- Cisco Community
- Technology and Support
- Security
- VPN
- Does FTD support authorization-required in tunnel.group ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-01-2023 10:11 PM
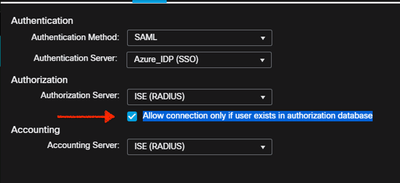
- AuthC with SAML
- AuthZ with ISE
tunnel-group MFA general-attributes
authorization-server-group ISE
accounting-server-group ISE
authorization-required
tunnel-group MFA webvpn-attributes
authentication saml
- A default-group-policy with vpn-filter DENY ACL (user still connected.. No good experience)
- A default-group-policy with vpn-simultaneous-logins 0
Solved! Go to Solution.
- Labels:
-
AnyConnect
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-05-2023 05:43 AM
Ciao, let me explain a little more. In a configuration where authentication and authorization process is splitter, for example authentication with SAML and authorization with RADIUS, during my testing lab I see that if the authentication works fine but authorization reply with an access reject, an Anyconnect user is able to connect with the default group-policy configured on FTD. So it's not mandatory for the authorize-only config to replay with ACCESS-ACCEPT.
With ASA I configure the authorization-required command to force a good response for the authorization. But I didn't find it in FTD.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2023 07:26 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-02-2023 12:07 AM
FTD 7.0 onwards authorization supported :
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-05-2023 05:43 AM
Ciao, let me explain a little more. In a configuration where authentication and authorization process is splitter, for example authentication with SAML and authorization with RADIUS, during my testing lab I see that if the authentication works fine but authorization reply with an access reject, an Anyconnect user is able to connect with the default group-policy configured on FTD. So it's not mandatory for the authorize-only config to replay with ACCESS-ACCEPT.
With ASA I configure the authorization-required command to force a good response for the authorization. But I didn't find it in FTD.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2023 07:26 AM
Resolved !!!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide