- Cisco Community
- Technology and Support
- Security
- Network Access Control
- I have same exact issue on a
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-21-2017 03:08 AM - edited 03-11-2019 12:28 AM
Solved! Go to Solution.
- Labels:
-
AAA
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2017 03:48 PM
I have same exact issue on a Motorola device running android 7
TAC originally recommended I perform the steps in the following youtube video however it did not resolve my issue. It may fix your issue.
https://www.youtube.com/watch?v=z0sRiffVdpg
If I get a solution I'll post it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-13-2018 05:29 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2017 03:48 PM
I have same exact issue on a Motorola device running android 7
TAC originally recommended I perform the steps in the following youtube video however it did not resolve my issue. It may fix your issue.
https://www.youtube.com/watch?v=z0sRiffVdpg
If I get a solution I'll post it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2017 04:13 PM
Thanks for sharing the video and the workaround in the video. I will give it a go and and update here if it works in my case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-29-2017 08:56 AM
Closed out my TAC Case
I needed the fix from the video and an ALC I was using had a typo in it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-29-2017 09:47 AM
If I may ask, is your ISE deployment upgraded from ISE 2.1 to 2.2 or is it an entirely new ISE 2.2 deployment?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-29-2017 09:50 AM
Mine was an upgrade 2.1 to 2.2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-30-2017 06:46 AM
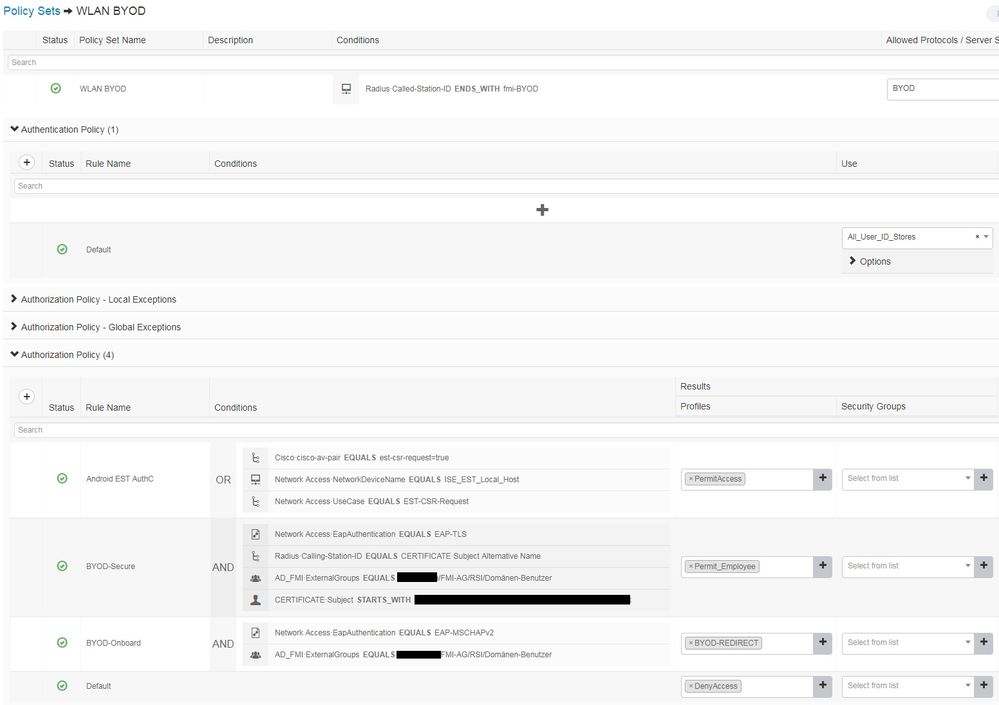
We got it working now, turns out we needed to open another port through the firewall from the BYOD-network (where the Android client is) to the ISE-servers. This was port TCP 8084, as shown in the opening posters log from the Android device. In ISE 2.1 we didn't need to have this port open to on-board Android devices.
.......
"2017.02.21 16:33:32 INFO:EST Server port =8084"
.......
We also applied the new AuthZ rules shown in the Cisco ISE video above.
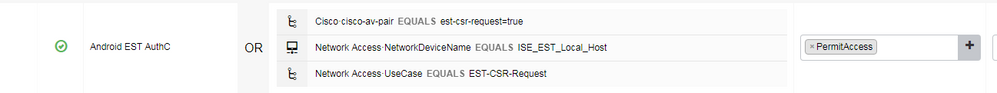
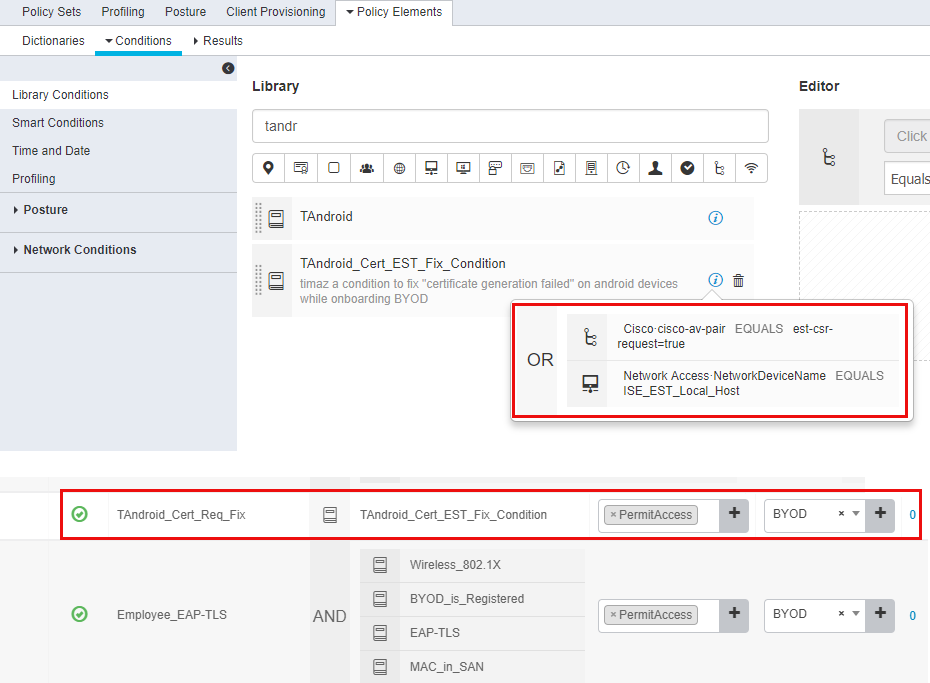
What is not shown in the video is that the certificate request from Android to ISE using EST-CSR is sent using PAP-ASCII, which forced us to make a new top-level condition containing only one of the two "fixes" from the video (both of them work). Because our normal AuthZ top-level conditions are based on "MAB" and "Wireless_802.1X", the EST-CSR request fell through all of our rules and got denied at the end at first but after creating a new top-level condition, it is now working. While this is a deployment specific error based on how you match and group your rules, it's good to know.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-26-2018 04:32 AM
I'm using ISE 2.4 patch 1 and Android 7.0; But this workaround didn't work for me. I'm still getting the same error message stating that "certificate generation failed".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-16-2017 01:53 PM
Hi, i have the exact issue, what do you mean by ALC?
Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2017 05:10 PM
Hi John,
After a bit of delay, we tested the workaround in the youtube video and either of the rules make the BYOD onboarding of Android 6.0 devices work. Thanks for sharing.
Regards,
Rick.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2017 02:19 PM
I would like to add that PAP-ASCII was added to my "Allowed Protocols Services" and it worked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-25-2018 02:42 AM
Hi,
I got the exact same issue with ISE 2.4 and Android 8.0. The spw.log of NSA shows the following:
2018.05.25 11:05:59 ERROR:ISEEnrollmentAsynchTask
2018.05.25 11:05:59 ERROR:java.lang.NullPointerException: Attempt to invoke virtual method 'java.lang.String java.security.cert.Certificate.toString()' on a null object reference
2018.05.25 11:05:59 ERROR:Attempt to invoke virtual method 'java.lang.String java.security.cert.Certificate.toString()' on a null object reference
I followed the instructions given in the video but still no success. My AuthC Rules looks like this:
PAP/ASCII is allowed.
Any help is appreciated,
Marc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-02-2018 11:58 PM
Please use RADIUS live logs to check whether the auth attempt matched correctly. Keep in mind to enter the same password used in joining the WPA2-Enterprise WiFi network, in case single-SSID BYOD, when the Network Setup Assistant app prompts for the network password.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2018 06:22 AM
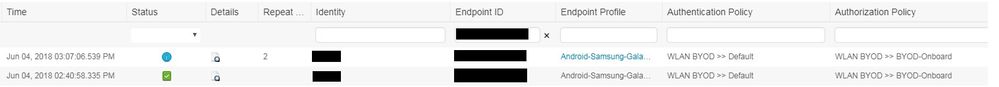
That's everything I get from radius live logs when filtering by the mac address of the android device:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-26-2018 05:08 AM
I also have the exact same issue. I'm using ISE 2.4 patch 1, Android device 7.0 and Network Setup Assistant v2.2.0.54.
I've created a new condition as stated regarding EST but I got no hit on that authz rule.
As seen I put this new authz rule before others, but it shows no hit at all. I found some said that use manual certificate input but it is a silly solution, as BYOD means "simplicity" for regular clients to connect them to the network. If I should deploy certificates manually to 1000 users, I would prefer to not allow anybody to connect their personal devices to the network at all!!
It should not be such a cumbersome; it has been 2 weeks that I'm playing with these stuffs just to allow BYOD connectivity. What a mess ISE!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide