- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: LAN Routing problem
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
LAN Routing problem
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-04-2012 09:49 PM - edited 03-07-2019 05:58 AM
HI
I have a network with CISCO catalyst L3 switch and other L2 switches with 17 vlans configured as shown in the figure
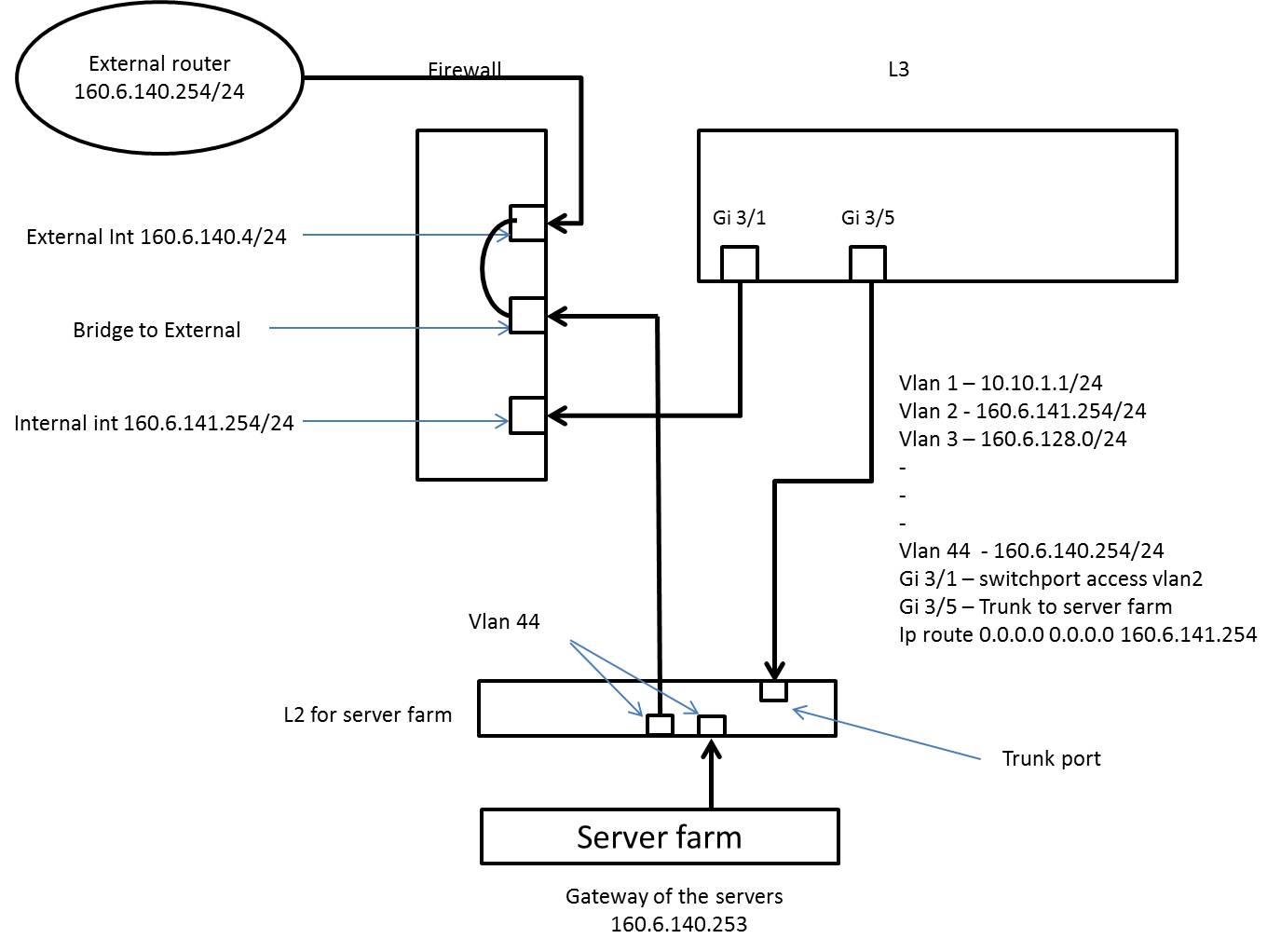
The problem that is being faced is that except vlan 2 no other vlan is able to access the external network. All other vlans cannot ping 160.6.140.254 but they can ping their gateway. Rest all vlans, some times are able to ping 160.6.141.254 and sometimes not. And if I remove vlan 44 or disconnect Gi 3/5, than vlan2 is also not able to reach 160.6.140.254 which idealy it should do, via firewall. I have reinstalled and reconfigured the firewall but still have the same problem.
The vlan 1 is for the switches management.
Vlan44 is bridged to external as our DC is ADC and needs to replicate with CDC in external network. (This was thought as shortcut rather than opening the ports in firewall). If I remove vlan 44 and make Gi 3/1 no switchport with an IP 160.6.136.1/24, change the ip of internal interface as 160.6.136.254/24 and also create a new IP route 0.0.0.0 0.0.0.0 160.6.136.254 then none of the vlans are able to ping the servers and the external router, but L3 still can ping the external router.
-------- (Rest all the L3 ports are trunk)-----------
Please help to reconfigure the L3 and resolve the problem.
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2012 12:14 AM
Hi Harish,
Do you have ip routing enabled globally ?
Regards,
Smitesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2012 12:53 AM
yes ip routing is enables in L3 and globally
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2012 06:41 AM
Harish,
As per my understanding of your topology, there are multiple areas which need correction:
- first & foremost, you cannot have same subnets across two sites. Atleast there is not an easy way to do this, this requires extending of vlans and it cannot be done across an L3 router.
- in your diagram, the device connected to Firewall & server farm switch, is it a L3 device or L2? If its L2 then you seriously shouldn't bridge the two ports for vlan 44 subnet, instead simply put both of them in Vlan 44. If its L3 device, then I really do not see any reason for you to use two L3 devices as a single L3 switch or router would have enabled connectivity of servers with external router. Just keep one device as L3 device which will make routing decision for all the vlans
try simplifying your topology, something like this, if possible:
L2 with vlan 44--trunk-- L3 switch with all other vlans ---vlan44-- firewall -- External router
use vlan interfaces on L3 switch as gateway for all hosts present in various vlans, Put a default route on L3 switch pointing towards external router, this should be able to provide connectivity
- you have same ip's configured on L3 switch's vlan2 & Internal interface on left, vlan 44 on L3 switch & External router. they cannot be same
- I am assuming that you are running your firewall in transparent mode as otherwise you cannot have this 160.6.140.0/24 subnet on the inside & outside(connected to external router) interface
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2012 07:04 AM
Are you using a routing protocol?
Could you post at least the config you have on the switches and the firewall if possible?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2012 02:26 AM
This is the current configuration
!
vtp domain ''
vtp mode transparent
ip subnet-zero
!
spanning-tree extend system-id
!
!
vlan 2-3
!
vlan 4
name ****
!
vlan 5
!
vlan 6
name ****
!
vlan 7-16
!
vlan 17
name ****
!
vlan 18-22
!
vlan 23
name ****
!
vlan 44
name ****
!
vlan 142,160-162
!
interface GigabitEthernet1/1
switchport trunk encapsulation dot1q
switchport mode trunk
no cdp enable
!
interface GigabitEthernet1/2
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/1
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/2
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/3
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/4
switchport access vlan 3
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/5
description SERVER
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet2/6
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet3/1
description FIREWALL
switchport access vlan 2
switchport mode access
!
interface GigabitEthernet3/2
description connected to rack1 l2
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet3/3
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet3/4
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet3/5
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
no cdp enable
!
interface GigabitEthernet3/6
description ****
switchport trunk encapsulation dot1q
switchport mode trunk
no cdp enable
!
interface Vlan1
description "Switch management"
ip address 10.10.1.1 255.255.255.0
!
interface Vlan2
description ****
ip address 160.6.141.1 255.255.255.0
!
interface Vlan3
description ****
ip address 160.6.134.1 255.255.255.128
!
interface Vlan4
description ****
ip address 160.6.134.129 255.255.255.128
ip access-group 104 in
!
interface Vlan5
description ****
ip address 160.6.135.1 255.255.255.128
!
interface Vlan6
description ****
ip address 160.6.135.129 255.255.255.128
ip access-group 106 in
!
interface Vlan10
description ****
ip address 10.10.10.1 255.255.255.0
ip helper-address 10.10.1.50
!
interface Vlan11
description ****
ip address 160.6.128.1 255.255.255.128
!
interface Vlan12
description ****
ip address 10.10.12.1 255.255.255.0
ip helper-address 10.10.1.50
!
interface Vlan13
description ****
ip address 160.6.128.129 255.255.255.128
!
interface Vlan14
description ****
ip address 10.10.14.1 255.255.255.0
ip helper-address 10.10.1.50
!
interface Vlan15
description ****
ip address 160.6.131.1 255.255.255.128
!
interface Vlan16
description ****
ip address 160.6.132.1 255.255.255.128
!
interface Vlan17
description ****
ip address 160.6.133.1 255.255.255.0
!
interface Vlan18
description ****
ip address 160.6.130.1 255.255.255.128
!
interface Vlan19
description ****
ip address 160.6.130.129 255.255.255.128
!
interface Vlan20
description "****
ip address 10.10.20.1 255.255.255.0
ip helper-address 10.10.1.50
!
interface Vlan21
description ****
ip address 160.6.129.1 255.255.255.0
!
interface Vlan22
description ****
ip address 10.10.22.1 255.255.255.0
!
interface Vlan23
no ip address
shutdown
!
interface Vlan44
ip address 160.6.140.253 255.255.255.0
!
interface Vlan75
no ip address
shutdown
!
interface Vlan133
ip address 10.10.18.1 255.255.255.0
!
interface Vlan135
ip address 10.10.5.1 255.255.255.0
!
interface Vlan142
ip address 10.10.2.1 255.255.255.0
!
interface Vlan222
ip address 160.6.143.1 255.255.255.0
!
ip classless
ip route 0.0.0.0 0.0.0.0 160.6.141.254
ip http server
!
!
access-list dynamic-extended
!
!
!
end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-08-2012 07:53 AM
Please hlp
as other all vlans except vlan 2 and vlan 44 are not able to able to communicate with the external world.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-08-2012 09:04 PM
Is the link from L2 to Router/Firewall a trunk? I guess from your topology that Vlan 44 goes directly to firewall, and all other vlans goes by L3 switch. If this is correct, your link from L3 G3/1 to firewall should be a trunk, but your G3/1 is configured as an access port, since only vlan 2 goes out. You need to configure that port as a trunk to be able to carry traffic from all vlans.
Hope this helps
Eugen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-09-2012 09:07 AM
I had made this port 3/1 trunk. But then, even vlan 2 stops communicating with external world. But, can I connect a trunk port with the internal interface of firewall having ip 160.6.141.254?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide