- Cisco Community
- Technology and Support
- Security
- VPN
- Re: How apply Two IPsec profile for Two different Tunnel in one router ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 09:42 PM - edited 02-21-2020 09:33 PM
Hi All,
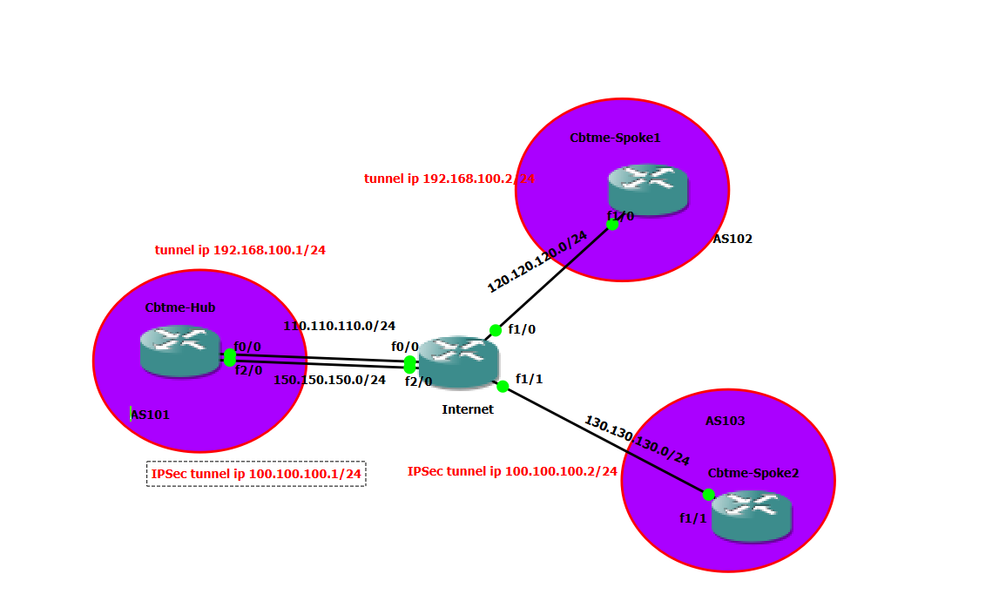
i am beginner in networking. now i try to setup vpn configuration as below network design.Hut Spoke is DMVPN.Hub to spoke 2 is IPSec. I apply different IPSec profile for different Tunnel. Because it is same saturation of operation.Now my PtP IPsec profile is down and when i check debug crypto. i saw below message in attachment. I upload detail error message with attachments.Please help me to solved.
*Feb 8 13:15:24.183: map_db_check_isakmp_profile profile did not match
*Feb 8 13:15:24.183: map_db_find_best did not find matching map
*Feb 8 13:15:24.183: IPSEC(ipsec_process_proposal): proxy identities not supported
*Feb 8 13:15:24.187: IKEv2:(SA ID = 1):There was no IPSEC policy found for received TS
*Feb 8 16:05:23.594: %CRYPTO-6-IKMP_NO_ID_CERT_ADDR_MATCH: ID of 110.110.110.1 (type 1) and certificate addr with
*Feb 8 16:05:23.598: %CRYPTO-6-IKMP_NO_ID_CERT_ADDR_MATCH: ID of 110.110.110.1 (type 1) and certificate addr with
Cbtme-Spoke2(config)#
*Feb 8 16:05:23.622: map_db_check_isakmp_profile profile did not match
*Feb 8 16:05:23.626: map_db_check_isakmp_profile profile did not match
*Feb 8 16:05:23.626: map_db_check_isakmp_profile profile did not match
*Feb 8 16:05:23.626: map_db_find_best did not find matching map
*Feb 8 16:05:23.626: IPSEC(ipsec_process_proposal): proxy identities not supported
Cbtme-Spoke2(config)#
Solved! Go to Solution.
- Labels:
-
IPSEC
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2019 01:45 PM
crypto ikev2 profile IPSec-profile
match identity remote fqdn PALO-ALTO.LAB.NET
identity local fqdn VPN-HUB.LAB.NET
I've never used PA firewall yet, but they support FQDN, email and IP address for IKE identity so the above example configuration for the DMVPN router should hopefully work. You would therefore need to define the local identity on the PA as PALO-ALTO.LAB.NET and remote identity as VPN-HUB.LAB.NET.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2019 04:32 AM
The error message above %CRYPTO-6-IKMP_NO_ID_CERT_ADDR_MATCH: ID would imply you aren't matching the identity retrieved from the peer. In your configuration you are using "identity local dn" but matching on an FQDN. Is the defined FQDN correct, is it the DN defined in the certifcate?
Is this just a lab for testing purposes? If this is a production scenario you probably would not want such an overly complex scenario. If you cannot achieve what you want to do with DMVPN, then you could look at using FlexVPN which supports Hub & Spoke and Spoke-to-Spoke, with AAA authorization for the more complex scenarios.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2019 11:14 AM
Hi,
This lab is testing for production of customer requirements.
I didn't defined dn in certificate.
Fqdn configuration is I thought correct .please don't mind place correct to me how define correctly fqdn in configuration and which one is the best practice to configure ikev2 profile?
I need to use different ike profile because ptp link is using paloalto firewall.Paloalto firewall cannot established to my Cisco router if I am using certificate map command in ike profile.so I am finding other way.I don't have knowledge flexvpn .so I worry to use this tech.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2019 01:45 PM
crypto ikev2 profile IPSec-profile
match identity remote fqdn PALO-ALTO.LAB.NET
identity local fqdn VPN-HUB.LAB.NET
I've never used PA firewall yet, but they support FQDN, email and IP address for IKE identity so the above example configuration for the DMVPN router should hopefully work. You would therefore need to define the local identity on the PA as PALO-ALTO.LAB.NET and remote identity as VPN-HUB.LAB.NET.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2019 02:13 AM - edited 02-10-2019 02:37 AM
Hi,
let me know i am suing below certificate. can i use your method in ike profile ? And then let me know we should be use same identity method both side ? Or can we use one side is certificate map and one side is match identity ?
Cbtme-Hub(config)#do sh crypto pki certificates verbose
Certificate
Status: Available
Version: 3
Certificate Serial Number (hex): 3C0000002D482BB4EB17FF36E400000000002D
Certificate Usage: General Purpose
Issuer:
cn=crypto-SUBCA-CA-1
dc=crypto
dc=local
Subject:
Name: cbtme-hub.crypto.local
cn=cbtme-hub.crypto.local
CRL Distribution Points:
ldap:///CN=crypto-SUBCA-CA-1,CN=SubCA,CN=CDP,CN=Public%20Key%20Services,CN=S ervices,CN=Configuration,DC=crypto,DC=local?certificateRevocationList?base?objec tClass=cRLDistributionPoint
Validity Date:
start date: 10:24:32 UTC Feb 10 2019
end date: 09:18:30 UTC Nov 29 2020
Subject Key Info:
Public Key Algorithm: rsaEncryption
RSA Public Key: (2048 bit)
Signature Algorithm: SHA256 with RSA Encryption
Fingerprint MD5: 26F075F0 4E4E22CE 2E380D90 CB597CD0
Fingerprint SHA1: 56631FFC E6FD00A1 F133C723 EAED1A98 AF1BBF5A
X509v3 extensions:
X509v3 Key Usage: A0000000
Digital Signature
Key Encipherment
X509v3 Subject Key ID: 92EE15EF 58858BD2 A5A30674 5A8AB926 982E20B8
X509v3 Authority Key ID: 5A5B753B 27296974 4BF22100 1B7A52CD C958765E
Authority Info Access:
Extended Key Usage:
Client Auth
1.3.6.1.5.5.8.2.2
IPSEC Tunnel
Associated Trustpoints: my-ca
Key Label: Cbtme-Hub.crypto.local
Key storage device: private config
CA Certificate
Status: Available
Version: 3
Certificate Serial Number (hex): 540000000278F61229E46F3DDB000000000002
Certificate Usage: Signature
Issuer:
cn=crypto-ROOTCA-CA
dc=crypto
dc=local
Subject:
cn=crypto-SUBCA-CA-1
dc=crypto
dc=local
CRL Distribution Points:
ldap:///CN=crypto-ROOTCA-CA,CN=RootCA,CN=CDP,CN=Public%20Key%20Services,CN=S ervices,CN=Configuration,DC=crypto,DC=local?certificateRevocationList?base?objec tClass=cRLDistributionPoint
Validity Date:
start date: 09:08:30 UTC Nov 29 2018
end date: 09:18:30 UTC Nov 29 2020
Subject Key Info:
Public Key Algorithm: rsaEncryption
RSA Public Key: (2048 bit)
Signature Algorithm: SHA256 with RSA Encryption
Fingerprint MD5: FCB6869A D1BC2817 06BD2C11 05DD9524
Fingerprint SHA1: 74EB383E 222320DA A928E502 AAF5C7B9 798199AD
X509v3 extensions:
X509v3 Key Usage: 86000000
Digital Signature
Key Cert Sign
CRL Signature
X509v3 Subject Key ID: 5A5B753B 27296974 4BF22100 1B7A52CD C958765E
X509v3 Basic Constraints:
CA: TRUE
X509v3 Authority Key ID: EAE798FD F125A1E5 846780EF FFC78392 82903CED
Authority Info Access:
Associated Trustpoints: my-ca
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide