- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: Need Helping Fixing "Enable" Password
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Need Helping Fixing "Enable" Password & VPN Access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 09:16 AM - edited 03-08-2019 12:26 PM
PROBLEM #1
I have 2 identical Cisco 3650 switches. I was trying to reset enable password on switch #1. Followed up tips in an older forum post I made and it ended up removing the pre-authentication that required I log in via privileged user first and then enter "enable" mode with enable password. Now, it logs in directly to enable mode instead. I cannot figure out how to re-add the user back so it requires that method first for extra security.
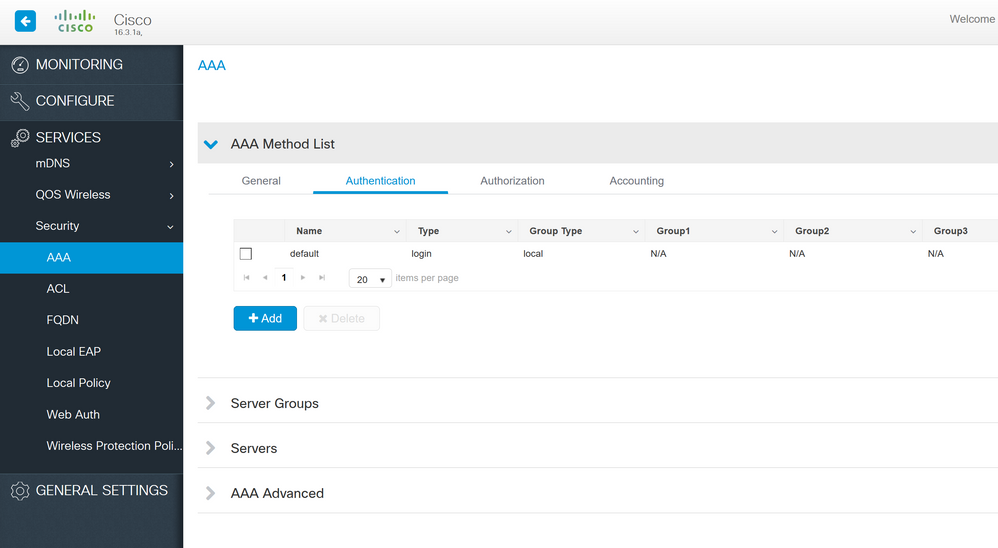
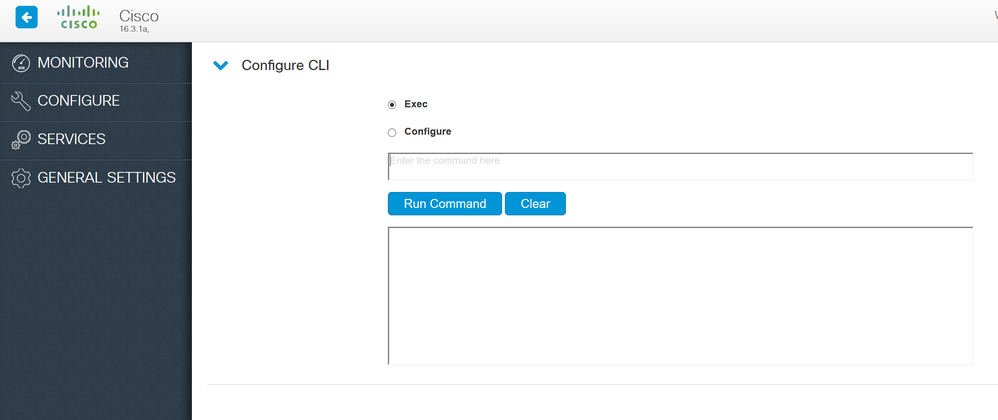
I'm using SecureCRT SSH2 protocol. I was able to access primary switch #1 via web gui using myusername still. I think I might be able to fix the issue via the interface there. See attached, not 100% sure though. Looks like the options are there, but I'd rather not fiddle until someone can clarify.
This is the only thing I see from the moment I log in (goes directly into enabled mode) and running that command, nothing else.
Cisco3650# Cisco3650#conf t Enter configuration commands, one per line. End with CNTL/Z. Cisco3650(config)#no aaa new-model Cisco3650(config)# Cisco3650(config)#end Cisco3650#wr Building configuration... Compressed configuration from 24401 bytes to 9027 bytes[OK] Cisco3650#
Here's a comparison of the 2 switches.
Switch #1 (main one trying to fix)
version 16.3 no service pad service timestamps debug datetime msec service timestamps log datetime msec service password-encryption service compress-config no service password-recovery no platform punt-keepalive disable-kernel-core ! hostname Cisco3650 ! ! vrf definition Mgmt-vrf ! address-family ipv4 exit-address-family ! address-family ipv6 exit-address-family ! ! no aaa new-model clock timezone EST -5 0 facility-alarm critical exceed-action shutdown switch 1 provision ws-c3650-24ts
Switch #2 (works correctly by logging into myusername first and manually having to enter "en" mode)
version 16.3 no service pad service timestamps debug datetime msec service timestamps log datetime msec service compress-config no service password-recovery no platform punt-keepalive disable-kernel-core ! hostname Switch2 ! ! vrf definition Mgmt-vrf ! address-family ipv4 exit-address-family ! address-family ipv6 exit-address-family ! no logging console enable secret 5 xxxxxxxxxxxxxxxx enable password TLNsxxxxxxxxxxxxxxxx ! no aaa new-model clock timezone EST -5 0 facility-alarm critical exceed-action shutdown switch 2 provision ws-c3650-24ts
PROBLEM #2
So in addition to the enable mode password issue on switch #1 I'm having this odd issue with switch #2 where it works fine (logs into myusername first, then into enable mode). However, it doesn't work with new enable password I set when I log in via VPN IP address which is already whitelisted in ACL and worked fine before I reset enable password. It's crazy, I log in just fine directly via SSH2 but via the VPN IP it no longer works. It works on myusername/pw but enable pw won't work. Same one works directly into switch. ACL config is 100% identical on switches #1 and #2 as well.
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2017 11:10 AM
Cisco3650#sh run | s ssh|vty|enable|privilege enable secret 5 $1$U/X8$xwPC/xxxxxxxxxxxxx username myusername privilege 15 secret 5 $1$Cbkx$xxxxxxxxxxxxx.cp4C1 ip ssh version 2 line vty 0 4 access-class Manage-SSH in exec-timeout 480 0 login local length 0 transport input ssh line vty 5 15 access-class Manage-SSH in exec-timeout 480 0 login local length 0 transport input ssh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2017 11:32 AM
Nothing is wrong with the config. Please reboot when it is convenient and let us know. Do NOT forget to save your changes before reboot.
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 10:38 AM
Didn't work.
1. Saved change via "wr" command
2. Rebooted via "reload" confirm method.
Still doesn't authenticate via username first before entering enable mode.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 04:54 PM
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 05:27 PM
Here's the output...(I've removed VLAN info and private stuff)
Cisco3650#sh run
Building configuration...
Current configuration : 26408 bytes
!
! Last configuration change at 22:28:21 EST Sun Oct 29 2017
!
version 16.3
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
service password-encryption
service compress-config
no service password-recovery
no platform punt-keepalive disable-kernel-core
!
hostname Cisco3650
!
!
vrf definition Mgmt-vrf
!
address-family ipv4
exit-address-family
!
address-family ipv6
exit-address-family
!
enable secret 5 $1$U/X8$xwPC/xxxxxxxxxxxxxxx
!
no aaa new-model
clock timezone EST -5 0
facility-alarm critical exceed-action shutdown
switch 1 provision ws-c3650-24ts
!
!
!
!
ip routing
!
!
!
ip name-server xxx.xxx.xxx.62 xxx.xxx.xxx.61
ip domain name company.com
!
!
!
!
!
!
!
!
vtp mode transparent
!
!
crypto pki trustpoint HTTPS_SS_CERT_KEYPAIR
enrollment selfsigned
serial-number
revocation-check none
rsakeypair HTTPS_SS_CERT_KEYPAIR
!
!
crypto pki certificate chain HTTPS_SS_CERT_KEYPAIR
certificate self-signed 01
quit
errdisable recovery cause udld
errdisable recovery cause bpduguard
errdisable recovery cause security-violation
errdisable recovery cause channel-misconfig
errdisable recovery cause pagp-flap
errdisable recovery cause dtp-flap
errdisable recovery cause link-flap
errdisable recovery cause gbic-invalid
errdisable recovery cause psecure-violation
errdisable recovery cause dhcp-rate-limit
errdisable recovery cause vmps
errdisable recovery cause loopback
errdisable recovery interval 120
license boot level ipbasek9
diagnostic bootup level minimal
spanning-tree mode rapid-pvst
spanning-tree extend system-id
!
username myusername privilege 15 secret 5 $1$Cbkx$xxxxxxxxxxxxxxx
!
redundancy
mode sso
!
hw-switch switch 1 logging onboard message
!
!
class-map match-any system-cpp-police-topology-control
description Topology control
class-map match-any system-cpp-police-sw-forward
description Sw forwarding, SGT Cache Full, LOGGING
class-map match-any system-cpp-default
description DHCP snooping, show forward and rest of traffic
class-map match-any system-cpp-police-sys-data
description Learning cache ovfl, Crypto Control, Exception, EGR Exception, NFL SAMPLED DATA, Gold Pkt, RPF Failed
class-map match-any system-cpp-police-punt-webauth
description Punt Webauth
class-map match-any system-cpp-police-forus
description Forus Address resolution and Forus traffic
class-map match-any system-cpp-police-multicast-end-station
description MCAST END STATION
class-map match-any system-cpp-police-multicast
description Transit Traffic and MCAST Data
class-map match-any system-cpp-police-l2-control
description L2 control
class-map match-any system-cpp-police-dot1x-auth
description DOT1X Auth
class-map match-any system-cpp-police-data
description ICMP_GEN and BROADCAST
class-map match-any system-cpp-police-control-low-priority
description ICMP redirect and general punt
class-map match-any system-cpp-police-wireless-priority1
description Wireless priority 1
class-map match-any system-cpp-police-wireless-priority2
description Wireless priority 2
class-map match-any system-cpp-police-wireless-priority3-4-5
description Wireless priority 3,4 and 5
class-map match-any non-client-nrt-class
class-map match-any system-cpp-police-routing-control
description Routing control
class-map match-any system-cpp-police-protocol-snooping
description Protocol snooping
!
policy-map port_child_policy
class non-client-nrt-class
bandwidth remaining ratio 10
policy-map system-cpp-policy
class system-cpp-police-data
police rate 200 pps
class system-cpp-police-sys-data
police rate 100 pps
class system-cpp-police-sw-forward
police rate 1000 pps
class system-cpp-police-multicast
police rate 500 pps
class system-cpp-police-multicast-end-station
police rate 2000 pps
class system-cpp-police-punt-webauth
class system-cpp-police-l2-control
class system-cpp-police-routing-control
police rate 1800 pps
class system-cpp-police-control-low-priority
class system-cpp-police-wireless-priority1
class system-cpp-police-wireless-priority2
class system-cpp-police-wireless-priority3-4-5
class system-cpp-police-topology-control
class system-cpp-police-dot1x-auth
class system-cpp-police-protocol-snooping
class system-cpp-police-forus
class system-cpp-default
policy-map speed25
class class-default
police cir percent 25 conform-action transmit exceed-action drop
!
!
!
!
!
!
!
!
!
!
!
!
!
!
ip forward-protocol nd
ip http server
ip http access-class 1
ip http authentication local
ip http secure-server
!
ip ssh version 2
!
ip access-list extended AutoQos-4.0-wlan-Acl-Bulk-Data
permit tcp any any eq 22
permit tcp any any eq 465
permit tcp any any eq 143
permit tcp any any eq 993
permit tcp any any eq 995
permit tcp any any eq 1914
permit tcp any any eq ftp
permit tcp any any eq ftp-data
permit tcp any any eq smtp
permit tcp any any eq pop3
ip access-list extended AutoQos-4.0-wlan-Acl-MultiEnhanced-Conf
permit udp any any range 16384 32767
permit tcp any any range 50000 59999
ip access-list extended AutoQos-4.0-wlan-Acl-Scavanger
permit tcp any any range 2300 2400
permit udp any any range 2300 2400
permit tcp any any range 6881 6999
permit tcp any any range 28800 29100
permit tcp any any eq 1214
permit udp any any eq 1214
permit tcp any any eq 3689
permit udp any any eq 3689
permit tcp any any eq 11999
ip access-list extended AutoQos-4.0-wlan-Acl-Signaling
permit tcp any any range 2000 2002
permit tcp any any range 5060 5061
permit udp any any range 5060 5061
ip access-list extended AutoQos-4.0-wlan-Acl-Transactional-Data
permit tcp any any eq 443
permit tcp any any eq 1521
permit udp any any eq 1521
permit tcp any any eq 1526
permit udp any any eq 1526
permit tcp any any eq 1575
permit udp any any eq 1575
permit tcp any any eq 1630
permit udp any any eq 1630
permit tcp any any eq 1527
permit tcp any any eq 6200
permit tcp any any eq 3389
permit tcp any any eq 5985
permit tcp any any eq 8080
ip access-list extended Manage-SSH
permit tcp host xxx.xxx.xxx.6 host 0.0.0.0 eq 22
permit tcp any host xxx.xxx.xxx.75 eq 22
permit tcp host xxx.xxx.xxx.10 host 0.0.0.0 eq 22
permit tcp host xxx.xxx.xxx.25 host 0.0.0.0 eq 22
!
access-list 1 permit xxx.xxx.xxx.25
access-list 101 permit tcp host xxx.xxx.xxx.25 host xxx.xxx.xxx.52 eq www
access-list 101 permit tcp host xxx.xxx.xxx.25 host xxx.xxx.xxx.52 eq 443
access-list 115 permit tcp host xxx.xxx.xxx.6 host 0.0.0.0 eq 22
!
snmp-server community public RO
snmp-server community private RW
!
ipv6 access-list preauth_v6
permit udp any any eq domain
permit tcp any any eq domain
permit icmp any any nd-ns
permit icmp any any nd-na
permit icmp any any router-solicitation
permit icmp any any router-advertisement
permit icmp any any redirect
permit udp any eq 547 any eq 546
permit udp any eq 546 any eq 547
deny ipv6 any any
!
control-plane
service-policy input system-cpp-policy
!
!
!
line con 0
exec-timeout 480 0
login local
stopbits 1
line aux 0
stopbits 1
line vty 0 4
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
transport input ssh
line vty 5 15
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
transport input ssh
!
ntp authenticate
ntp peer 81.6.42.224
ntp peer 96.47.67.105
ntp server 64.209.210.20
ntp server 50.255.89.205
wsma agent exec
profile httplistener
profile httpslistener
!
wsma agent config
profile httplistener
profile httpslistener
!
wsma agent filesys
profile httplistener
profile httpslistener
!
wsma agent notify
profile httplistener
profile httpslistener
!
!
wsma profile listener httplistener
transport http
!
wsma profile listener httpslistener
transport https
!
ap dot11 airtime-fairness policy-name Default 0
ap group default-group
ap hyperlocation ble-beacon 0
ap hyperlocation ble-beacon 1
ap hyperlocation ble-beacon 2
ap hyperlocation ble-beacon 3
ap hyperlocation ble-beacon 4
end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 05:44 PM
P.S.:- I also do not see the username/password combos in the output.
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 05:51 PM
I know, and that's my whole point of this thread is HOW to fix that.
The old copy of sh run output before I made changes (poor advice given by another user apparently), is below.
enable secret 5 $1$Df4G$.xxxxxxxxxxxx enable password xxxxxxxxxxxx
The VTY lines are exactly the same now and from old copy, FYI.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-30-2017 06:37 PM
I am also suspecting there could be a command which allows login to the top level (which is not posted -- may be related with interfaces).
One thing, you could try is adding the following command (if you have enable secret/password is configured):
line vty 0 4
access-class Manage-SSH in
exec-timeout 480 0
login local
privilege 1
length 0
transport input ssh
line vty 5 15
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
privilege 1
transport input ssh
!
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-31-2017 09:44 AM
One thing, you could try is adding the following command (if you have enable secret/password is configured):
You mean run each of those commands individually via en / conf mode? I'm confused.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-31-2017 03:45 PM - edited 10-31-2017 03:47 PM
You will need to login to the switch and run the following commands:-
config t
line vty 0 4
access-class Manage-SSH in
exec-timeout 480 0
login local
privilege level 1
length 0
transport input ssh
line vty 5 15
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
privilege level 1
transport input ssh
!
What the above commands do is restrict SSH access to privilege level 1. You will need to enter enable password to have exec access.
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-31-2017 04:29 PM
Thank you. I ran the below. I did not "wr" yet or of course reload the switch, but I still log in directly to enable access mode still. Didn't fix it yet.
Cisco3650#conf t Enter configuration commands, one per line. End with CNTL/Z. Cisco3650(config)#line vty 0 4 Cisco3650(config-line)#access-class Manage-SSH in Cisco3650(config-line)#exec-timeout 480 0 Cisco3650(config-line)#login local Cisco3650(config-line)#privilege level 1 Cisco3650(config-line)#length 0 Cisco3650(config-line)#transport input ssh Cisco3650(config-line)#line vty 5 15 Cisco3650(config-line)#access-class Manage-SSH in Cisco3650(config-line)#exec-timeout 480 0 Cisco3650(config-line)#login local Cisco3650(config-line)#length 0 Cisco3650(config-line)#privilege level 1 Cisco3650(config-line)#transport input ssh Cisco3650(config-line)#! Cisco3650(config-line)# Cisco3650#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-31-2017 04:36 PM
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 05:33 AM - edited 11-01-2017 05:35 AM
Here's the snippet that you're looking for...
Current configuration : 26420 bytes
!
! Last configuration change at 18:45:15 EST Tue Oct 31 2017 by myusername
!
version 16.3
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
service password-encryption
service compress-config
no service password-recovery
no platform punt-keepalive disable-kernel-core
!
hostname Cisco3650
!
!
vrf definition Mgmt-vrf
!
address-family ipv4
exit-address-family
!
address-family ipv6
exit-address-family
!
enable secret 5 $1$U/X8$xxxxxxxxxxxxxxxxxxxxxxxxxxx
!
no aaa new-model
clock timezone EST -5 0
facility-alarm critical exceed-action shutdown
switch 1 provision ws-c3650-24ts
!
!
!
!
ip routing
!
!
!
ip name-server xxx.xxx.xxx.62 xxx.xxx.xxx.61
ip domain name company.com
!
!
!
!
!
vtp mode transparent
!
!
crypto pki trustpoint HTTPS_SS_CERT_KEYPAIR
enrollment selfsigned
serial-number
revocation-check none
rsakeypair HTTPS_SS_CERT_KEYPAIR
!
!
crypto pki certificate chain HTTPS_SS_CERT_KEYPAIR
certificate self-signed 01
quit
errdisable recovery cause udld
errdisable recovery cause bpduguard
errdisable recovery cause security-violation
errdisable recovery cause channel-misconfig
errdisable recovery cause pagp-flap
errdisable recovery cause dtp-flap
errdisable recovery cause link-flap
errdisable recovery cause gbic-invalid
errdisable recovery cause psecure-violation
errdisable recovery cause dhcp-rate-limit
errdisable recovery cause vmps
errdisable recovery cause loopback
errdisable recovery interval 120
license boot level ipbasek9
diagnostic bootup level minimal
spanning-tree mode rapid-pvst
spanning-tree extend system-id
!
username myusername privilege 15 secret 5 $1$Cbkxxxxxxxxxxxxxxxxxxxxxxxxxxxx
!
redundancy
mode sso
!
hw-switch switch 1 logging onboard message
!
!
!
!
line con 0
exec-timeout 480 0
login local
stopbits 1
line aux 0
stopbits 1
line vty 0 4
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
transport input ssh
line vty 5 15
access-class Manage-SSH in
exec-timeout 480 0
login local
length 0
transport input ssh
!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 09:41 AM - edited 11-01-2017 09:46 AM
Did you try to SSH in from a different computer? When you attempt SSH from putty or secureCRT, you will need to be asked for "login as:" and "password" (unless you have configured "password xxxx" in line vty ..., which you did not). If not, I do not have anything else to say.
You could also try by enabling "aaa new-model".
The other thing I would do is reset to factory, reconfigure the switch, and see if it works.
HTH,
Meheretab
Meheretab
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 09:53 AM
How would I enable "aaa new-model"?
I tried to access via another IP, a VPN IP and it correctly authenticated with user/pw and then enable mode. Odd, not sure why it won't do that from my local IP (both are whitelisted in config).
I'm having the opposite effect from the switch #2 VPN IP (also whitelisted). This one, oddly enough authenticates via user/pw but won't work in enable mode. I'm using exact enable pw as I do directly when logging into 2nd switch. Also, 2nd switch *directly* works fine in user/pw authentication and enable mode. Not sure why first switch won't.
Result:
[root@vpn ~]# ssh username@xxx.xxx.xxx.53 Password: Switch2>en Password: Password: % Password: timeout expired! Password: % Password: timeout expired! % Bad secrets
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide