In this blog post, I'm going to add my network access devices (NADs) to my ISE deployment. These are the devices that will be sending RADIUS requests and profiling information to ISE about endpoints on the network and, depending on the policy, ISE will be returning an authorization profile which will give the access device instructions on how to treat that endpoint.
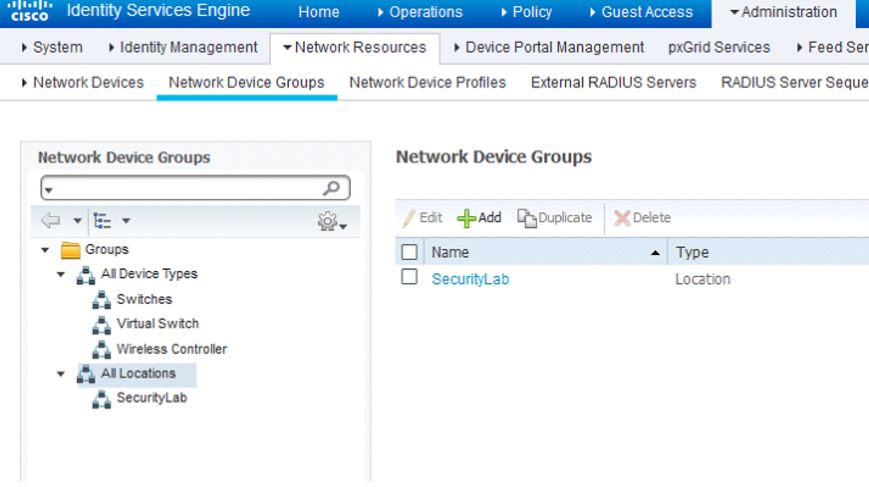
The first thing I like to do prior to adding the NADs is to create logical grouping for them such as their location, device type, etc. Navigate to Administration>Network Resources>Network Device Groups. We have a default grouping of All Device Types and All Locations. For my lab, I'm going to create the following groups: Switches, Virtual Switch, and Wireless Controller under the parent group of All Device Types. I will also create the SecurityLab group under the parent group of All Locations as detailed in the below screenshot:
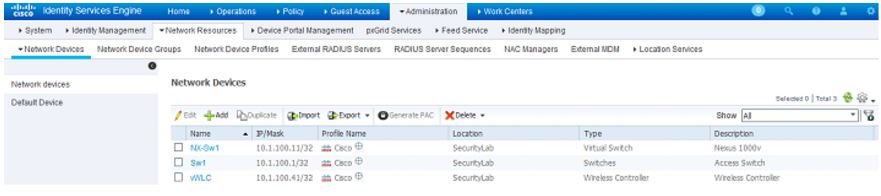
After creating my groups, I'm going to add my NADs.
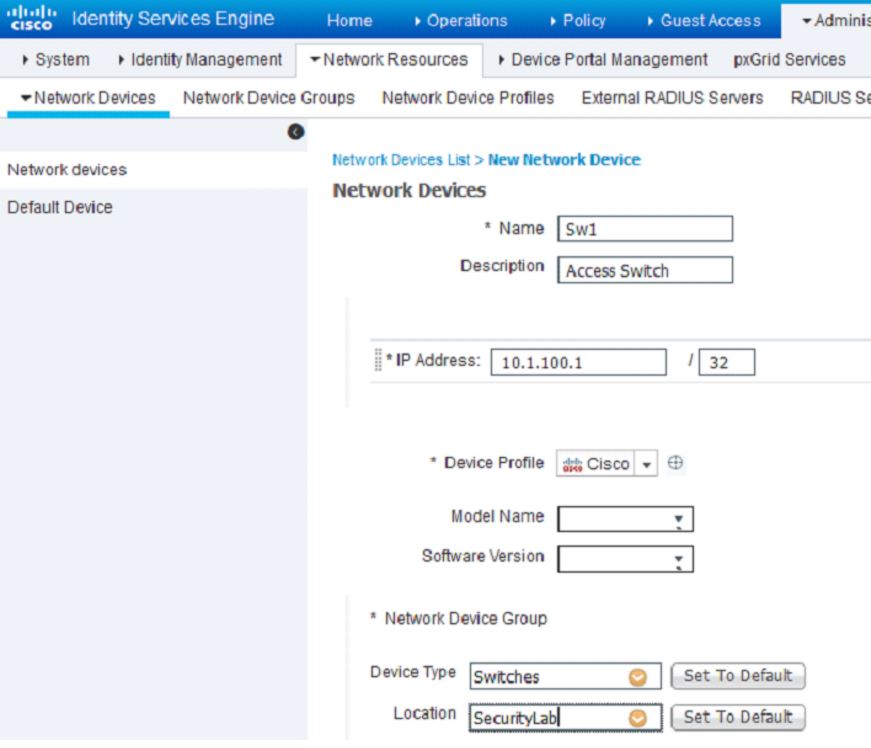
To add these devices, navigate to Administration>Network Resources>Network Devices and clickAdd. While I'm adding my devices, I always make sure to add the device to the logical groups I created for Device Type and Location:
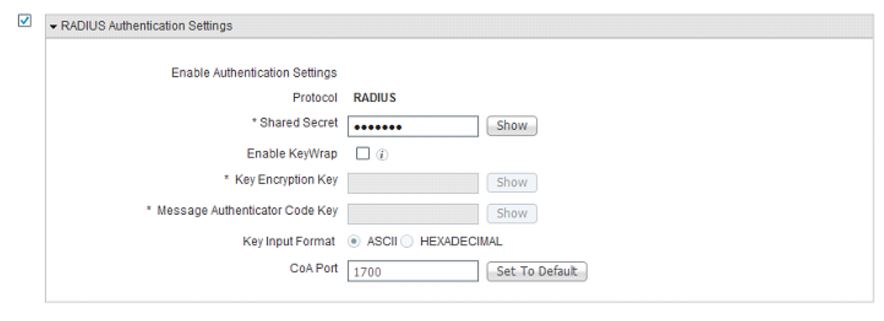
Check the box next to RADIUS Authentication Settings and keep everything at it's default except add a secret in the Shared Secret field. In this case, I'm going to use networknode as my secret:
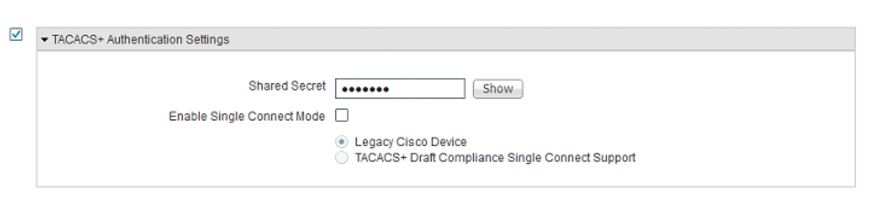
Check the box next to TACACS+ Authentication Settings and enter your preferred shared secret:
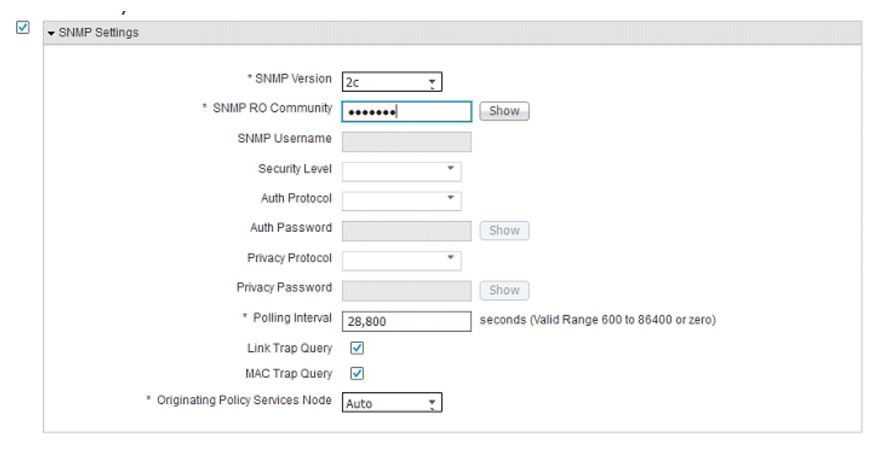
Check the box next to SNMP Settings. You have several SNMP settings you can choose but for the purpose of the lab, I'm going to stick with selecting 2c on the SNMP Version drop-down. Under theSNMP RO Community field, enter the community string of your choosing. You can adjust the polling interval and originating PSN if you choose to do so but since this is a lab, I only have one PSN so there's no need to make any adjustments:
Leave the Trustsec box unchecked for now. We will go over that in a separate TrustSec. ClickSubmit when you are done configuring your NAD.
Do the above for all the NADs in your deployment or lab.