- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- message does not go away in WLC 9800 -> message: Password lifetime has not been configured for yo...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
message does not go away in WLC 9800 -> message: Password lifetime has not been configured for your ID.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2019 06:18 AM - edited 07-05-2021 10:34 AM
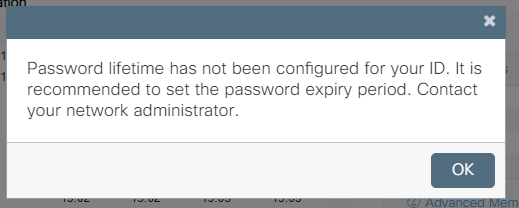
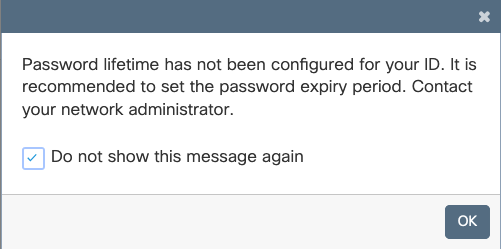
we get a popup message after successful login to the c9800-cl web management interface and the message comes by every login..
that’s the message:
Password lifetime has not been configured for your ID. It is recommended to set the password expiry period. Contact your network administrator.
has an idea how to get this message away?
I had already test the config under AAA Advanced / Password Policy / Validity to set "never expries" , I could not find any options to lifetime?!
Thanks!
Regards,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 05:38 AM
We are getting this pop up message too. It started happening after setting up TACACS+ logins. But it also shows up on the initial local admin account.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-02-2019 10:32 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-07-2019 01:25 AM - edited 10-07-2019 01:27 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 04:11 AM
Has anyone solved this problem ? On 16.2.3 it still happens
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 06:35 AM
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 07:12 AM
Hi Scott,
thanks for your reply. I´m doing Authentication via TACACS+ (which is working). But i also want to configure a local user in case TACACS+ or network fails.
If i´m not configuring a local user i get:
Password lifetime has not been configured for your ID. It is recommended to set the password expiry period. Contact your network administrator.
If i have an local user configured (with the same username) and a AAA password-profile bound (lifetime 1 year)
aaa common-criteria policy TEST
min-length 18
max-length 127
numeric-count 3
upper-case 3
lower-case 3
char-changes 5
lifetime year 1
I`ll get:
Your password has expired. To access this application, you are required to change your password now.
Thanks in advance
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 09:01 AM
I still have the message on all my controllers... I didn’t hide it and I didn’t set any policies as it doesn’t really bother me.
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 01:40 PM
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-23-2020 02:16 PM
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2020 10:25 PM
same happening on ISR4351 - isr4300-universalk9.16.09.06.SPA.bin
i've created user webadmin. but still this message pops up....annoying
username webadmin privilege 15 common-criteria-policy AAA secret 5 $1$2mr6$9tFQ8doSDG9MbdlRhonB21
BORDER-ISR4351#sh run | i aaa aaa new-model aaa local authentication default authorization default aaa authentication login default local aaa authentication webauth default local aaa authorization console aaa authorization exec default local aaa common-criteria policy AAA aaa login success-track-conf-time 24 aaa session-id common ip http authentication aaa login-authentication default ip http authentication aaa exec-authorization default ip http authentication aaa command-authorization 15 default
aaa common-criteria policy AAA min-length 6 max-length 127 char-changes 4 lifetime year 40
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide