxxxx.local
subject-name CN=xxxxxxxxASA
serial-number
proxy-ldc-issuer
crl configure
crypto ca trustpool policy
crypto ca certificate chain xxxxxxxxCert
certificate cffdf657
3082036f 30820257 a0030201 020204cf fdf65730 0d06092a 864886f7 0d010105
05003047 31133011 06035504 03130a41 646d6972 616c4153 41313030 12060355
0405130b 4a414432 30323330 34435430 1a06092a 864886f7 0d010902 160d6164
6d697261 6c2e6c6f 63616c30 1e170d31 36313030 37303234 3431335a 170d3236
31303035 30323434 31335a30 47311330 11060355 0403130a 41646d69 72616c41
89dcd2ca 48d03495 655c1b39 35d26809 40d73e65 8bebfe10 c3c07753 75d6ba67
e7fd3326 5ee135c4 bf96971a 99e5ed5c 72c22c56 bda3e047 97f5e667 57504628
5b64c134 279b5205 2ebf37fe 81174d03 e2c9a30f acdf2893 f3136e20 4221bca0
121616e7 7014f20f dbf9733a bca6055a 15f68e68 8fa67ea5 0c63d7ed 712e5517
a392775d 2f4bdd5a df207e10 0413c878 fba699
quit
crypto ikev2 policy 1
encryption aes-256
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 10
encryption aes-192
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 20
encryption aes
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 30
encryption 3des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 40
encryption des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 enable outside client-services port 443
crypto ikev2 enable testConn client-services port 443
crypto ikev2 remote-access trustpoint xxxxxxxxCert
crypto ikev1 enable outside
crypto ikev1 enable testConn
crypto ikev1 policy 20
authentication rsa-sig
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 30
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 50
authentication rsa-sig
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 60
authentication pre-share
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 80
authentication rsa-sig
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 90
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 110
authentication rsa-sig
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 120
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 140
authentication rsa-sig
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 150
authentication pre-share
encryption des
hash sha
group 2
lifetime 86400
telnet timeout 5
no ssh stricthostkeycheck
ssh 192.168.10.0 255.255.254.0 inside
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0dhcpd auto_config outside
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server xxx.xxx.xxx.44 source testConn prefer
ssl trust-point xxxxxxxxCert outside
ssl trust-point xxxxxxxxCert inside
ssl trust-point xxxxxxxxCert testConn
webvpn
enable outside
enable testConn
anyconnect image disk0:/anyconnect-win-4.3.01095-k9.pkg 1
anyconnect profiles xxxxxxxxVPNMain_client_profile disk0:/xxxxxxxxVPNMain_client_profile.xml
anyconnect profiles xxxxxxxxVPN_client_profile disk0:/xxxxxxxxVPN_client_profile.xml
anyconnect profiles TestVPN_client_profile disk0:/TestVPN_client_profile.xml
anyconnect enable
tunnel-group-list enable
cache
disable
error-recovery disable
group-policy GroupPolicy_xxxxxxxxVPN internal
group-policy GroupPolicy_xxxxxxxxVPN attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel
default-domain none
webvpn
anyconnect profiles value xxxxxxxxVPN_client_profile type user
group-policy GroupPolicy_TestVPN internal
group-policy GroupPolicy_TestVPN attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel
default-domain none
webvpn
anyconnect profiles value TestVPN_client_profile type user
group-policy GroupPolicy_xxxxxxxxVPNMain internal
group-policy GroupPolicy_xxxxxxxxVPNMain attributes
wins-server none
dns-server value 8.8.8.8
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel
default-domain none
webvpn
anyconnect profiles value xxxxxxxxVPNMain_client_profile type user
dynamic-access-policy-record DfltAccessPolicy
username xxxxx password xxxxxxxxxxx encrypted privilege 15
tunnel-group xxxxxxxxVPN type remote-access
tunnel-group xxxxxxxxVPN general-attributes
address-pool VPN_xxxxxxxx
default-group-policy GroupPolicy_xxxxxxxxVPN
tunnel-group xxxxxxxxVPN webvpn-attributes
group-alias xxxxxxxxVPN enable
tunnel-group TestVPN type remote-access
tunnel-group TestVPN general-attributes
address-pool VPN_xxxxxxxx
default-group-policy GroupPolicy_TestVPN
tunnel-group TestVPN webvpn-attributes
group-alias TestVPN enable
tunnel-group xxxxxxxxVPNMain type remote-access
tunnel-group xxxxxxxxVPNMain general-attributes
address-pool VPN_xxxxxxxx
authentication-server-group NPS
default-group-policy GroupPolicy_xxxxxxxxVPNMain
tunnel-group xxxxxxxxVPNMain webvpn-attributes
group-alias xxxxxxxxVPNMain enable
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
: end
Switch configuration to which ASA is directly connected and that is doing all the routings
show running-config
Running configuration:
; J8697A Configuration Editor; Created on release #K.15.15.0008
; Ver #XXXXXX
hostname "SW1-XXXX-01"
module 1 type j9538a
module 3 type j9534a
module 4 type j9534a
module 5 type j9534a
module 6 type j9536a
console baud-rate 9600
console idle-timeout 3600
console idle-timeout serial-usb 3600
dhcp-snooping
dhcp-snooping authorized-server 192.168.0.253
dhcp-snooping vlan 100
trunk A8,F22 trk1 lacp
trunk C21-C24 trk2 trunk
trunk C5 trk10 dt-lacp
trunk A1 trk11 dt-lacp
trunk A2 trk12 dt-lacp
trunk A3 trk13 dt-lacp
trunk A4 trk14 dt-lacp
trunk A5 trk15 dt-lacp
trunk A6 trk16 dt-lacp
trunk E1-E2 trk50 lacp
filter protocol ipx drop A1-A8,C1-C24,D1-D24,E1-E24,F1-F22
filter protocol appletalk drop A1-A8,C1-C24,D1-D24,E1-E24,F1-F22
filter protocol netbeui drop A1-A8,C1-C24,D1-D24,E1-E24,F1-F22
filter protocol sna drop A1-A8,C1-C24,D1-D24,E1-E24,F1-F22
timesync sntp
sntp unicast
sntp server priority 1 192.168.0.186
sntp server priority 2 192.168.0.230
time daylight-time-rule western-europe
time timezone 60
no web-management
web-management ssl
ip arp-mcast-replies
ip default-gateway 192.168.254.1
ip dns domain-name "SW1.local"
ip dns server-address priority 1 192.168.0.186
ip dns server-address priority 2 192.168.0.230
ip ssh filetransfer
ip directed-broadcast
ip route 0.0.0.0 0.0.0.0 192.168.254.1
ip routing
switch-interconnect trk1
interface A1
name "172.17.101.10"
exit
interface A2
name "172.17.101.20"
exit
interface A3
name "172.17.101.30"
exit
interface A4
name "172.17.101.40"
exit
interface A5
name "172.17.101.50"
exit
interface A6
name "172.17.101.60"
exit
interface A7
dhcp-snooping trust
name " ESX01_ALL_NET_172.17.101.121"
exit
interface A8
name "Interconnect"
exit
interface C1
name "COMPANY"
exit
interface C2
name "VPN-SG560"
exit
interface C3
name "USB to LAN switch"
exit
interface C5
name "FIREWALL-0/0-LACP"
exit
interface C12
name "IPTV"
exit
interface C13
name "172.17.101.111"
exit
interface C14
name "NIMBL_SAN01_CTRL_A_MGMT_172.17.101.101"
exit
interface C21
name "UPL_HP4108"
exit
interface C22
name "UPL_HP4108"
exit
interface C23
name "UPL_HP4108"
exit
interface C24
name "UPL_HP4108"
exit
interface E13
name "NIMBL_SAN01_CTRL_A_ISCSI_ETH2"
exit
interface E14
name "NIMBL_SAN01_CTRL_A_ISCSI_ETH4"
exit
interface E15
name "NIMBL_SAN01_CTRL_B_ISCSI_ETH3"
exit
interface F20
name "DTHB-PORT"
exit
interface F21
dhcp-snooping trust
name " 172.17.101.122"
exit
interface F22
name "Interconnect"
exit
interface Trk1
dhcp-snooping trust
exit
interface Trk10
unknown-vlans disable
exit
interface Trk11
unknown-vlans disable
exit
interface Trk12
unknown-vlans disable
exit
interface Trk13
unknown-vlans disable
exit
interface Trk14
unknown-vlans disable
exit
interface Trk15
unknown-vlans disable
exit
interface Trk16
unknown-vlans disable
exit
snmp-server community "public" unrestricted
snmp-server community "private"
router vrrp
ipv4 enable
exit
vlan 1
name "DEFAULT_VLAN"
no untagged C1-C4,C6-C20,D1-D24,E3-E24,F1-F20,Trk2,Trk10,Trk50
untagged A7,F21,Trk1,Trk11-Trk16
no ip address
exit
vlan 2
name "192.168.254.0/29"
tagged Trk1,Trk10
ip address 192.168.254.4 255.255.255.248
vrrp vrid 2
virtual-ip-address 192.168.254.4
priority 255
enable
exit
exit
vlan 6
name "IPTV"
untagged C12
tagged Trk1,Trk13,Trk15
ip address 10.50.50.1 255.255.255.0
ip igmp
exit
vlan 10
name "wired"
tagged Trk1-Trk2
ip address 192.168.10.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 10
virtual-ip-address 192.168.10.1
priority 255
enable
exit
exit
vlan 20
name "Terminal"
tagged C4,Trk1-Trk2,Trk10-Trk12
ip address 192.168.20.254 255.255.255.0
exit
vlan 100
name "LAN_192.168_0_0/23"
untagged C6-C11,C18-C20,D1-D3,D5-D23,E3-E12,E16-E21,F1,F6-F19,Trk2,Trk50
tagged A7,F21,Trk1,Trk11-Trk16
ip address 192.168.0.10 255.255.254.0
vrrp vrid 100
virtual-ip-address 192.168.0.10
priority 255
enable
exit
exit
vlan 101
name "SW-MGMT-172.17.101.0/24"
untagged C13-C17
tagged A7,F21,Trk1,Trk11-Trk16
ip address 172.17.101.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 101
virtual-ip-address 172.17.101.1
priority 255
enable
exit
exit
vlan 110
name "SERVER-172.17.110.1/24"
untagged C3,D4
tagged A7,F21,Trk1,Trk13,Trk16
ip address 172.17.110.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 110
virtual-ip-address 172.17.110.1
priority 255
enable
exit
exit
vlan 111
name "ISCSI"
untagged E13-E15,E22-E24
tagged A7,F21,Trk1,Trk16
no ip address
jumbo
exit
vlan 120
name "BB"
tagged Trk1
no ip address
ip igmp
exit
vlan 130
name "BUILDING-FLOOR0"
untagged F2-F5
tagged Trk1,Trk11-Trk12
ip address 172.17.130.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 130
virtual-ip-address 172.17.130.1
priority 255
enable
exit
exit
vlan 131
name "BUILDING-FLOOR1"
tagged Trk1
ip address 172.17.131.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 131
virtual-ip-address 172.17.131.1
priority 255
enable
exit
exit
vlan 132
name "BUILDING-FLOOR2"
tagged Trk1
ip address 172.17.132.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 132
virtual-ip-address 172.17.132.1
priority 255
enable
exit
exit
vlan 133
name "BUILDING-FLOOR3"
tagged Trk1
ip address 172.17.133.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 133
virtual-ip-address 172.17.133.1
priority 255
enable
exit
exit
vlan 134
name "BUILDING-FLOOR4"
tagged Trk1
ip address 172.17.134.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 134
virtual-ip-address 172.17.134.1
priority 255
enable
exit
exit
vlan 135
name "BUILDING-FLOOR5"
tagged Trk1
ip address 172.17.135.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 135
virtual-ip-address 172.17.135.1
priority 255
enable
exit
exit
vlan 136
name "BUILDING-FLOOR6"
tagged Trk1
ip address 172.17.136.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 136
virtual-ip-address 172.17.136.1
priority 255
enable
exit
exit
vlan 137
name "BYG24"
untagged D24
tagged Trk1,Trk13-Trk16
ip address 172.17.137.1 255.255.255.0
ip helper-address 192.168.0.253
vrrp vrid 137
virtual-ip-address 172.17.137.1
priority 255
enable
exit
exit
vlan 900
name "WIRELESS_MGMT"
tagged C4,Trk1
no ip address
exit
vlan 919
name "WIRELESS_TERMINAL"
tagged C4,Trk1
no ip address
exit
vlan 940
name "WIRELESS_COMPANY"
tagged C4,Trk1
no ip address
exit
vlan 941
name "WIRELESS_GUEST"
tagged C4,Trk1
no ip address
exit
vlan 942
name "WIRELESS_MICROSHHT"
tagged C4,Trk1
no ip address
exit
vlan 997
name "WAN"
untagged C1-C2
tagged A7,F21,Trk1,Trk10-Trk16
no ip address
exit
vlan 999
name "DTHB"
untagged F20
ip address 10.254.254.1 255.255.255.0
exit
spanning-tree Trk1 priority 4
spanning-tree Trk2 priority 4
spanning-tree Trk10 priority 4
spanning-tree Trk11 priority 4
spanning-tree Trk12 priority 4
spanning-tree Trk13 priority 4
spanning-tree Trk14 priority 4
spanning-tree Trk15 priority 4
spanning-tree Trk16 priority 4
spanning-tree Trk50 priority 4
no tftp client
no tftp server
loop-protect C1-C4,C6-C20,D1-D24,E3-E24,F1-F19
loop-protect trap loop-detected
loop-protect disable-timer 900
distributed-trunking peer-keepalive vlan 999
distributed-trunking peer-keepalive destination 10.254.254.2
distributed-trunking role-priority 1
no autorun
no dhcp config-file-update
no dhcp image-file-update
trunk-load-balance L4-based
password manager
password operator
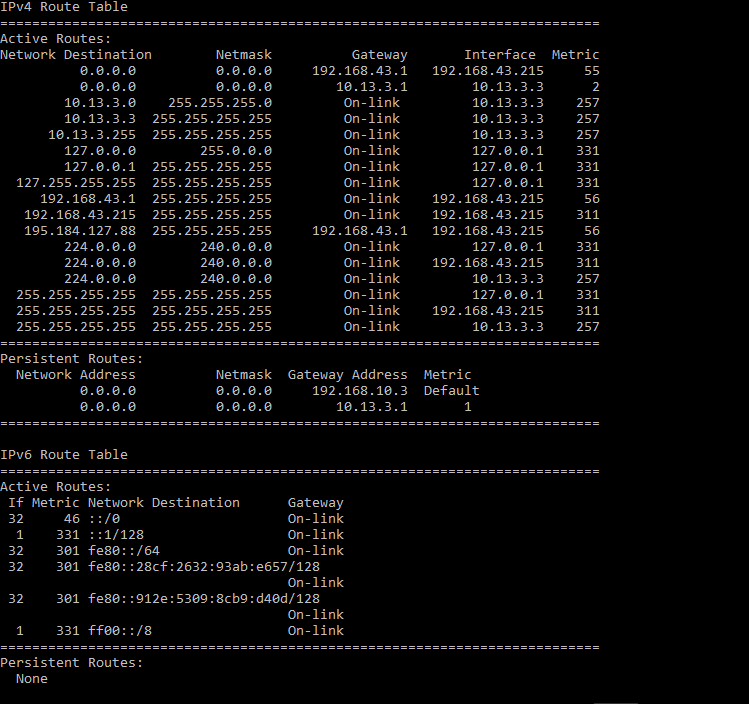
Routes of the Snapgear VPN that works

ASA VPN route
Also I need to inform you that when I connected ASA to the customers network, I could ping any interface of any subnet/network from the ASA which means that routes are correctly set, but as soon I use VPN and try to ping from outside through the tunnel of inside device/server/interface, I cannot reach any of them...
What could possibly causing the issue?
Thank you in advance and have yourself a great day.
- Labels:
-
AnyConnect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2016 05:01 AM
Hi,
Yours is exactly the same issue that another customer faced on this link: https://supportforums.cisco.com/discussion/13142306/failing-access-my-inside-network-through-antconnect
Please follow this link and let me know if that resolved the issue or not.
Thanks,
Vishnu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2016 06:03 AM
Vishnu, are you sure this has to do with reaching internal network, because I don't need to access ASDM from inside via VPN, I need to access the PCs, Servers, Switches and other services of internal network from VPN client (outside)... Honestly I don't see any connection regarding management-access and possible routing issue within inside network.
From Cisco official documentation
If your VPN tunnel terminates on one interface, but you want to manage the ASA by accessing a different interface, you can identify that interface as a management-access interface. For example, if you enter the ASA from the outside interface, this feature lets you connect to the inside interface using ASDM, SSH, Telnet, or SNMP; or you can ping the inside interface when entering from the outside interface. Management access is available via the following VPN tunnel types: IPsec clients, IPsec LAN-to-LAN, and the AnyConnect SSL VPN client.
To specify an interface as a mangement-only interface, enter the following command:
hostname(config)# management access management_interface
where management_interface specifies the name of the management interface you want to access when entering the security appliance from another interface.
You can define only one management-access interface.
Best regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2016 09:47 AM
You are correct that there is no connection between pinging the inside interface and testing connectivity to the internal hosts. The only reason i wanted you to enable management access so that you can test whether you are able to ping the first interface in the local network. If interface is not pingable, then there is no point troubleshooting on switches or router on inside network and inside interface will not allow you to ping it until you enable management-access <interface>.
Please do not get confused by the term management access. Moreover the link that I shared, talks about checking routing on downstream switch for the return traffic. Please go ahead with these tests and let me know.
Hope this helps.
Thanks,
Vishnu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-19-2016 02:44 AM
Hi Vishnu,
Since we visit our customers every Tuesday, I will arrange with my colleague to place the switch in hotel to test this. The only thing that I am not sure, which configuration should I use, dynamic one which is assigning the interface of the ASA and getting the routes from Core switch or static one where I placed the IP and set static routes?
Also I will enable this so I can try to see the result.
Best regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2016 01:21 AM
Actually, I think what might be the issue:
- Customer is running the core switch which is doing all the routing. ASA has VPN connection, and when it is not connected it can ping all the devices (since there is a static route that is set from ASA side), reply can be received because it is directly connected to core switch so it has route to ASA.
(please refer to the attachment - routes.png)
When VPN is on, it has network 10.13.3.0/24 and it probably sends the packets to the networks that are set on the core switch, but I cannot get any reply since there is not static route for network 10.13.3.0/24 via 192.168.10.3 (ASA gateway).
What do you think? Can this be reason?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide