Certificate Templates can play a big role in ISE and pxGrid integration in our lab and most likely in any production rollout of ISE. While recent versions of ISE do support using ISE as a certificate authority, most production implementations of ISE that I've seen leverage an Active Directory Certificate Authority. In later blog posts, I will end up going through a lot of these same steps using the ISE CA but I'm going to start with doing it via a Microsoft CA.
So why are certificates so important? The first things that come to mind is certificate authentication with dot1x. User certificates, computer certificates, or both can be used to authenticate to ISE and allow access to the network. You can also have BYOD certificate templates which are issued via SCEP in ISE to provide access to mobile devices and other BYOD machines that are not part of your Active Directory domain and you still want them to be able to have some access to the network beyond guest access or if you don't want them to have to sign into a guest portal every time they bring that device onto your network. The pxGrid certificates will be used to authenticate and establish secure communication between your ISE nodes on your network and pxGrid clients whether they be Cisco products or a third-party vendor.
If you're unfamiliar with pxGrid, It's a pretty cool concept. Instead of having to create single-purpose platform-specific APIs to send information between ISE and other products, Cisco developed a created a unified framework for other vendors to use to share context and information bidirectionally. An example of this is say you have Product 1 that has an AD Agent and can map usernames to IP addresses - like your average firewall. While this is great for identifying users, it really doesn't get very specific on where they are accessing the network from, what kind of device, what policy is being applied, SGT, etc. Also, what if they're signing onto the network without a AD account? This would be the case with a sponsor account created through ISE. With pxGrid, the firewall would be able to get granular contextual information from ISE that you otherwise wouldn't see in Active Directory such as their location, what kind of device, their authorization policy, security group tags that are assigned (if any), etc.
In some cases, this firewall could take it a step further and use this pxGrid communicate to mitigate an incident on the network. A good example of this is if you have a client download malware and at the time of download, the firewall could not issue a disposition on that file and allowed the client to download it. After some time, the firewall might discover that file was malware and while it can now block future downloads of that file, it still initially got past the firewall in the first place and there's a patient zero somewhere on your network. With pxGrid mitigation, that firewall could send a message to ISE to blacklist that device from the network until the IT or Security team has a chance to clean the device.
Pretty cool stuff if you ask me. If you're interested, here are some links for reference:
I'm going to walk you through the configuration of the certificate templates. Go to your Start menu and open Certification Authority. On this MMC, highlight the Certificate Templates folder and right-click. Choose Manage
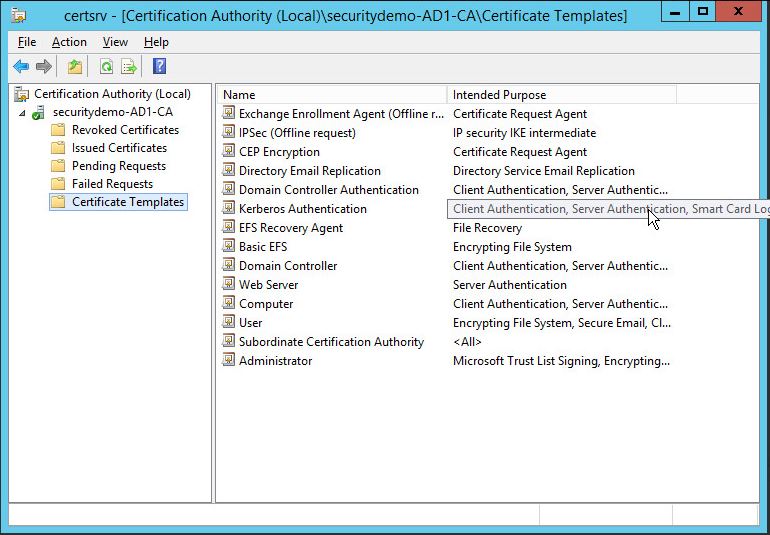
The Certificate Template Console window will open. Highlight the User certificate template first and right-click on it. Choose Duplicate Template.
On the duplicated template, click on the General tab and create a logical name for this template. For me, I was going to be pushing this User certificate down through my group policy so it's aptly named GPO-USER for me

On the Request Handling tab, uncheck the Allow private key to be exported box. There is no reason for this certificate that we need to be allowing the private key to be exported.
On the Extensions tab, highlight the Application Policies and click Edit. Add the Server Authentication policy to the Application Policies
On the Security tab, highlight Domain Users and check the Allow boxes for Read, Enroll, and Autoenroll. This will be important later when we push this through our Group Policy to auto-enroll the user when they sign on our network.
If you want to exclude e-mail addresses from this Certificate template, I would advise going to the Subject Name tab and unchecking email. If not, your certificate will not issue for the user if the user does not have an email address specified in Active Directory.
Click Ok to close this window and save the template.
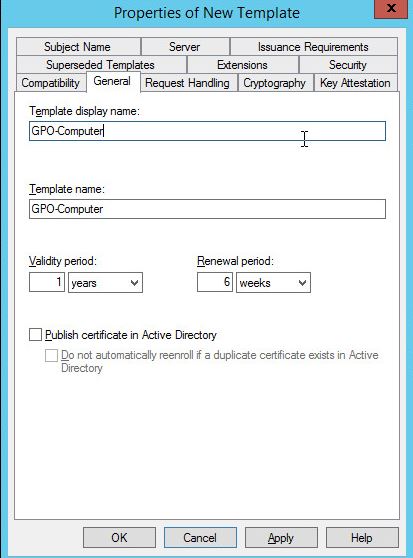
Next, we will create our computer certificate template. Highlight the Workstation Authentication template and duplicate it just like you did for the User template. On the General tab, choose a good name for this template. For me, I choose GPO-Computer since this will be the Computer certificate template I will be using with my Group Policy.
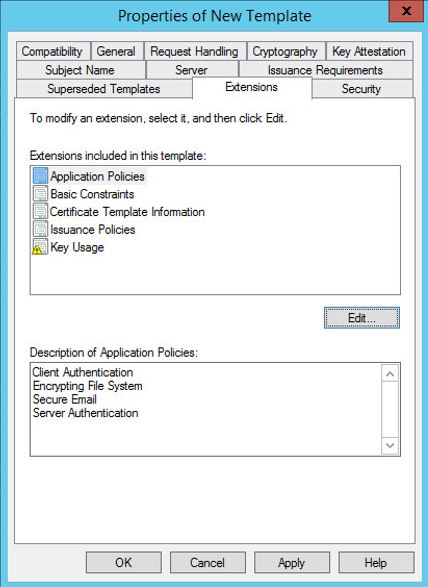
Under the Extensions tab for this template, highlight Application Policies and click Edit. Click Add and choose Server Authentication like we did for the User certificate template:

On the Security tab, highlight Domain Computers and check the Allow boxes for Read, Enroll, and Autoenroll

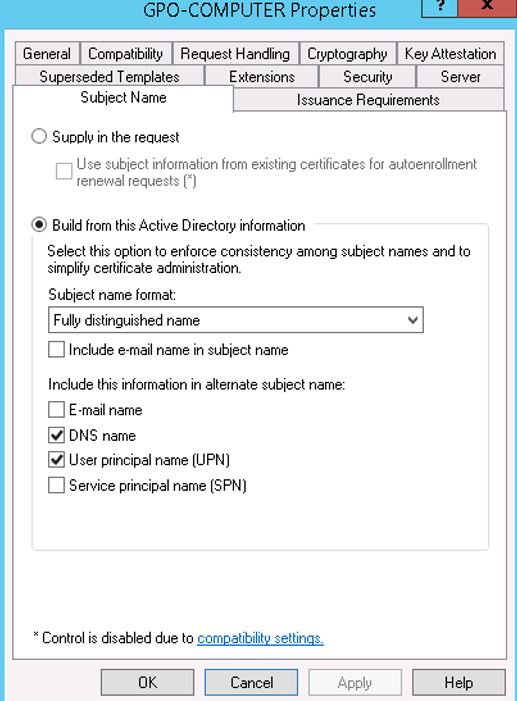
On the Subject Name tab, check the User Principle Name (UPN) box and under Subject Name Format, I usually change it to Fully distinguished name:
Click Ok to close this window and save your certificate template.
Next, we will configure our pxGrid certificate template. Highlight the previously created GPO-User template and duplicate this template. On the General tab, name this template Pxgrid.

On the Security tab, highlight Domain Users and be sure to uncheck autoenroll since we don't want this template to be issued through our Group Policy at any point.
On the Extensions tab, edit the Application Policies like we have in previous steps and remove everything except Client Authentication and Server Authentication. These are the critical extensions needed for the pxGrid certificates:

