- Cisco Community
- Technology and Support
- Security
- VPN
- It appears Phase 1 completes
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2014 08:52 PM
Hi,
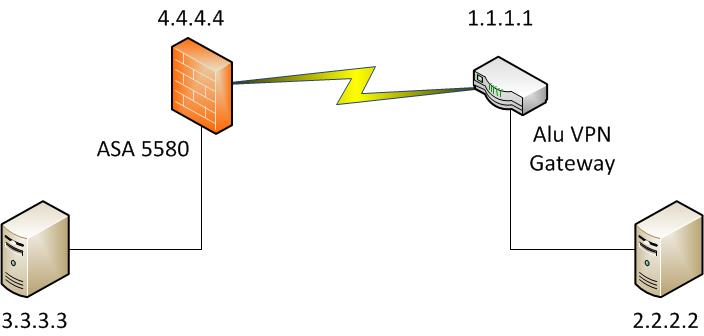
I have a IPsec VPN problem. We have a ASA 5580 to build site to site VPN with ALU VPN gateway (from Partner). The VPN connection is not established at all. We checked pair devices configurations but cannot found any problem so far. I tried to do debug crypto isakmp 127 and got log as below. We are still trying to find out the root cause of it and could I have your advice to this problem please? Thanks. (Actual IP address are changed for confidentialty)
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, IKE SA Proposal # 1, Transform # 1 acceptable Matches global IKE entry # 2
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing ISAKMP SA payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing Fragmentation VID + extended capabilities payload
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE SENDING Message (msgid=0) with payloads : HDR + SA (1) + VENDOR (13) + NONE (0) total
length : 104
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE RECEIVED Message (msgid=0) with payloads : HDR + KE (4) + NONCE (10) + NONE (0) total
length : 180
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, processing ke payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, processing ISA_KE payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, processing nonce payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing ke payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing nonce payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing Cisco Unity VID payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing xauth V6 VID payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, Send IOS VID
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, Constructing ASA spoofing IOS Vendor ID payload (version: 1.0.0, capabilities: 20000001)
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, constructing VID payload
Apr 08 10:43:45 [IKEv1 DEBUG]: IP = 1.1.1.1, Send Altiga/Cisco VPN3000/Cisco ASA GW VID
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, Connection landed on tunnel_group 1.1.1.1
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, Generating keys for Responder...
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE SENDING Message (msgid=0) with payloads : HDR + KE (4) + NONCE (10) + VENDOR (13) +
VENDOR (13) + VENDOR (13) + VENDOR (13) + NONE (0) total length : 256
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE RECEIVED Message (msgid=0) with payloads : HDR + ID (5) + HASH (8) + NOTIFY (11) +
NONE (0) total length : 92
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing ID payload
Apr 08 10:43:45 [IKEv1 DECODE]: Group = 1.1.1.1, IP = 1.1.1.1, ID_IPV4_ADDR ID received
1.1.1.1
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing hash payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, Computing hash for ISAKMP
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing notify payload
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, Connection landed on tunnel_group 1.1.1.1
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing ID payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing hash payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, Computing hash for ISAKMP
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing dpd vid payload
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE SENDING Message (msgid=0) with payloads : HDR + ID (5) + HASH (8) + VENDOR (13) + NONE
(0) total length : 84
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, PHASE 1 COMPLETED
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, Keep-alive type for this connection: None
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, Keep-alives configured on but peer does not support keep-alives (type = None)
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, Starting P1 rekey timer: 21600 seconds.
Apr 08 10:43:45 [IKEv1 DECODE]: IP = 1.1.1.1, IKE Responder starting QM: msg id = 0dbcde8a
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE RECEIVED Message (msgid=dbcde8a) with payloads : HDR + HASH (8) + SA (1) + NONCE (10)
+ KE (4) + ID (5) + ID (5) + NONE (0) total length : 524
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing hash payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing SA payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing nonce payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing ke payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing ISA_KE for PFS in phase 2
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing ID payload
Apr 08 10:43:45 [IKEv1 DECODE]: Group = 1.1.1.1, IP = 1.1.1.1, ID_IPV4_ADDR ID received
2.2.2.2
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Received remote Proxy Host data in ID Payload: Address 2.2.2.2,
Protocol 0, Port 0
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, processing ID payload
Apr 08 10:43:45 [IKEv1 DECODE]: Group = 1.1.1.1, IP = 1.1.1.1, ID_IPV4_ADDR ID received
3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Received local Proxy Host data in ID Payload: Address 3.3.3.3,
Protocol 0, Port 0
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, QM IsRekeyed old sa not found by addr
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 1...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 1, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 2...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 2, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 3...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 3, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 4...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 4, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 5...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 5, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 6...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 6, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 7...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 7, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 8...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 8, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, checking map = Outside_map, seq = 9...
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Static Crypto Map check, map = Outside_map, seq = 9, ACL does not match
proxy IDs src:2.2.2.2 dst:3.3.3.3
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Rejecting IPSec tunnel: no matching crypto map entry for remote proxy
2.2.2.2/255.255.255.255/0/0 local proxy 3.3.3.3/255.255.255.255/0/0 on interface Outside
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, sending notify message
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing blank hash payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing qm hash payload
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE SENDING Message (msgid=456db437) with payloads : HDR + HASH (8) + NOTIFY (11) + NONE
(0) total length : 576
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, QM FSM error (P2 struct &0x3d51e058, mess id 0xdbcde8a)!
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, IKE QM Responder FSM error history (struct &0x3d51e058) <state>,
<event>: QM_DONE, EV_ERROR-->QM_BLD_MSG2, EV_NEGO_SA-->QM_BLD_MSG2, EV_IS_REKEY-->QM_BLD_MSG2, EV_CONFIRM_SA-->QM_BLD_MSG2, EV_PROC_MSG--
>QM_BLD_MSG2, EV_HASH_OK-->QM_BLD_MSG2, NullEvent-->QM_BLD_MSG2, EV_COMP_HASH
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, sending delete/delete with reason message
Apr 08 10:43:45 [IKEv1]: Group = 1.1.1.1, IP = 1.1.1.1, Removing peer from correlator table failed, no match!
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, IKE SA MM:db841932 rcv'd Terminate: state MM_ACTIVE flags
0x00010042, refcnt 1, tuncnt 0
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, IKE SA MM:db841932 terminating: flags 0x01010002, refcnt 0,
tuncnt 0
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, sending delete/delete with reason message
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing blank hash payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing IKE delete payload
Apr 08 10:43:45 [IKEv1 DEBUG]: Group = 1.1.1.1, IP = 1.1.1.1, constructing qm hash payload
Apr 08 10:43:45 [IKEv1]: IP = 1.1.1.1, IKE_DECODE SENDING Message (msgid=c1606511) with payloads : HDR + HASH (8) + DELETE (12) + NONE
(0) total length : 80
Apr 08 10:43:45 [IKEv1]: Ignoring msg to mark SA with dsID 2781184 dead because SA deleted
Apr 08 10:43:46 [IKEv1]: IP = 1.1.1.1, Received encrypted packet with no matching SA, dropping
Solved! Go to Solution.
- Labels:
-
VPN
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-08-2014 06:19 AM
It appears Phase 1 completes successfully but when the remote end sends traffic that should match your crypto map and establish a Phase 2 IPsec SA, it does not match:
Rejecting IPSec tunnel: no matching crypto map entry for remote proxy
Doublecheck that "2.2.2.2 to 3.3.3.3" is in your end's crypto map (and that the obverse is in the remote side).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-08-2014 06:19 AM
It appears Phase 1 completes successfully but when the remote end sends traffic that should match your crypto map and establish a Phase 2 IPsec SA, it does not match:
Rejecting IPSec tunnel: no matching crypto map entry for remote proxy
Doublecheck that "2.2.2.2 to 3.3.3.3" is in your end's crypto map (and that the obverse is in the remote side).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-09-2014 07:51 PM
Thanks Marvin.
After checked and compared crypto map, we found inconsistent configurations on both ends. VPN is up after corrected it.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

