ASA Multi-Context virtualizes single hardware and transforms it into multiple small firewalls which can help the enterprise to segment their networks efficiently and manage effectively. Similarly, service providers leverage this to provide firewall services to various customers in a cost-effective manner. Cisco FTD Multi-instance attempts to meet the new requirements of the customers seeking next-generation firewall capabilities.
Customers moving from ASA Multi context deployment to FTD Multi-instance deployment may find it challenging. This blog describes the tools required for migration and resources available for accelerating the migration process.
To understand the migration process, let us consider an example of migrating one ASA context to an FTD. Different challenges arise when merging multiple ASA context; for example, some of the challenges include merging policies and configurations. This article does not cover on merging multiple ASA context and clustering aspects.
The following figure depicts a typical migration process:
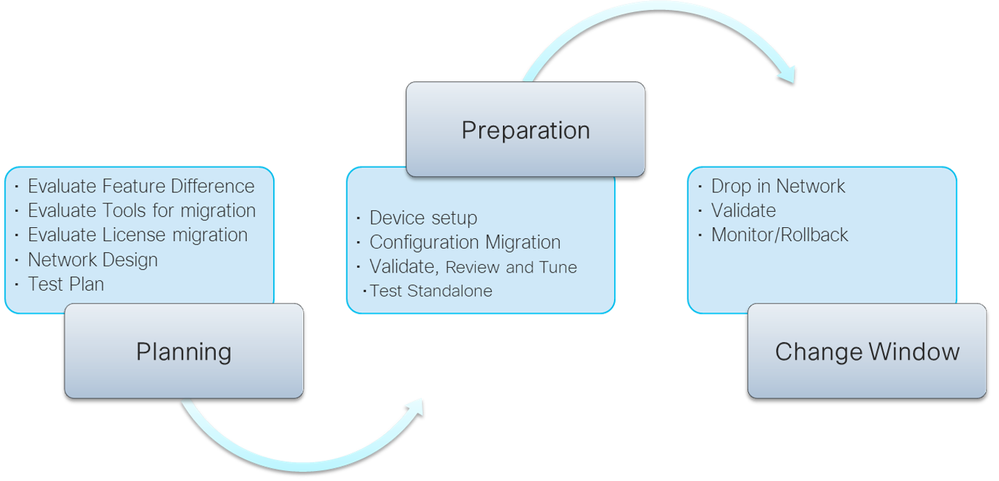
As a first step, you must prepare a thorough plan that includes sizing, interface allocations, and so on.
Consider the following questions during migration:
- What are the gaps between ASA and FTD solution?
Review the ASA configuration and understand the features which are not supported by FTD and then evaluate the critical unsupported features and plan steps to mitigate them. In ASA multi-context to FTD multi-instance migration, the primary gap is scaling. Therefore, if you cannot map a context with an instance, then merge multiple contexts in a single instance. Also, plan for migrating the license as well, as ASA and FTD cannot use the same license.
- How do you size your instances?
It is essential to size FTD instances; that is, you must determine the required resource profile and how interfaces must be associated. The resource allocation in Firepower chassis is based on core, which is much simpler compared to multi-context resource allocation. You can create different resource profiles based on the number of concurrent connection allocations. Each instance requires one “instance” license along with usual feature licenses, therefore, consider additional license requirements as well.
- What about licenses?
FTD uses Smart licensing, and therefore, you must migrate the ASA PAK licenses to smart licenses. Typically, the license migration must be performed after migrating ASA to FTD. Cisco Smart Software Manager allows you to convert the ASA PAK license to smart licenses. For more information on smart license conversion, see How to Convert a Classic License or PAK to a Smart License.
- How to configure the management interface for the instances?
There are several ways to decide the allocation of the management interface for your instance. It is recommended to create a port channel with two interfaces and share along with all instances.
- Do you need an event interface?
If you expect a considerable event load on the deployment, you can consider a separate event interface instead of leveraging the management interface. This consideration isolates event traffic from the management traffic and thereby enhances the performance of FMC by improving the time taken to apply the policy to FTDs. However, to ensure a fault-tolerant channel, you must create a port channel which reserves another two 10 Gig interfaces and reduces the number of interfaces available for data.
- How to do data interface sharing?
The most critical being the data interface and with limited ports, you must consider various aspects such as fault tolerance, instance sharing to cascade instances, and so on.
You must create port channels to provide a fault tolerant channel. For a cascade multi-context configuration, that is, when the outbound traffic from one context becomes inbound traffic for another context, you must use ‘Data-sharing’ interfaces.
See the Shared Interface Best Practices for best practices for the shared interface.
You must consider the tools required for migrating the configuration and the configuration that needs to be migrated manually. You can leverage the Cisco Firepower Migration tool to migrate ASA firewall rules, NAT rules, static route and critical interface configuration to FTD, which covers a significant volume of the ASA configuration. The remaining configuration must be migrated manually. There are other third-party vendor tools for migration, but this article focuses only on Cisco Firepower Migration Tool.
Additionally, you must plan tests to be performed at various stages for a successful migration with minimal network disruption. You must plan the activities to monitor the new deployment and have a rollback plan handy if the migration fails.
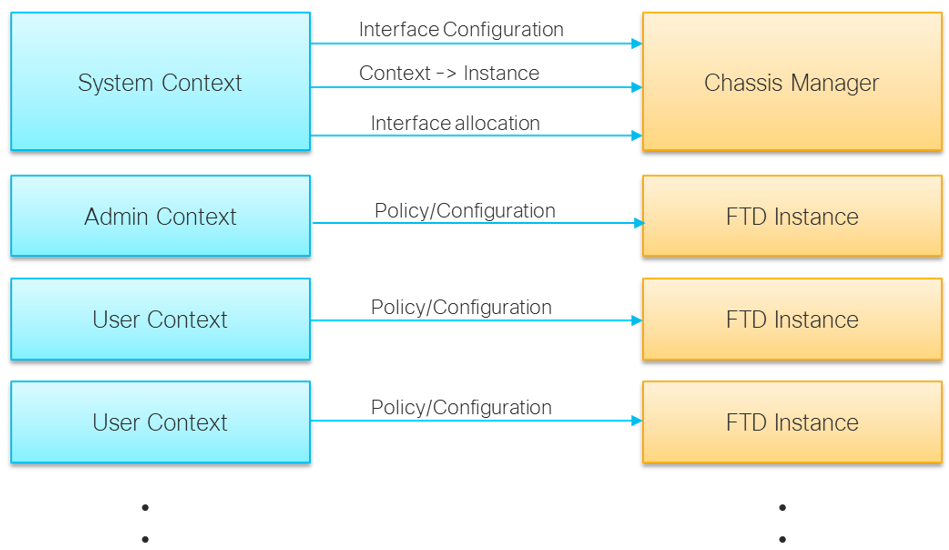
The following diagram shows how different context configuration of ASA multi-context maps to FTD multi-instance solution:
Once the migration plan is in place, the next phase includes the execution phase where you prepare for migration and then perform the actual switch over to the newly migrated device during the change window. At a high level, this phase includes the following major steps shown below:
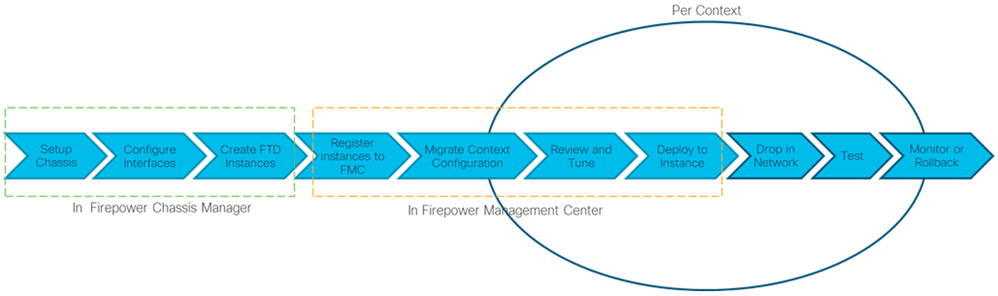
After setting up the chassis and configuration interfaces, the next steps are executed based on the context. You can create all instances at once and register them in FMC. It is recommended to replace the context with FTD instance one at a time except for the cases where you have cascaded the contexts.
The following section describes this procedure:
- Setup Chassis.
Deploy FTD 4100/9300 in your network and connect interfaces. Power on the appliance. Follow the instructions provided in the Cisco Firepower 4100 Getting Started Guide or Cisco Firepower 9300 Getting Started Guide to complete the procedure.
- Configure Interfaces and Resource Profiles on Chassis Manager.
- Create all port channels.
- Define management and event interfaces.
- Create sub and shared interfaces to leverage the big channel with multiple instances or where instance cascading is required.
This configuration is similar to the interface configuration in a system context in the ASA Multi-Context.
- Create FTD instances on Chassis Manager and allocate necessary resources.
- Create an FTD instance based on the context.
- Select Resource profile.
- Assign interfaces which match the interfaces allocated to the context.
- Use the data-sharing interface where cascade instances are required.
Make sure to assign the same number of interfaces which have been allocated to context.
You can complete all chassis manager activities for all ASA user contexts by repeating step 3.
- Register all the instances in FMC.
Maintain the device display name like your context names for easy mapping.
- Migrate configuration to an instance.
The actual configuration conversion starts from this step onwards. We can use the Firepower Migration tool to migrate most of the configuration with little manual intervention. For more information, see Cisco Firepower Migration Tool. If you are using the tool for the first time, we recommend you go through the configuration guides. Some configurations cannot be migrated by the tool and therefore, must be migrated manually. It is assumed that you have identified all critical gaps in the planning phase.
- Launch the Firepower Migration tool and login. Select the source ASA or upload the show tech support. The tool provides you with an option to select the context you want to migrate.
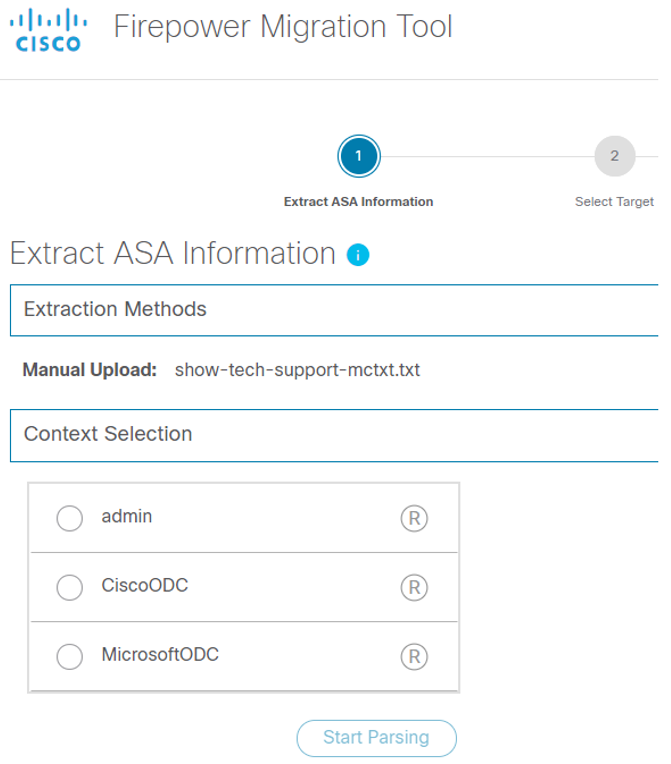
In this window, you will not see the system context as it maps to the chassis manager configuration, which you have already done.
- Select the instance as shown in the following figure:
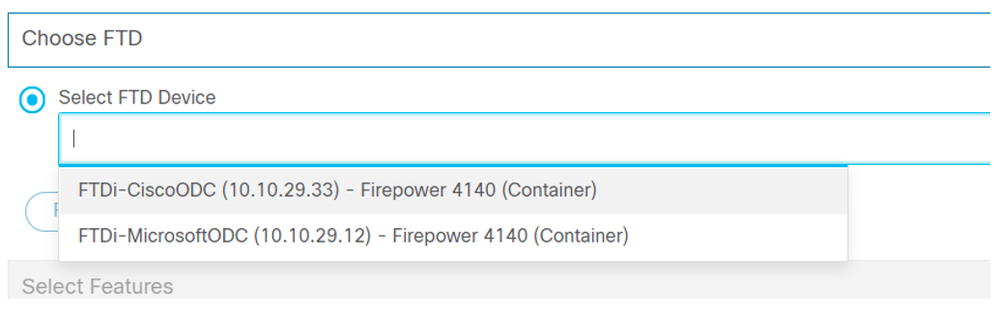
An FTD instance with a suffix ‘Container’ appears. Select the instance corresponding to context.
- In the subsequent step, you must map the interfaces:
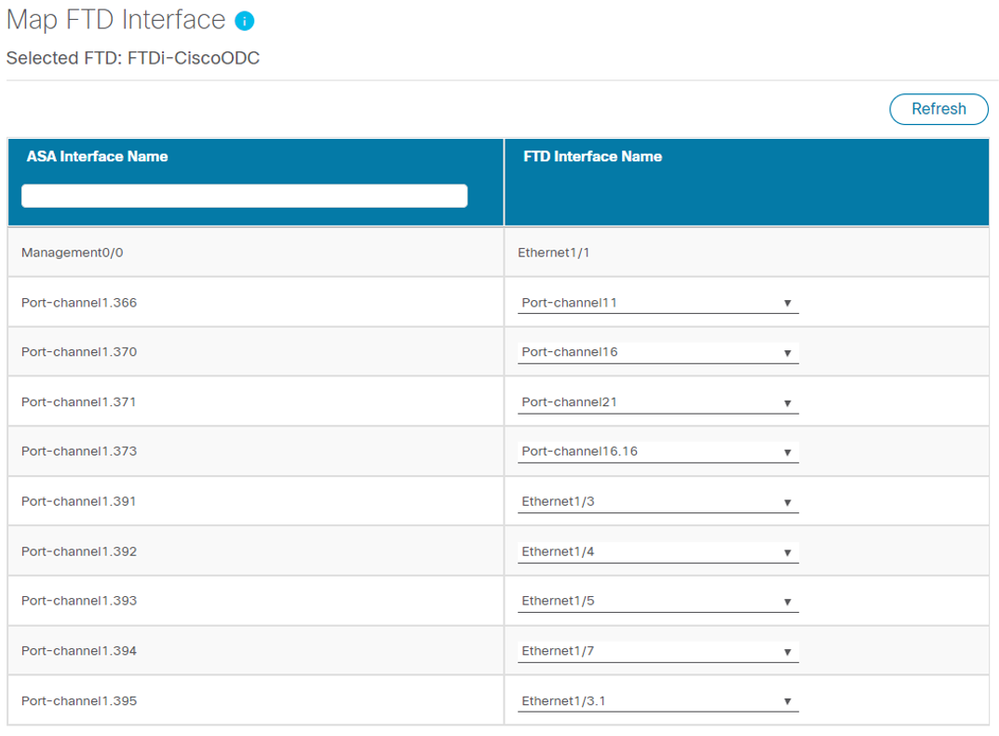
- If there are insufficient interfaces, you cannot proceed from this step. However, you can complete this step by adding the missing interfaces to the target FTD in FMC and clicking the Refresh button.
- If you are adding interface through chassis manager, then add the required interfaces and save the instance. Go to FMC and synchronize the interface on that instance and save the changes. Refresh the screen on the Firepower Migration tool to get those interfaces for mapping.
Now the tool converts ASA firewall rules, NAT rules, static routes, and basic interface configuration. Also, the tool generates a premigration report which provides configurations that support and does not support migration.
- Verify the result with your analysis done during the planning stage. Use this report to refer during the manual migration of the configurations. Review them in the tool and tune as required. After completing the review, migrate the firewall rules, NAT, static route, and interfaces from the Firepower Migration tool by pushing the configuration to FMC.
- Download the post-migration report. Use this report along with the pre-migration report to understand the configurations which are not migrated from the supported configurations, i.e. firewall rules, NAT rules, static route, and interface.
- Login to FMC and manually configure the ASA configurations which are not migrated by the tool.
- Review and Tune.
Pre and Post-migration report from the “Firepower Migration Tool” is very critical. You should thoroughly review and ensure all essential configuration is migrated.
Make sure to consider the disabled rules either by tuning the enabled rules appropriately or by inserting new rules to match the posture of FTD with ASA w.r.t allowing legitimate traffic and blocking illegitimate traffic.
You can tune the interface IP configuration if you don’t want to use the ASA IP addresses.
- Deploy to the device.
Deploy the configuration to FTD device and review the configuration on the device as a standalone. Perform necessary tests on the FTD device before you connect it to the network to replace ASA.
- Drop in Network.
While dropping in the network with cascaded contexts, you must drop in all FTD instances corresponding to the cascaded ASA’s contexts.
If you are planning to use the same IP address as your ASA contexts, then bring down ASA interfaces and clear ARP caches on surrounding switch infrastructure. Otherwise, update routing configuration in surrounding infrastructure which points to FTD interface’s IP addresses instead of the ASA interface’s IP addresses.
- Test
Once the FTD instances are in the traffic path, perform the necessary tests as planned during the planning phase.
- Monitor or rollback
If the test pass, you could migrate the next context to FTD instance. If the test fails, rollback to context and return to the planning phase.
Once you complete the migration, start migrating your license as well.
I hope you had a tremendous migrating experience!
- Vikas Sharma