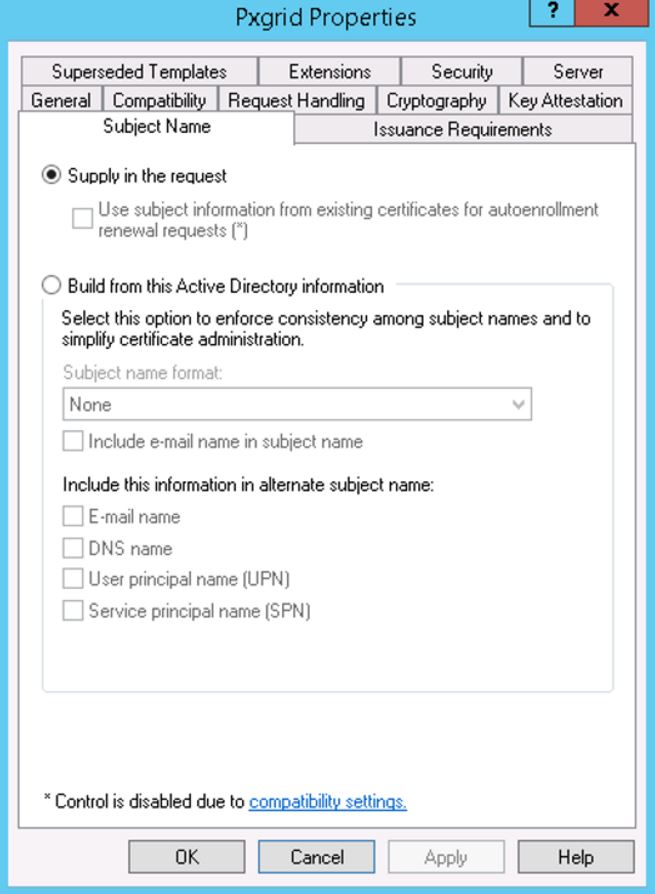
On the Subject Name tab, choose the radio button for Supply in the request:
Click Ok to close the window and save the certificate template.
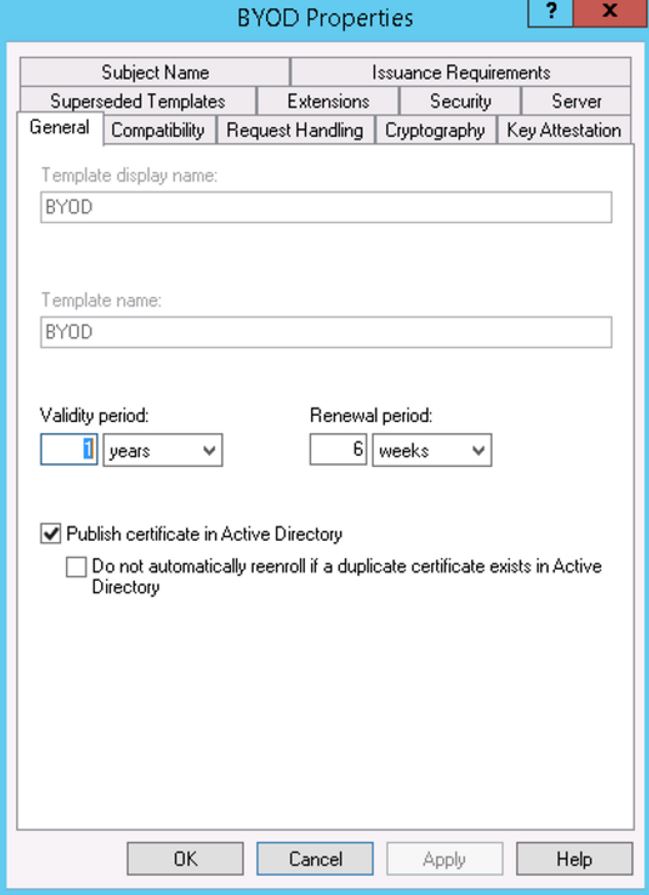
Now we're going to create a BYOD template. One thing to note: in most cases, the ISE CA makes for a great CA for BYOD certificates and much more efficient but I'm going to go through the configuration of it on the AD CA server to go over it. Highlight the User template and duplicate it again. This time we're going to name it BYOD.
Under the Subject Name tab, change it to the radios button of Supply in the request:
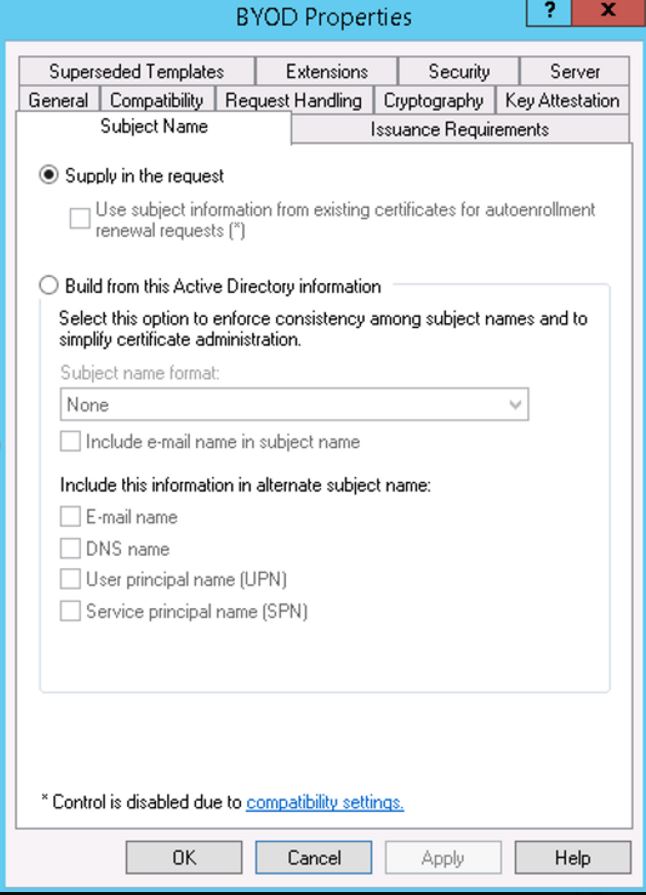
Under the Subject Name tab, change it to the radios button of Supply in the request:

Click Ok to close the window and save the template.
Close the Certificate Templates Console window. On the Certification Authority window, highlight the Certificate Templates folder and right-click. Choose New>Certificate Template to Issue and in the pop-up, highlight the templates you just created and click Ok. This will publish the new templates to the Certificate Authority and make them usable
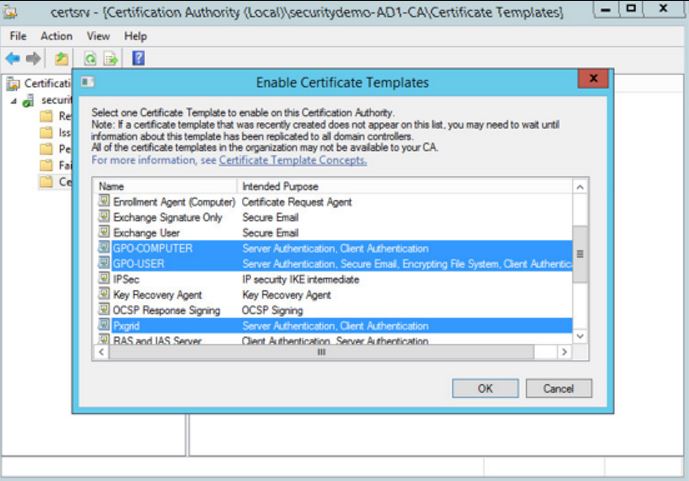
At this point, you should be able to close out the Certification Authority Window. You've now created your BYOD, User, Computer and Pxgrid templates for use and published them in your CA.
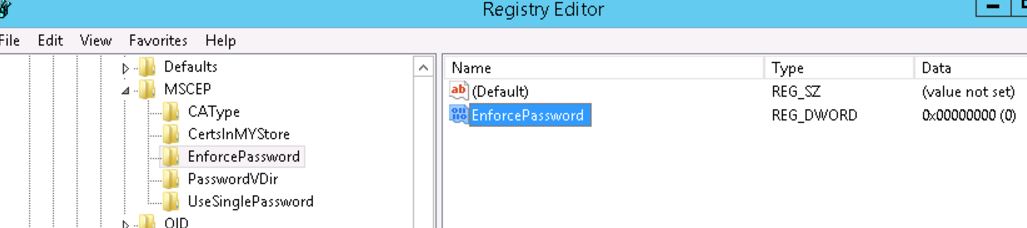
For the BYOD certificate, that will be published in the future through SCEP in my lab so there are some additional steps we would need to take in order to get that ready. Go to your Start menu and type in regedit to edit the registry.
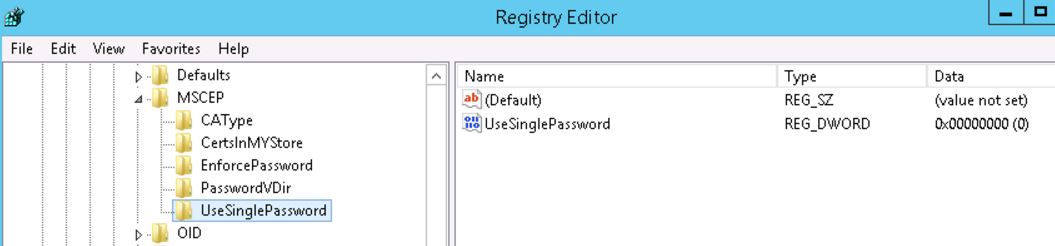
In the registry tree, navigate to HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Cryptography>MSCEP
We will want to make sure that we change the following data values for the following to BYOD:
EncryptionTemplate
GeneralPurposeTemplate
SignatureTemplate

Under the EnforcePassword folder, change the value to 0:
Ensure that UseSinglePassword is set to 0 as well: