- Cisco Community
- Technology and Support
- Security
- VPN
- IPSEC TUNNEL CONFIGRATION
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 08:59 AM - edited 11-29-2021 09:25 AM
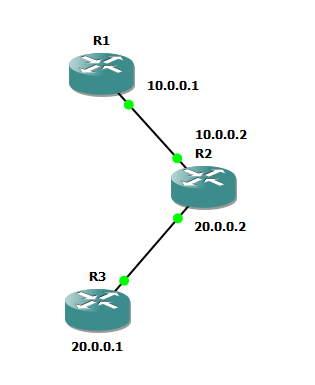
I am trying to setup a IPSEC between R1 and R3. Configured the IP Address as per below snapshot, and IP SEC Session is up and data is flowing encrypted. But As soon as I enable Crypto Map on interface , R1 to R2 and R3 to R2 become unreachable. Please check the attached config and suggest
Solved! Go to Solution.
- Labels:
-
Other VPN Topics
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 09:34 AM
@himanshudwivedi other than adding "crypto map IPSEC" to the external interfaces nothing has changed. You still need to follow the suggestion above.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2021 03:40 AM
because the traffic now is tunnel and hide from R2, this is why IPSec use in Internet to make all other not seen the traffic between two peer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 09:23 AM
@himanshudwivedi you've only configured 1 interface on both R3 and R1, you need to define inside interfaces or loopbacks. You then configure your ACL to encrypt traffic between the local inside network(s) or loopback and the remote networks (not permit any any as you are currently doing). Once the crypto map is enabled on the egress interface, any traffic matching the ACL will be encrypted and sent over the VPN tunnel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 09:27 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 09:34 AM
@himanshudwivedi other than adding "crypto map IPSEC" to the external interfaces nothing has changed. You still need to follow the suggestion above.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-01-2021 08:58 AM
yes it worked
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2021 03:40 AM
because the traffic now is tunnel and hide from R2, this is why IPSec use in Internet to make all other not seen the traffic between two peer.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide